Featured News
-

 347How To
347How ToTop 10 Best Ways to Improve Your Wi-Fi Router’s Performance
Short Bytes: Today we are bringing you some of the best ways to improve your Wi-Fi router’s performance. This top 10 list...
-

 133How To
133How ToHow To Remove Pre-Installed Apps on Windows 10
Many users might hate these pre-installed apps in Windows 10, so we have made an article on How To Remove Pre-Installed Apps...
-
 173News
173NewsAnonymous Hacks Mexican Govt Website, Demand Justice For Rubén Espinosa
The online hacktivist Anonymous attacked the Mexican government website against the murder of Rubén Espinosa, a local photojournalist. Anonymous Mexico is all...
-

 112Opinion
112OpinionDEF CON – Upgrading your mom’s basement
If Black Hat is becoming the new RSA, then DEF CON is oozing toward Black Hat, it seems, and B-Sides is the...
-

 194Surveillance
194SurveillanceResearchers Develop Glasses To Protect You from Facial Recognition
Facial recognition software is cropping up everywhere, so it was only a matter of time before anti facial recognition tech started to catch...
-

 244Hacked
244HackedPakistani Intelligence Planning Hacking Attacks, Warns Indian Government
Short Bytes: The government of India has warned its six ministries regarding a probable Pakistani hacking attack to retrieve sensitive information from the computers...
-

 348News
348NewsHacking GPS Signals of Smartphones and In-Car Navigation System
We have already discussed that how our online connected world has become vulnerable to the hacking, which is causing our day-to-day things...
-

 367Geek
367GeekWindows 10 is Free, But Microsoft is Charging For Add-Ons/Other Features
Windows 10 is absolutely free for those who are upgrading from Windows 7 or Windows 8, but Microsoft played a clever trick...
-

 345News
345NewsHackers Turn Bus Terminal into Adult Movie Theater
Websites being the target of hackers is not a new phenomenon; we read about it every day. What one will not read...
-
 147How To
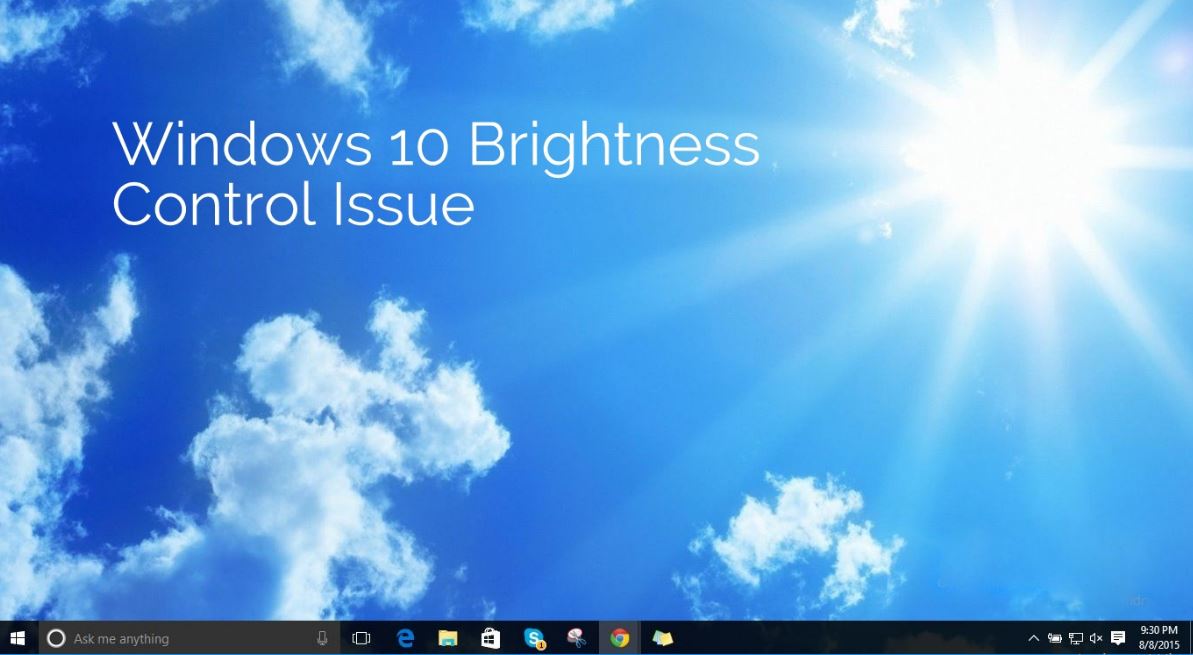
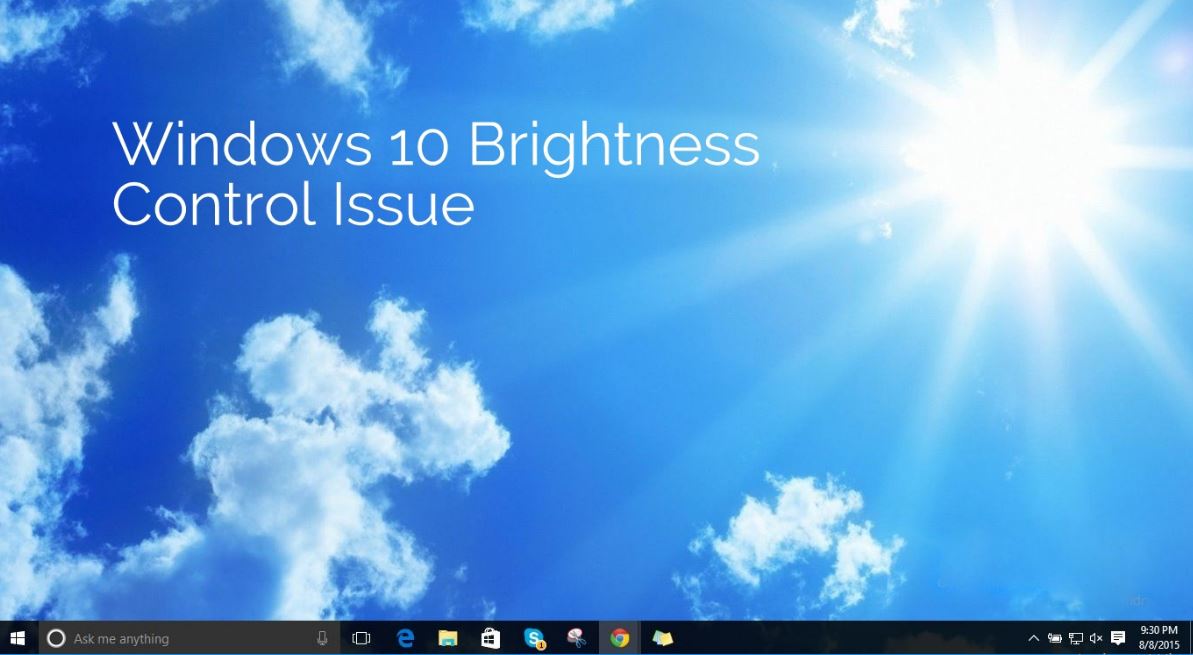
147How ToHow to Fix Windows 10 Brightness Control Not Working Issue
Short Bytes: Some Windows 10 users are experiencing a Windows 10 brightness control “not working” issue. This problem in the relevant drivers...
-

 309Hacked
309HackedFind a Bug in Windows 10, Get Up to $100,000 Microsoft Bug Bounty
Short Bytes: Microsoft has announced that it has updated its bug bounty program and increased the maximum $50,000 reward to $100,000. This...
-

 214Hacked
214HackedNow Electric Skateboards Have Been Hacked Using “FacePlant” Exploit
Short Bytes: Security researchers in Australia have exposed a serious flaw in the low energy Bluetooth controlled devices, as they hacked an...
-

 308Data Security
308Data Security7 Unexpected Hacks of 2015, Thanks To DefCon and Black Hat
This year, at DefCon 23 and Black Hat USA 2015 security conferences, hackers are going to discuss how vulnerable and severely flawed...
-

 249News
249NewsTiny Drones Using Insect-Like Vision for Better Navigation
Researchers and designers are working together to design tiny bug-sized drones but what’s giving them a hard time is their navigation system....
-
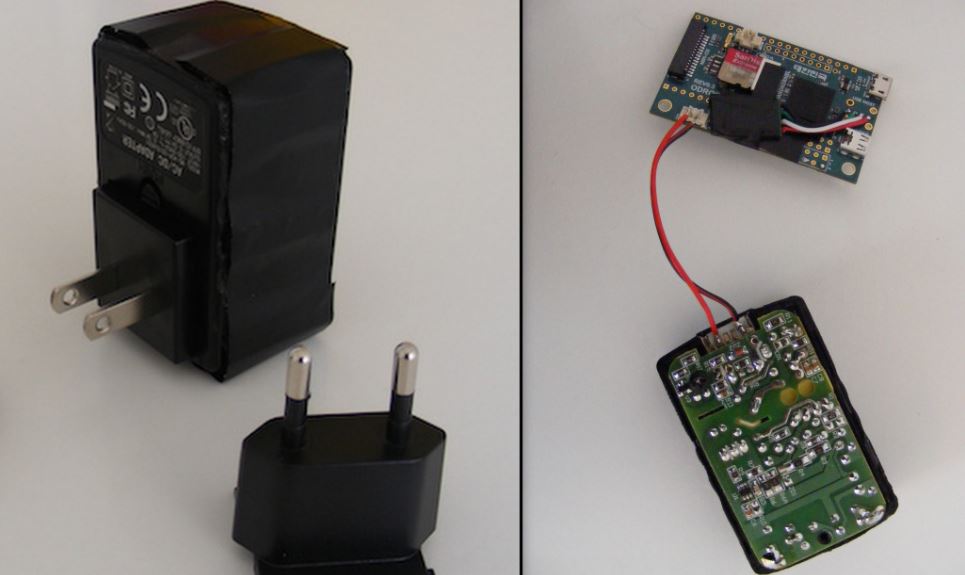
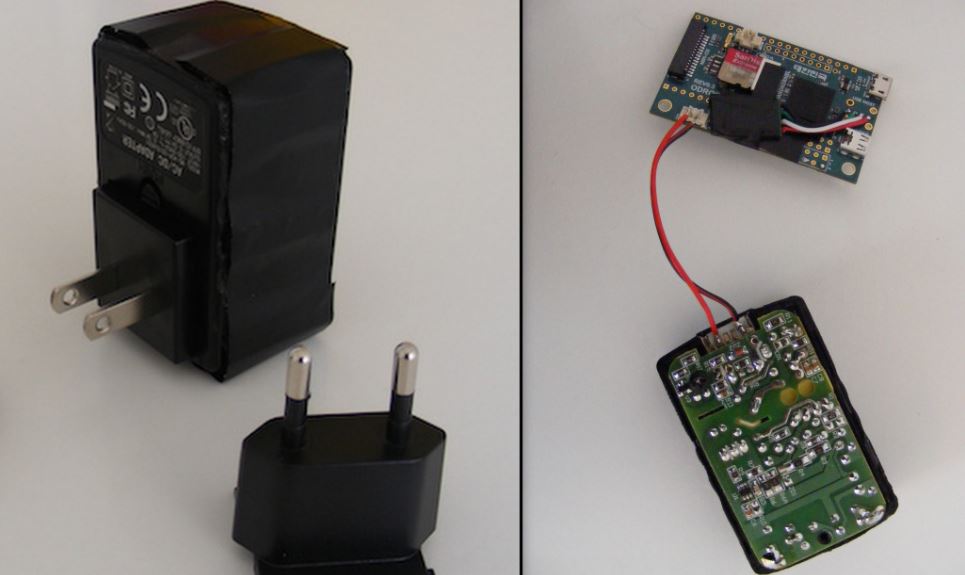 198Geek
198GeekHow to Convert a USB Charger Into a Linux Computer
Short Bytes: This DIY from Chris Robinson of NODE will show you how to make your own Linux computer from a USB...
-

 299Cyber Events
299Cyber EventsSpear Phishing Attack at Pentagon’s Network, Breached 4000 Military Accounts
The United States is now blaming the Russian hackers for hacking computers at the Pentagon. The United States military officials believe Russian...
-

 282Hacked
282HackedLaika BOSS: Lockheed Open Sources Secret Cyber Threat Detection Weapon
Short Bytes: Lockheed Martin has decided to open source its secret cyber threat detection tool Laika BOSS at the Black Hat Conference...
-

 103Opinion
103OpinionBlack Hat 2015 – Threats hit the road
This year at Black Hat, the focus was as much on hacking the intersections of data as on a specific computer platform.
-

 280Hacked
280HackedMan in the Cloud: Hackers Can Access Your Dropbox, Google Drive, OneDrive Files WITHOUT Password
Short Bytes: Researchers have found a new way to hack into your cloud syncing accounts without any username or password by deploying...
-
 289Hacked
289HackedRussian Hackers Attack Pentagon Computers, Used New and Unseen Methods
Short Bytes: In a recent cyberattack at Pentagon, Russian hackers are being suspected as the key players. This attack was launched around July...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




