Featured News
-
 223Data Security
223Data SecurityShield Your PC from Radiofrequency, Hackers Can Steal Data Using Radio/Sound Waves
A recent experiment by a researcher would force you to reconsider the safety of your important data and make you put a...
-
 280Hacked
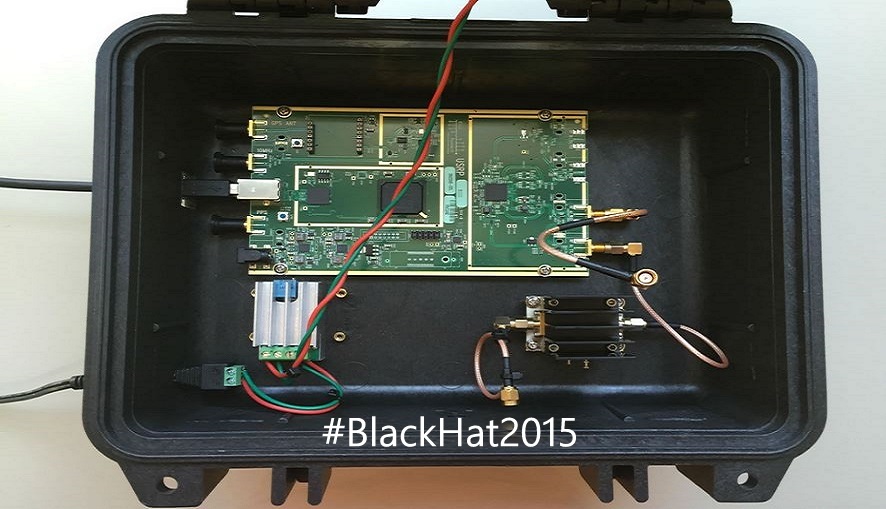
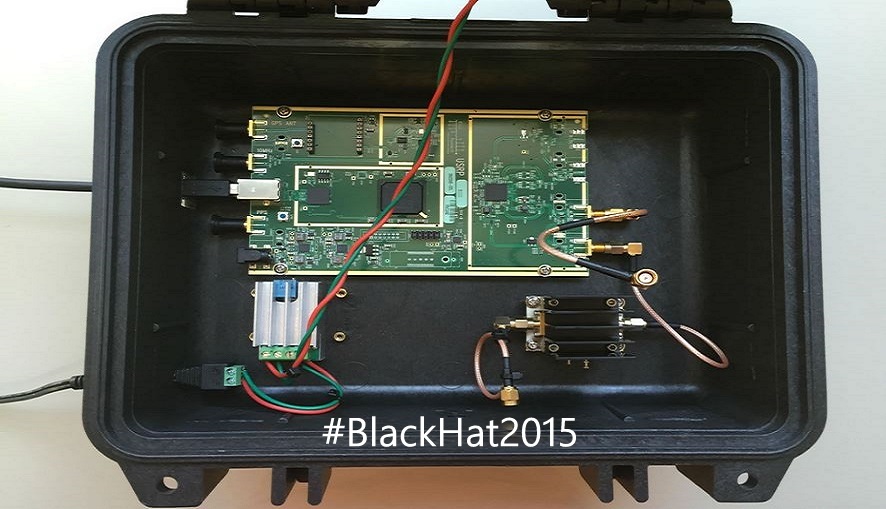
280HackedSatellite Hack: Hackers Can Easily Crack Satellites, Controlling Your Cars and Phones
Short Bytes: Colby Moore, a researcher from cyber security firm Synack, has taught the attendees of Black Hat Conf. something that can...
-

 232Hacking Tutorials
232Hacking TutorialsRunAsDate – Cracking Trial Software
It infuses the predefined date and time to the objective programming in this way preventing it from expiry. Demo variant programming basically...
-

 155Opinion
155OpinionHow’s Black Hat in 2015? It grows up (and leaves mom’s basement)
Blackhat grew! Not only did the hacker types leave their mom’s basement and get jobs, some even were forced to start explaining...
-

 205Cyber Crime
205Cyber CrimeISIS Social Media Recruiters Owned By 3 Chechen Girls
The extremist militant organization the so-called Islamic State (IS, previously ISIS/ISIL) often uses the recruitment tactic of catfishing, which means hiring Western females specifically...
-
 236Privacy
236PrivacyWindows 10, Privacy 0? ESET deep dives into the privacy of Microsoft’s new OS
Windows 10 offers more personalisation and integration than ever before. We take a look at the privacy implications of this.
-

 279Hacked
279HackedBiggest Security Update in History, Google Fixes Android Hijack Bug Stagefright
Short Bytes: This week, Google is releasing the “single largest software update the world has ever seen”. It has started rolling out patches for...
-

 335Hacked
335HackedSound Wave Hacking: Computers and Printers Hacked to Send Data as Sound Waves
Short Bytes: A team of security researchers have successfully demonstrated that the standard equipment inside computers, printers and other devices could be hacked...
-
 209Surveillance
209SurveillanceYour Smartphone and Laptop Battery Invading Your Privacy
A new research conducted by a group of researchers demonstrates how your smartphone and laptop battery can be used to invade your...
-

 240Cyber Events
240Cyber EventsU.S. Based Medical Software Company Breach Expose 4 Million People
The U.S. Department of Health and Human Services reports that earlier this year the records of 3.9 to 4 million people nationwide...
-
 444How To
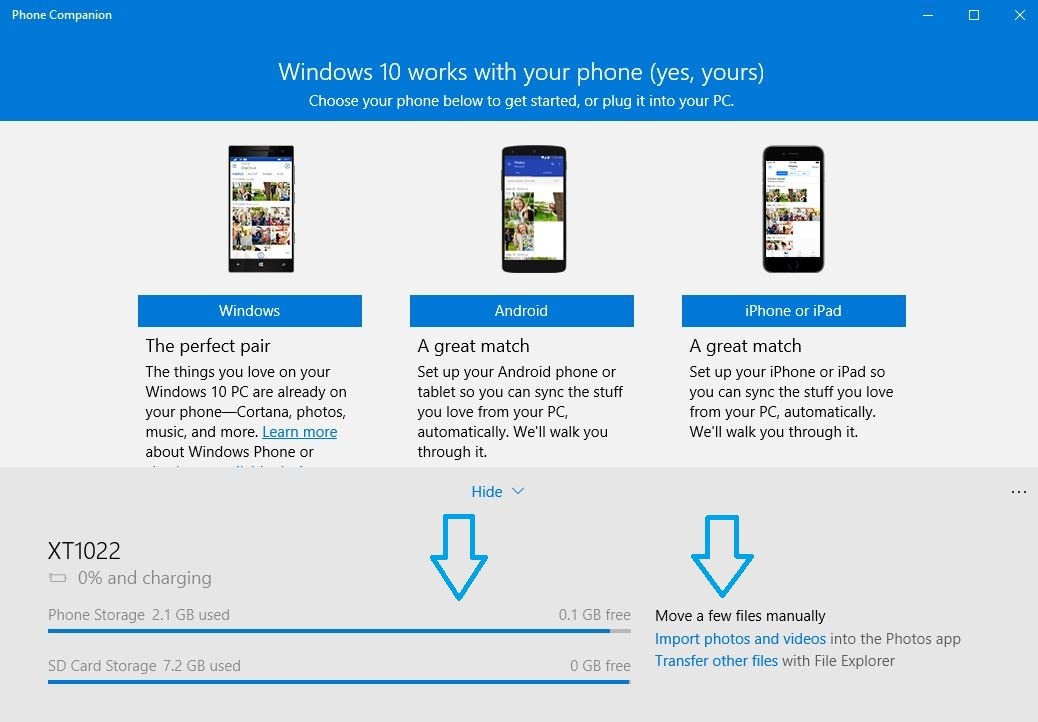
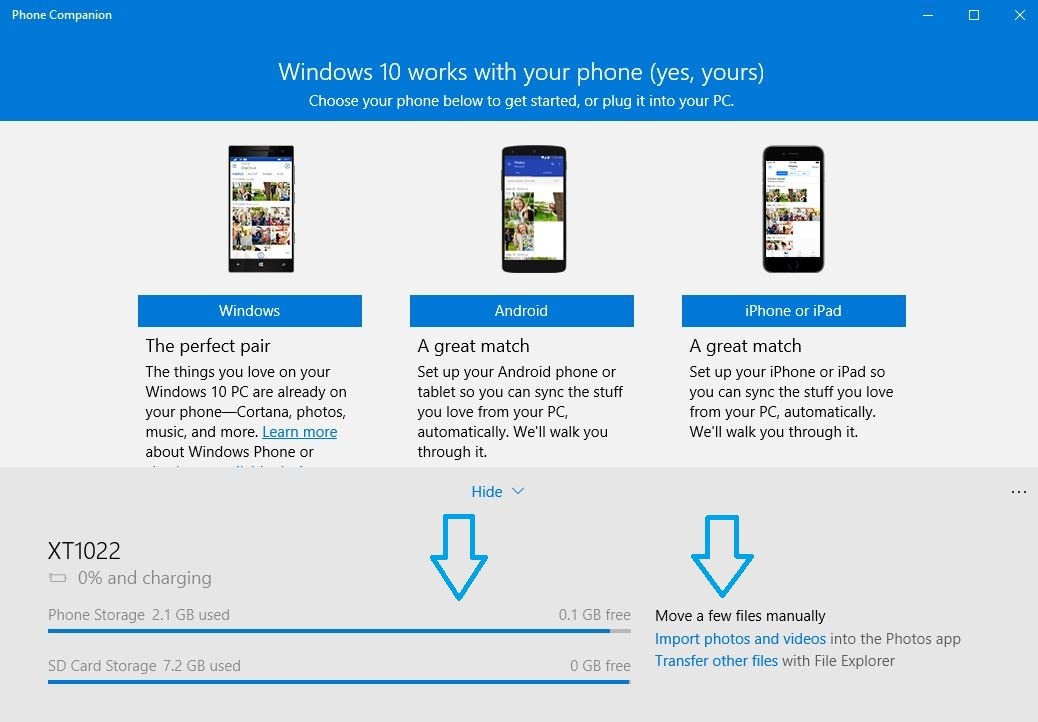
444How ToHow to Sync Your Android Phone and iPhone With Windows 10
Short Bytes: With Windows 10, there comes a pre-installed app called Windows 10 Phone Companion app. This app helps you to sync...
-

 292How To
292How ToCanonical Tells How to Choose the Best Laptop to Install Linux
Short Bytes: Canonical has released a list of Ubuntu desktop certified hardware to tell you the best laptop to install Linux. Even if...
-

 323Data Security
323Data SecurityElectronic Skateboards Are Easy To Hack
As we are approaching the much-awaited hacking conferences DefCon and Black Hat, security researchers and engineers are revealing their studies and exploits...
-
 252Data Security
252Data SecurityMiddle East’s Largest Classified Website Dubizzle Suffers Security Breach
Dubizzle, the popular Middle Eastern online classifieds for bargain hunters, sellers and job seekers has had its UAE servers compromised – albeit...
-

 72Malware
72MalwareTerracotta VPN network helps hackers remain anonymous
Hackers are using a commercially available VPN network in China to obscure the origin source of their activities.
-

 204Interview
204InterviewLightbulb moment: Why the Internet of Things is a security watershed
Senior research fellow Righard J. Zwienenberg on why the Internet of Things could be *the* key security issue for the foreseeable future.
-
 173Hacked
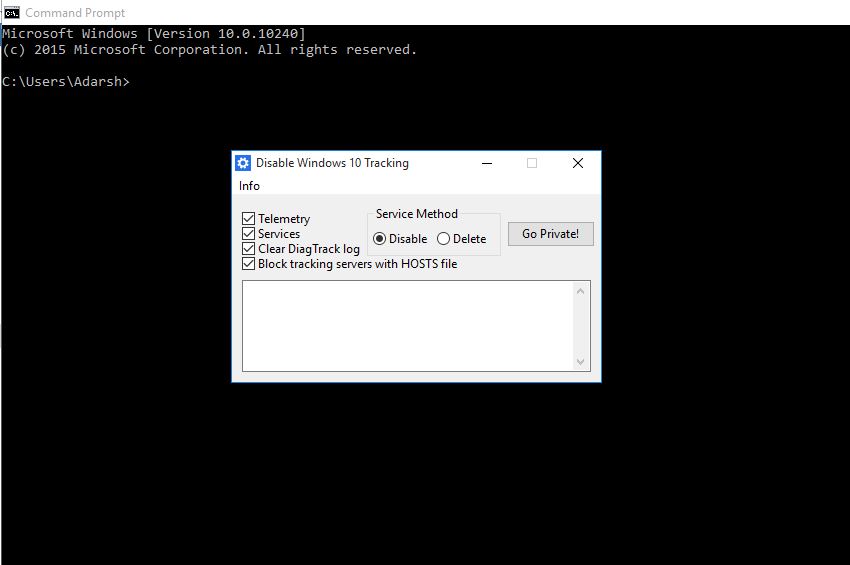
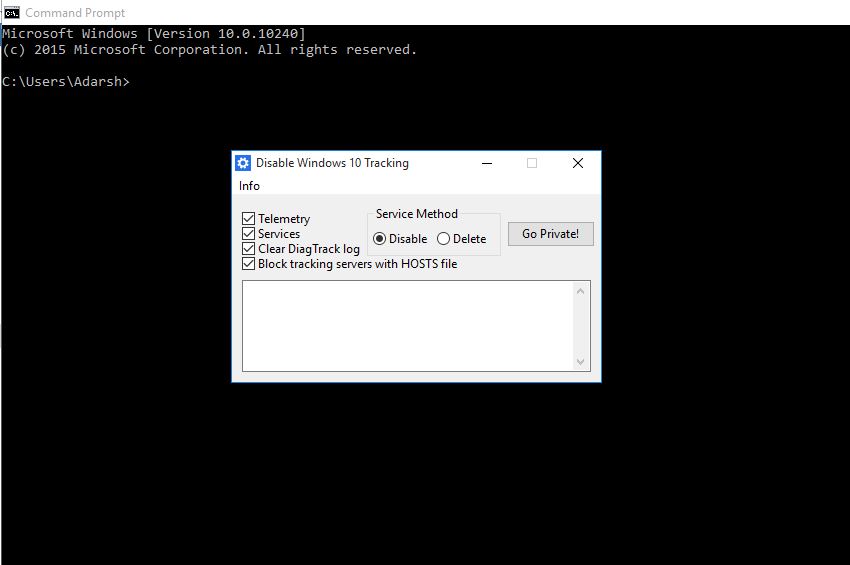
173HackedThis Open-source App Wants to Stop Windows 10 From Tracking You
Short Bytes: A developer has released an open-source tool called Disable Windows 10 Tracking to address your Windows 10 privacy concerns. This tool,...
-

 318Data Security
318Data SecurityYahoo Ad Network Hacked, Infecting Millions of Devices with Malware, Ransomware
Yahoo ad network has been exploited by a group of hackers that resulted in a serving of malware and ransomware adverts on...
-

 228News
228NewsSri Lankan Prime Minister’s Office Website Hacked
The Sri Lankan prime minister Ranil Wickremesinghe has his office website hacked by a hacktivist who hacks for #ForSyria. A hacker going with...
-
 296How To
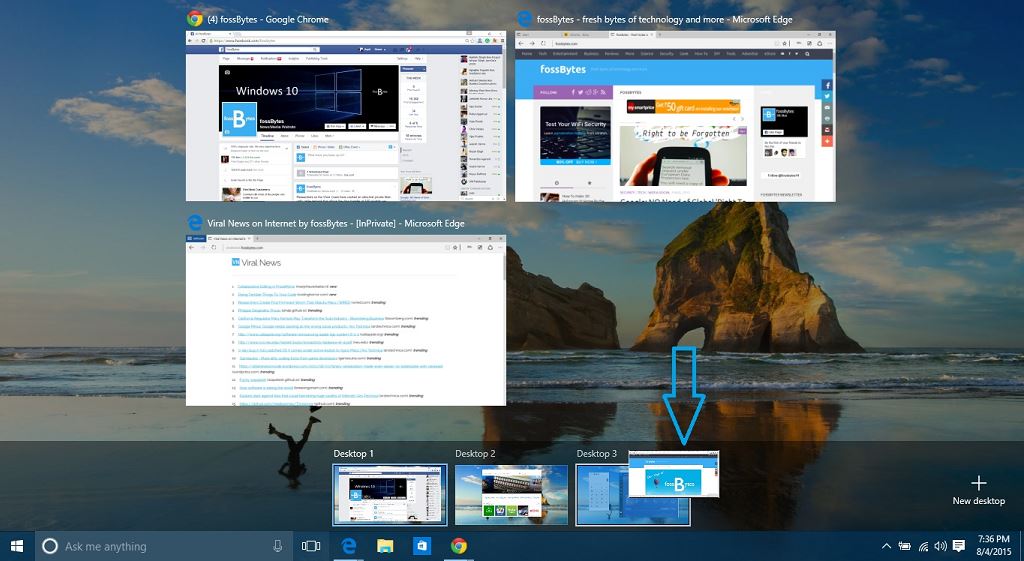
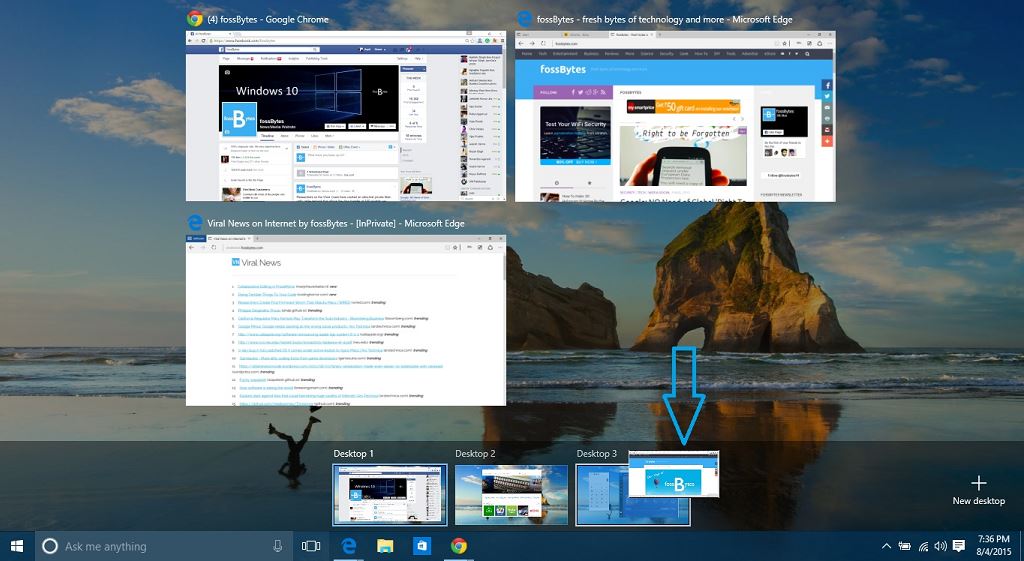
296How ToHow to Create and Use Virtual Desktops in Windows 10?
Short Bytes: Realizing the popularity of Virtual Desktops and needs of a power user, Microsoft has finally integrated this service in Windows...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




