Featured News
-

 82Malware
82MalwareSignatures, product testing, and the lingering death of AV
Is it time to revalue the role of anti-malware? Maybe, but uninformed or intentionally misleading mutterings about signatures are not where to...
-

 169Surveillance
169SurveillanceExposing Facebook privacy flaw is a crime? Sure Seems Like It
Aran Khanna, a Harvard student, was deprived of a chance to intern at Facebook after he exposed a critical privacy related flaw...
-

 371Hacked
371HackedWindows 10 Sends Tons of Data Every 30 Minutes to Microsoft Even When Told Not To
Short Bytes: Microsoft has some options in Windows 10 to enable the privacy protection, but according to some latest research done by...
-

 188How To
188How ToHow to Check the Status of Popular Websites
Short Bytes: Every popular online service exposes a status page to show the status of various service they offer to end user...
-
 344How To
344How ToRevenge of Mozilla: Firefox 40 for Windows 10 Changes Cortana’s Default Bing Search
Short Bytes: Mozilla has released Firefox 40 for Windows 10 and it comes with changes in user interface trying to blend with...
-

 259Privacy
259PrivacyHow to stop pervy pics popping up on your iPhone
Don't be cyber-flashed by a pervert. Make sure that your iOS device's AirDrop settings are configured properly to protect your eyes from...
-
 292News
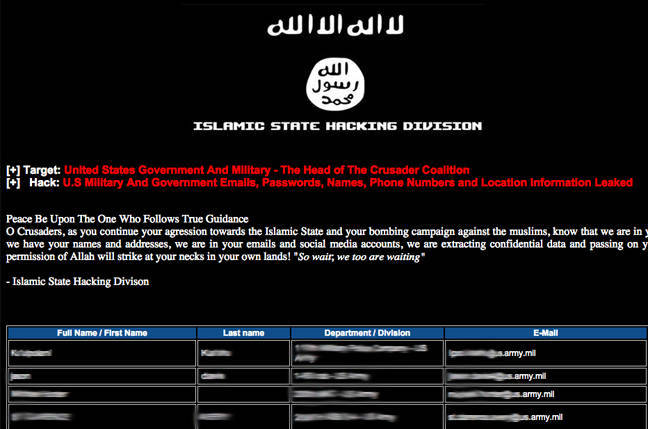
292NewsISIS Affiliated Hackers Leak Hacked Data of 1500 U.S. Military, Govt Personnel
A group of ISIS Affiliated Hackers has claimed to have hacked U.S. government servers stealing the personal data of hundreds of Government...
-
 300Geek
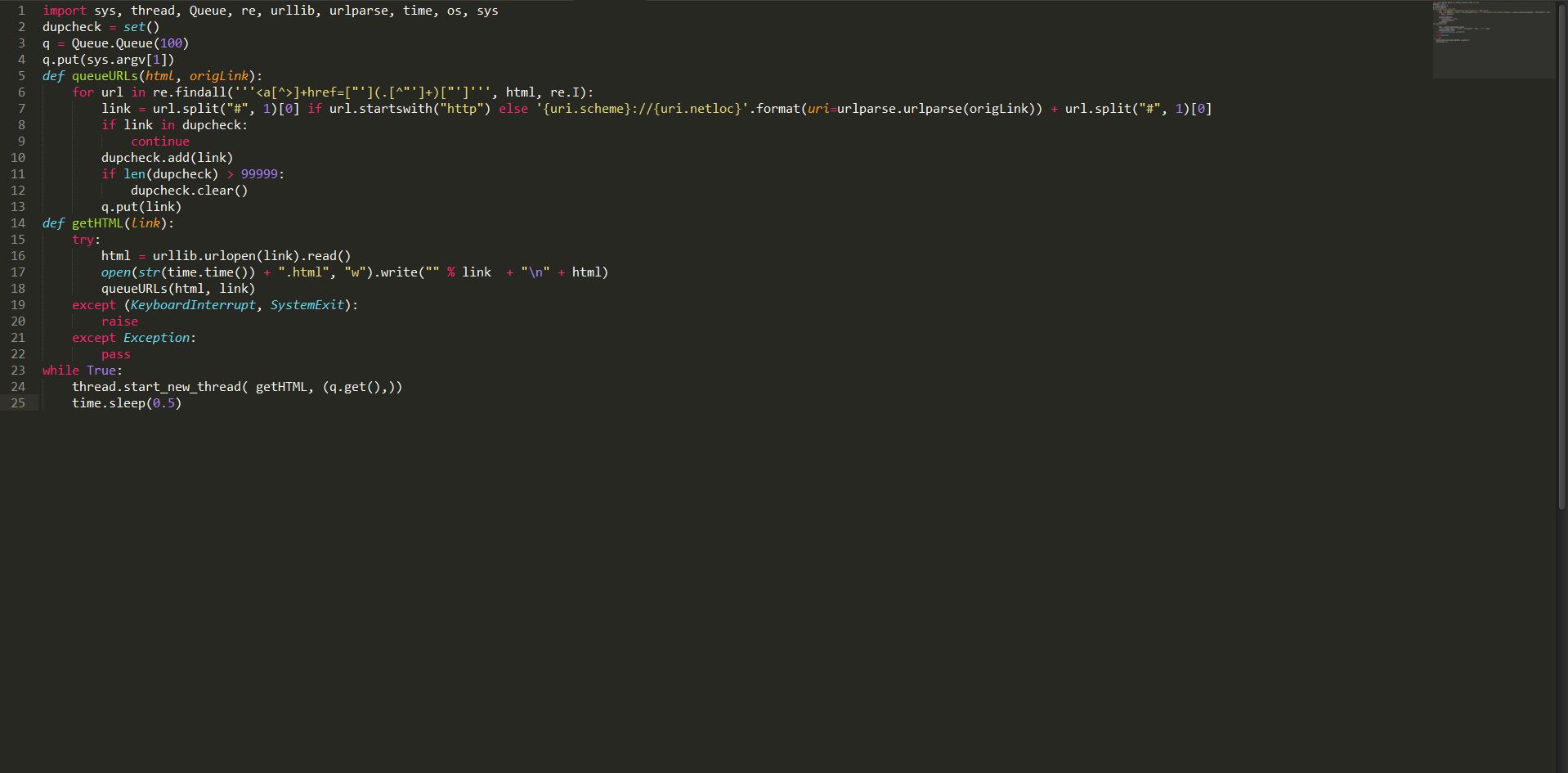
300GeekHow to Build a Basic Web Crawler in Python
Short Bytes: Web crawler is a program that browses the Internet (World Wide Web) in a predetermined, configurable and automated manner and performs...
-

 270Data Security
270Data SecurityResearchers Show How To Hack Corvette with A Text Message
A video demonstration by the University of California researchers how a simple text message can control your car. The months of July and August have...
-
 405How To
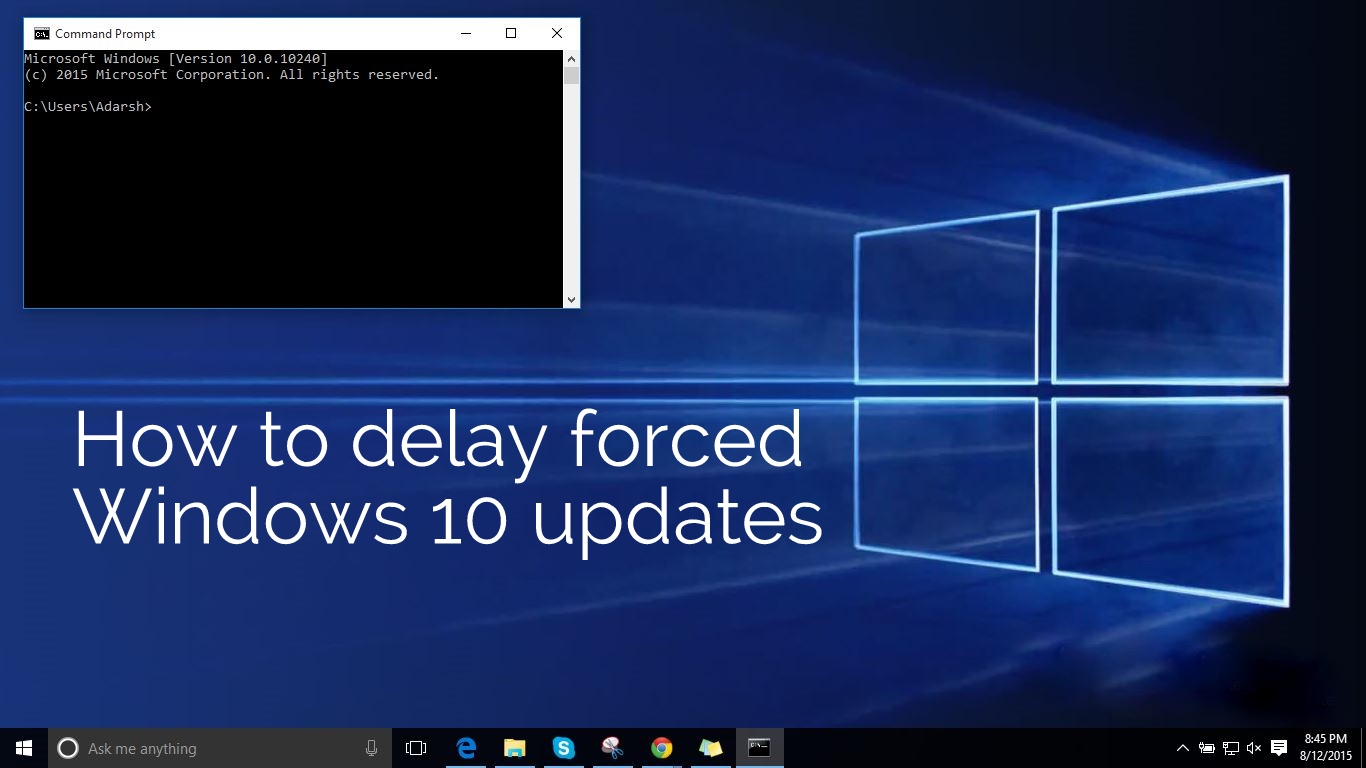
405How ToHow To Delay Forced Windows 10 Updates By Enabling Metered Connection Option
Short Bytes: With Windows 10, Microsoft has also overhauled the Windows Update process. You might already be knowing their no way of pausing...
-

 362Data Security
362Data SecurityWindows 10 Security Flaw Could Be Used To Exploit User Credentials
The first ever security flaw in Windows 10 is here — A team of security researchers have found a vulnerability in the...
-

 312News
312NewsCover Your Cams: Webcam of This Couple Got Hacked While Watching Netflix
Earlier we reported how hackers are using Remote Access Trojan (RAT) to get into your computer and record your online activity including your webcam...
-

 332Hacked
332HackedTop 10 Websites/Services To Protect Your Online Privacy
Short Bytes: In the world of cyber threats and privacy breaches, here’s a list of 10 websites and services you should know to...
-

 262Wifi Hacking
262Wifi HackingHacking WiFi – Selecting the best strategy
Not every hack will work under every circumstance, so choosing the right strategy is more likely to lead to success and less...
-

 257Hacking Tutorials
257Hacking TutorialsOllydbg – Cracking software like a pro
If you’ve ever wondered how software pirates can take software and crack it time and time again, even with security in place,...
-

 268Hacked
268HackedKali Linux 2.0 is Released, Download ISO and Torrent Files Here
Short Bytes: Kali Linux 2.0 has been released with tons of new features and it’s now based on Debian Jessie. It comes...
-

 116Cyber Crime
116Cyber CrimeHackers Steal $47 Million From American Tech Firm Ubiquiti
An unusual admission has been made by a tech firm to its investors — Posing as its employee, a hacker stole $46.7...
-

 226Data Security
226Data SecurityFacebook API Security Flaw Left 1.44 Billion Users’ Identities at Risk
A security flaw in the Facebook API allows hackers to decrypt and scan IDs, which left 1.44 billion Facebook users identities at...
-

 266How To
266How ToHow To Install Android Apps on Windows 10 Mobile
If your bored of using Windows phone then you can try this tutorial. In this article we will teach you “How To...
-

 302Data Security
302Data SecurityGas Stations Offering Internet-linked Fuel Tanks New Target for Hackers
In 2013, we at HackRead reported how oil and gas sector faces serious physical and online security threats. Now researchers have found...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




