Featured News
-

 110Data Security
110Data SecurityAndroid Devices in Danger! New Vulnerability Can Make Them Lifeless
Trend Micro has discovered a new vulnerability in the Android media service just days after the identification of Stagefright bug by Zimperium....
-

 180News
180NewsHotshot Antivirus Firms are Getting Hacked, Latest Victim is “BitDefender”
Popular anti-virus firm and computer security agency BitDefender has become the victim of a highly embarrassing data hack. Apparently, hackers took away...
-

 260Social Media Hacking
260Social Media HackingFlooding a Facebook User
This guide will show you how to flood a persons facebook wall, comments, and messages. What is flooding? Basically spamming the same...
-
 285Hacked
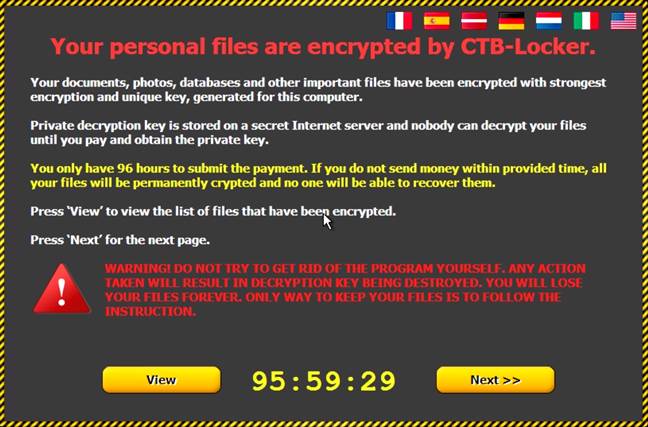
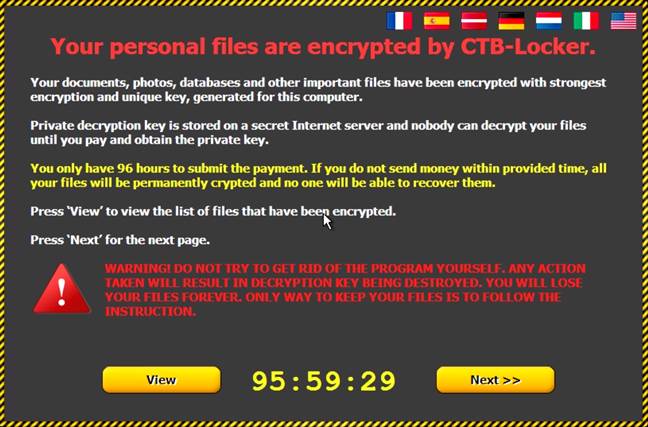
285HackedBeware: A Dangerous Windows 10 Ransomware Scam Is Spreading Online
Short Bytes : A Windows 10 Ransomware scam has been reported by Cisco security blog. This phishing scam sends fake emails that look...
-

 339Surveillance
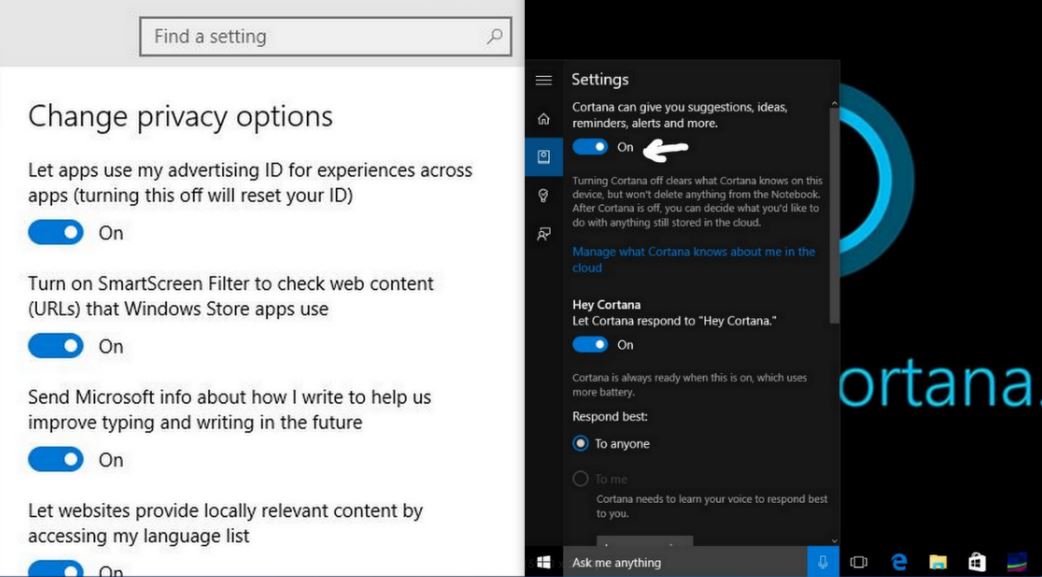
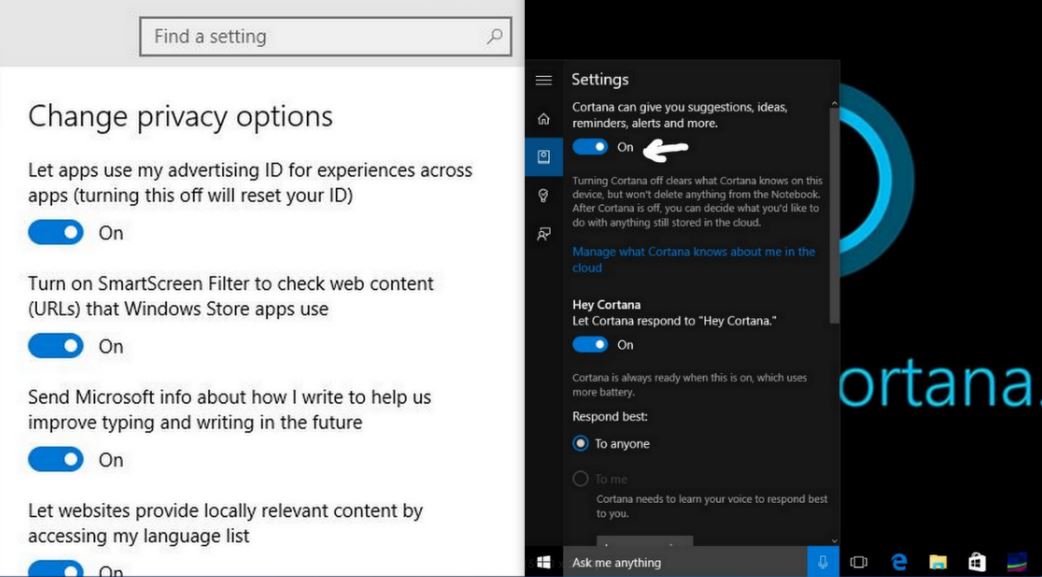
339SurveillanceWindows 10 is spying on you, but there’s a way out
If you have installed Windows 10 and agreed to its terms and conditions during installation then you are being spied on and this...
-

 133Cyber Crime
133Cyber CrimeHacking Team and other breaches as security lessons learned
Recent aggressive hacks on companies underline the need for good risk analysis, situational awareness, and incident response. Just ask AshleyMadison, Hacking Team,...
-

 200Hacked
200HackedUS Decides To Counter-attack Against Chinese Hacking
Short Bytes : As the cyber attacks are getting more and more pervasive, the White House is seeking ways to retaliate against...
-
 321Hacked
321HackedHow to Stop Windows 10 From Spying on You
Short Bytes : Windows 10 is released for all with lots of good features. On the other hand, its privacy policies are...
-

 252Geek
252GeekWhich are the Most Popular Programming Languages at Hackathons
Short Bytes : Devpost is the most popular tool used as a backend infrastructure in US hackathons. Recently, they released data telling...
-

 319Data Security
319Data SecurityTime To Cover Webcams: Wannabe Hackers Invading Your Privacy Using RAT
Digital hacking and learning about hacking has now become easier than you ever imagined, investigation report by the Digital Citizens Alliance reveals...
-

 347Hacked
347HackedTop 5 Facebook Scams That You Should Be Aware Of
Short Bytes: Social media sites such as Facebook and their immense user base are prone to scams most of the times. Here’s...
-

 179How To
179How ToPrank Your Friends With This Android Feature
Every one hates when their smartphone works very slow. In this tutorial we will teach you how to make an android smartphone...
-

 311Data Security
311Data SecurityHacker Shows How to Locate, Unlock, Start GM Cars with a Hacked Mobile App
As the dates for the Black Hat and Def Con Hacking Conference are approaching closer and closer, we are hearing more and...
-

 342Lists
342ListsMicrosoft Tells Which Lumia Phones Are Getting Windows 10 Mobile at Launch
Microsoft has released a list of Lumia phones that will be getting Windows 10 Mobile upgrade at the time of launch. Not...
-
 326How To
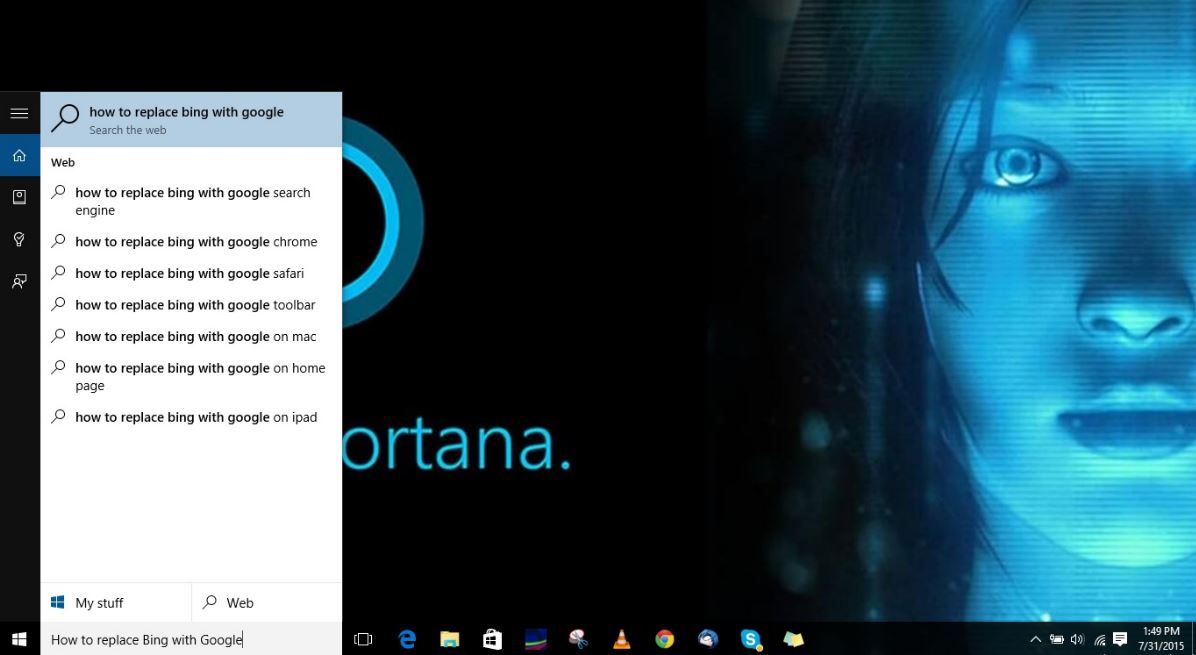
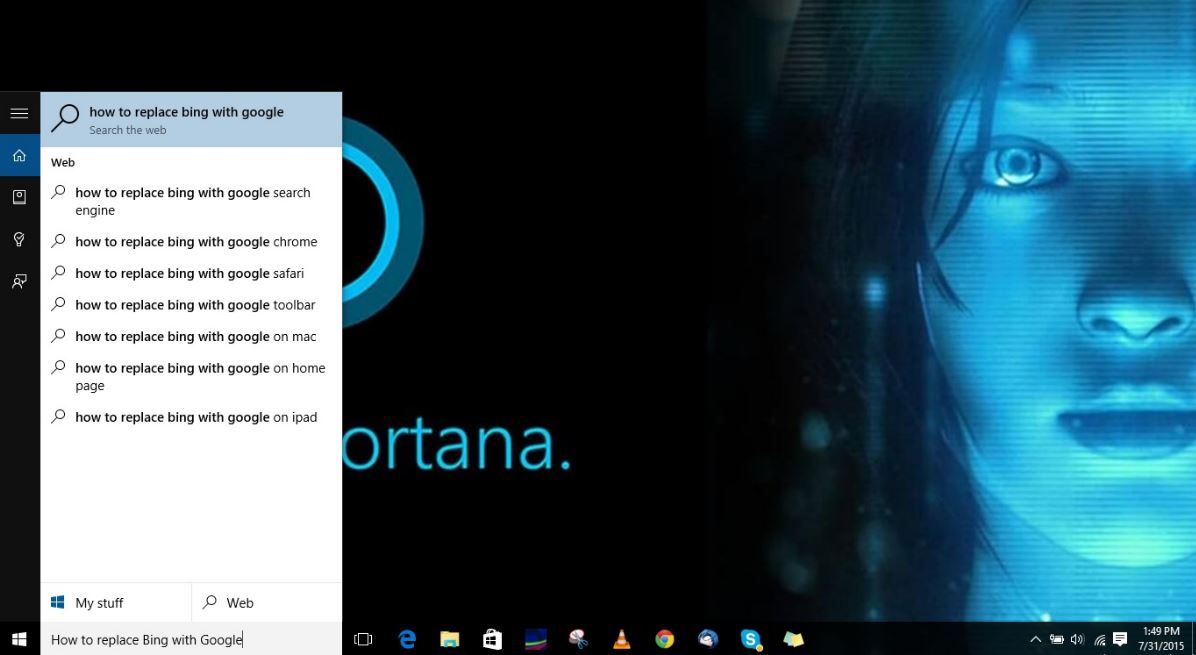
326How ToHow To Change Cortana’s Bing Search to Google in Windows 10 Using Bing2Google
Short Bytes : Bing search is deeply integrated in Windows 10 and you can’t change this search engine from your Cortana desktop...
-

 71How To
71How To5 Systems Admin relationship tips (so you’re on talking terms again)
Want to mend your systems admin relationship? On this Systems Administration appreciation day, we give you a few tips to help mend...
-
 414How To
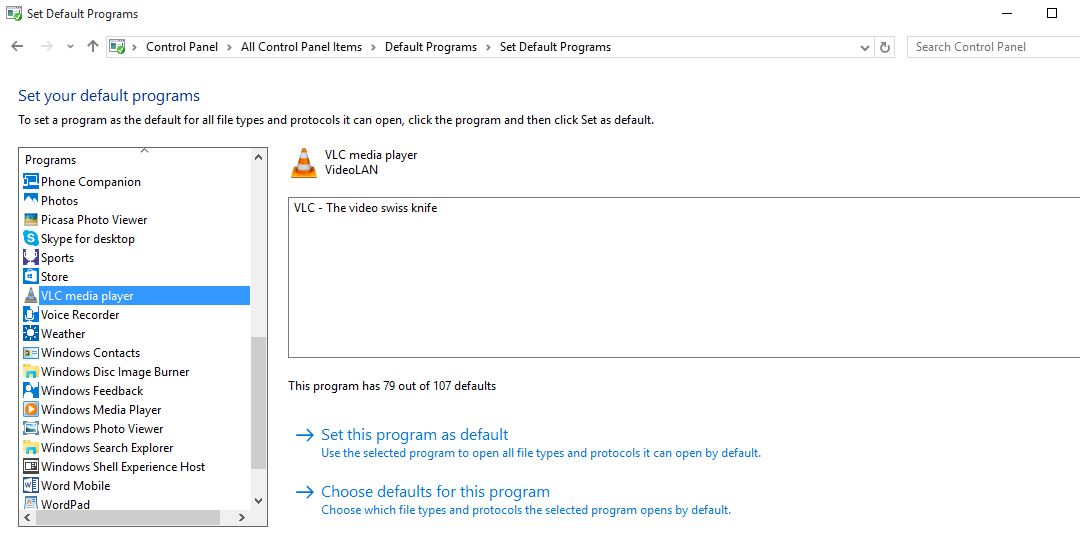
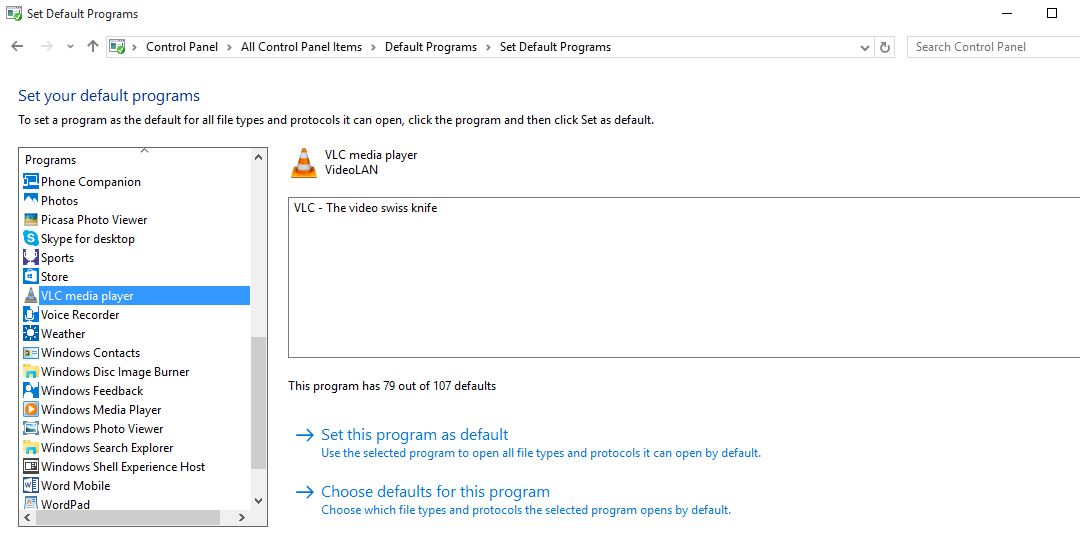
414How ToHow to Change Default Browser and Programs in Windows 10
Short Bytes : Windows 10 upgrade keeps your files, apps, and settings, but it changes your app preferences of last OS. Today...
-
 226Cyber Events
226Cyber EventsAnti-abortion Hackers Shut Down Planned Parenthood Website
On 29th July 2015, we reported how a group of anti-abortionist hackers hacked into the servers of Planned Parenthood, a pro-abortion organization. Now,...
-
 165Hacked
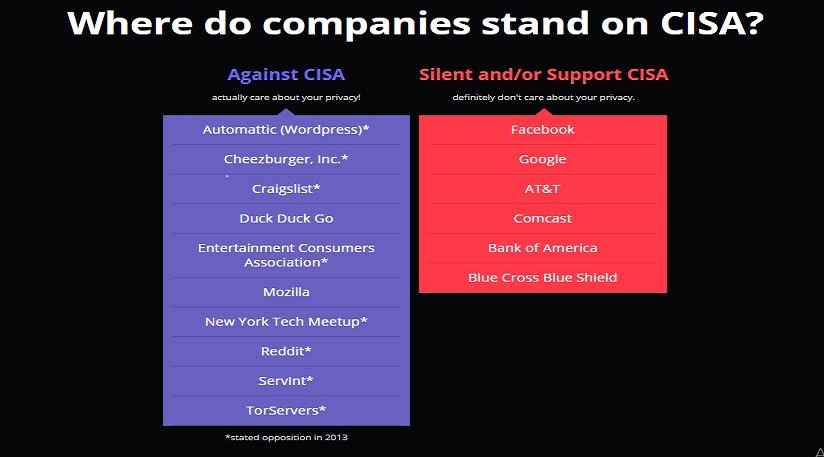
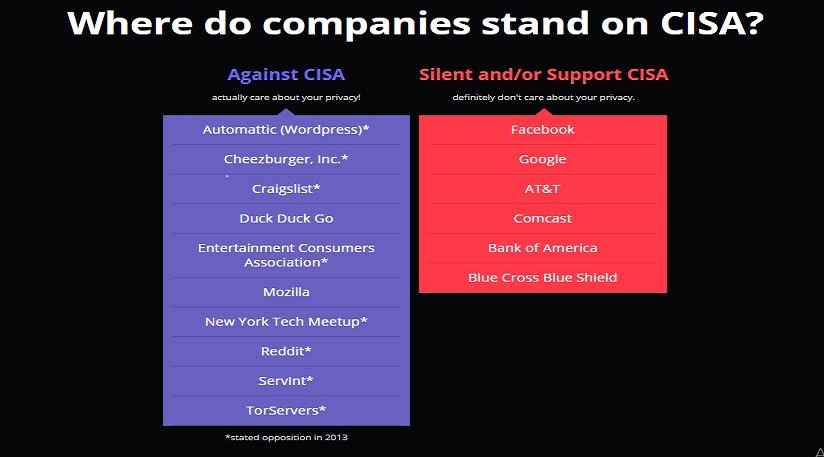
165HackedCISA Bill To Give Your Entire Personal Info To Government
Short Bytes : The recently proposed Cybersecurity Information Sharing Act (CISA) by the government looks like another surveillance law that outrightly gives...
-
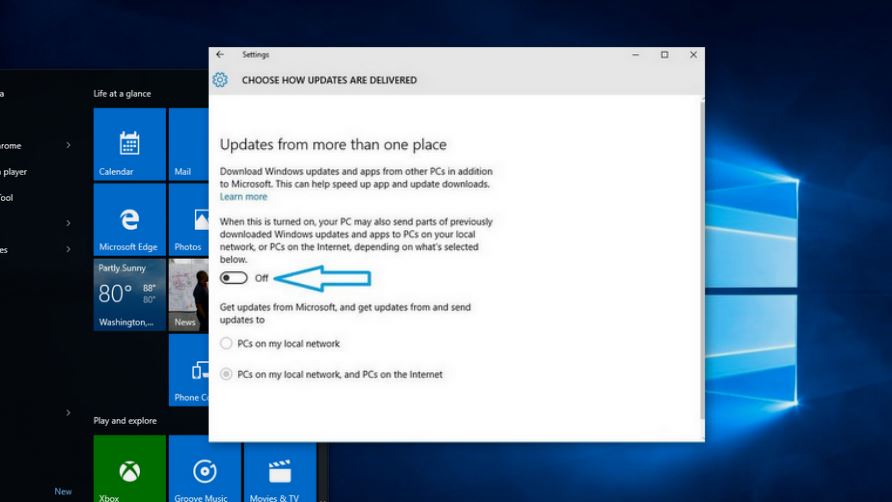
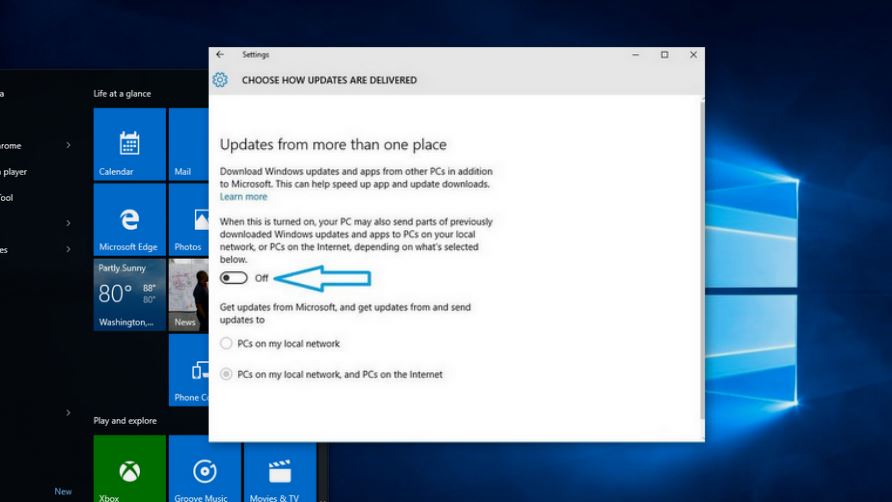 401How To
401How ToWindows 10 Steals Your Internet Bandwidth to Send Updates to Others, Disable It Here
Short Bytes: Windows 10 steals your internet bandwidth without your knowledge to share updates with others. This option is enabled by default...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




