Featured News
-

 259News
259NewsGoogle, Microsoft, Kaspersky Labs, NIC For Morocco Domains Hacked
Who says high-profile websites are unhackable? We just witnessed Moroccan hackers taking over websites of tech giants and those claiming to protect...
-
 215Hacked
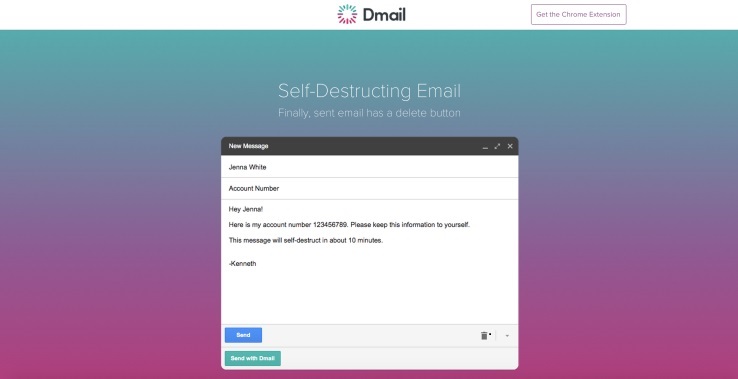
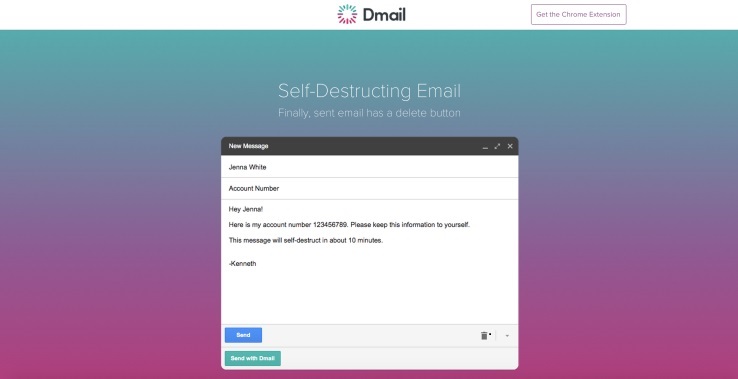
215HackedHow To Self Destruct Email With Dmail
Admit it, you have wanted this for a long time. There must have been instances when you regretted sending an email with...
-

 262Geek
262GeekAnonymous Attacks ISIS Supporters, Spams Twitter Accounts with Anime Pics
The online hacktivist Anonymous has been fighting an online battle against the Islamic State (IS, previously ISIS/ISIL). And now they have just extended their...
-

 478Privacy
478PrivacyResearchers unveil super‑fast anonymity network
A group of six academics have published a paper describing a new high speed anonymity network that could increase the privacy of...
-
 161Geek
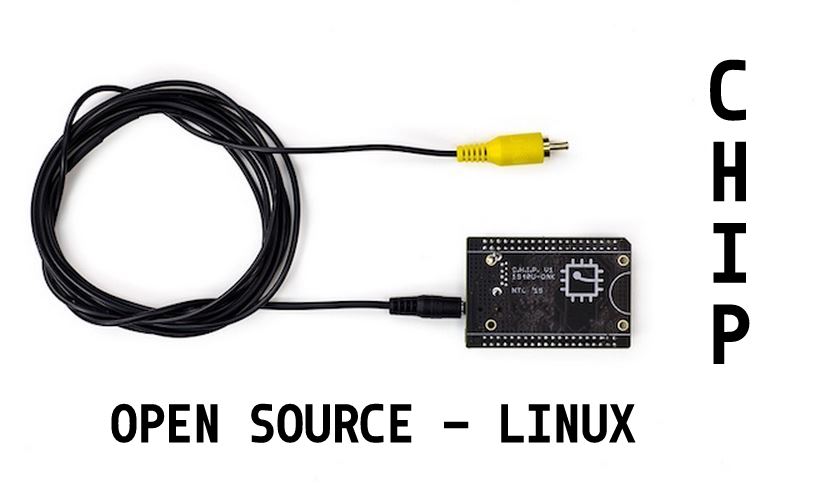
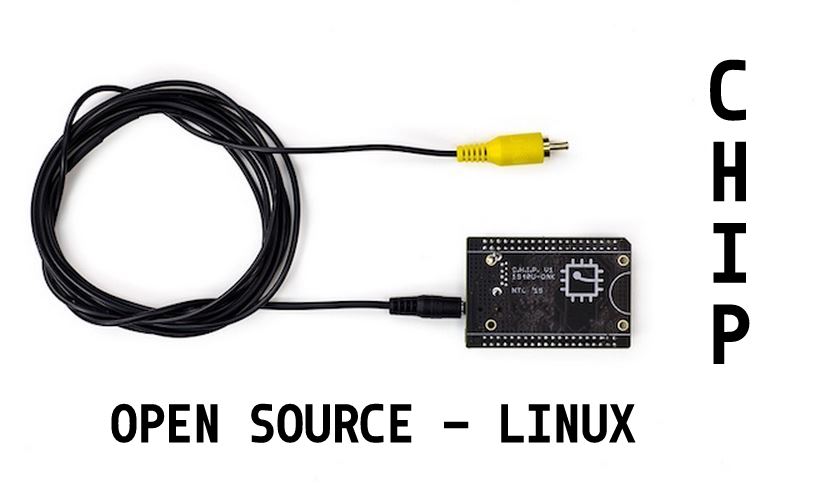
161Geek$9 Computer CHIP Reveals Its Open Source Details, Runs on Linux Kernel
If you are interested in the latest technologies and advancements in computing, you must have read about the $9 computer CHIP. This...
-

 206How To
206How ToHow to Create Your Own Google Deep Dream Nightmares in Seconds
Google’s Deep Dream robot has been creating one hell of a stir in recent weeks and fossBytes isn’t untouched by the same....
-
 322Hacked
322HackedHORNET: Tor-like Anonymity Network With Superfast Speeds
The Deep Web is a place that is hidden from the ordinary world because the browsers used to access the Deep Web, continuously encrypt...
-
 317Operating Systems
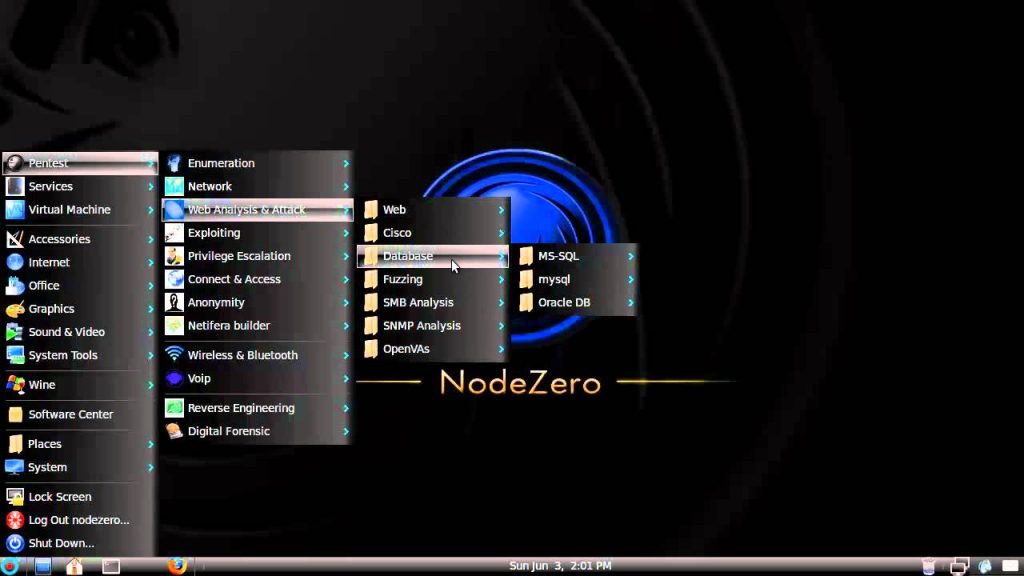
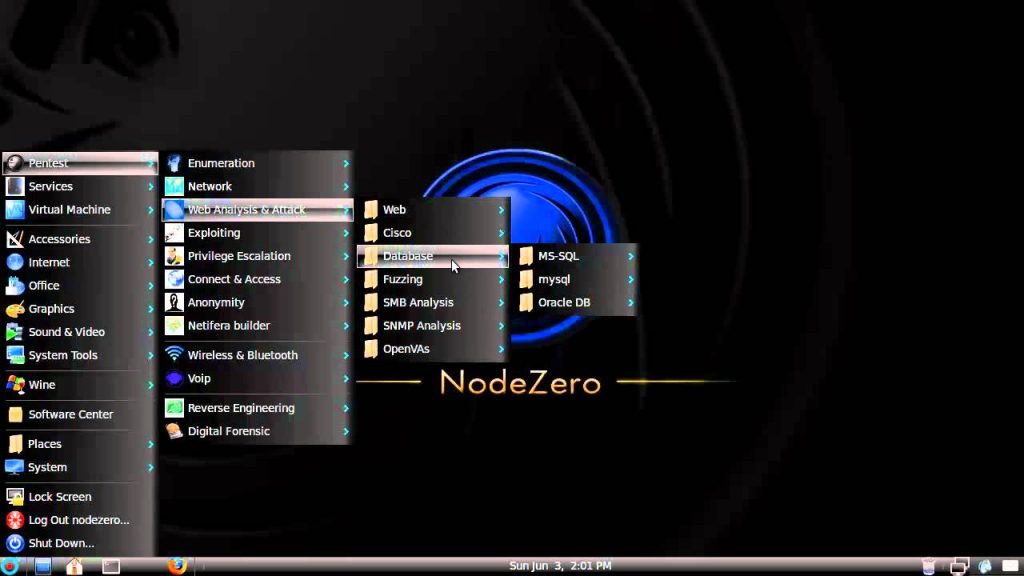
317Operating SystemsNodeZero – Lurking in the shadows of Pentesting
Us penetration testers have of course all heard of BackTrack it’s the most popular penetration testing distro out there but Node Zero...
-
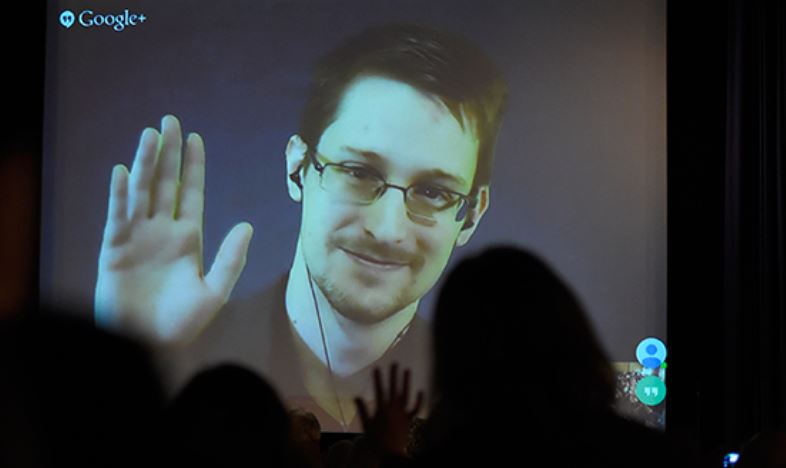
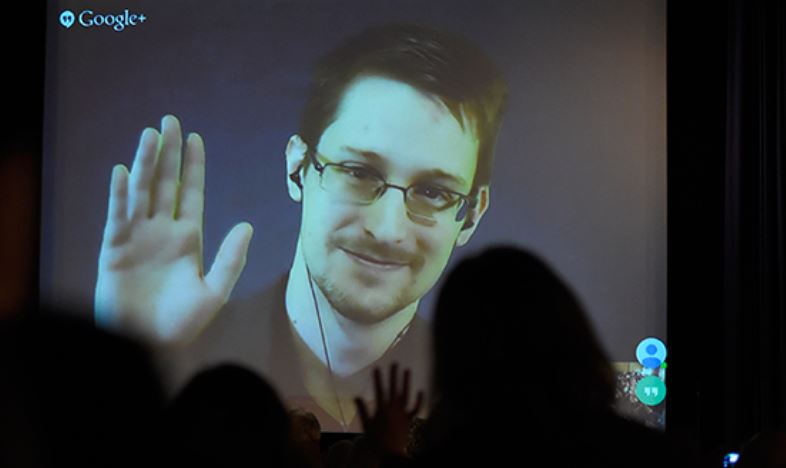 314Hacked
314HackedEdward Snowden Tells How to Build an Internet Focused on Privacy
When someone like Edward Snowden, tells you how to make an internet focused on privacy and user welfare, you listen, and you...
-

 190Cyber Events
190Cyber EventsAnonymous Hacks U.S. Census Bureau, Leaks Officials’ Personal Data Against TPP/TTIP
Remember the Anonymous hackers behind the massive World Trade Center (WTC) leak? Well, he’s back with another breach and this time their...
-

 74Malware
74MalwarePorn clicker keeps infecting apps on Google Play
A recently identified trojan porn clicker is still infecting apps on Google Play.
-
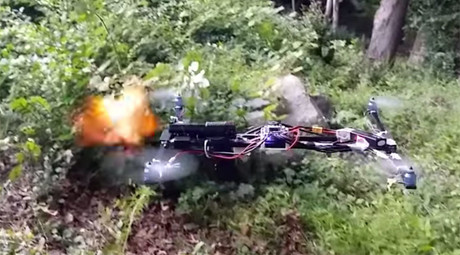
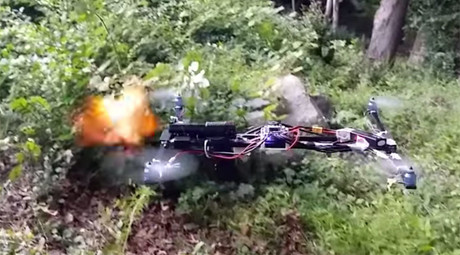 272Hacked
272HackedGun Firing Drone Appears Legal, FAA Still Investigating
Remember the Drone Gun? The quadcopter hovering in the woods of Clinton, Connecticut and firing rounds of shots and completely legal...
-
 431Scams
431ScamsSupport Scammers and Self‑Justification
Support scammers: old twisters, new twists, and scammer psychology.
-

 302Data Security
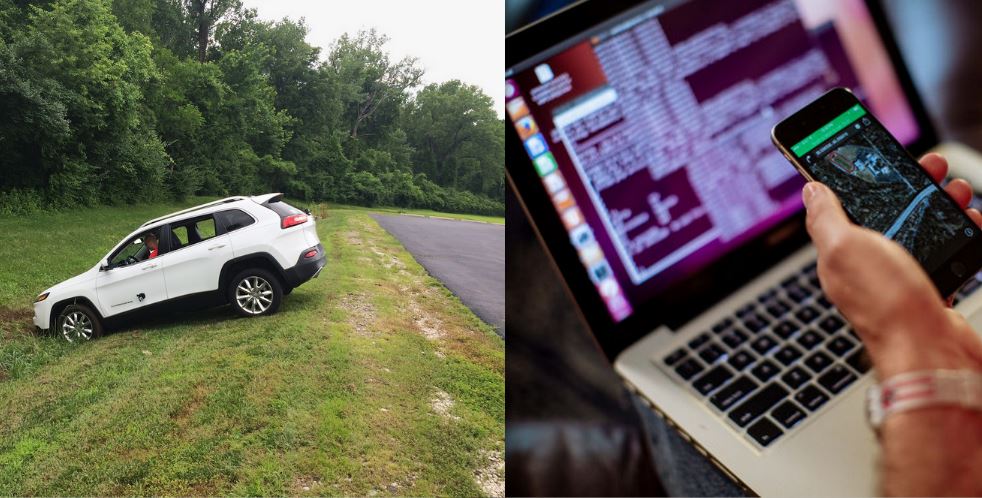
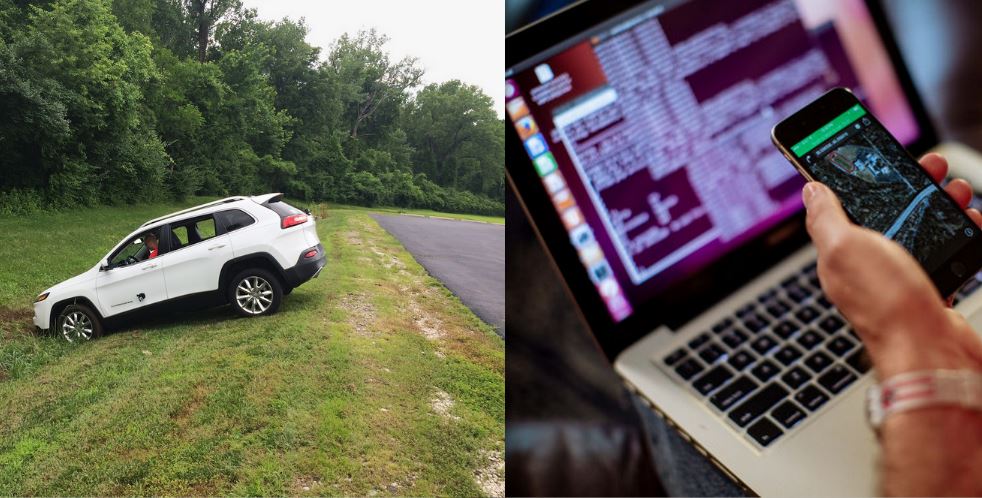
302Data SecurityJeep Cherokee On-Board System Hacked, More Than 470,000 Vehicles at Risk
We have heard about hacking websites, computers, planes, and other devices, but hacking a moving car? Well, it happened and it happened live....
-

 78Cyber Crime
78Cyber CrimeTech giants take action on ad click fraud
Some of the biggest digital companies have banded together to take action on the rising tide of ad click fraud.
-
 183Hacked
183HackedHackers Remotely Hacked This Car Running at 70mph on Highway
As our vehicles become smarter and more dependent on computers, the risk of a car hack automatically increases. Articles titled how to...
-

 100Privacy
100PrivacySmartwatch security ‘lacking’ says HP study
Smartwatch security is noticeably absent in most devices, leaving users at risk of cyberattacks.
-
 182Hacked
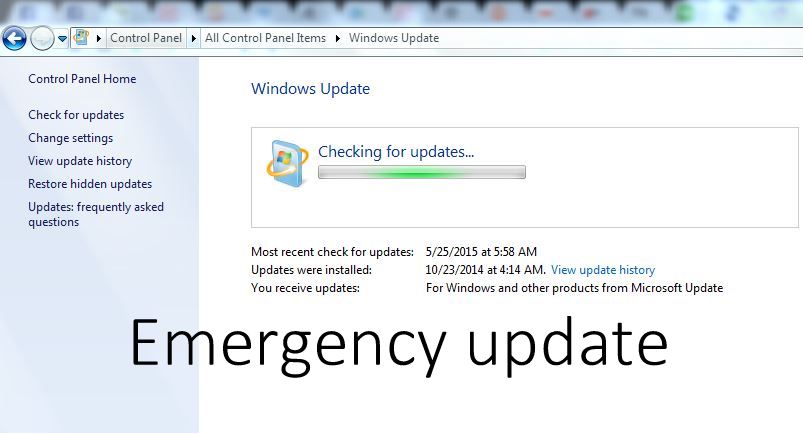
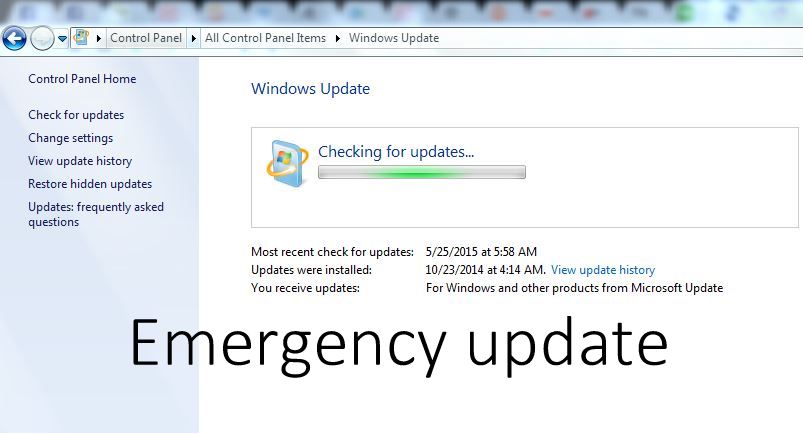
182HackedDownload this Critical Windows Update Now, Flaw Allows Hackers to Control Entire System
A newly discovered vulnerability can allow hackers to remotely execute codes and take over your entire system. A user could be tricked...
-

 214Cyber Events
214Cyber EventsAnonymous Targets Canadian Police, Crashes RCMP’s Website
This week, on July 17th, there was a police-involved shooting in Dawson Creek, British Columbia Canada, where one of the members of...
-
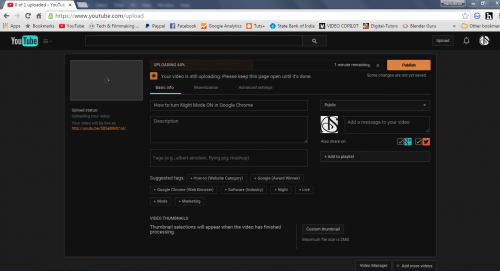
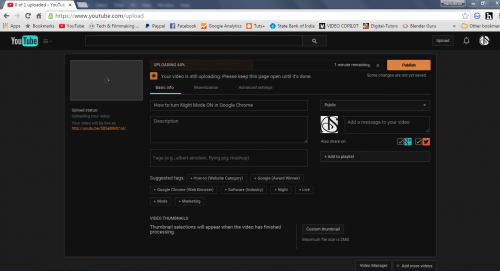 130How To
130How ToHow to turn night mode ON in Google Chrome
Google Chrome is the most used browser on the Internet as it is fast and secure. Google Chrome has many extensions in...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




