Featured News
-
 285Hacked
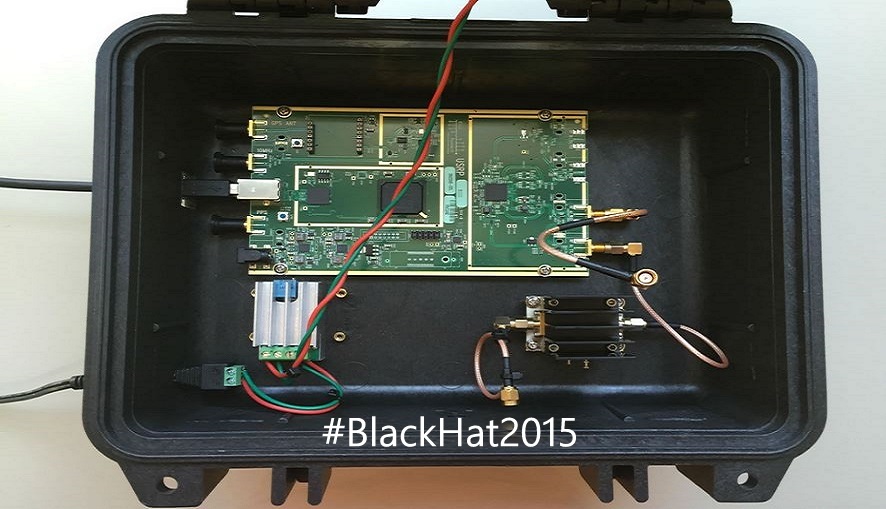
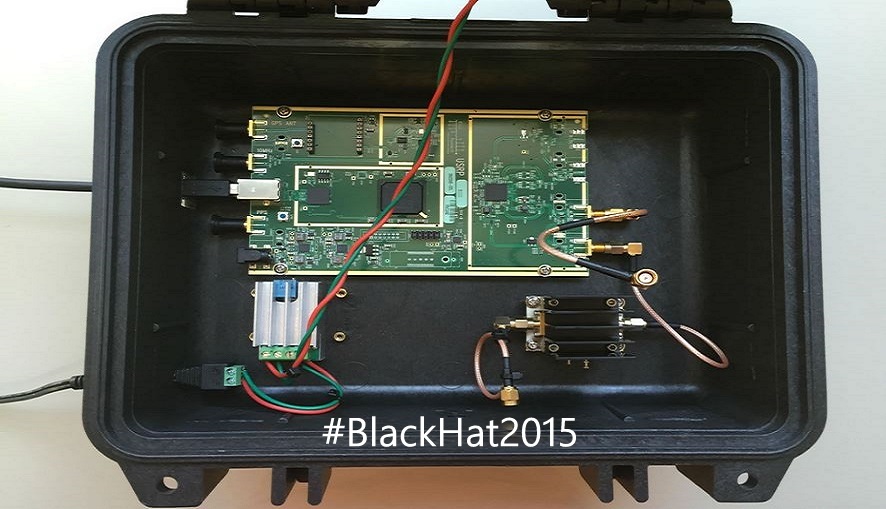
285HackedSatellite Hack: Hackers Can Easily Crack Satellites, Controlling Your Cars and Phones
Short Bytes: Colby Moore, a researcher from cyber security firm Synack, has taught the attendees of Black Hat Conf. something that can...
-

 238Hacking Tutorials
238Hacking TutorialsRunAsDate – Cracking Trial Software
It infuses the predefined date and time to the objective programming in this way preventing it from expiry. Demo variant programming basically...
-

 160Opinion
160OpinionHow’s Black Hat in 2015? It grows up (and leaves mom’s basement)
Blackhat grew! Not only did the hacker types leave their mom’s basement and get jobs, some even were forced to start explaining...
-

 209Cyber Crime
209Cyber CrimeISIS Social Media Recruiters Owned By 3 Chechen Girls
The extremist militant organization the so-called Islamic State (IS, previously ISIS/ISIL) often uses the recruitment tactic of catfishing, which means hiring Western females specifically...
-
 239Privacy
239PrivacyWindows 10, Privacy 0? ESET deep dives into the privacy of Microsoft’s new OS
Windows 10 offers more personalisation and integration than ever before. We take a look at the privacy implications of this.
-

 286Hacked
286HackedBiggest Security Update in History, Google Fixes Android Hijack Bug Stagefright
Short Bytes: This week, Google is releasing the “single largest software update the world has ever seen”. It has started rolling out patches for...
-

 342Hacked
342HackedSound Wave Hacking: Computers and Printers Hacked to Send Data as Sound Waves
Short Bytes: A team of security researchers have successfully demonstrated that the standard equipment inside computers, printers and other devices could be hacked...
-
 213Surveillance
213SurveillanceYour Smartphone and Laptop Battery Invading Your Privacy
A new research conducted by a group of researchers demonstrates how your smartphone and laptop battery can be used to invade your...
-

 245Cyber Events
245Cyber EventsU.S. Based Medical Software Company Breach Expose 4 Million People
The U.S. Department of Health and Human Services reports that earlier this year the records of 3.9 to 4 million people nationwide...
-
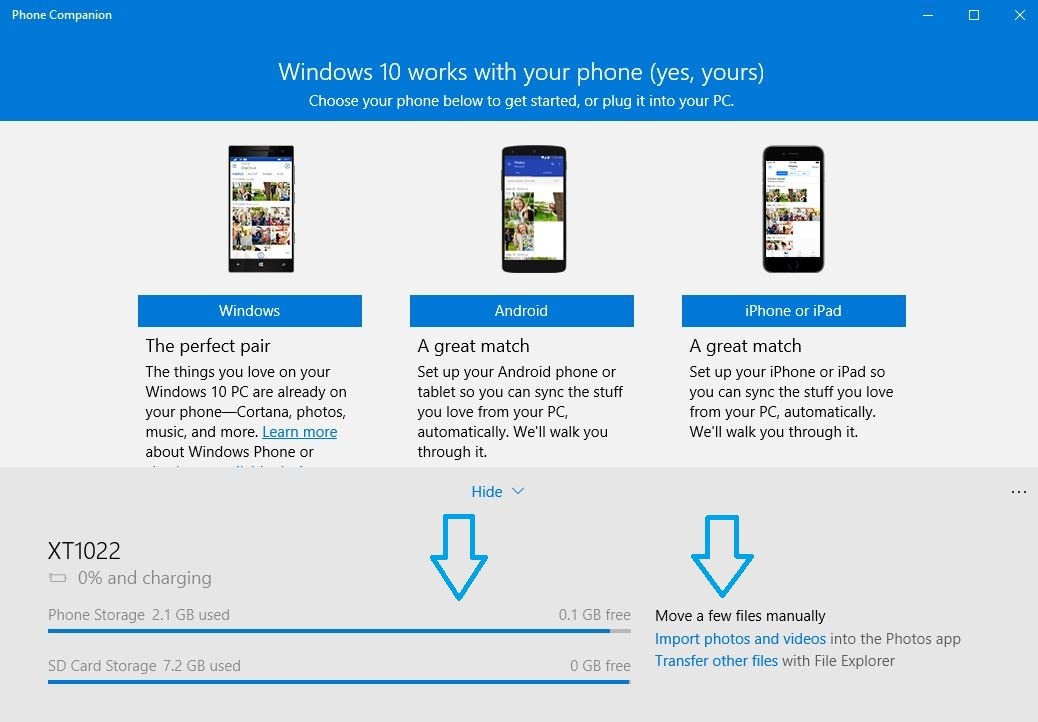
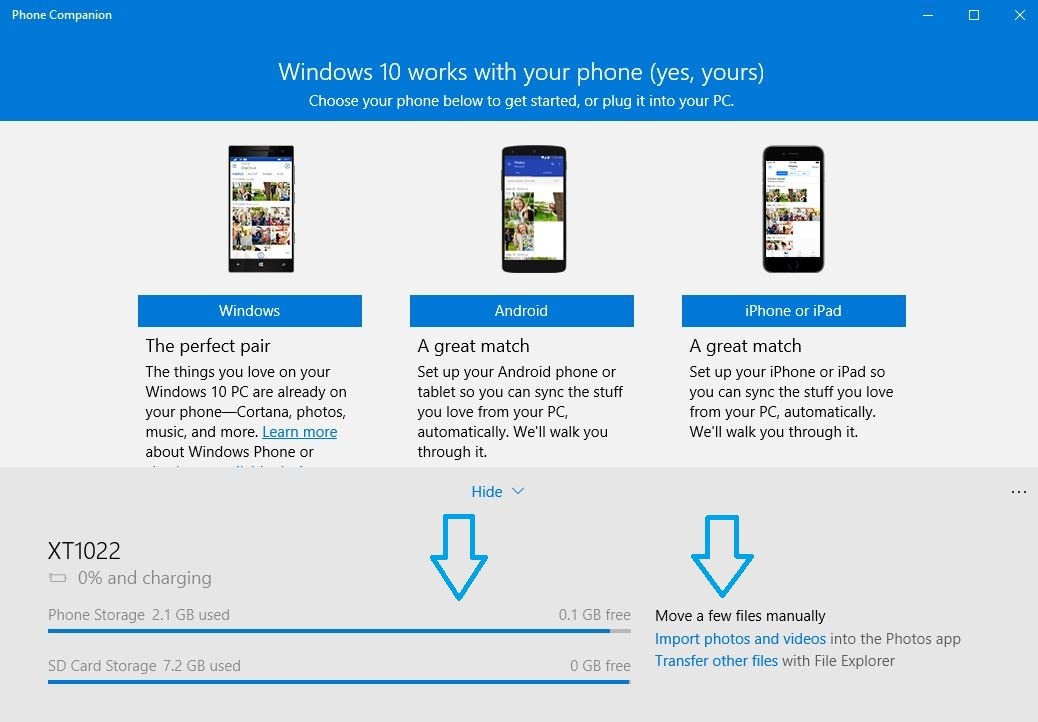 449How To
449How ToHow to Sync Your Android Phone and iPhone With Windows 10
Short Bytes: With Windows 10, there comes a pre-installed app called Windows 10 Phone Companion app. This app helps you to sync...
-

 295How To
295How ToCanonical Tells How to Choose the Best Laptop to Install Linux
Short Bytes: Canonical has released a list of Ubuntu desktop certified hardware to tell you the best laptop to install Linux. Even if...
-

 325Data Security
325Data SecurityElectronic Skateboards Are Easy To Hack
As we are approaching the much-awaited hacking conferences DefCon and Black Hat, security researchers and engineers are revealing their studies and exploits...
-
 258Data Security
258Data SecurityMiddle East’s Largest Classified Website Dubizzle Suffers Security Breach
Dubizzle, the popular Middle Eastern online classifieds for bargain hunters, sellers and job seekers has had its UAE servers compromised – albeit...
-

 76Malware
76MalwareTerracotta VPN network helps hackers remain anonymous
Hackers are using a commercially available VPN network in China to obscure the origin source of their activities.
-

 207Interview
207InterviewLightbulb moment: Why the Internet of Things is a security watershed
Senior research fellow Righard J. Zwienenberg on why the Internet of Things could be *the* key security issue for the foreseeable future.
-
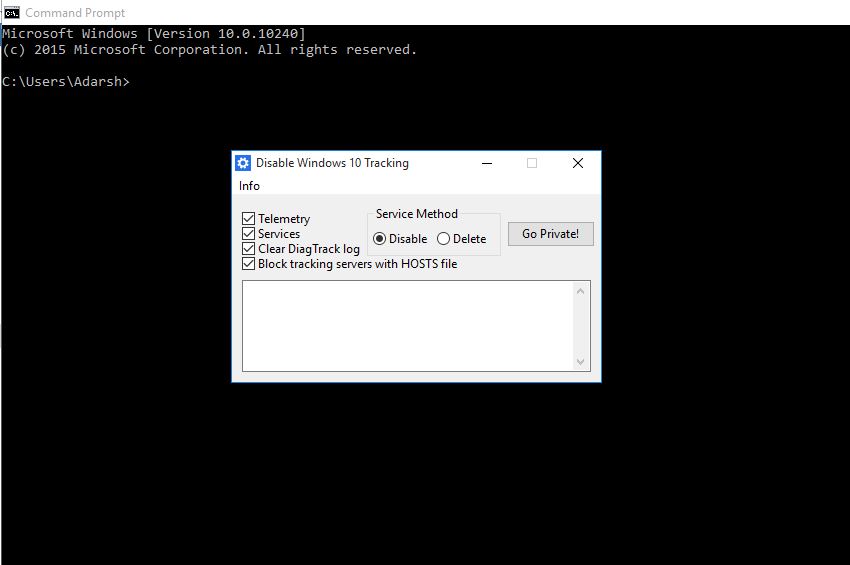
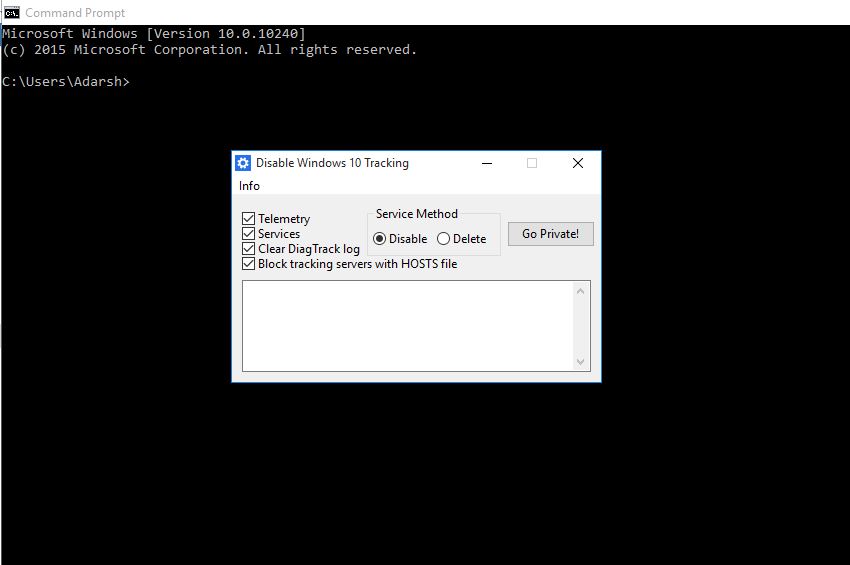 175Hacked
175HackedThis Open-source App Wants to Stop Windows 10 From Tracking You
Short Bytes: A developer has released an open-source tool called Disable Windows 10 Tracking to address your Windows 10 privacy concerns. This tool,...
-

 321Data Security
321Data SecurityYahoo Ad Network Hacked, Infecting Millions of Devices with Malware, Ransomware
Yahoo ad network has been exploited by a group of hackers that resulted in a serving of malware and ransomware adverts on...
-

 238News
238NewsSri Lankan Prime Minister’s Office Website Hacked
The Sri Lankan prime minister Ranil Wickremesinghe has his office website hacked by a hacktivist who hacks for #ForSyria. A hacker going with...
-
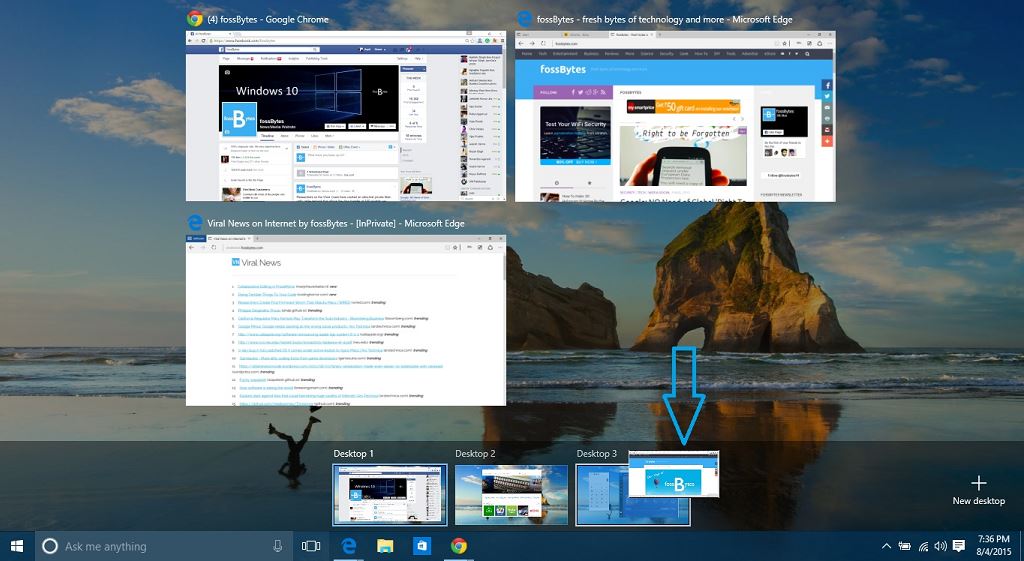
 301How To
301How ToHow to Create and Use Virtual Desktops in Windows 10?
Short Bytes: Realizing the popularity of Virtual Desktops and needs of a power user, Microsoft has finally integrated this service in Windows...
-

 317News
317NewsDonald Trump’s Website Hacked with Jon Stewart Tribute
Donald Trump organization’s official website Trump.com was attacked by hackers yesterday and a message was posted in which Jon Stewart was praised...
The Latest
-
 Vulnerabilities
VulnerabilitiesFoxit PDF Reader Flaw Exploited by Hackers to Deliver Diverse Malware Arsenal
-
 Vulnerabilities
VulnerabilitiesDefending Your Commits From Known CVEs With GitGuardian SCA And Git Hooks
-
 Malware
MalwareCyber Criminals Exploit GitHub and FileZilla to Deliver Malware Cocktail
-
 Malware
MalwareLatrodectus Malware Loader Emerges as IcedID’s Successor in Phishing Campaigns
-
 Malware
MalwareGrandoreiro Banking Trojan Resurfaces, Targeting Over 1,500 Banks Worldwide
-
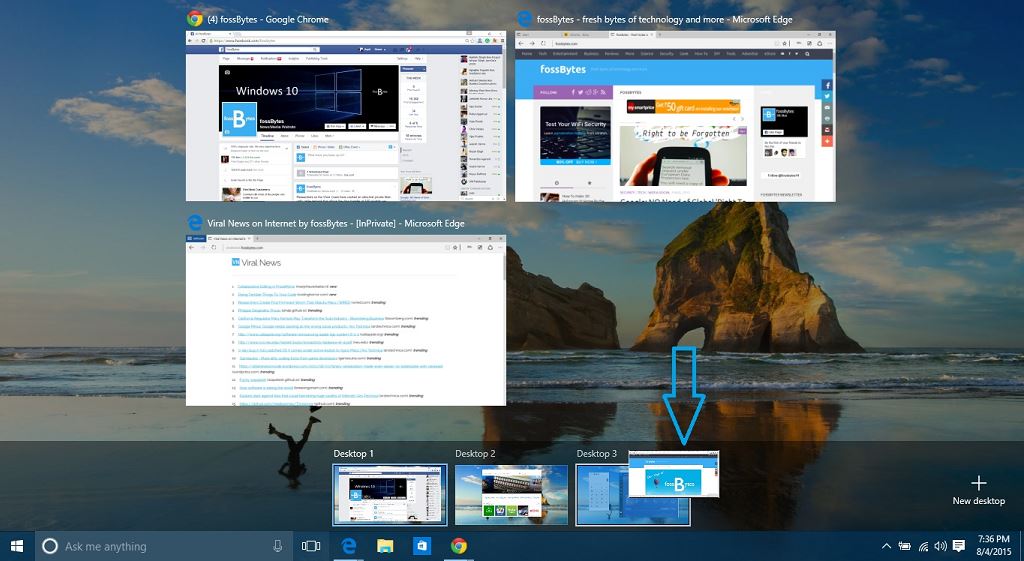
 Malware
MalwareKinsing Hacker Group Exploits More Flaws to Expand Botnet for Cryptojacking
-
 Malware
MalwareChina-Linked Hackers Adopt Two-Stage Infection Tactic to Deploy Deuterbear RAT
-
 Malware
MalwareKimsuky APT Deploying Linux Backdoor Gomir in South Korean Cyber Attacks
-
 Vulnerabilities
VulnerabilitiesNew Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
-
 Malware
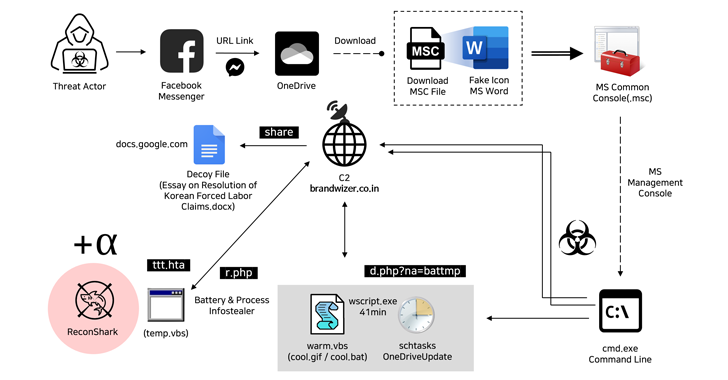
MalwareNorth Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
-
 Malware
MalwareCybercriminals Exploiting Microsoft’s Quick Assist Feature in Ransomware Attacks
-
 Vulnerabilities
VulnerabilitiesGoogle Patches Yet Another Actively Exploited Chrome Zero-Day Vulnerability
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Malware
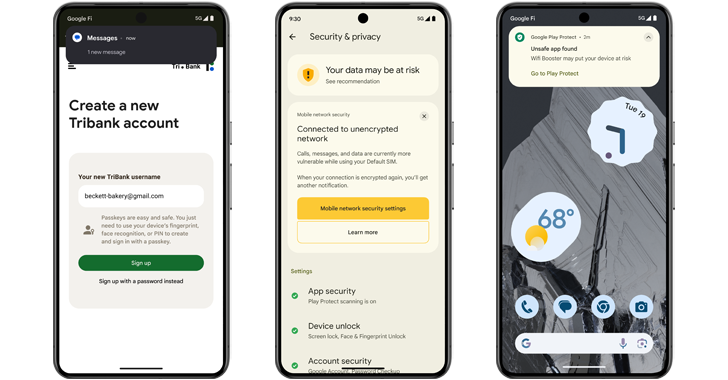
MalwareAndroid 15 Rolls Out Advanced Features to Protect Users from Scams and Malicious Apps
-
 Malware
MalwareTurla Group Deploys LunarWeb and LunarMail Backdoors in Diplomatic Missions
-
 Vulnerabilities
Vulnerabilities(Cyber) Risk = Probability of Occurrence x Damage
-
 Malware
MalwareEbury Botnet Malware Compromises 400,000 Linux Servers Over Past 14 Years
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Vulnerabilities
VulnerabilitiesVMware Patches Severe Security Flaws in Workstation and Fusion Products
-
 Vulnerabilities
VulnerabilitiesNew Chrome Zero-Day Vulnerability CVE-2024-4761 Under Active Exploitation




