Featured News
-

 120Opinion
120OpinionThe ABC of information security
There are three fundamental elements that must not be overlooked when starting out in corporate security, summarized as the 'ABC of information...
-

 224How To
224How ToDeveloper Makes Tool to Play GTA V in Any Web Browser
Short Bytes: A developer has developed a program called jsmped-vnc. If your PC isn’t powerful enough to run GTA V, you can...
-
 279How To
279How ToHow to Get Windows 10 at the Lowest Price
Short Bytes : Many of you would be wondering- why I’m writing this “how to get Windows 10 at the lowest price”...
-

 270Data Security
270Data SecurityPakistan to Shut Down BlackBerry Services Amid Security Concerns
Pakistan Telecommunication Authority has ordered the local cellular operators to completely shut down Canadian smartphone maker’s BlackBerry Enterprise Services (BES) by the...
-

 384Lists
384ListsEverything You Need to Know About Windows 10 Upgrade – FAQs
Short Bytes: Now, Windows 10 is launched and Microsoft is convincing as much as users to take the advantage of its free Windows...
-

 80Cyber Crime
80Cyber CrimeValve Steam bug sees accounts hacked
A serious bug in Valve’s Steam engine has allowed a series of user credentials to be stolen over the past week, according...
-

 101Privacy
101PrivacyAccidental pocket dials can be used in evidence, says US court
Accidental ‘pocket dials’ are now admissible in evidence against you, the US Appeals court has ruled.
-

 74Cyber Crime
74Cyber CrimeCybercrime update: take downs, arrests, convictions, and sentences
Information security could use some good news right now, something to offset the string of bad news about data breaches and system...
-
 190Geek
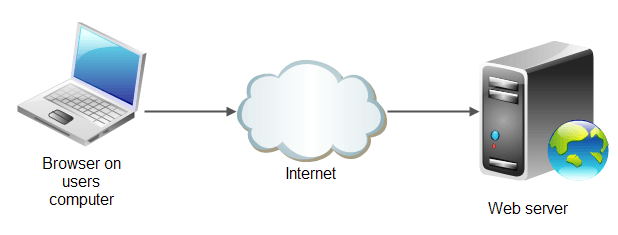
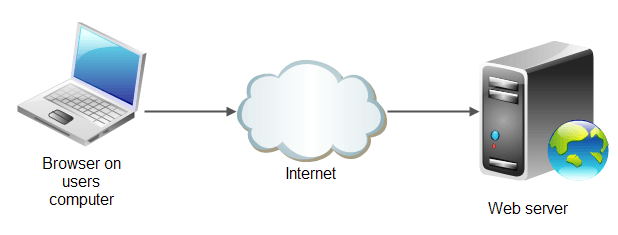
190Geekrwasa High Performance Web Server Claiming to be Better than nginx and lighttpd
2 Ton Digital – a company which provides products, services and support for any company or individual that is interested in security, network...
-

 278Geek
278GeekTop Airbnb Open Source Projects You Must Know
This is the 4th post in the series covering top open source projects by most popular companies in the world. Today, we...
-
 182Hacked
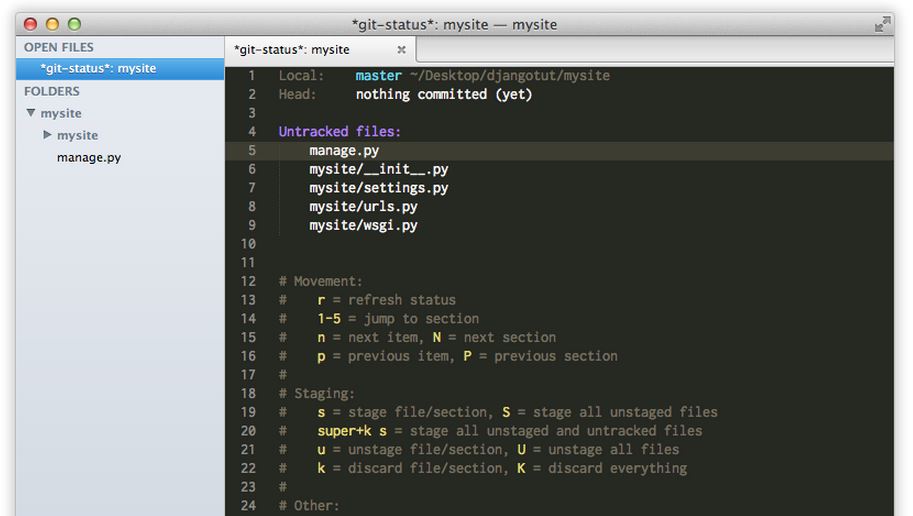
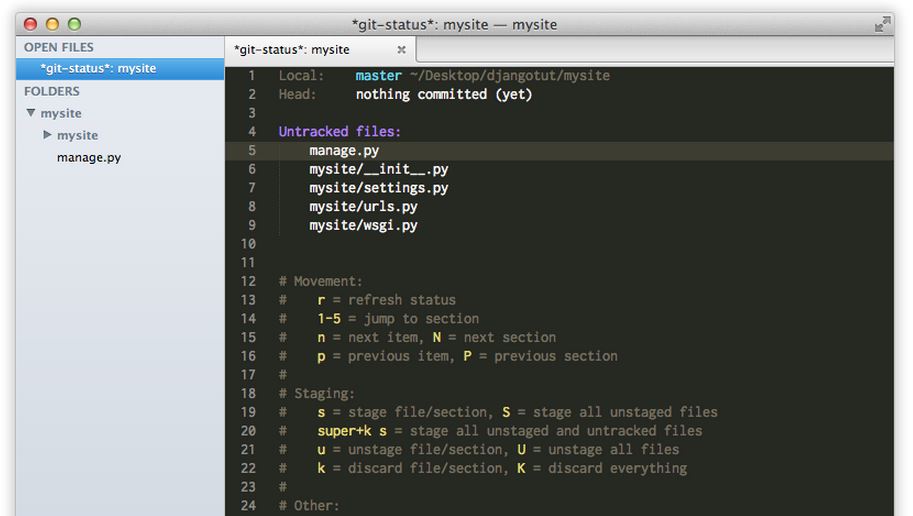
182HackedOne in Every 600 Websites Has .git Exposed, How to Check Yours and Hide It
Recently, I read about an innocent mistake committed often by web developers and thought it’d be nice to share it on fossBytes....
-

 204Surveillance
204SurveillanceHere’s A Mobile Spy App That Fulfills All Your Monitoring Needs
Mobile spy apps are available at the handful, but you don’t need them that way at all, one good spy app would...
-
 253How To
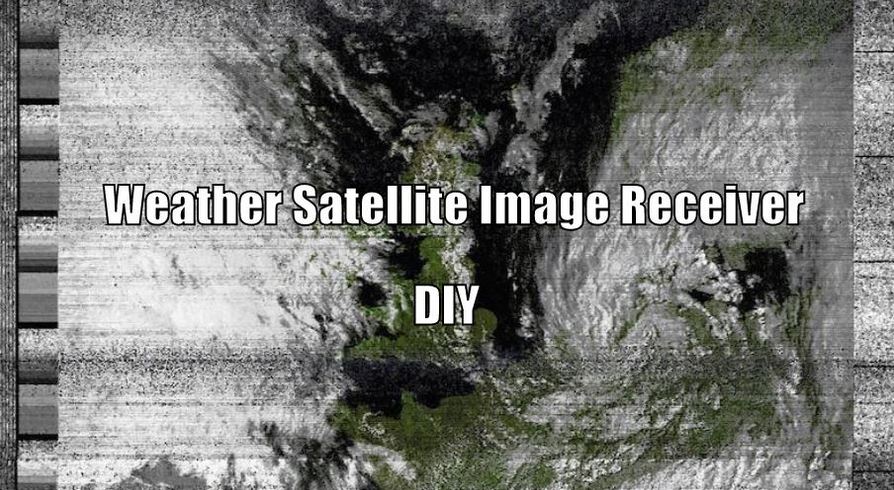
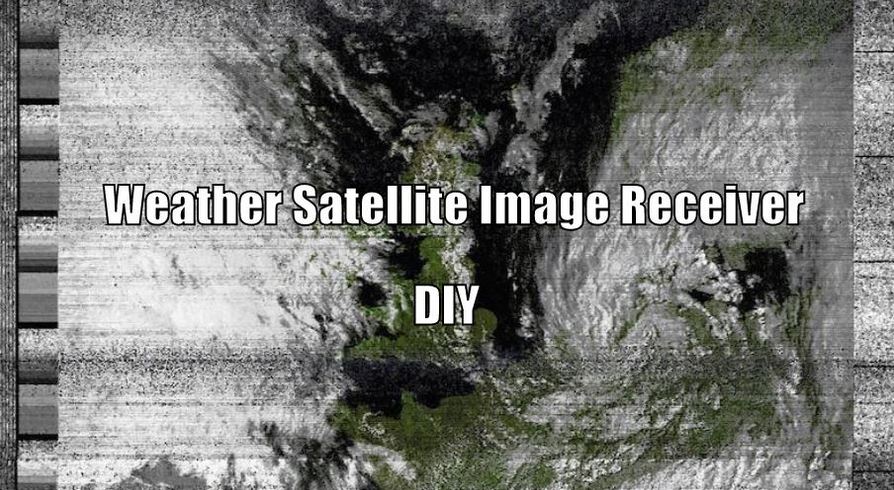
253How ToHow to Build Weather Satellite Images Receiver With $20 Dongle
This “how-to build weather satellite images reciever” is based upon Matt Gray’s project on receiving weather satellite image with £8 dongle. Matt Gray is...
-

 274Hacked
274HackedGoogle Tells You How To Stay Safe Online
When most of your Facebook timeline is flooded with news like cyber threats and security, how cyber criminals steal your money, and...
-

 271Surveillance
271SurveillanceHORNET – Faster and Secure Anonymity Network Than Tor
Most of you must have heard about Tor, which is one of the renowned network based on onion router, delivers a good...
-

 179Hacked
179Hacked500 Million Devices at Risk Due to Leaked “Easy to Use” RCSAndroid Malware
The massive data breach at the Hacking Team has resulted in tons of revelations regarding different kinds of spyware and the potential security...
-

 283Surveillance
283SurveillancePakistan’s ISI Plans to Tap International Undersea Cables, Rivals the NSA, GCHQ
The most powerful intelligence and spy agency of Pakistan, specifically Inter-Services Intelligence (ISI), has now planned to tap all the Internet traffic...
-
 312Hacked
312HackedMovie Studios Repeatedly Report Their Own 127.0.0.1 Localhost for Piracy
The torrent pirates that keep hurting the million-dollar movie studios by uploading the data using their torrent clients are their biggest enemies...
-

 264News
264NewsGoogle, Microsoft, Kaspersky Labs, NIC For Morocco Domains Hacked
Who says high-profile websites are unhackable? We just witnessed Moroccan hackers taking over websites of tech giants and those claiming to protect...
-
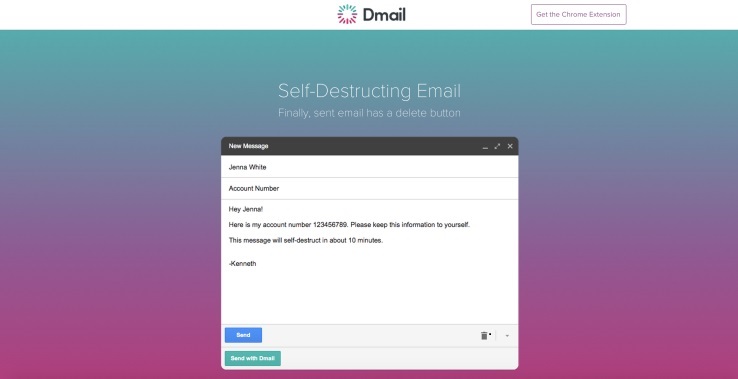
 219Hacked
219HackedHow To Self Destruct Email With Dmail
Admit it, you have wanted this for a long time. There must have been instances when you regretted sending an email with...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




