Featured News
-

 276Data Security
276Data SecurityComputer Controlled Sniper Rifle Hacked, 1000 Rifles Left Vulnerable
Recently we reported that some security researchers managed to hack into the Jeep’s onboard entertainment system to remotely take over the vehicle’s...
-
 322Hacked
322HackedWhat is Traffic Fingerprinting and How it is Used to Attack Tor Network
Short Bytes: Traffic fingerprinting is a technique used to sniff the web traffic by analyzing the data packets’ flow pattern- without removing...
-

 207Cyber Crime
207Cyber CrimeUnited Airlines customer flight records breached
United Airlines customer flight records have been lost in a data breach it has been reported.
-

 274News
274NewsUnited Airlines Hacked by Same Chinese Group Behind The OPM Breach
From cars to trains from computers to planes, anything connected with the Internet is vulnerable to cyber attacks. It is believed that a...
-

 165Hacked
165HackedHackers Can Hack Smart Sniper Rifles Running on Linux And Change Its Target
Images: Wired Short Bytes : Security researchers have found a way to hack the Tracking Point sniper rifles. These “smart” snipers run...
-

 279Hacked
279HackedExperts Explain The Car Hack Process – How to Hack a Car
Short Bytes : The recent Fiat Chrysler car hack exposed the vulnerabilities and the extent to which insecure IoT can be dangerous....
-

 368How To
368How ToHow to Regain Up To 20GB Disk Space After Windows 10 Upgrade?
If you have got the latest Windows 10 upgrade, you will notice about 15-20GB space missing from your disk drive. These files...
-

 379How To
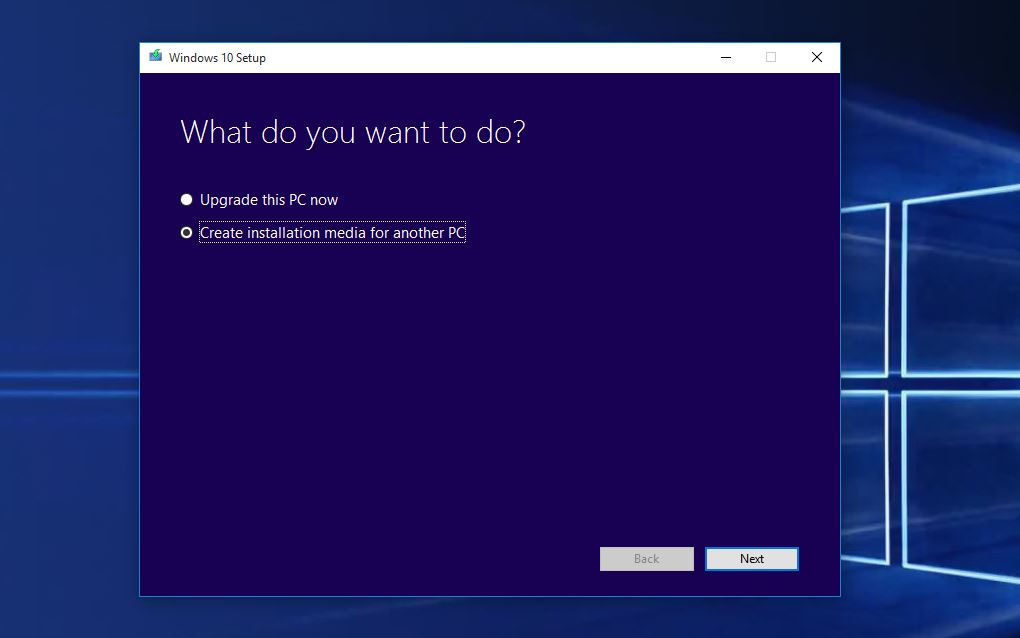
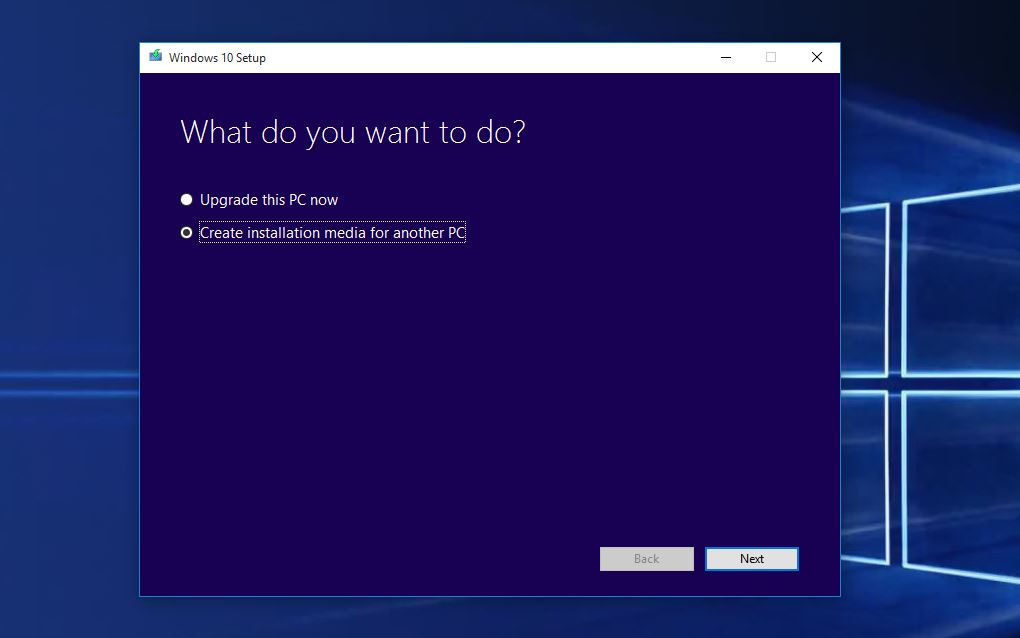
379How ToHow to Install Windows 10 Without Windows Update
Short Bytes: After rolling out the Windows 10 upgrade, Microsoft has released Windows 10 ISO files. If you don’t want to go...
-

 217News
217NewsGoogle, MSN Domains for Pitcairn Islands Hacked By Bangladeshi Hackers
On July 25, 2015, we reported how a group of Morrocan hackers hacked and defaced the official domains of Google, Microsoft and...
-
 276Geek
276GeekLinux Based Solus OS Now Boots in Flat 1.2 Seconds
Short Bytes : The developer team behind Linux-based Solus distro has achieved a remarkable feat as they brought down the boot time...
-

 184Hacked
184Hacked5 Best Free Android Antivirus Apps of 2015
Short Bytes : Your smartphone is at the equal risk of getting infected by malware as is your computer. Hers’s a list...
-

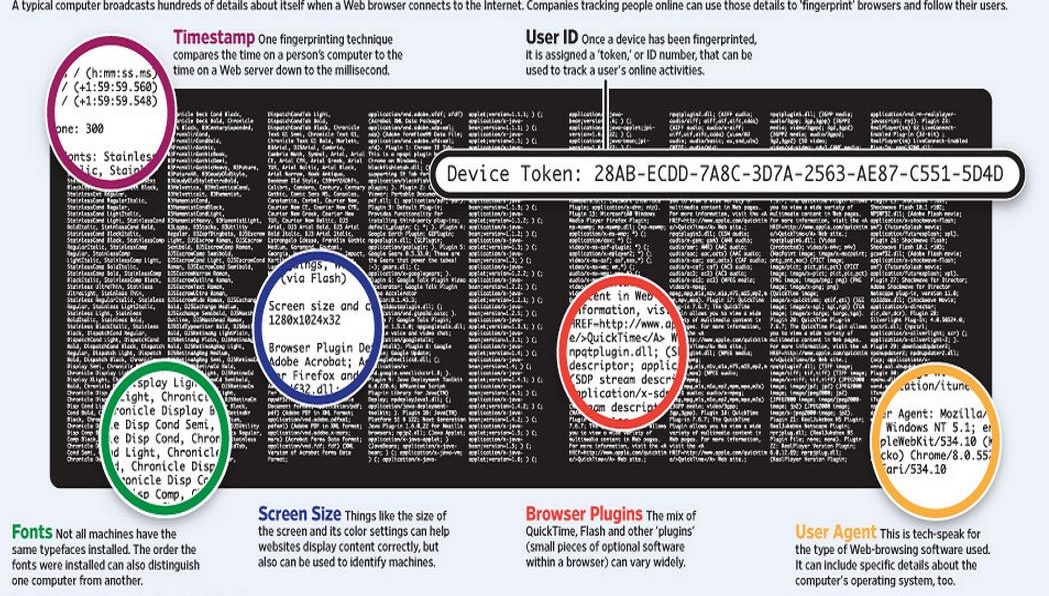
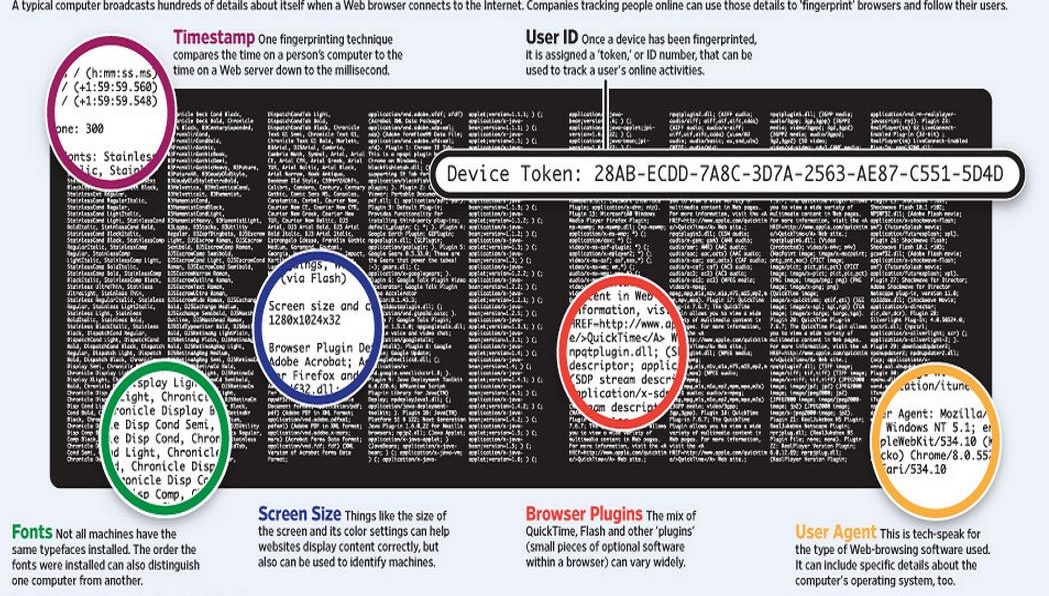
 208Privacy
208Privacy‘Keystroke Biometrics’ exploit defeats Tor privacy
Security researchers have created a practical privacy attack out of a well-known theory around user behaviour. The attack appears to defeat privacy...
-
 343How To
343How ToHow To Perform A Clean Windows 10 Installation Using ISO Files
Short Bytes: Microsoft has released Windows 10 ISO files for performing a clean install on your PCs after the Windows 10 upgrade....
-

 108Cyber Crime
108Cyber CrimeMoonpig warns of password breach – but it may be more than their users who are at risk
Moonpig, the online personalised card company, has blocked the accounts of an unspecified number of customers after users' details were published online.
-

 110How To
110How ToHow to shop online safely during the summer sales
The summer sales are upon us and there are plenty of good deals to be had online, but internet shopping is not...
-

 319How To
319How ToHow to Get the Windows 10 Upgrade – The Upgrade Guide
Short Bytes: Microsoft has released its best OS ever and it looks like “back to the future” of Windows. Realizing the mistake...
-
 335Hacked
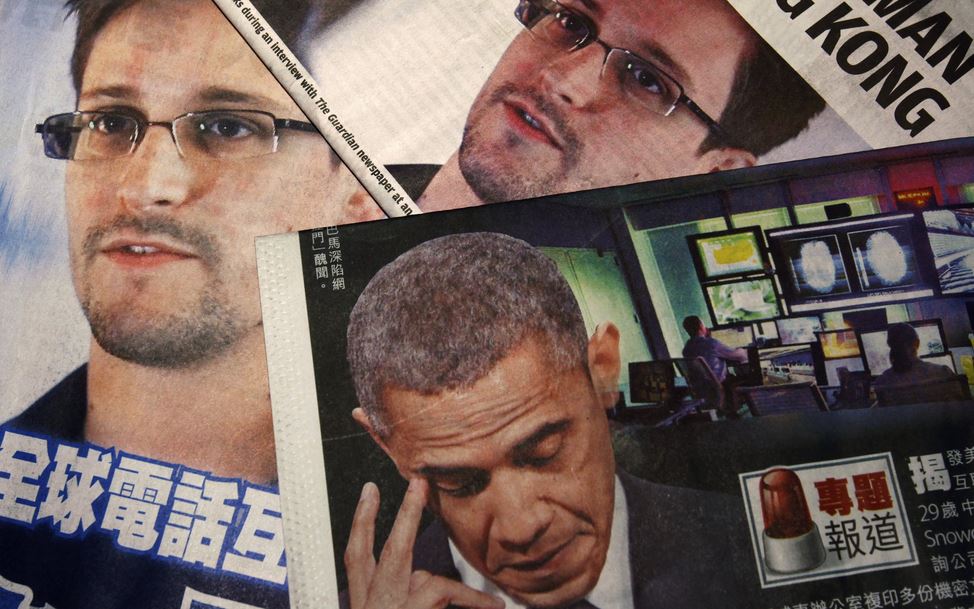
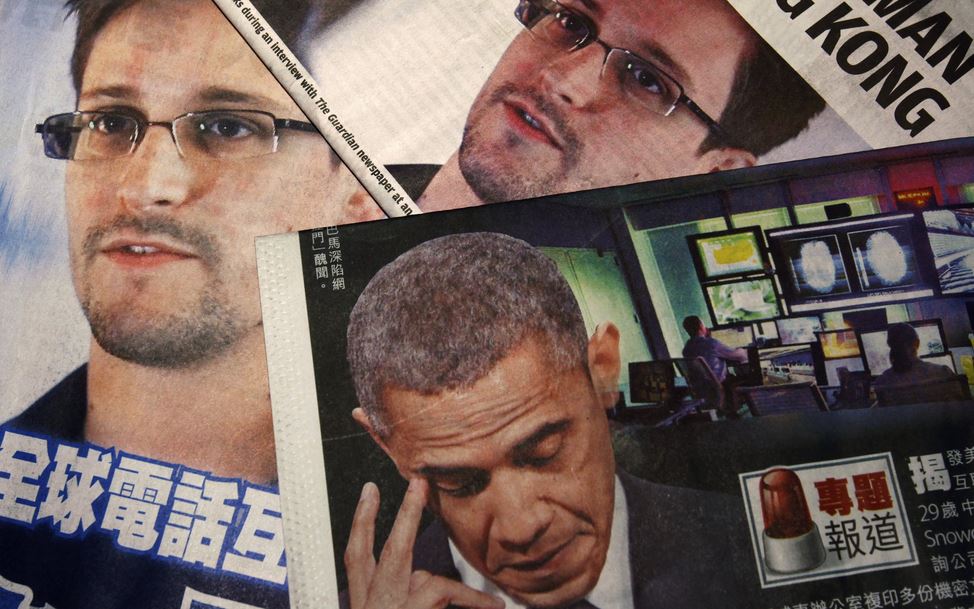
335HackedU.S. Government Wants to Send Edward Snowden to Prison, Rejects Pardon Request
(Credit: Reuters/Bobby Yip) Short Bytes : The White House has rejected a petition with more than 167,000 signatures to pardon whistleblower Edward...
-

 277News
277NewsPlanned Parenthood Servers Hacked by Anti-Abortionist Hackers
The servers of Planned Parenthood, the non-profit reproductive health care organization, has recently been hacked by anti-abortionist hacker group. While the compromised...
-
 297Geek
297GeekAndroid Stagefright Bug Is Critical, Let Hackers Snoop into Your Phone Silently
Are you an Android phone user? Please pay attention as now it only takes one text message to hack an Android phone....
-

 386Password
386PasswordNew report explains gulf between security experts and non‑experts
Security experts and non security experts take very different attitudes to staying safe online, according to new research.
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




