Featured News
-

 66Cyber Crime
66Cyber CrimeMillions of records lost in huge OPM US data breach
The US Office of Personnel Management has admitted that the widely-publicised data breach in June was more wide-reaching than at first thought.
-

 179Malware
179MalwareSednit APT Group Meets Hacking Team
The infamous Sednit espionage group is currently using the Hacking Team exploits disclosed earlier this week to target eastern European institutions.
-

 203Geek
203GeekComputer Program ‘Helium’ Fixes Old and Rotten Code Faster than Expert Engineers
Do you know the meaning of term software rot or bit-rot? It’s the gradual deterioration in the performance of a software and...
-

 262News
262NewsNew York City Comptroller Office Website Hacked by Pro-Palestinian Hacker
Hackers have a passion for hacking, but the way they choose their targets is something hard to understand. Just like this unpredictable hack we...
-

 278Hacked
278HackedCongrats Hacking Team: After Governments, Now Terrorists Have Your Tools
This Sunday, in a massive data breach at the Hacking Team, about 400GB of internal documents, spyware source codes, and tools were...
-
 145Cyber Crime
145Cyber Crime“Internet Capacity Warning” Phishing Scam Aims to Steal Your Login Details
Let’s Welcome the New and Upcoming Phishing Scam —“Internet Capacity Warning.” Internet users are receiving an email that claims to be sent...
-

 82Cyber Crime
82Cyber CrimeAspiring singer jailed for hacking Madonna and stealing unreleased tracks
Breaking into the music business is one thing. Breaking into Madonna's computer without permission is quite another.
-

 292Cyber Events
292Cyber EventsAnonymous is Relatively Much Bigger Than You Anticipated
The global Anonymous network is relatively much bigger than your actual anticipation, a recent visual analysis by a University of Copenhagen graduate...
-

 162Data Security
162Data SecurityWas Anonymous Behind NYSE Glitch? They predicted it a Day Before
The mysterious message Tweeted by Anonymous, the widely known hacktivist group, has left many wondering whether they were behind the cyberattack on NYSE,...
-

 98Malware
98MalwareAdobe rushes to patch Flash flaw under attack
Adobe Systems has issued a sizeable security update with patches for 36 vulnerabilities, at least one of which is currently under attack...
-

 91Malware
91MalwareApps on Google Play Steal Facebook Credentials
Over 500,000 Android users targeted by phishing apps harvesting their Facebook credentials. ESET detects these trojans as Android/Spy.Feabme.A.
-

 364Hacked
364HackedTor Honeypot: How to Hack True Identity of Tor Users
Tor is a free software that is widely used by people to protect their identity and avoid network surveillance. The Onion Router...
-

 307Data Security
307Data SecurityTerrorists Can Use Our Leaked RCS Spyware, Hacking Team Says
The infamous spyware dealer, Hacking Team, has now begun to complain that their recently leaked Remote Control System (RCS) spyware tool which...
-
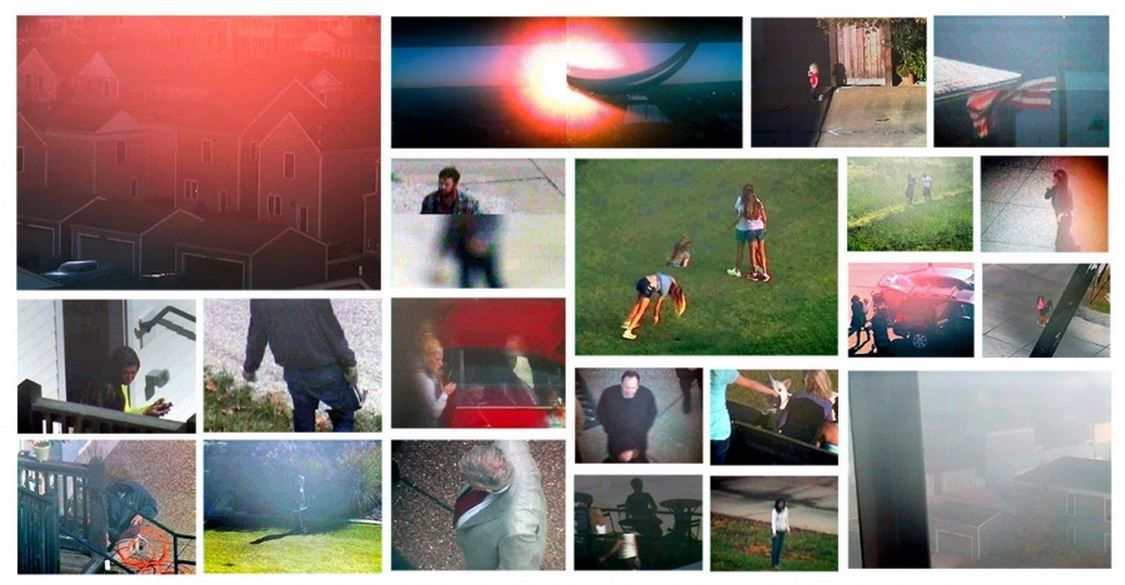
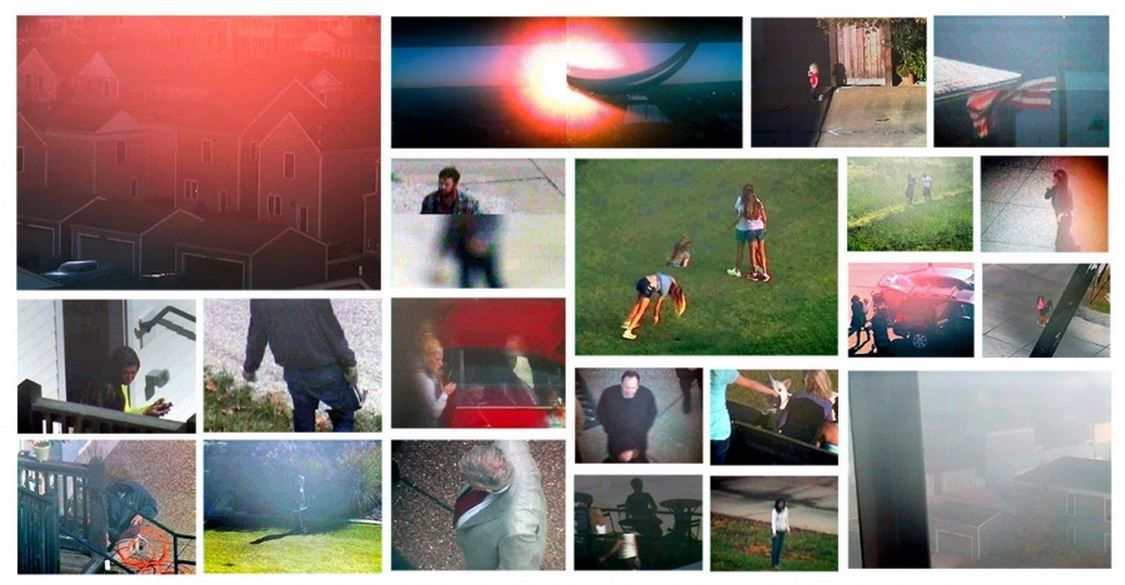 165Hacked
165HackedArtist Hacks Surveillance Cameras to Spy on Town and Makes Photo Album
The New Town photographs by Andrew Hammerand According to a report by IHS, there were 245 million surveillance cameras operating globally in...
-
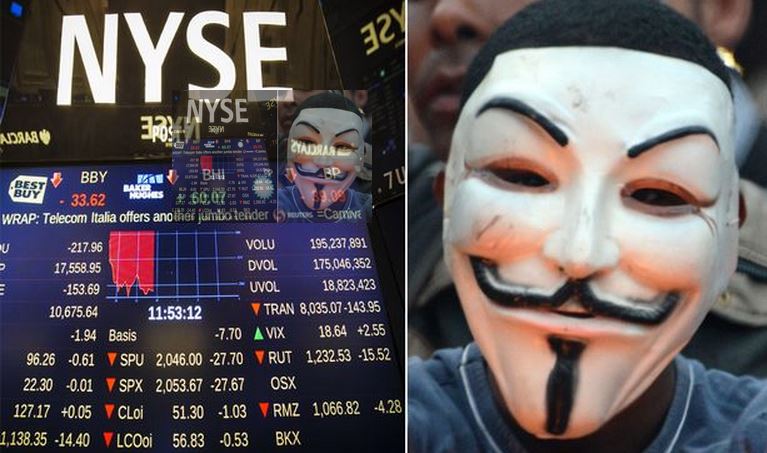
 197Hacked
197HackedDid Anonymous Hack New York Stock Exchange?
When you have the power of anonymity, you can do things that are unimaginable for others. The hacktivist group Anonymous is well-known...
-

 182Cyber Crime
182Cyber CrimeGoogle Docs Users Targeted with “Confidential Document” Phishing Scam
The purpose of this scam message is to steal Google Account Login credentials. Users are urged to click on a fake link...
-

 279News
279NewsSubdomain of U.S. Dept. of Energy’s Argonne National Lab Hacked by ISIS Hackers
Did you notice the pro-ISIS hackers are targeting high-profile websites without any restriction? Yesterday, we exclusively reported how the State Ministry for Euro-Atlantic...
-
 385How To
385How ToHow To Prevent Your Computer From Overheating
An overheating computer spells trouble. You would want your girlfriend to be smoking hot but trust me, neither you want your computer...
-
 323Data Security
323Data SecurityKovter AdFraud Malware Updates Flash Plugin to Latest Version
We all know that one of the basic procedures to keep our computer system secure and free from viruses and malware is...
-

 221Hacked
221HackedKali Linux 2.0 Release Day Scheduled: Kali Sana Coming, Powerful Than Ever
Ever since its debut in the year 2013, Kali Linux users were waiting for a new and revamped version of the hack-friendly...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets




