Featured News
-

 347Hacked
347HackedHow Do Cyber Criminals Steal Your Money?
Image: shutterstock Today is the world where people worry less about getting mugged on street and more on the internet. With the cyber...
-

 192Data Security
192Data SecurityDude Finds Flaw in World’s Biggest Gambling Site, Steals $1M in Bitcoin
An online gaming/gambling site lost $1 million in bitcoin to an attacker who exploited its random number generation (RNG) system. A leading...
-

 341Data Security
341Data SecurityNew Spam Campaign Spreading Dridex Banking Malware
The latest spam campaign is equipped with the Dridex banking malware and targeting company accountants through deceptive emails. According to Heimdal Security,...
-

 213Cyber Crime
213Cyber CrimeWomen More Vulnerable to Phishing Scams: This Lady Lost Her Life Savings
Studies show women are more vulnerable to phishing scams than men and same has happened with Vivian Gabb who told media how she...
-
 196Cyber Crime
196Cyber CrimeHackers Steal $5 Million Worth of Bitcoin with A Simple Phishing Attack
Back in the month of January, one of the most popular bitcoin exchange namely BitStamp was hacked which resulted in the stealing...
-

 199Hacked
199Hacked20-year-old Trojan King Revealed, Maker of over 100 Banking Trojans
A 20-year-old Brazilian kid has been revealed as the maker of more than 100 banking trojans by the security firm Trend Micro....
-

 306Hacked
306HackedXKEYSCORE: NSA’s Search Engine to Hack Into Your Lives is as Simple as Google
We all know NSA is powerful. Getting into your email accounts and accessing all the private information that include your pictures, voice...
-
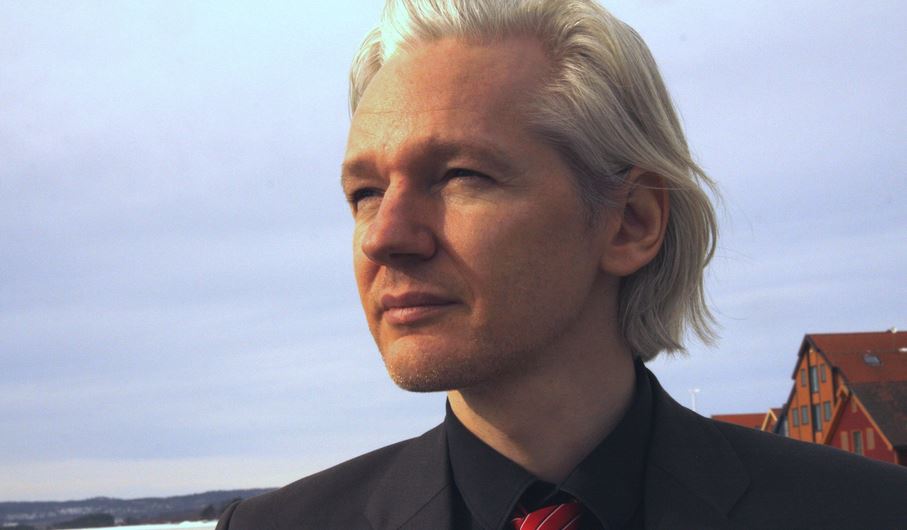
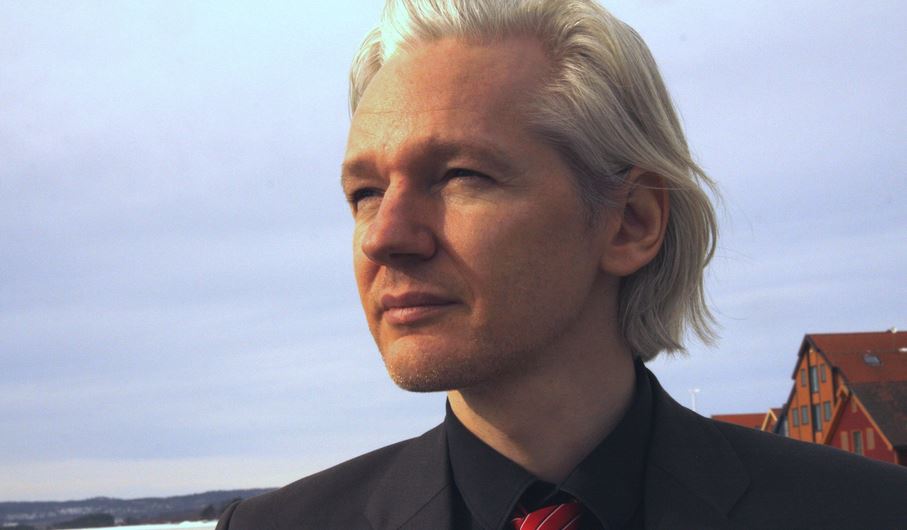 289Hacked
289HackedWikiLeaks Founder Julian Assange’s Protection Request Denied by France
WikiLeaks founder Julian Assange has revealed many controversial documents in the past couple of weeks related to Germany and France. Recently he...
-

 291Data Security
291Data SecurityHackers Develop Android Malware Every 17 Seconds
By the first quarter of 2015, hacker/cyber-attackers have optimized their efforts to design Android Malware to such an extent that every seventeen...
-

 172News
172NewsPrivate Messages Leaked after Plex Forums Hack
Plex Media Sever forum’s registered users received an email from the firm announcing that a breach of their system has exposed private...
-
 205Geek
205GeekDon’t have Internet Access? Facebook Laser Beam will Bring it to you
Mark Zuckerberg vows to make Internet and Facebook available in remote communities through LASERS — Facebook Laser Beam is coming. Mark Zuckerberg, Facebook’s...
-

 333How To
333How ToTop 20 Best Google Search Tips and Tricks That You Must Know
Web search has become synonymous with Google search. Other search engines like Bing and Yahoo are trying their best to give a...
-

 163Data Security
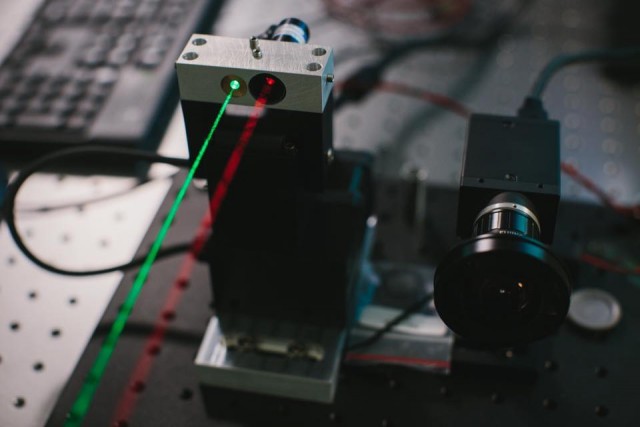
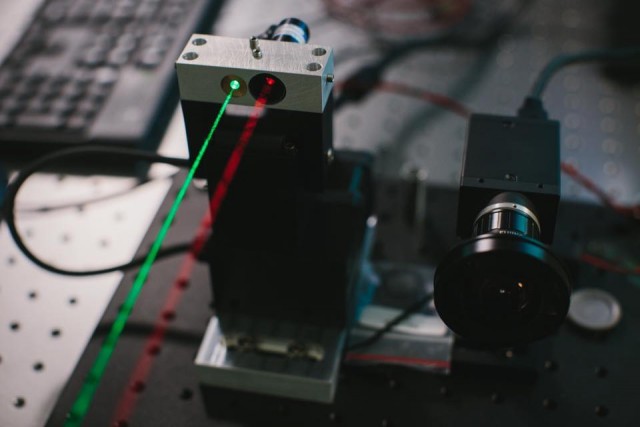
163Data SecurityAnonymously Access Wi-Fi Located Up To 2.5 Miles Away Using This Device
In this era of government surveillance, remaining anonymous has become next to impossible for every Internet user. There is almost nothing we...
-

 186Password
186PasswordMastercard trials selfies as password replacement
A new app could see Mastercard accepting selfies instead of passwords to make purchases online.
-

 176How To
176How ToHow To Get More Likes On Facebook Posts
While you share an incredibly happy moment or a deep thought on social media or change to a new dashing profile picture,...
-

 94Cyber Events
94Cyber EventsExclusive: Anonymous Breaches Canadian Government Servers Again!
Not so long ago, Canadian servers were working under peace, but after the approval of controversial anti-terror bill C-51, there’s no peace...
-
 111Geek
111GeekExclusive: Minds Founder Talks Transparency, Security, Anonymous and Evolution
Remember those rumors about Anonymous hacktivists creating their own social media? Well, they aren’t! However, some privacy advocates are indeed working on a...
-

 161News
161NewsWikiLeaks Exposes NSA’s Addiction of Eavesdropping on Its Friends
A new assortment of documents have been released by WikiLeaks revealing National Security Agency has been spying on its German associates who are...
-

 296Geek
296GeekGoogle Image Recognition Software Tags Black Couple as Gorillas
Google Apologizes after its Image Recognition Software Mistakenly Tags Black couple as Gorillas. A computer programmer Jacky Alcine saw his and a...
-

 215News
215NewsDonald Trump Hotels Face Major Credit Card Breach as Hackers Target the Empire
The meltdown of Donald Trump’s empire is slowly but continuously gaining momentum and the latest to add more misery to the real...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




