Featured News
-

 198Surveillance
198SurveillanceUsing Drone for Abortion: Here Comes The Abortion Drone
Dutch based campaigners are focusing on women’s access to “easy and safe” method to bring an end to pregnancy with the help of...
-

 181Lists
181ListsTop 5 Supercomputers Of The World
Courtesy: Prof. Jack Dongarra Supercomputers of today are the retrogressive image of the one’s in 1960s i.e. a gigantic machine racking up an...
-

 179Surveillance
179SurveillanceHackers Posting Nude Pictures of Women without Their Knowledge
Nude pictures of more than 700 Aussie females leaked online without their permission or knowledge. An individual hosting the cache in a cloud...
-

 241News
241NewsHackers Target Gospel News Portal, Leave LGBT Flag Behind
The U.S supreme court yesterday ruled in favor of same-sex marriages nationwide. Some are celebrating and some are unhappy with the ruling, but...
-
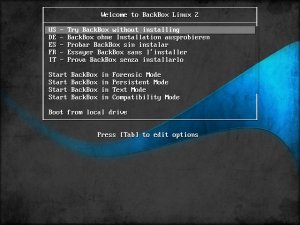
 205Operating Systems
205Operating SystemsBackbox – Turning heads in the pentesting scene
A relative newcomer to the forensic and penetration testing live CD scene, Italian project BackBox is already turning heads as it hits...
-

 218Android Hacking
218Android HackingTurning your Android into a hacking device
Now days, smartphones and tablets are the most popular gadgets. The reason behind this is that people utilize tablets for most of...
-
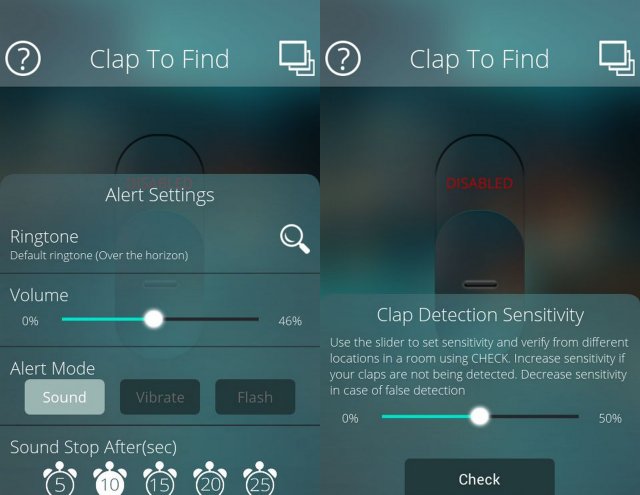
 331How To
331How ToHow to find your Silent Phone in a room without Internet
When busy with an important task, people like to put the mobile phone on Silent Mode. But what if you misplaced your...
-

 236Lists
236ListsMIT Lists 50 Smartest Companies That Owned the Year 2015
Short Bytes: This is an era of technological amelioration and every tech giant is striving to be the best. This article presents...
-
 121Hacked
121HackedHow To Remove Your Embarrassing Photos From All Social Media Websites
Work Hard and Party Even Harder. That’s the byword of today’s generation. Most of us have the same motto, myself being its hardcore...
-
 441Hacked
441HackedWatching Porn In Incognito Mode In Your Browser Isn’t As Safe As You Think
Short Bytes: The web browsers we use are shipped with settings that promise private browsing to the users. In Google Chrome, this...
-
 131Geek
131GeekRacket-lang: A Programmable Programming Language
You must have read our coverage on programming language and its development. If not, I would recommend you to go through it once....
-
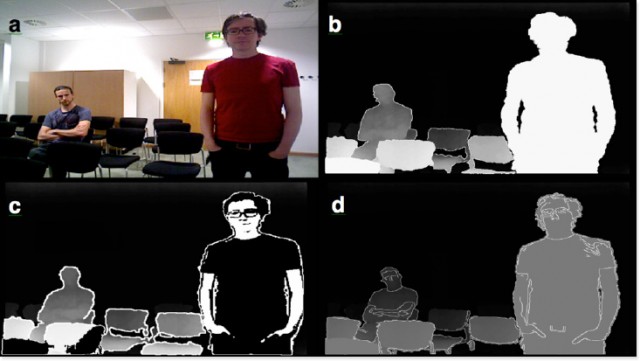
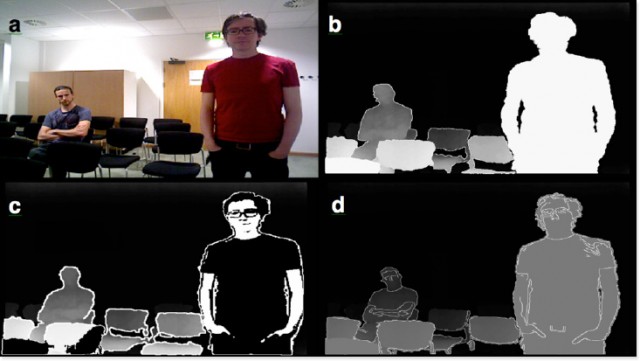 281Geek
281GeekThese Wearable Glasses Lets Legally Blind People See Again
SmartSpecs are wearable glasses developed by Startup VA-ST using augmented reality so that visually impaired could see clearly once again. A University...
-

 201Geek
201GeekFacebook Algorithm Recognise You in Images Even if You’re Not Looking
Facebook’s new Algorithm powerful enough to identify you even if you aren’t looking at the camera. Facebook’s AI/artificial intelligence lab introduced an...
-

 119News
119NewsCredentials of over 47 U.S Government Agencies Leaked on the Internet
Reportedly, login credentials of around 47 U.S government institutions across 89 different domains have been leaked. Apparently, in the earlier part of...
-
 213Surveillance
213SurveillanceSecret Audio Recording Exposes Doctors Making Fun of Patient’s Penis
Patient Records Audio While being Operated- Hears doctors Making Fun of His Penis. You surely wouldn’t expect doctors to laugh at your...
-

 285Reviews
285ReviewsBayangtoys X7 Quadcopter is Your Ultimate Affordable Flying Machine
We have been writing about various types of drones from a long time on fossBytes and in the continuously expanding drone universe,...
-

 152Scams
152ScamsPhone Scams: Increasing Numbers, Wider Scope
There's a lot more to phone scams than tech support, giving rise to an escalating number of complaints. Here's what two recent...
-
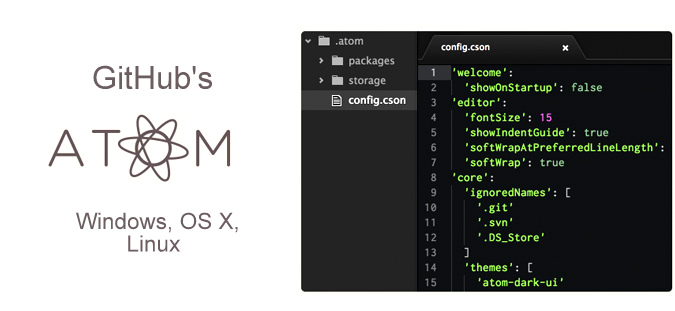
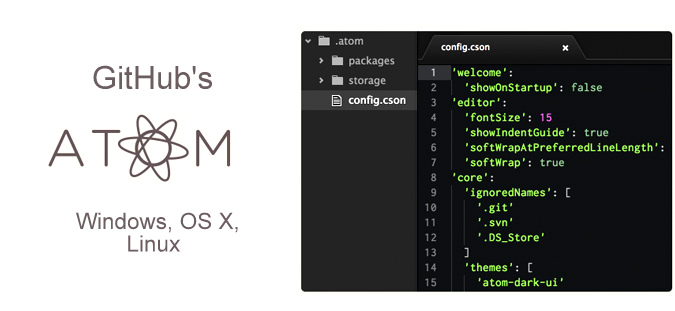 284Geek
284GeekGitHub’s Very Own Hackable Text Editor Atom Hits 1.0, Get it Now
About eighteen months ago, GitHub launched its homegrown text editor named Atom. Atom was a result of about six years of research...
-

 249News
249NewsOpBillC51: Anonymous Hacks Police Association of Ontario, Leaks Trove of Data
When Anonymous goes against you, there’s no way out! Same is going on with Canadian government who’s constantly under cyber attack against...
-

 271Data Security
271Data SecurityFacebook Join Forces with Kaspersky to Spot Malware on Computers
The problem with Facebook is thousands of active phishing scams but the social media giant has partnered with popular security software developer firm...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




