Featured News
-

 127Geek
127GeekHackerville: Inside the World’s Most Dangerous Town
Have you ever heard of a small town named Râmnicu Vâlcea from Romania? I’m pretty sure that your answer is no. This...
-

 278Geek
278GeekGetting Started with Linux: Part II (Installation and more)
Read the Part 1 and Part 3 of Getting Started with Linux : Choosing the desired Linux distribution and Command Line After downloading a...
-

 280Surveillance
280SurveillanceTeen Tracking Lost Phone Using App Shot Dead
Teen shot dead while using mobile phone tracking app — All that it took to take the life of an innocent teen was a...
-
 110Opinion
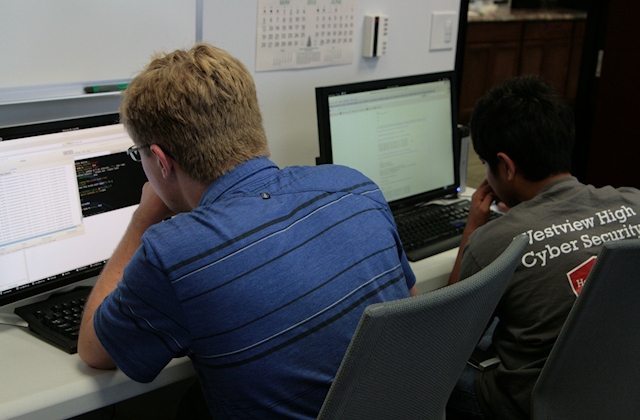
110OpinionCyber Boot Camp: a head start for tomorrow’s cyber workforce
Every June, a select group of students from high schools and middle schools in San Diego County, California, get five days of...
-
 119News
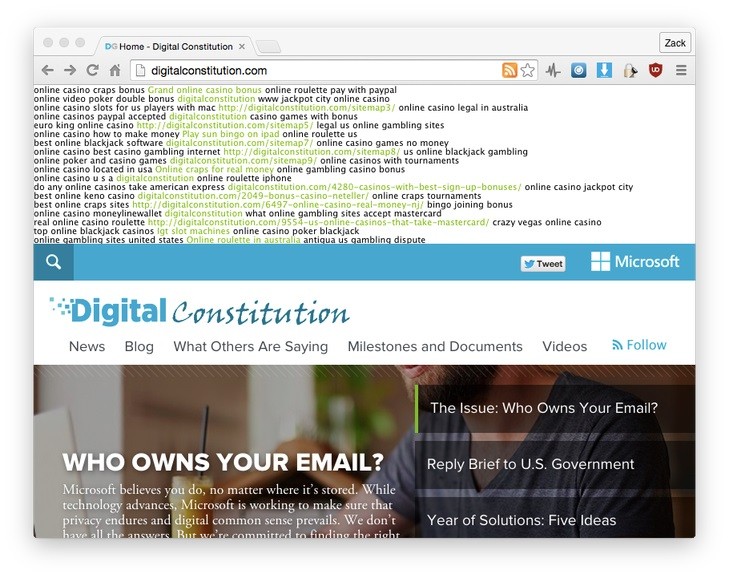
119NewsAnti-US Govt Surveillance Website by Microsoft Hacked
Microsoft, just like all other software companies, constantly asks its customers to update their applications on their computers to remain fully secure...
-

 115Privacy
115PrivacyDuckDuckGo traffic up after Apple integration and privacy issues
Privacy search engine DuckDuckGo has seen traffic rocket after recent widely publicized privacy scares, according to the company.
-

 200Hacked
200HackedMicrosoft’s Website to Fight Government Surveillance Just Got Hacked
Microsoft’s dedicated website to fight the US government surveillance and privacy breachings has just been hacked. While Microsoft is aiming to bring...
-

 269Geek
269GeekGoogle, Microsoft, Apple and Mozilla Working Together On WebAssembly For Faster Web
The genius minds at Google, Microsoft, Mozilla and Apple are coming together to create WebAssembly (also known as wasm). This is a...
-

 251Cyber Events
251Cyber EventsAnonymous Shuts Down Canadian Govt Websites Against Bill C-51
The online hacktivist Anonymous claimed responsibility for conducting DDoS attacks on Canadian government servers against the approval of anti-terror law C-51 that...
-
 275Data Security
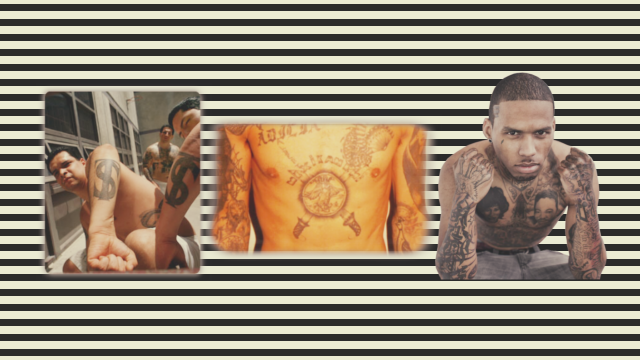
275Data SecurityTattoo Recognition System Could Identify Criminals Very Soon
Tattoo Recognition System is coming! Recently committed a crime? Do you happen to have a large visible tattoo? Then you could soon...
-
 298Geek
298GeekBelgian Watchdog Sues Facebook for Tracking Users
Facebook is in hot water. The social media giant is being taken to court by Belgium’s Privacy Commission (BPC), among accusations that...
-
 202Data Security
202Data SecurityEmojis To Be Your New Pin Codes
So long Password1234 or surname1, there is a new, more readily memorable password system on our doorstep — That is what Intelligent...
-

 284Data Security
284Data SecuritySecurity Flaw in Samsung Keyboard Puts 600m Android Devices Vulnerable
Android phone users have long shared the view that, despite the continual announcements of ongoing security breaches in an evermore technological world,...
-

 112Password
112PasswordUK Consumers willing to share DNA with banks to secure identity
Consumers in the UK would be happy to share their DNA if it would help secure their financial and personal information, according...
-

 265Cyber Crime
265Cyber CrimeOnline Predators Hunting Users with Video Chat Extortion Scams
In October last year, we reported how a 10-year-old filipino virtual girl “sweetie” takes pedophile to prison in Australia for good. Now a...
-

 80Cyber Crime
80Cyber CrimeTop US baseball team accused of hacking rival
The St. Louis Cardinals, one the United States's top major league baseball teams, is being investigated for allegedly hacking into the computer...
-

 274News
274NewsLithuanian Armed Forces Website Hacked, Defaced with False Information
Someone hacked the official website of Lithuanian Armed Forces and posted false information about NATO ready to attack Kaliningrad Oblast. A group of unknown...
-

 313Cyber Crime
313Cyber CrimeBeware of New ‘Forbidden Content’ Facebook Phishing Scam Hitting Inbox
Another day, another Facebook phishing scam — Facebook users must be cautious since a new phishing scam message is circulating on the...
-
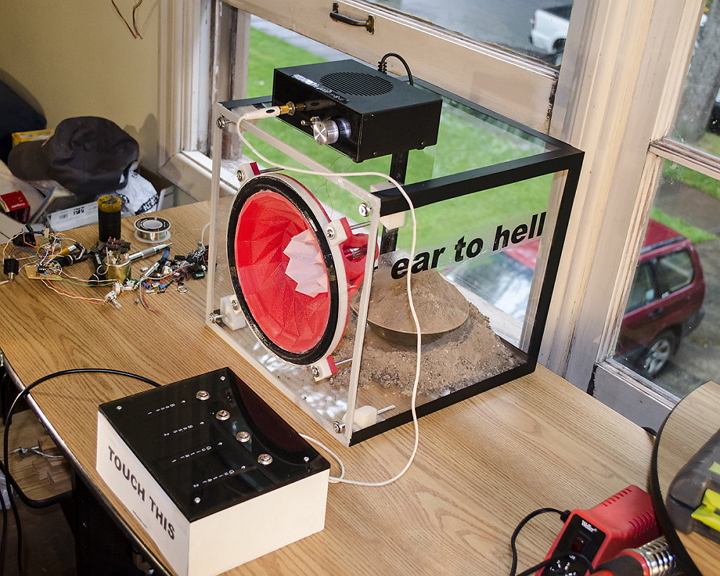
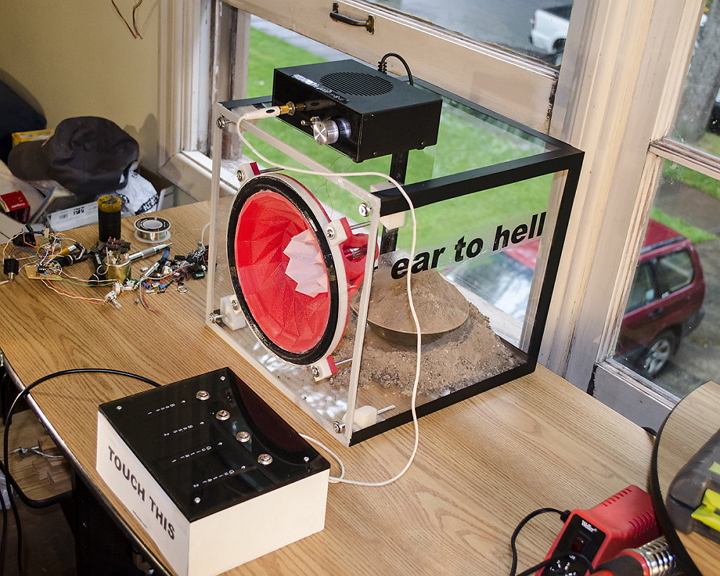 295Geek
295GeekHere’s a 3D Printed Remaking of ‘Ear of Hell’ Classic Audio Speakers
A San Francisco Bay Area based artist and designer Ted Kessler has always yearned to merge art with science. A bachelor in...
-
 317Data Security
317Data SecurityHackers Used ‘Stolen Foxconn certs’ to Hack Kaspersky Via Duqu 2.0 Malware
‘Stolen Foxconn certs’ used for embedding Duqu 2.0 malware into Windows PC — The crafty super-sophisticated malware infiltrated Kaspersky Labs. Reportedly, Duqu...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




