Featured News
-

 110Privacy
110PrivacyEU data protection regulation overhaul inches closer
The 28 EU member states have taken a significant step towards a historic overhaul of EU-wide data protection laws, first proposed three...
-

 235Geek
235GeekFacebook launches new photo sharing App, Moments
Do you remember asking your friend with a Camera on a Trip to share the photographs with you? Or do you remember...
-

 375Hacked
375HackedAnonymous is Supporting New Social Network “Minds”: Facebook’s Latest Challenge
Just when you thought that you’ve had enough social networking today and you definitely need a new social network around, here comes...
-
 219Computer Forensics
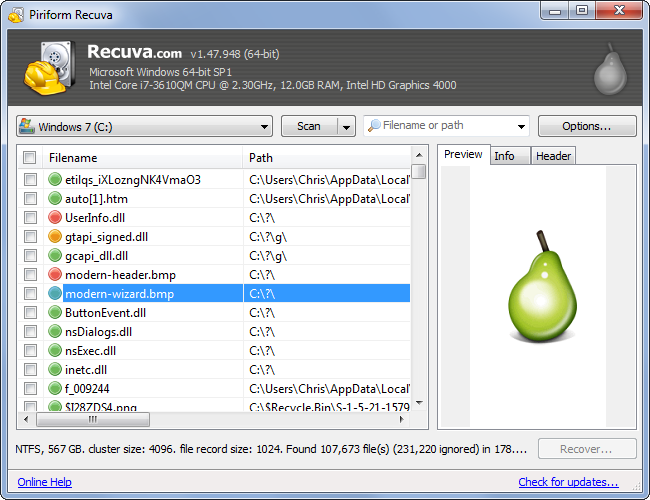
219Computer ForensicsRecovering your Deleted Files
It has happened to most of us. You deleted a file and realize you need it back. But is it really deleted?...
-

 112News
112NewsUber Petition Website Hacked- Hacker Uploaded Ad of Rival Firm Lyft
Due to a security flaw, researcher Austin Epperson took control of a page of Uber’s website and displayed the ad of its arch-rival...
-

 261News
261NewsLeading Password Security Company LastPass Hacked
Joe Siegrist from LastPass, a famous password manager program, admitted that its database comprising of email addresses, server per user salts, password...
-

 206Password
206PasswordPassword security firm LastPass compromised
Popular online password vault provider LastPass has warned users to update their master account passwords after their network was hacked.
-

 115How To
115How ToA beginner’s guide to starting in InfoSec
Much ink has been spilt about the shortage of people trained in information security – especially the lack of women in the...
-

 265Cyber Crime
265Cyber CrimeNew Facebook Phishing Scam Posts Links on Friends Timeline
Facebook timelines nowadays are displaying a new phishing scam message with the title “Here’s the Link HeHe.” The text of this scam...
-
 177Data Security
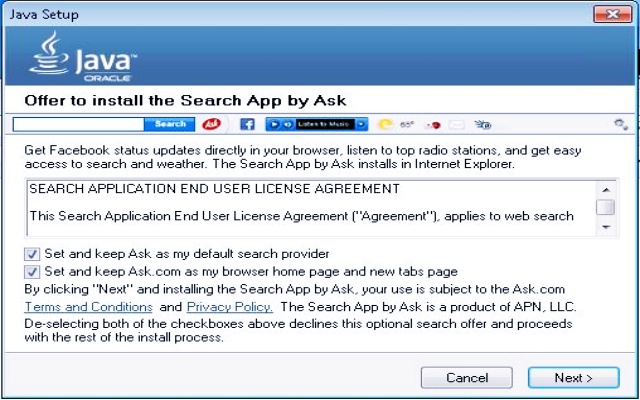
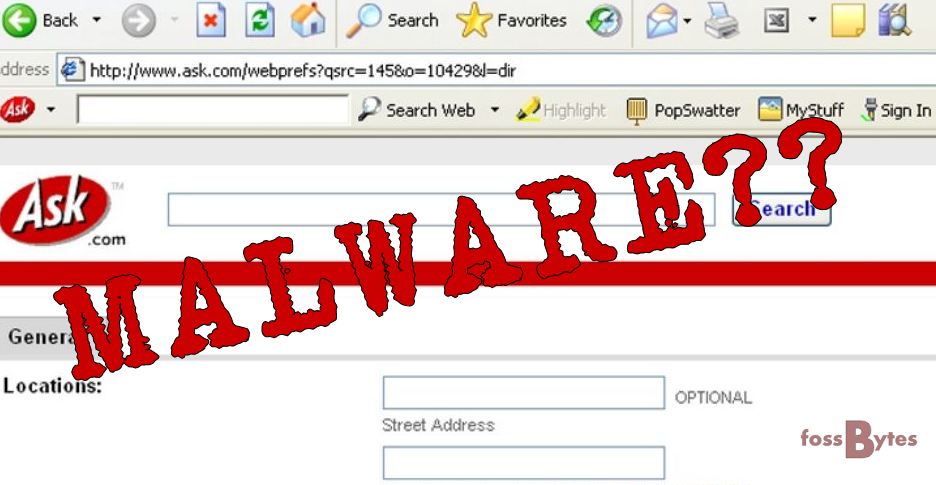
177Data SecurityMicrosoft Declares Ask toolbar as Dangerous Malware
In April 2015, we reported how Ask.com toolbar is working as a malware to hijack your computer. Now proving our claim right, previous...
-
 209Surveillance
209SurveillanceGood News for Wikipedia Readers- Encrypted Connections Coming Soon
Awesome News for Wikipedia Readers- Encrypted Connections Coming Your Way Pretty Soon. Currently, data between users and Wikipedia.com is unencrypted, and this increases...
-

 232Data Security
232Data SecurityUnpatched Security Flaws Openly Solicited by US Navy
Governments unsurprisingly are trying to buy unpatched security exploits in the name of surveillance or cyber defence but refrain from admitting it....
-

 513How To
513How ToHow To Get Windows 10 Upgrade Icon If Missing – Official Method by Microsoft
Microsoft is trying desperately to convince the users to upgrade their Windows 7 and Windows 8.1 PCs to the next iteration to...
-
 201How To
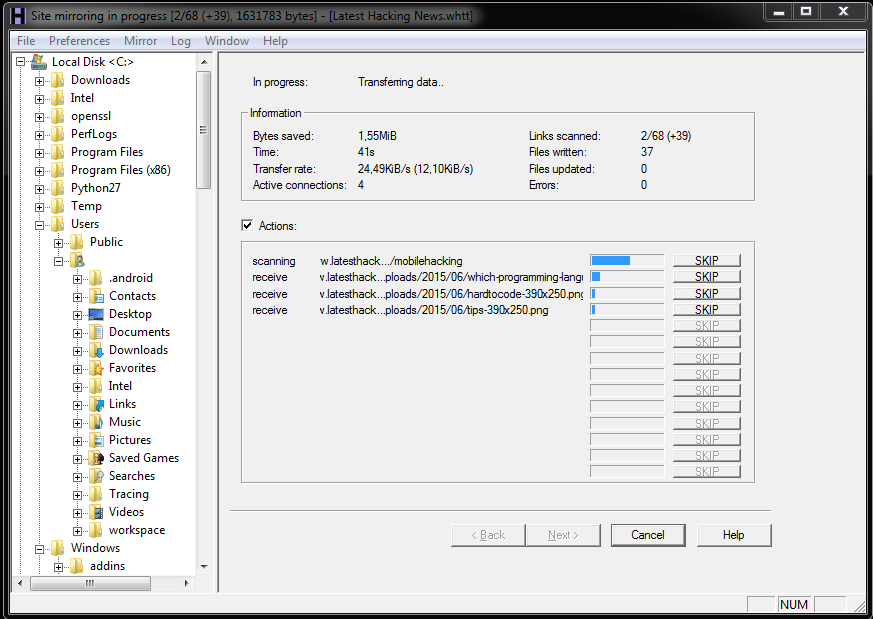
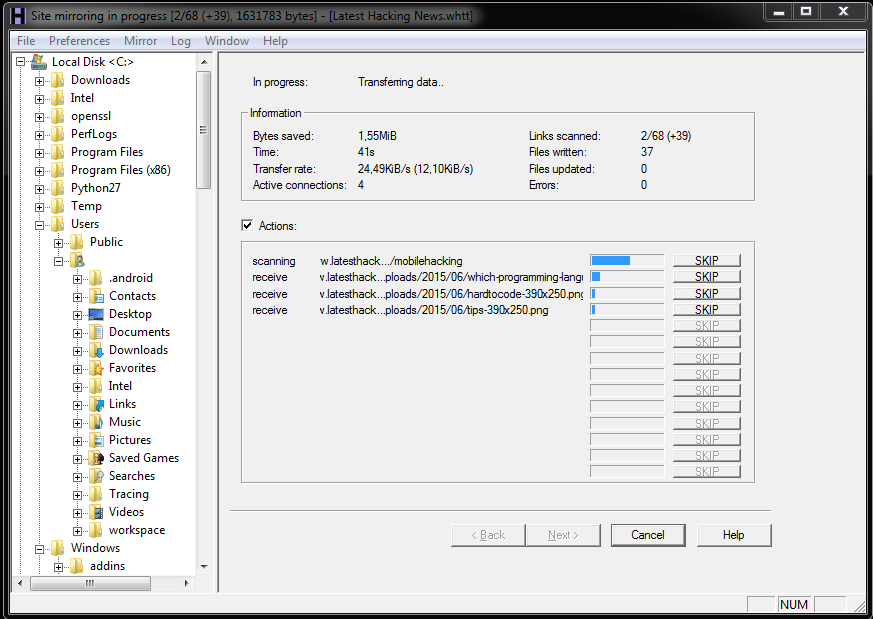
201How ToHow To Download And View Website Offline
Few times you have to give up on loading multiple website with slow internet connection or having problem with internet, or when...
-

 195Privacy
195PrivacyWikipedia switches to HTTPS by default
Wikimedia has announced that all of its web properties – including the enormously popular crowd-sourced dictionary Wikipedia – will now use HTTPS...
-
 221Hacked
221HackedAsk Toolbar in Your Browser is a Malware: Microsoft
The vintage Ask toolbar that you can spot in your computer’s web browser has now been termed as threat to your PC...
-
 160Tricks & How To's
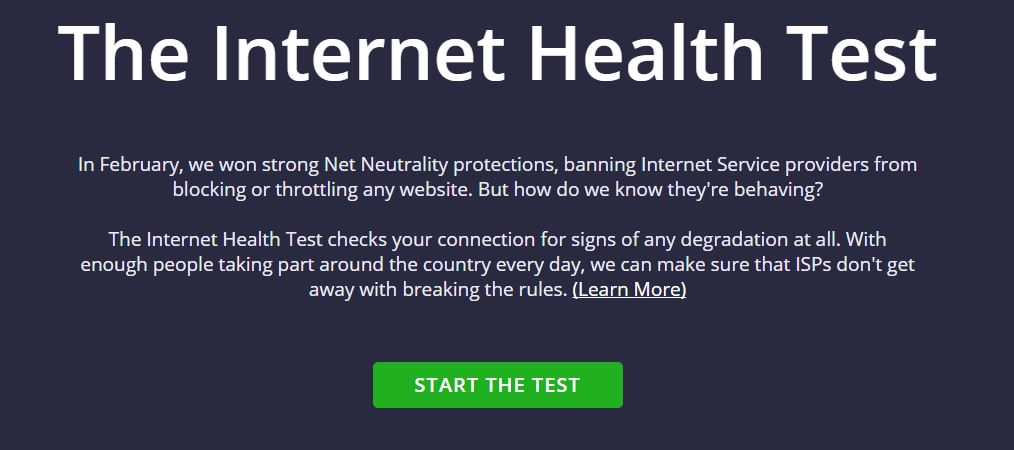
160Tricks & How To'sHow to check whether your ISP is Throttling your Internet speeds.
You, the usual and the average consumer, doesn’t know the boundaries that define the exploitation when it comes to the net neutrality...
-

 306How To
306How ToA Complete Guide On Facebook Tips And Tricks
Who would have thought something that started as a mischief could go on to become the heart of a billion people’s social...
-

 283Data Security
283Data SecurityHacker Targets Pedophiles with TOX Ransomware
Tox is yet another example of cyber justice that has been meted out by cyber criminals. In this case, Tox sends a...
-

 186Geek
186GeekNew Computer Algorithm Learns Rap Lyrics and Writes Its Own Rap Song
Have you ever wondered how musicians write music? Do you think it’s possible to technically generate a composition and write lyrics to...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




