Featured News
-

 282News
282NewsSecond Hack Rattles US Federal and Military Personnel
Another hack has just exposed the personal details of more than 14 million people. According to intelligence reports, the hack was linked...
-

 232Geek
232GeekNew Headsets will Merge Night Vision and Thermal Imaging Features
A new headset is being developed by the BAE Systems Plc, which will merge thermal imaging and night vision to make night...
-
 240Hacked
240HackedHere’s How You Can Track the FBI Spy Planes
In a report earlier his month, it was reported that the Federal Bureau of Investigation (FBI) is flying spy planes over the...
-

 236Data Security
236Data SecurityApps will Automatically Detect Malware in Windows 10
Software developers will have the opportunity to integrate their application to any antimalrware program (available on their computer) in windows 10. Microsoft...
-

 126Cyber Crime
126Cyber CrimeCanadian Hacker Jailed in U.S. for Hacking Military and Xbox
A hacker from Mississauga, Canada got imprisoned for leading a worldwide computer hacking group that managed to penetrate the U.S military network...
-

 524Privacy
524PrivacySnapchat bolsters security with optional Two‑factor authentication
Snapchat has added an option for two-factor authentication in its latest update, followed in the footsteps of Apple, Twitter and Facebook.
-

 107Data Security
107Data SecuritySecurity Bug Makes Millions Of iOS 8.3 iCloud Passwords Vulnerable
You may need to change the password of your iOS device as a security researcher reported that a flaw in Apple’s systems can...
-

 132Data Security
132Data SecurityFacebook Users Left Red-Faced After Porn Malware Attack
Hackers spammed Facebook timelines and newsfeeds with malicious malware that spread pornographic videos and images. The attack left hundreds of social media...
-

 334Data Security
334Data SecurityFrance Believes Russia Hacked TV5Monde Posing as ISIS Hackers
The involvement of a Russian hacking group posing as ISIS/ISIL militants in the April cyberattack that crippled a French-language broadcaster has been...
-

 78Cyber Crime
78Cyber CrimeFBI trace celebrity iCloud hacks to Chicago home
The FBI has seized a computer, cellphones and storage devices belonging to a Chicago man thought to be responsible for last year's...
-

 315News
315NewsHackers Hiding Vawtrak Banking Malware Command Servers in Tor
Some versions of Vawtrak banking Malware or Neverquest have been discovered to be having hidden command and control servers at Tor anonymity...
-

 246Cyber Crime
246Cyber CrimeEuropol shuts down cybercrime ring with 49 arrests
Europol's European Cybercrime Centre has arrested 49 suspects in a joint international operation targeting the takedown of a major cybercrime ring.
-

 282News
282NewsEven the Best isn’t Safe: World’s Leading Cybersecurity Firm Kaspersky Hacked
An expensive and highly sophisticated hack attack was carried out on the Moscow-based Kaspersky Lab by state-backed hackers. On Wednesday the world’s...
-

 151Cyber Crime
151Cyber CrimeCredit Unions and the Data Security Act of 2015
Credit Unions lost a lot of money due to recent breaches, so financial institutions are eager to see merchants held to higher...
-

 111Cyber Crime
111Cyber Crime“Attempts to Export Opengraph File” Phishing Scam Targeting Facebook Users
A new phishing scam has surfaced on the web via Facebook in the form of a message titled “Attempts to Export Opengraph...
-

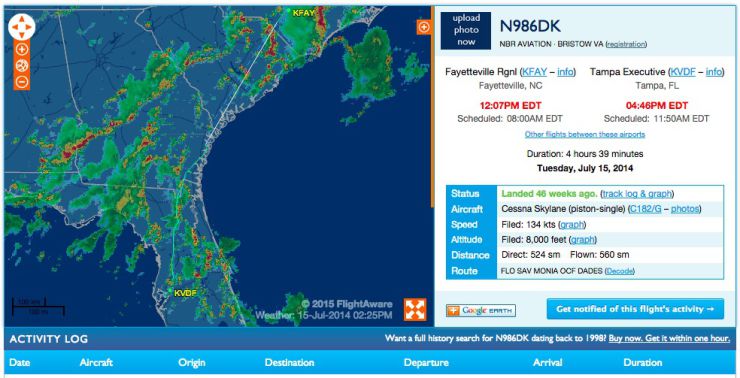
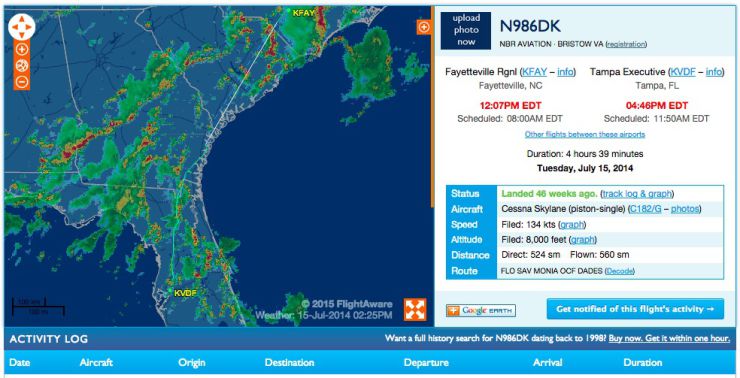
 252Surveillance
252SurveillanceCanada’s New Anti-Terror Bill C-51 will Ruin Internet Privacy
Canada approves anti-terror law C-51 that weakens Internet privacy – NDP-Liberal coalition may get triggered as a result warn conservative critics. At...
-

 268News
268NewsPro-Palestine Group Hacks Subdomains of US Air Force Website
Summary: Yesterday, it was the pro-Assad hackers from Syrian Electronic Army who took over the US Army website, today the pro-Palestinian hackers...
-

 94Cyber Crime
94Cyber CrimeBritish businesses spend £34bn a year defending cyberattacks, limiting growth
A new survey has estimated that British businesses spend around £34bn a year ($52.5bn) protecting the country from cyberattacks,
-
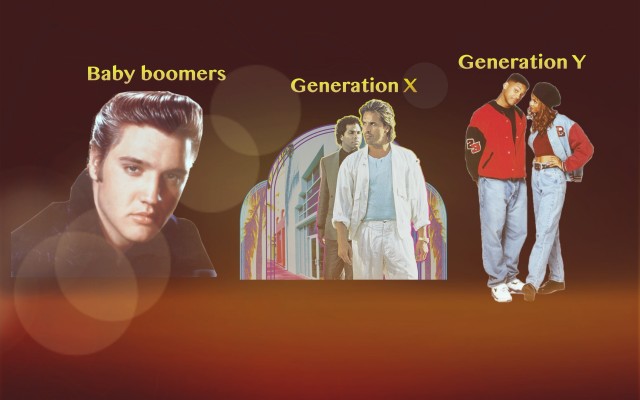
 194Cyber Events
194Cyber EventsGeneration Y is More Vulnerable to Cyber Attacks than Generation X, says study
A survey conducted by the Gartner-affiliated research firm Software Advice shows that Generation Y – those born after the 80s – is more vulnerable...
-

 222Cyber Events
222Cyber EventsUN Watchdog Warns of Increase in Cyberattacks on Nuclear Facilities
Computer systems at nuclear facilities all over the world face cyberattacks on a daily basis, says a UN nuclear watchdog group while addressing...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




