Featured News
-

 290Data Security
290Data SecurityHacker Targets Pedophiles with TOX Ransomware
Tox is yet another example of cyber justice that has been meted out by cyber criminals. In this case, Tox sends a...
-

 187Geek
187GeekNew Computer Algorithm Learns Rap Lyrics and Writes Its Own Rap Song
Have you ever wondered how musicians write music? Do you think it’s possible to technically generate a composition and write lyrics to...
-

 286News
286NewsSecond Hack Rattles US Federal and Military Personnel
Another hack has just exposed the personal details of more than 14 million people. According to intelligence reports, the hack was linked...
-

 233Geek
233GeekNew Headsets will Merge Night Vision and Thermal Imaging Features
A new headset is being developed by the BAE Systems Plc, which will merge thermal imaging and night vision to make night...
-
 245Hacked
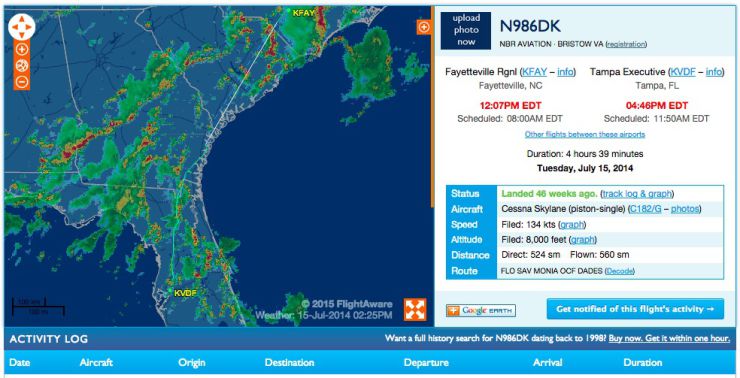
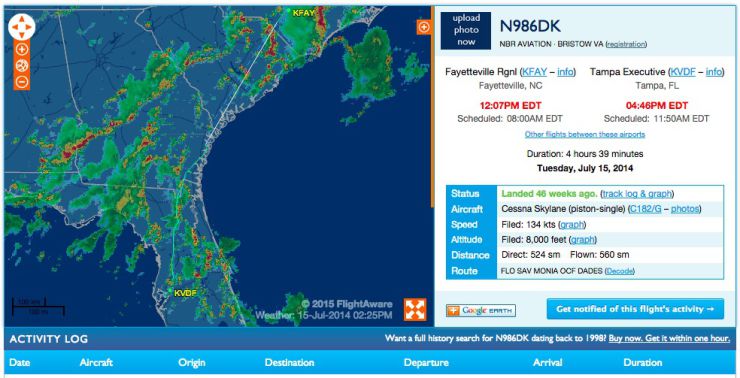
245HackedHere’s How You Can Track the FBI Spy Planes
In a report earlier his month, it was reported that the Federal Bureau of Investigation (FBI) is flying spy planes over the...
-

 240Data Security
240Data SecurityApps will Automatically Detect Malware in Windows 10
Software developers will have the opportunity to integrate their application to any antimalrware program (available on their computer) in windows 10. Microsoft...
-

 130Cyber Crime
130Cyber CrimeCanadian Hacker Jailed in U.S. for Hacking Military and Xbox
A hacker from Mississauga, Canada got imprisoned for leading a worldwide computer hacking group that managed to penetrate the U.S military network...
-

 529Privacy
529PrivacySnapchat bolsters security with optional Two‑factor authentication
Snapchat has added an option for two-factor authentication in its latest update, followed in the footsteps of Apple, Twitter and Facebook.
-

 109Data Security
109Data SecuritySecurity Bug Makes Millions Of iOS 8.3 iCloud Passwords Vulnerable
You may need to change the password of your iOS device as a security researcher reported that a flaw in Apple’s systems can...
-

 135Data Security
135Data SecurityFacebook Users Left Red-Faced After Porn Malware Attack
Hackers spammed Facebook timelines and newsfeeds with malicious malware that spread pornographic videos and images. The attack left hundreds of social media...
-

 336Data Security
336Data SecurityFrance Believes Russia Hacked TV5Monde Posing as ISIS Hackers
The involvement of a Russian hacking group posing as ISIS/ISIL militants in the April cyberattack that crippled a French-language broadcaster has been...
-

 81Cyber Crime
81Cyber CrimeFBI trace celebrity iCloud hacks to Chicago home
The FBI has seized a computer, cellphones and storage devices belonging to a Chicago man thought to be responsible for last year's...
-

 318News
318NewsHackers Hiding Vawtrak Banking Malware Command Servers in Tor
Some versions of Vawtrak banking Malware or Neverquest have been discovered to be having hidden command and control servers at Tor anonymity...
-

 249Cyber Crime
249Cyber CrimeEuropol shuts down cybercrime ring with 49 arrests
Europol's European Cybercrime Centre has arrested 49 suspects in a joint international operation targeting the takedown of a major cybercrime ring.
-

 285News
285NewsEven the Best isn’t Safe: World’s Leading Cybersecurity Firm Kaspersky Hacked
An expensive and highly sophisticated hack attack was carried out on the Moscow-based Kaspersky Lab by state-backed hackers. On Wednesday the world’s...
-

 157Cyber Crime
157Cyber CrimeCredit Unions and the Data Security Act of 2015
Credit Unions lost a lot of money due to recent breaches, so financial institutions are eager to see merchants held to higher...
-

 114Cyber Crime
114Cyber Crime“Attempts to Export Opengraph File” Phishing Scam Targeting Facebook Users
A new phishing scam has surfaced on the web via Facebook in the form of a message titled “Attempts to Export Opengraph...
-

 258Surveillance
258SurveillanceCanada’s New Anti-Terror Bill C-51 will Ruin Internet Privacy
Canada approves anti-terror law C-51 that weakens Internet privacy – NDP-Liberal coalition may get triggered as a result warn conservative critics. At...
-

 272News
272NewsPro-Palestine Group Hacks Subdomains of US Air Force Website
Summary: Yesterday, it was the pro-Assad hackers from Syrian Electronic Army who took over the US Army website, today the pro-Palestinian hackers...
-

 96Cyber Crime
96Cyber CrimeBritish businesses spend £34bn a year defending cyberattacks, limiting growth
A new survey has estimated that British businesses spend around £34bn a year ($52.5bn) protecting the country from cyberattacks,
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




