Featured News
-

 146Hacked
146HackedMozilla: Firefox Tracking Protection Speeds Up Web Pages by 44%
Do you know that not all web sites honor the native Do Not Track feature of your web browser? Even in the...
-

 67Cyber Crime
67Cyber Crime5 hackers who came over from the dark side
Five reformed hackers who turned their lives around to help in the fight against cybercrime, leaving their blackhat past behind.
-
 151Hacking Tutorials
151Hacking Tutorials6 Ways to Secure a Wireless Wi-Fi Network
Wireless Networking (Wi-Fi) has made it so easy for anyone to use Internet on your computer, mobile phones, tablets and other wireless...
-

 263Hacked
263HackedNSA Prepares to SHUT DOWN Mass Phone Tracking Program
As a result of a midnight session, the American Senate has voted down the USA Freedom Act- the basis of NSA’s mass...
-

 279News
279NewsAnonymous Breaches Thailand Senate Website against Human Trafficking
The online hacktivist Anonymous breached into the official website of Thailand Senate and Public Health Ministry, ending up leaking login credentials against country’s alleged...
-

 232News
232NewsWebsite of Uzbek Embassy in Kuwait hacked by anti-Assad Hacker
The anti-Bashar Al Assad hacker from Syria hacked into the official website of Uzbekistan Embassy in Kuwait and demanded governments around the world...
-
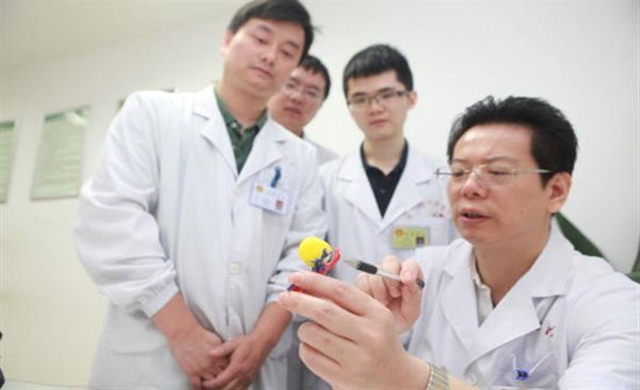
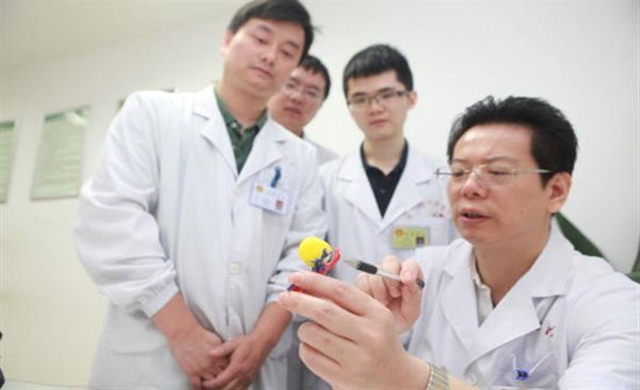 281Geek
281GeekMiracle Miracle! A woman’s kidney tumor cured by 3D printing
When it’s about performing surgeries on vital organs, today’s advanced imaging techniques such as CT scans, MRIs and ultrasound machinery have made...
-

 313Surveillance
313SurveillanceThese Iris scanners can now identify people from 40 feet away
It’s a high point for “Biometric technology” as in the latest advancement now. It is possible to record data about an individual’s...
-
 174News
174NewsAdult dating site hack reveals sexual secrets of millions, including feds and cops
An Adult Dating website AdultFriendFinder is the newest victim of a huge hack that exposed the personal information, with sexual orientation details,...
-

 297Geek
297GeekInjured Turtle Gets 1st 3D Printed Titanium Jaw Implant
A big day in the history of animal prostheses has arrived, Turkey’s medical 3D printing company provided an injured turtle with a...
-
 201How To
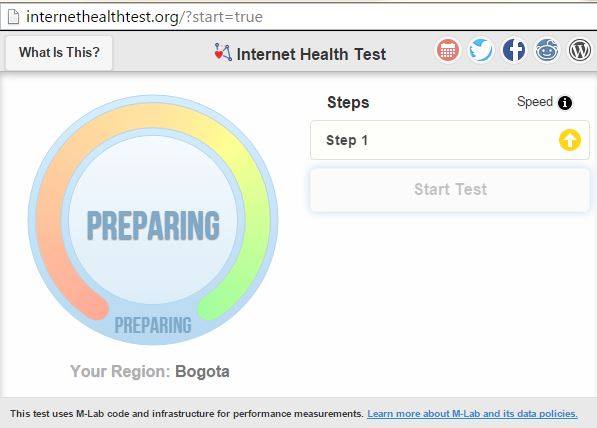
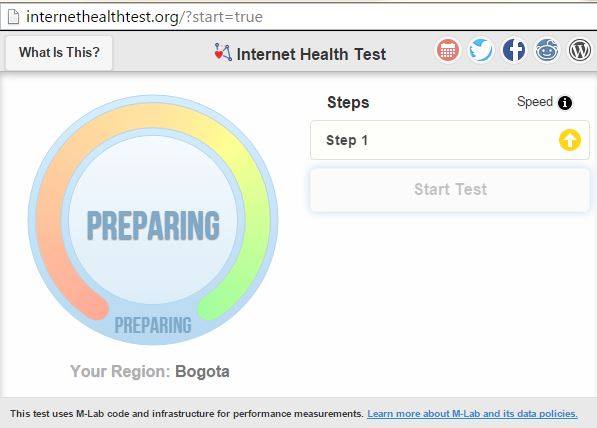
201How ToHow to Check if Your ISP is Violating Net Neutrality and Slowing You Down
The net neutrality debate continues to evolve and now the common people have a better understanding of the topic. Here at fossBytes,...
-
 325Cyber Events
325Cyber EventsHackers leak Confidential data from Saudi Ministry of Foreign Affairs! It’s Crazy
Yemen Cyber Army claims it breached into the Saudi Ministry of Foreign Affairs server and leaked plain-text login credentials of Saudi officials...
-

 87Cyber Crime
87Cyber CrimeThe wider world of security research output: webinars
Security research is published in many forms. For example, there are live and recorded webinars that cover a range of cybersecurity topics.
-

 133Password
133PasswordGoogle reveals failure of ‘secret question’ password recall
A research paper from Google has looked into the difficulties of standard 'forgotten password' personal information verification.
-

 451Geek
451GeekMom Shames 13-year-old Daughter for acting slutty on Facebook
Denver mom Val Starks becomes enraged and publicly humiliates daughter on Facebook for posing as 19 and posting indecent pictures — Video has...
-

 89Privacy
89PrivacyAdult dating site hacked, leaking private information
Casual dating website 'Adult FriendFinder' has been hacked, leaking data from as many as 3.9 million accounts, according to an investigation by...
-

 91Password
91PasswordApple bolsters app store security with 2FA and Touch ID
A new update to the Apple Store app for iPhone and iPad has bolstered its security features, adding two-factor authentication (2FA) and...
-

 295How To
295How To5 security questions to ask before clicking on a link
Should you trust that link? We Live Security runs down five quick security questions to ask before you click on a URL.
-

 81Malware
81MalwareScareware: Fake Minecraft apps Scare Hundreds of Thousands on Google Play
ESET has discovered over 30 scareware apps available for download from the Google Play store. The apps have been installed by more...
-

 292Cyber Events
292Cyber EventsMassive US Healthcare Company Hacked, 1.1 million customers affected
Massive Healthcare Company is another victim of malicious Hacking — Currently the third Blue Cross and Blue Shield insurer targeted. Hackers have targeted...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




