Featured News
-

 114Mobile Security
114Mobile SecurityGoogle to add permission controls in upcoming Android M
At the Google I/O event in San Francisco, the company announced a number of changes to its Android mobile operating system, including...
-

 213Password
213PasswordGaana music streaming hack could affect over 10 million users
One of India's most popular music streaming services, Gaana, was pulled offline after a hack resulted in a leak of data affecting...
-

 246Cyber Crime
246Cyber CrimeFacebook Predator sentenced to 29 years on child pornography, sexual offenses
The 23year old Sacramento, CA, Paradise resident Jordan James Kirby has been sent to jail for 29years by United States District Judge...
-
 207Scams
207ScamsPhish Phood for Thought
In 2007, David Harley and Andrew Lee suggested at Virus Bulletin that poorly-designed phish quizzes did more harm than good. Has the...
-

 237How To
237How ToHow to Connect Two Computers Via Crossover Ethernet Cable
In this tutorial we are going to show you how to transfer data from one computer to another. We need to PC/Laptop...
-

 212Data Security
212Data SecurityNew Security Checkup Tested by Facebook for Optimal Security of your Account
Numerous tweaks in security features have been made by Facebook over the past few years. This has been done to ensure that your...
-

 105Cyber Events
105Cyber EventsChina to beef up its cyber force to combat security threats
A military white paper said on Tuesday that China needs to take strong measures in order to speed up the development of...
-
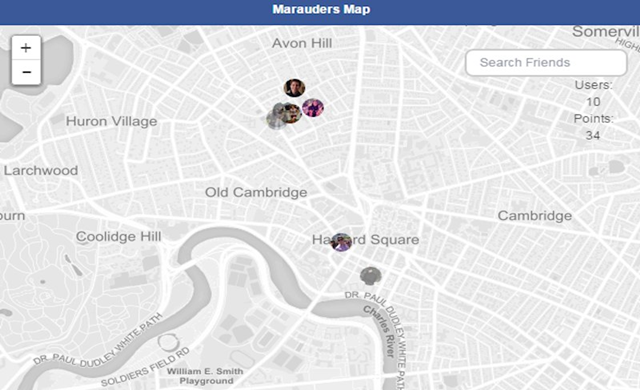
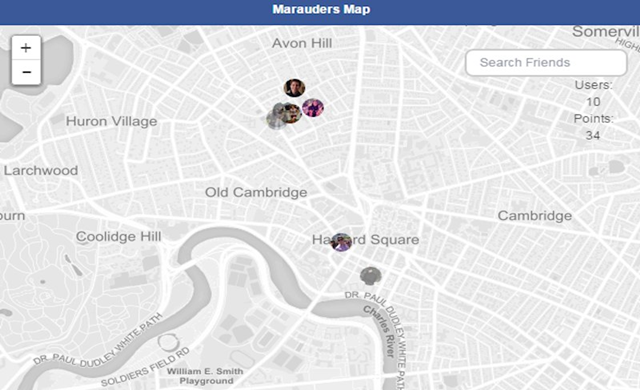 206Surveillance
206SurveillanceA Hack Lets You View map of Wherever Facebook knows you, your folks have been
Summary: A new Google Chrome extension has been identified by The Next Web with which you can check out a personal map...
-

 290Small business
290Small businessIrish businesses may be penalized over inadequate IT security
Irish businesses have been criticized for their IT security standards after it was revealed that a significant majority are not currently meeting...
-

 159Data Security
159Data Security“Android, OS X, iOS and Windows are all malware”, says GNU creator
Richard Stallman, the famous creator of GNU operating system, which is often called Linux, opined in a post in The Guardian that...
-

 88Malware
88MalwareESET uncovers another porn clicker on Google Play
Porn clickers pretending to be the the Dubsmash application have found their way back onto Google Play, a month after being removed.
-

 98How To
98How ToCyber risk analysis, assessment, and management: an introduction
Risk analysis is the first step towards managing risks, particularly when it comes to cyber risks. This recorded webinar introduces and explains...
-
 217How To
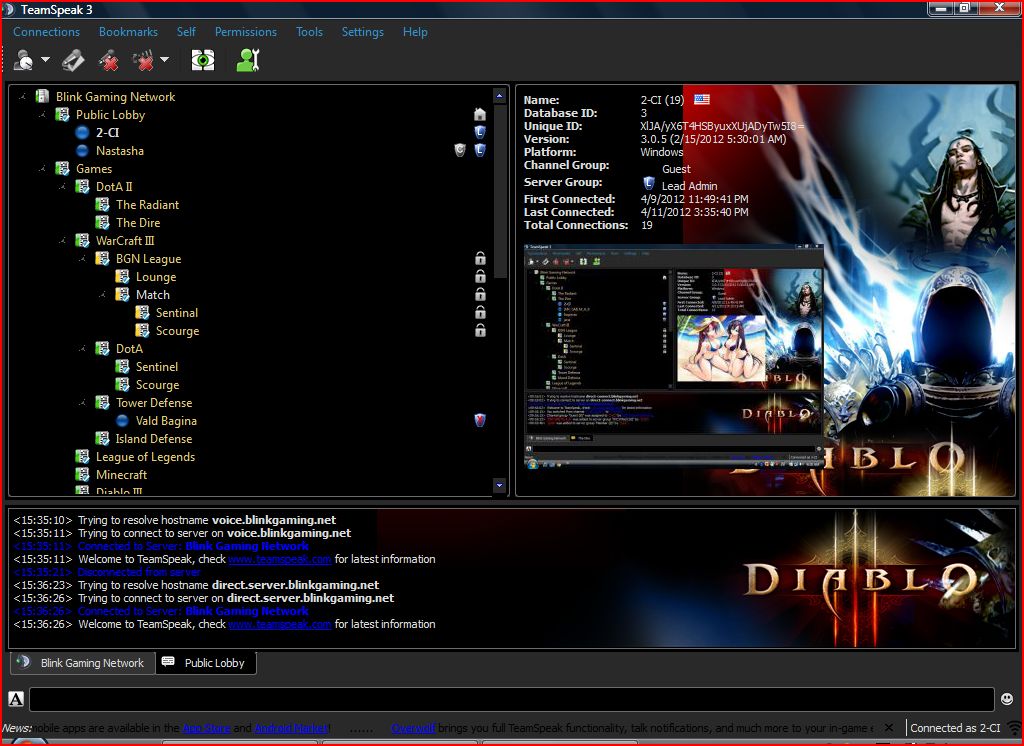
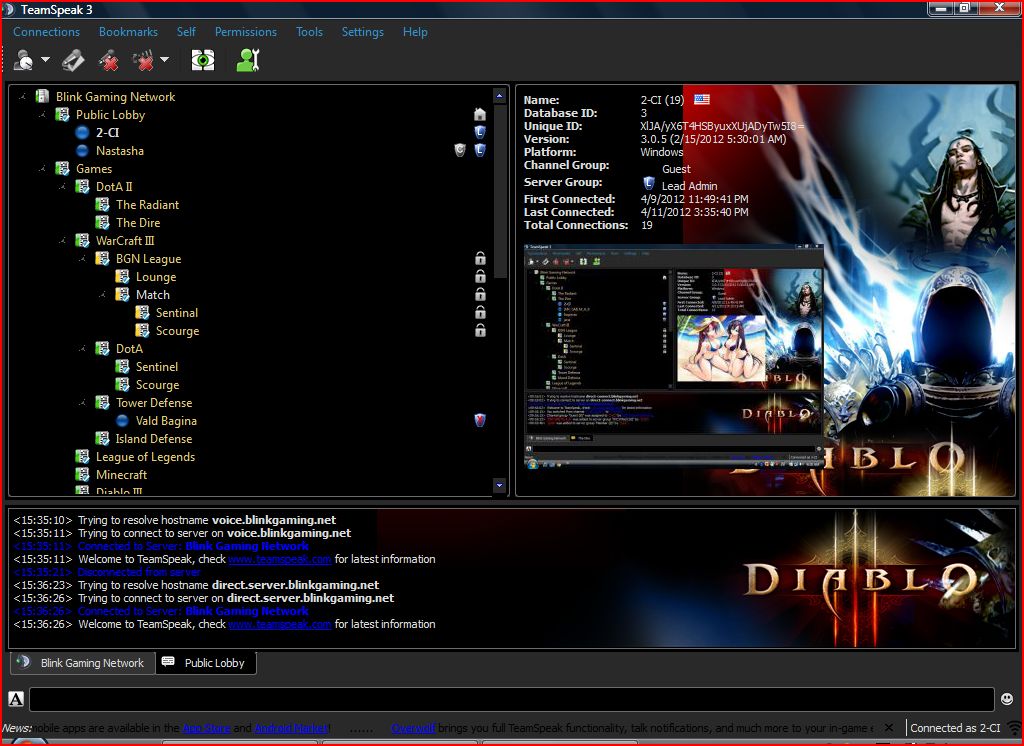
217How ToHow To Create A Team Speak Server
Team speak is a software for voice communication on Internet mostly used by gamers. This software is cost free and easy to...
-

 118Geek
118GeekPersonal information of 500million Android users at risk
Summary: Personal Data of More than 500Million Android Users in Danger — Researchers Claim it is Impossible to Fully Delete Data from...
-

 297Data Security
297Data SecurityA bug lets you crash anyone’s iPhone with a text message
Apple iOS mobile operating system’s Message App bug causes its devices iPad, iPhone and Apple Watch to crash and/or reboot. Apple announced...
-

 261Data Security
261Data SecurityThanks IRS for poor security: Financial Info On 100,000 Taxpayers Stolen
The IRS announced in an official statement today that it has closed down an online service to obtain tax records after sensing...
-

 190Geek
190GeekThis Smartphone app can be a potential life saver during earthquake
The earthquake measuring 7.8 on the Richter scale that hit Nepal on April 25 and caused 8000 plus casualties and rendered tens...
-
 338Geek
338GeekGetting Started With Linux : Part-1 (Choosing a Distribution)
There are hundreds of Linux distributions to choose from. Each of them has their merits. Some of them have their separate package...
-

 111Mobile Security
111Mobile SecurityHackers could track subway users via phone accelerometer data
Researchers from Nanjing University have found a way in which hackers could track a smartphone user on the subway - even when...
-

 299Banking
299BankingMobile banking security still a barrier for consumers
Customers are increasingly turning to mobile apps to make simple banking transactions, but a significant portion of those who don't bank on...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




