Featured News
-

 266Cyber Events
266Cyber EventsAnonymous Steals 1 Terabyte Passwords From Expo 2015 in Italy
Anonymous Italian attackers continue to haunt the Expo 2015 Universal Exposition being hosted in Milan as it faces an array of attacks...
-

 293Geek
293GeekL’Oreal joins forces with Bioprinting Company to 3D print human skin
In an attempt to suspend animal testing and upsurge lab-based skin production L’Oreal is going to 3D print human skin — That...
-

 105Password
105PasswordResearchers design ‘decoy password’ system to fool hackers
Researchers have developed a system to protect password databases, allowing hackers to believe they have cracked the file, only to be given...
-
 302Data Security
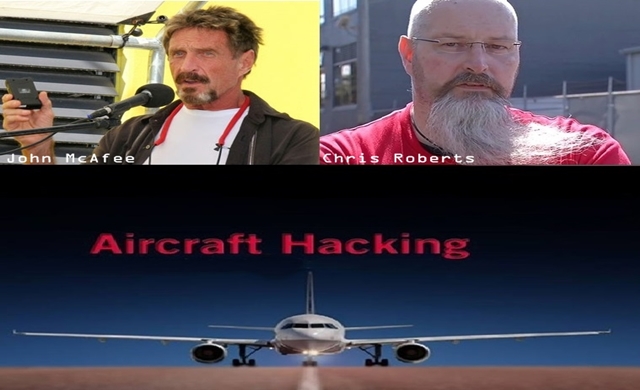
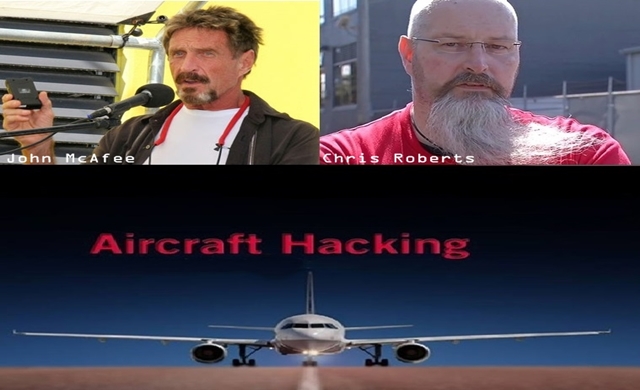
302Data SecurityJohn McAfee supports his pal who found security flaw, hacked an aircraft
Summary: An official statement issued by an FBI agent reveals that InfoSec researcher Chris Roberts has confessed to hacking into the controls of...
-

 216How To
216How ToHow To Stop Chrome From Killing Your Computer
There was a time when I loved my Chrome browser very much. But from the first day of my blogging life, when...
-

 323Cyber Crime
323Cyber CrimeChinese Woman Gives Birth in Internet Cafe, keeps on surfing Web
In an shocking news on Monday a woman from Shandong, China, gave birth to a daughter at an Internet café – and...
-

 292Reviews
292ReviewsReview of $29.39 Xiaomi Small Ants Smart IP Camera
Xiaomi is a very versatile company. We know of it as primarily a phone maker, but it does a lot of other...
-

 169Privacy
169PrivacyGoogle and Apple among tech giants urging Obama to block phone surveillance
Google and Apple have signed a letter to President Barack Obama urging him to reject any proposal that would grant police access...
-

 185Interview
185InterviewAryeh Goretsky talks “very promising” Windows 10 security
Windows expert Aryeh Goretsky discusses threats to Windows past, present and future. Will Windows 10 mean hackers have to work harder?
-

 181Data Security
181Data Security“Failure in Parcel Delivery” Fake Email Drops Malware on USPS Customers’ PC
Please note that the email that appears to be sent by USPS informing that due to incorrect address the firm has failed...
-

 324Geek
324GeekMan 3D prints a wirelessly power-driven desk lamp inspired by Tesla
It was more like a mission for engineer, David Choi, to 3D print something inspired by Nikola Tesla’s wireless power transmission something...
-

 164How To
164How ToHow To Capture Someone’s Picture Who Tries To Unlock Your Phone
Some things are better if kept private. I have seen many people hating it like anything when their friends or family members...
-

 206Anonymity
206AnonymityHow to Delete yourself from the Internet
Have you ever wondered what information web pages have on you? Just perform a simple google search and check out the results! You...
-

 282Cyber Crime
282Cyber CrimeRansomware attack forces animal porn collector to plead guilty to police
A UK man has been charged this week with a non-custodial sentence, after a ransomware infection on his computer made him confess...
-

 216Surveillance
216SurveillanceFingerprints will tell cops if you are high on cocaine
New Breakthrough suggests that Fingerprints will soon reveal to cops if suspects are High on cocaine. According to advancement in “drug test”...
-

 108Scams
108ScamsLove hurts: Online dating scams are Australia’s top financial fraud
Australians were tricked out of around AUS$82 million (US$66 million) during 2014, with online dating scams accounting for the biggest losses.
-

 106Privacy
106PrivacyUK government amends hacking laws to give intelligence service immunity
The British government has passed legislation amending the Computer Misuse Act to prevent GCHQ, the police and intelligence services from prosecution over...
-

 250Cyber Events
250Cyber EventsData of 18k Penn State University Folks affected in Chinese-led cyber attack
The officials at The Penn State College of Engineering announced that its servers were attacked in two “extremely sophisticated” cyber-attacks and as...
-

 307News
307NewsWayne County (Indiana) Sheriff’s Dept Website Defaced, Login Data Leaked
The online hacktivist AnonGhost just hacked, defaced the official website of Wayne Country Sheriff’s department and publicly leaked its database containing login...
-

 155Cyber Events
155Cyber EventsAnonymous Hacks Chile Govt in support of student protests, against police brutality
Anonymous hacktivist breached a government of Chile website and leaked login details of officials in support of student protests against the government’s...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets




