Featured News
-

 108Privacy
108PrivacyUK government amends hacking laws to give intelligence service immunity
The British government has passed legislation amending the Computer Misuse Act to prevent GCHQ, the police and intelligence services from prosecution over...
-

 251Cyber Events
251Cyber EventsData of 18k Penn State University Folks affected in Chinese-led cyber attack
The officials at The Penn State College of Engineering announced that its servers were attacked in two “extremely sophisticated” cyber-attacks and as...
-

 309News
309NewsWayne County (Indiana) Sheriff’s Dept Website Defaced, Login Data Leaked
The online hacktivist AnonGhost just hacked, defaced the official website of Wayne Country Sheriff’s department and publicly leaked its database containing login...
-

 157Cyber Events
157Cyber EventsAnonymous Hacks Chile Govt in support of student protests, against police brutality
Anonymous hacktivist breached a government of Chile website and leaked login details of officials in support of student protests against the government’s...
-
 215How To
215How ToFind Out What Your Name Would be if You Were Born Today
Our name is an integral part of our existence and this is our basic identity. But the way people name their children...
-
 255How To
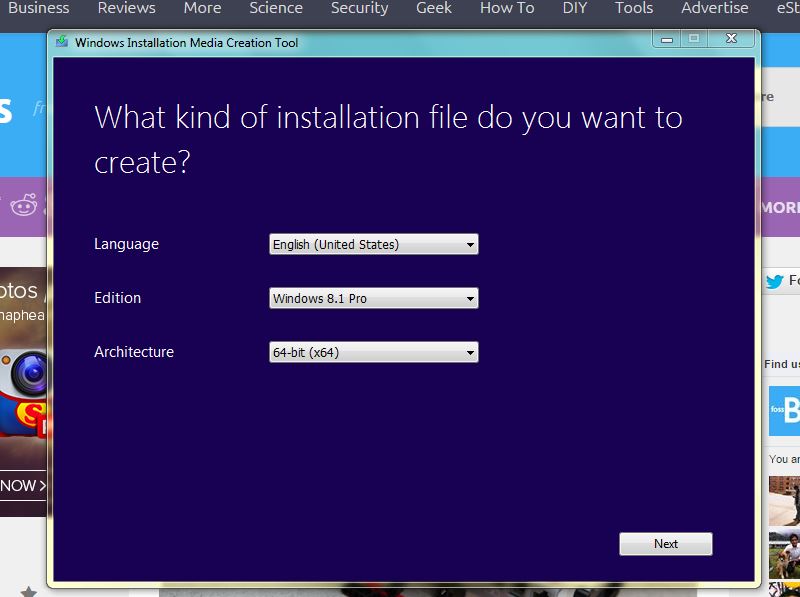
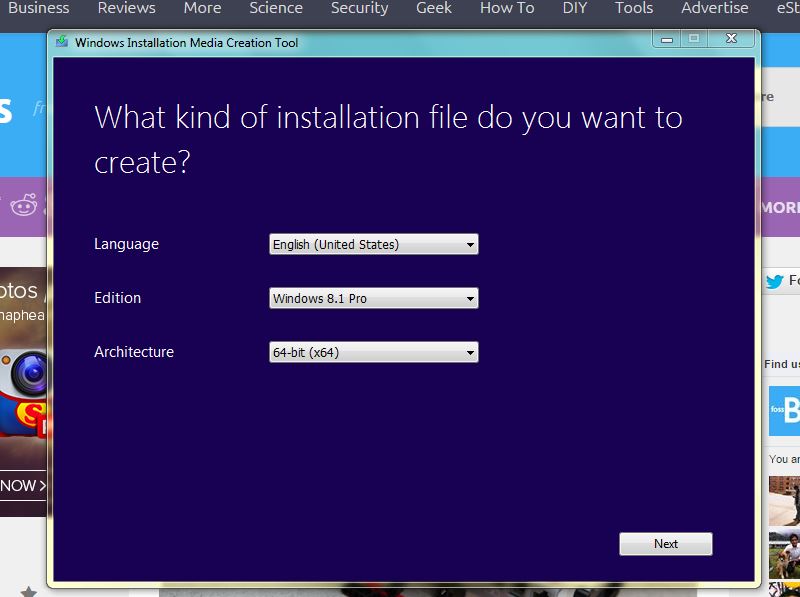
255How ToHow to Download Windows 8.1 Legally Without Product Key
Installing a fresh Windows 8.1 hasn’t been the easiest thing in the world till now as Windows 8 users needed a licensed...
-
 231Hacked
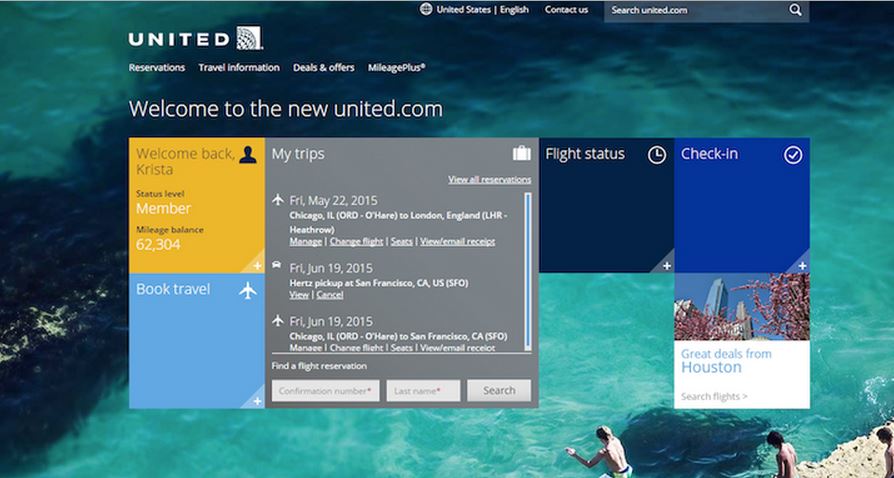
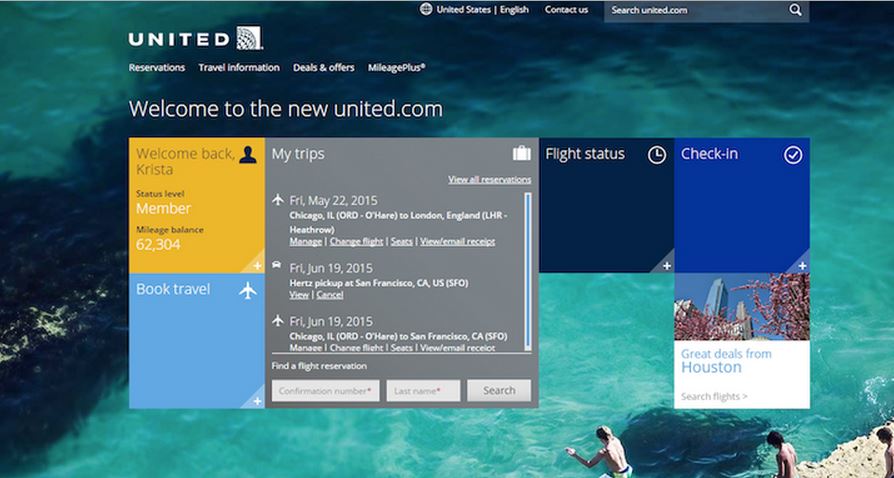
231HackedHack United Airlines Website and Get Paid in Million Miles
Are you good at programming and do you call yourself a computer expert? Here’s a chance to earn a million miles and...
-

 214Cyber Events
214Cyber EventsWhat is Enforced Transparency? A Western Trend?
The concept of Transparency carries a simple meaning, if practiced by governments it will empower the masses, place them in a position...
-
 274News
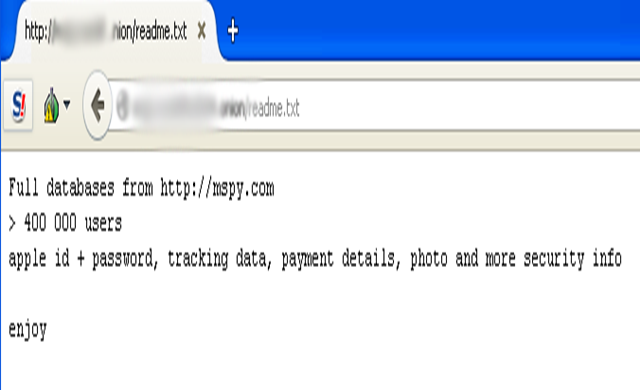
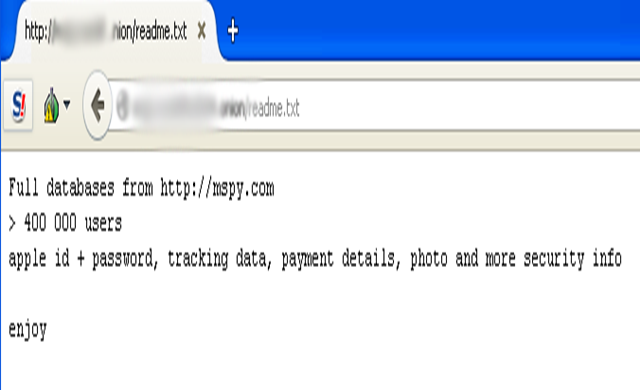
274NewsMobile Spy Software Maker mSpy Hacked, Personal data of 400k users leaked
mSpy, the notorious software-as-a-device product which so far enabled two million plus people spy on their spouses and kids, is believed to...
-

 202Tricks & How To's
202Tricks & How To'sLive Stream Twitch in VLC to avoid buffering
Twitch has been making some very awful encoding and additional bad choices for streamers and viewers of Twitch.tv. This method has been...
-

 196How To
196How ToFree Microsoft Office alternatives
Many people feel the need to use Torrents to pirate software that would normally be paid for, however by doing this torrent...
-

 215How To
215How To10 Games That Teach Kids To Code
In this world 36 million kids have taken part in Hour of code activities, by helping them to develop their skill in...
-

 104Cyber Crime
104Cyber CrimeA Compromised .GOV URL Hosting Phishing Attacks on Apple Users
A couple of months ago we reported how [linked url=”https://www.hackread.com/app-store-phishing-email-stealing-apple-user-credentials/”]an app store phishing email is stealing Apple user credentials[/linked]. Now a government of Vietnam domain...
-
 230Data Security
230Data SecurityWhatsApp users hit with ‘You Just Got an Audio Recording’ Email Malware
The email apparently is sent from the popular messaging service WhatsApp and claims that you have received an audio recording. A malicious...
-
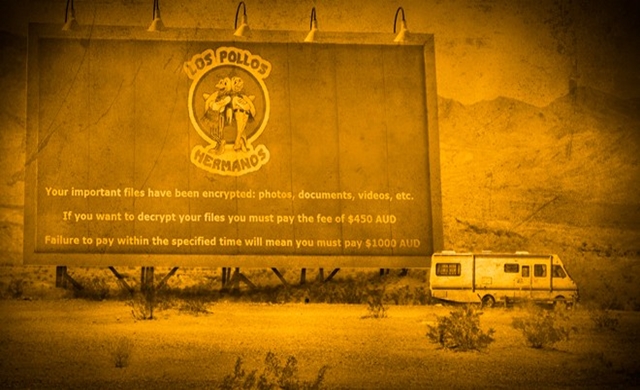
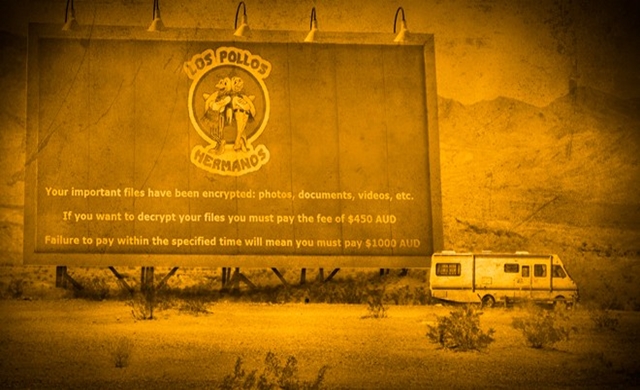 287Data Security
287Data SecurityInternet users hit with Breaking Bad Theme Crypto-Malware
To demonstrate their creativity cybercriminals have released a new ransomware equipped with file encryption abilities and this time they have chosen logo...
-

 94Privacy
94PrivacyApple seeks to block sale of RadioShack customer data
Apple has filed a court objection against the sale of RadioShack customer data for those who had purchased its products, reports Ars...
-
 199Interview
199InterviewHow did the Internet change the everyday work of a security researcher?
Aryeh Goretsky and David Harley talk to Sabrina Pagnotta about the internet's impact on security research.
-

 108Privacy
108PrivacyGoogle turns down 60 percent of ‘right to be forgotten’ requests
A year after Google introduced its controversial 'right to be forgotten' feature, the search giant has published some statistics about its implementation.
-
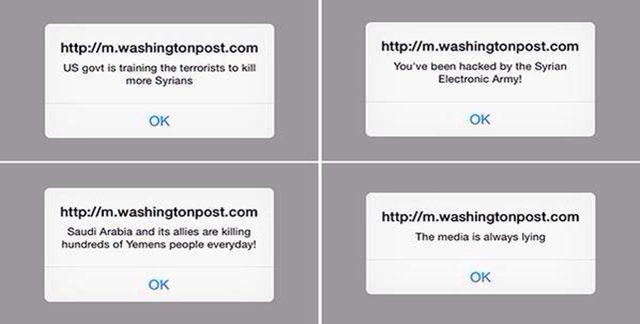
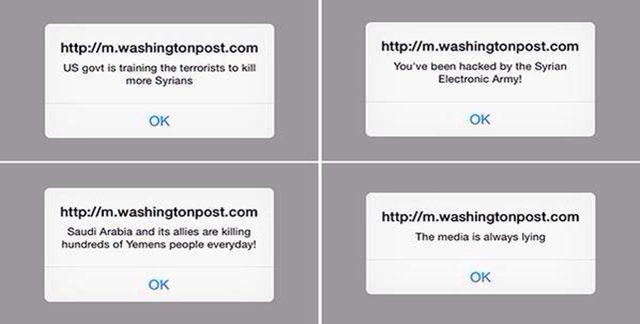 292News
292NewsSyrian Electronic Army Hacks Washington Post Mobile Site
The official mobile website of American daily newspaper The Washington Post was hacked by Syrian Electronic Army (SEA), a group loyal to Syrian President Bashar...
-

 351Data Security
351Data SecurityUnited Airlines Bug Bounty Program: Report Security Flaw, Get Rewards
If you are a hacker or an IT security researcher, United Airlines has announced its first ever Bug Bounty program for you...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




