Featured News
-

 224Geek
224GeekUbuntu 15.10 Codename Finally Announced: Wily Werewolf
If you are Linux enthusiast, you would be aware of the fact that a new Ubuntu release is soon followed by the...
-
 227Geek
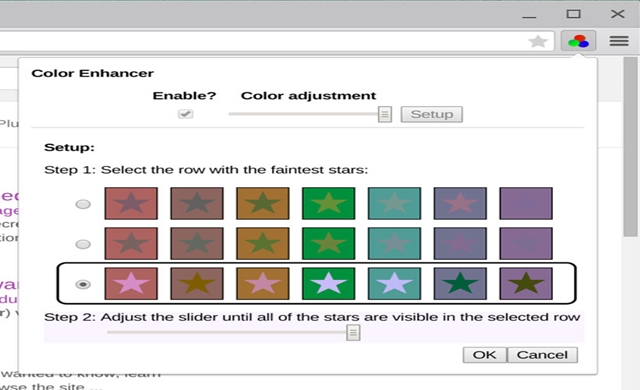
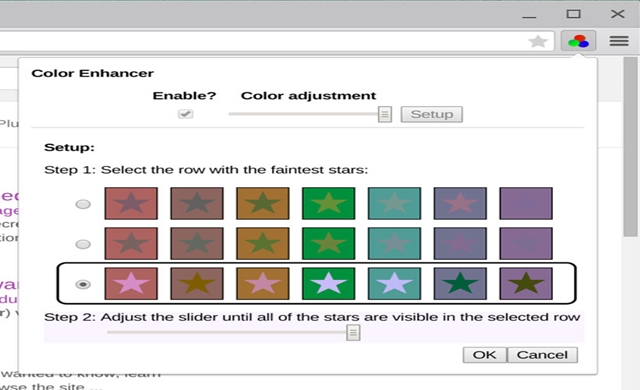
227GeekNow Color-Blind people can View Web– Thanks to New Chrome Extension
New Google Chrome extension helps color-blind users surf Internet without any problem. To pass the leisurely time, the Internet isn’t always one of the...
-

 172Surveillance
172SurveillanceUS Court rules NSA phone surveillance program illegal
A Three-judge panel of the Second Circuit Court of Appeals decided that the telephone metadata collection program of NSA is illegal under...
-

 265Data Security
265Data SecurityLenovo accused of ‘massive security risk’ by researchers
The IOActive researchers reported that Lenovo devices software has serious security flaws and vulnerabilities that can be easily exploited by cyber criminals...
-

 94Malware
94MalwareIs online voting a security risk?
The world is moving online and so too now is politics. But as online, electronic voting (e-voting) increasingly becomes reality, are we...
-

 75Cyber Crime
75Cyber CrimeThe big small business security challenge: mobile and BYOD
In this recorded webinar the security challenge that mobile devices and BYOD bring to the businesses, notably smaller businesses, is reviewed; then...
-

 78Malware
78MalwareCPL Malware in Brazil: somewhere between banking trojans and malicious emails
Not only is Brazil one of the most populated countries in the world, but it is also one of the countries with...
-
 128Hacked
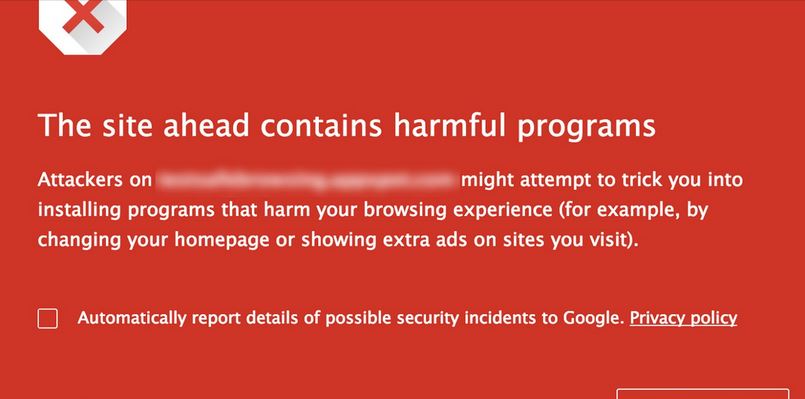
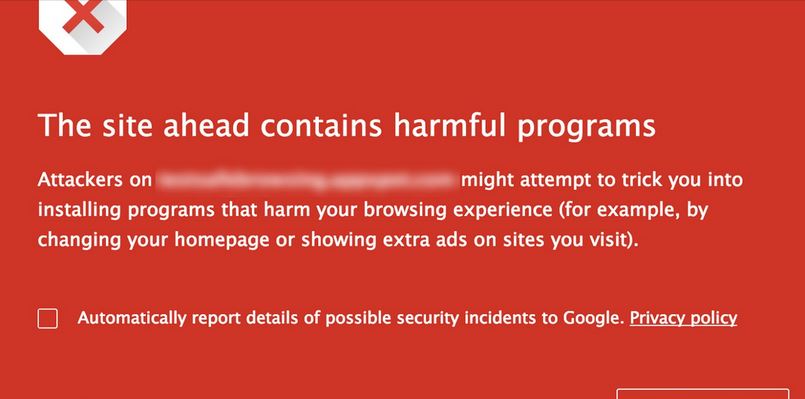
128HackedGoogle Says Ad Injecting Malware Affecting Millions of Users
Google’s recent study shows the effect of the Ad Injection in our digital media. We already know and hate the ad frauds,...
-
 225Cyber Crime
225Cyber CrimeApple users hit with KYC Validation/iCloud ID review phishing scam
A fake email supposedly sent by ‘Apple Genius Assistance’ informs that users need to review their Apple ID information within 2 days...
-
 192Data Security
192Data SecurityThis New Rombertik Malware Crashes Your PC Once Detected
A complex malware dubbed as Rombertik has been designed to steal user data and comprises of several layers of anti-analysis functionality and...
-

 369Surveillance
369SurveillanceSnowden documents show how NSA converts Audio calls into searchable data
A new Edward Snowden document released by The Intercept describes the way NSA converted voice calls into searchable text files for about...
-

 95Privacy
95PrivacySecurity concerns prompts ‘gold rush’ for Chinese enterprise computing market
Concern over the security of Windows in China has led to a 'gold rush', as Chinese firms race to fill the gap...
-

 79Malware
79MalwareRombertik: the malware that ‘destroys’ computers if detected
Researchers have uncovered a new malware which will try to 'destroy' the computer, reports Cisco. Let's understand how it really is.
-

 246Geek
246GeekNew iPhone case charges your phone battery without being plugged in
Nikola Labs has launched an iPhone case that transforms radio frequencies into DC electrical current and thus, can charge devices. The first device...
-

 118Mobile Security
118Mobile SecurityNo iOS Zone, the vulnerability that enables DoS attacks on Apple devices
Two researchers surprised people by demonstrating how they could carry out a denial of service (DoS) attack on iOS devices.
-
 240Hacked
240HackedBeware Rombertik, This “Suicide Virus” Destroys Your PC If Detected
Cyber criminals and security researchers face each other each day in a never ending battle. Both are two sides of a single...
-

 86Cyber Crime
86Cyber CrimeAustralian game hacker flees to Europe before trial
An Australian man facing 25 hacking charges has fled to Europe, ahead of being trialled for attacks which targeted major computer firms.
-
 260Cyber Events
260Cyber EventsGitHub website is down – Turkish hackers claim they did it
GitHub, the web-based Git repository hosting service is down right now and Turkish hackers from Turk Hack Team claim they are behind this attack....
-

 243Opinion
243OpinionSmartphone Authentication: the Passing of the Passcode?
Smartphone authentication: is biometric technology ready to replace PINs and passwords?
-

 296News
296NewsBrazilian MMA, UFC Fighter Vitor Belfort’s Website Hacked
You may be a UFC champ in real life but when it comes to online world, hackers have an upper hand. A group...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




