Featured News
-

 407Malware
407MalwareNew malware ‘Punkey’ detected in new point‑of‑sale attack
A new advanced malware program targeting point-of-sale terminals is putting customer credit card details at risk, following a number of similar attacks...
-

 332Data Security
332Data SecurityXSS Vulnerability Found in Famous WordPress Plugins
Researchers have identified a relatively “common” cross-site scripting flaw (XSS) in some famous WordPress plugins — A coordinated plugin update has been released to...
-

 271Hacked
271HackedHow New Zealand and NSA Plotted Hack on China
China’s foreign ministry has expressed serious concerns over the reports of hacking attacks on China planned by New Zealand and NSA in recent...
-

 418Mobile Security
418Mobile Security1,500 iOS apps open to simple man‑in‑the‑middle attacks
Around 1,500 apps for iPhone and iPad contain an HTTPS vulnerability making it 'trivial' for hackers to perform man-in-the-middle attacks to steal...
-

 280News
280NewsAnonymous Hacks Israeli Arms Importer Site, Leaks Massive Client Login Data
Online hacktivist Anonymous has breached into the website of an Israeli arm importer and manufacture Fab-Defanse (fab-defense.com) and leaked login credentials plus personal...
-

 273Data Security
273Data SecurityFlash Player Bug Records Audio and Video without User Permission
Researchers have identified a vulnerability in some Adobe Flash Player versions that can be exploited by attackers for spying on users having...
-

 530How To
530How ToGoogle Now Lets You Download Your Entire Search History, Here is How To Do This
image: Lifehacker Google now allows you to export and download your entire search history in no time. Last year Google tested a...
-
 275Cyber Events
275Cyber EventsBrazil will sue Facebook for blocking picture of indigenous woman
Brazilian Ministry of Culture is planning to sue Facebook on blocking the picture of an Indian woman from 1909 just because her...
-
 318Geek
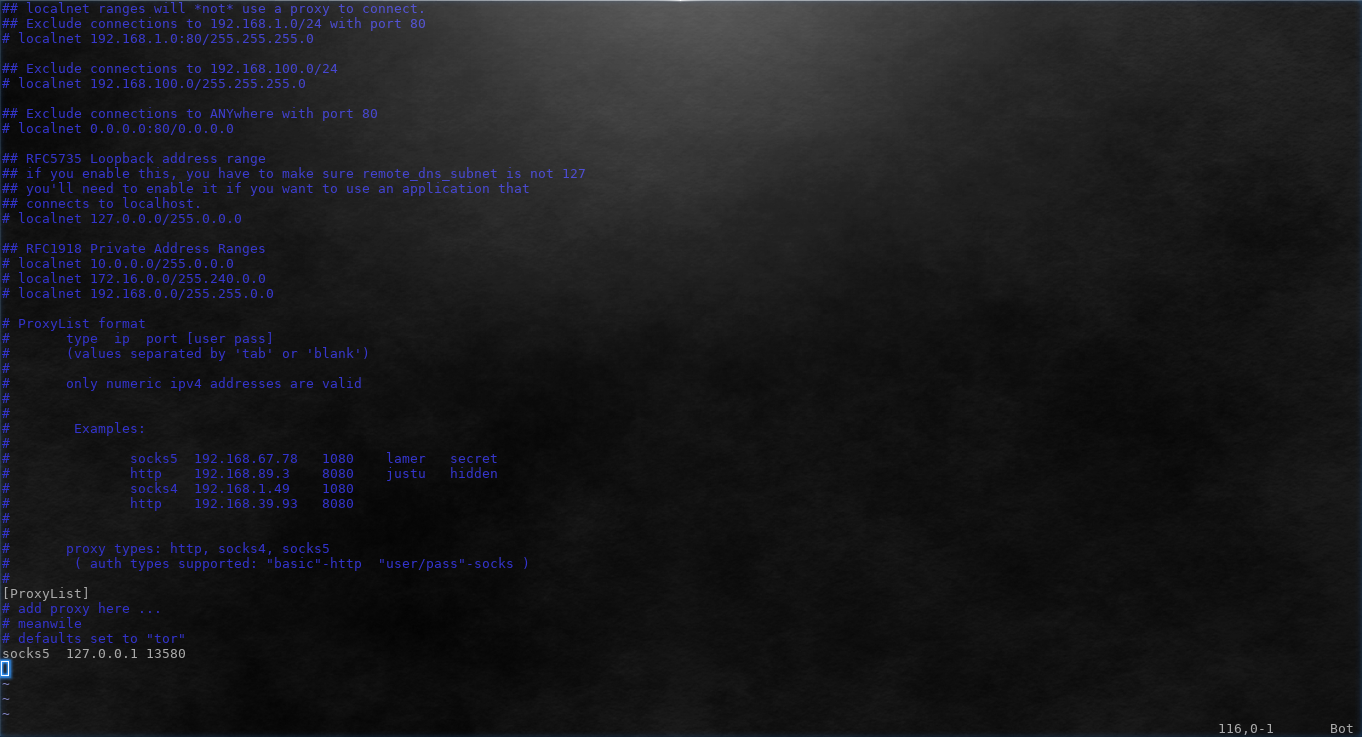
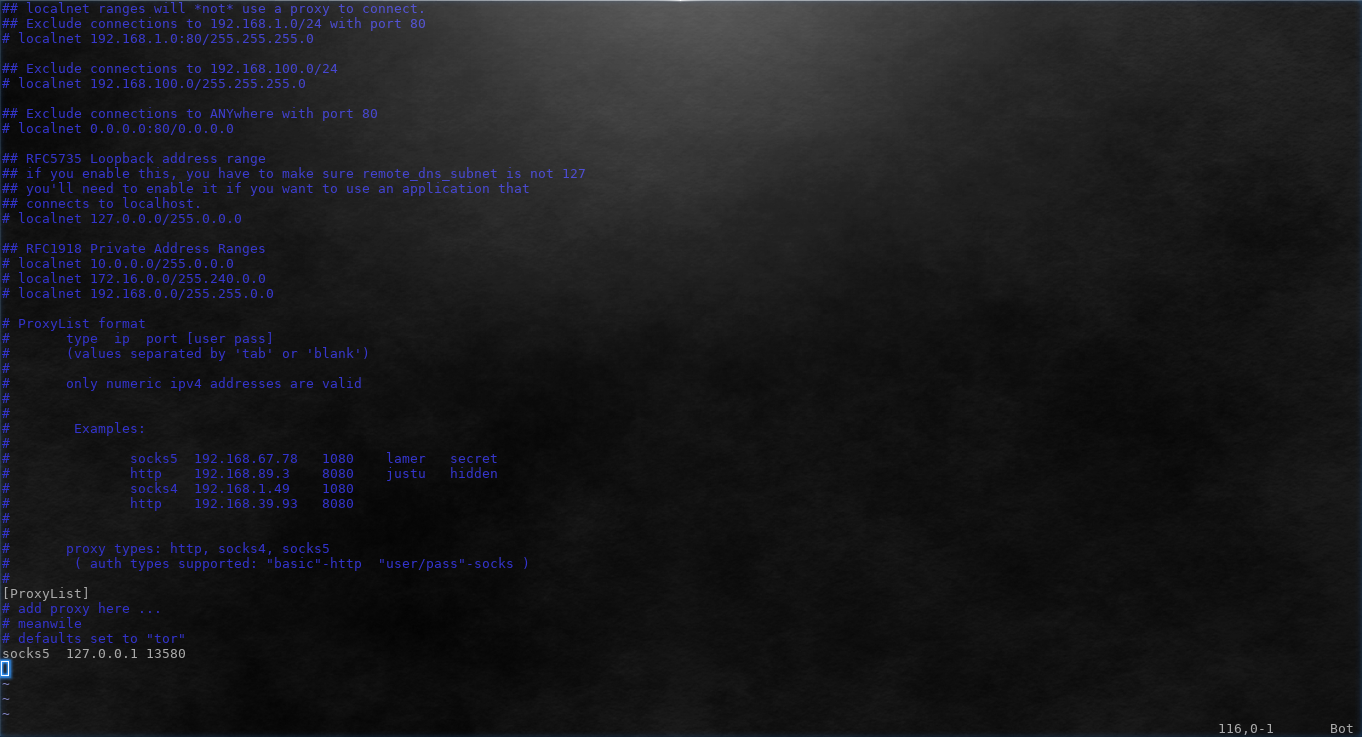
318GeekHow to Use Proxychains to Run Applications Behind Proxy
Some applications do not support proxy by default. Other applications might support HTTP proxy but fail when using SOCKS. As Tor provides...
-

 78Cyber Crime
78Cyber CrimeAustralian infosec body lobbies for mandatory security baseline
Australia's infosec industry is lobbying for a mandatory security baseline to ensure basic IT standards are met across the country, with penalties...
-

 186Cyber Crime
186Cyber CrimeTarget agrees to $19 million data breach settlement with MasterCard
Target has ended its dispute with MasterCard over the retail giant's 2013 data breach by agreeing to a $19 million reimbursement to...
-
 212Tricks & How To's
212Tricks & How To'sHow to find out if you’ve been HACKED with CMD
There are numerous methods to see if you have been hacked. Using the Command Prompt, you can run a command which will...
-

 229Data Security
229Data SecurityMan who revealed plane can be hacked offloaded for the second time
Earlier this week the FBI denied air travel to Chris Roberts due to his sarcastic tweets about United Airlines’ security system on...
-
 306Cyber Crime
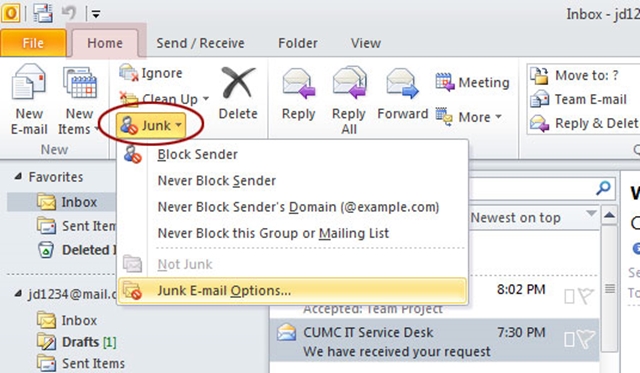
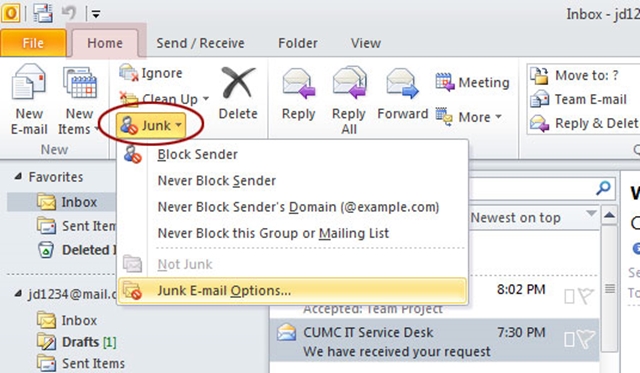
306Cyber CrimeMicrosoft Outlook Users Hit with ‘Discontinue Support’ Phishing Scam
‘Discontinue Support’—Latest Phishing Scam Targeting Microsoft Outlook Users. An email is being circulated by cybercriminals that appears to be sent by Outlook.com...
-

 385How To
385How ToHow To Enable YouTube’s Transparent Player
I think we all agree that YouTube is the best place to watch online videos, and this is why it is world...
-
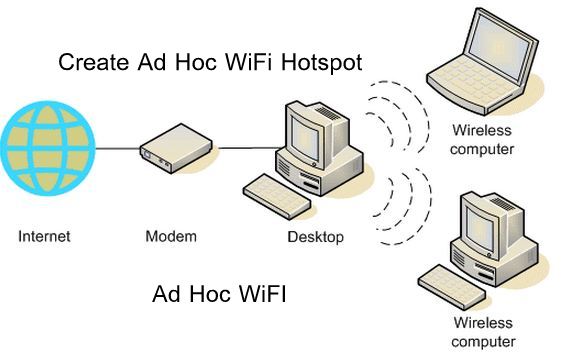
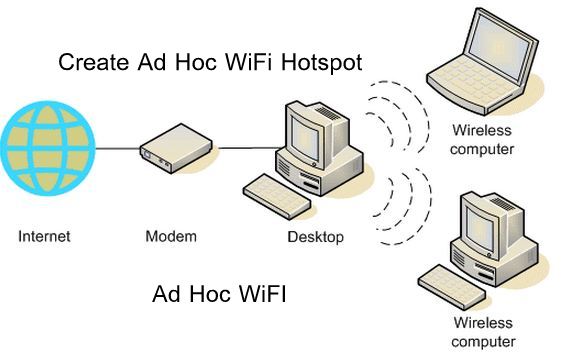 167How To
167How ToHow to Connect to Ad Hoc WiFi Network in Windows 8.1
Having Windows 8.1 and then connecting to a wireless network, sometimes it may create some problems. Well I use Ubuntu most of...
-

 277News
277NewsTOP 100 Unique sites
These sites solve at least one problem really well and they all have simple web addresses(URLs) that you can easily memorize thus...
-

 231IOS Hacking
231IOS HackingHow to Check If A Used iPhone Is Stolen
Apple attempted to address this issue with the Find My iPhone service in 2010, but that could be defeated by turning the...
-

 320Cyber Events
320Cyber EventsAnonymous Hacks and Removes X-Rated Animal Abuse Websites
Anonymous hackers have started a new operation under the banner of #OpNullDenmark and #OpBEAST. The purpose of this operation is to raise awareness...
-

 120Cyber Events
120Cyber EventsU.S Military to hire civilian cybersecurity specialists
If you are a cybersecurity specialist then U.S Military is ready to hire you. Lt. Gen Cordon announced that U.S Military is planning...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




