Featured News
-

 236Geek
236GeekMicrosoft Launches .NET Core Preview For Linux and Mac Users
Source: TechCrunch From Last November, Microsoft was teasing its developers by saying that some of the key features for Microsoft .NET platform...
-
 307Geek
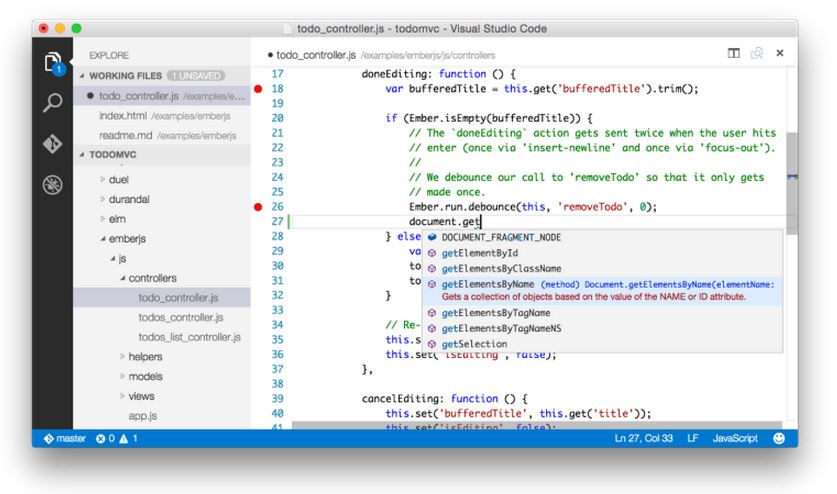
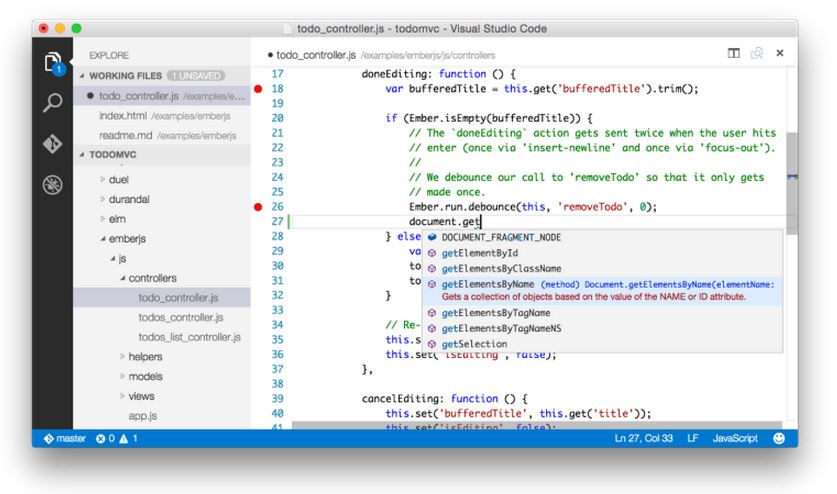
307GeekMicrosoft Releases Free Visual Studio Code for Windows, Mac and Linux
Microsoft released a new development tool – Visual Studio Code – that works Windows, Linux, and Mac. This is being seen as...
-
 165Surveillance
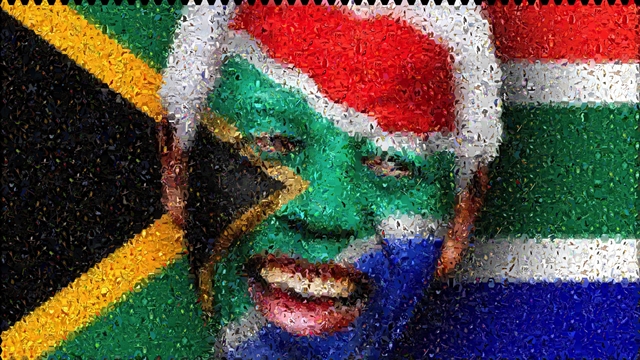
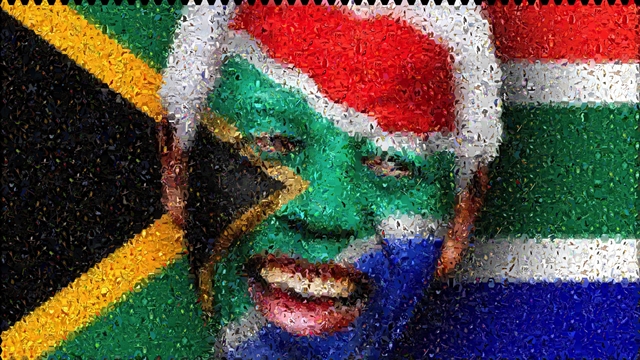
165SurveillanceSouth African Government Spying on its Citizens- Report
The South African Right2Know campaign has released its “Big Brother Exposed” report. The report revealed details about the way activists and community leaders...
-

 179Hacked
179HackedHow a Hacker Hacked PayPal by Remote Code Execution Vulnerability
Today even the big financial players like PayPal, who are expected to deliver secured services to its users, aren’t safe from the...
-

 132Geek
132GeekNew Samsung App Assists Alzheimer’s Patients Remember Their Loved Ones
The importance of a Smartphone was redefined when Azer Jaafoura along with his team members thought about helping Alzheimer’s patients a year...
-
 207Hacked
207HackedChina Attacks on Facebook Using The Great Cannon
For the past few days, we have been hearing about the Great Cannon. This Great firewall system developed by China is terrorizing the...
-

 363News
363NewsMasterCard Website Hacked by Indonesian Hackers
On 25th April, 2015, Indonesian hackers going with the group handle of Gantengers Crew hacked and defaced the Online Resources domain of US based Financial Services...
-
 109Hacked
109HackedYahoo’s Bodyprint Can Unlock Your Smartphone Using Your Ear
You will not need your fingerprints or the face-detection feature of your phone very soon to ensure that your tablet or smartphone...
-

 253Data Security
253Data SecurityResearchers show how medical robots can be hacked during surgery
University of Washington in Seattle’s research team managed to hijack a tele-operated surgical robot. This exposed major security vulnerabilities in machines that...
-

 168Cyber Crime
168Cyber CrimePolice bust hackers who stole $15 million from 24 countries
Twenty five international cyber criminals (who were involved hacking into banking systems and making of clone payment cards) are arrested by the...
-

 339How To
339How ToHow To Run Android Apps In Chrome Browser Using Google ARC
Now Google lets you run your Android apps in Chrome with its ARC Welder app. They recently released the beta version of...
-

 116Cyber Crime
116Cyber CrimeOFAC! An acronym that cybersecurity professionals need to know
OFAC will soon be enforcing economic and trade sanctions against individuals and groups outside the United States that use cyber attacks to...
-

 368Cyber Crime
368Cyber CrimeThe curious case of the ex‑hacker “banned from the internet”
What kind of punishment best fits a convicted hacker? Jail time for serious computer crimes is almost a certainty, but for one...
-

 222How To
222How ToMake Your Own Simplest Electric Train
Have you ever thought of making some cool stuff at home? Well if not, you are about to learn how to make an electric...
-

 207Geek
207GeekGoogle wants to be your wireless carrier with encrypted connection
For all of you who want to know what currently Google is planning to work on, the answer is “Project Fi”— Now...
-
 455Hacked
455HackedHow to Stop Google From Tracking You in Few Simple Steps
Privacy is one of the biggest concern to everyone these days, and to respect your privacy, few days ago Google enabled the option...
-
 301Hacked
301HackedHow to Detect NSA’s Complex “Quantum Insert” Attacks
In the past, whistleblower Edward Snowden has exposed numerous hacking operations run by the US intelligence agency NSA. Out of all these...
-

 95Malware
95MalwareWattsUpDoc: US hospitals trial AC power probes to treat medical malware
Two major hospitals in the United States are trialling a new system for detecting malware on medical devices, using probes that monitor...
-

 216Hacking Tutorials
216Hacking TutorialsHow to protect yourself against Phishing
Phishing is the method of stealing login info(usernames and passwords) by directing the victim to a clone(fake) login page, that logs the...
-

 96Cyber Crime
96Cyber CrimeThirty Meter Telescope website falls over in hacktivist DDoS attack
Hacktivists have launched a distributed denial-of-service attack against the website of TMT (Thirty Meter Telescope), which is planned to be the Northern...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




