Featured News
-

 94Cyber Crime
94Cyber CrimeFour Mortal Kombat moves cybercriminals use to attack your security
Some of the tricks employed by the characters in the Mortal Kombat series aren't a million miles away from those deployed by...
-

 237Cyber Crime
237Cyber CrimeThis Dude Hacked Lottery Computers to Win $14.3M Jackpot in U.S.
Former security director suspected for tampering with lottery computers to win $14.3m Jackpot. According to prosecutors there is strong evidence suggesting that...
-

 74Cyber Crime
74Cyber CrimeDutch government to launch Global Forum on Cyber Expertise
The Dutch government is to launch the Global Forum on Cyber Expertise, with the intention of capacity building in the fields of...
-

 223News
223NewsGoogle Malaysia Domain Hacked by Bangladeshi hacker
A Bangladeshi hacker (going with the handle of Tiger M@te) hacked the official Google Malaysia domain earlier today and redirected it to...
-

 254Scams
254ScamsTech Support Scammers with Teeth
Some support scammers and their assassination threats may seem dumb, but they're no joke.They can cause serious damage as we discuss it...
-
 256Cyber Events
256Cyber EventsHackers Shut Down Vatican City Website Against Pope’s Comment
Turkish hacker shutdown Vatican City official website against Pope Francis’ remarks in which he used the word ‘genocide’ to refer to mass...
-

 244Surveillance
244SurveillanceNSA Wants Tech Giants to give it ‘Front Door’ access to your encrypted data
The National Security Agency wants tech companies to provide it a front door access to your data so it can spy on millions of Americans...
-

 368How To
368How ToHow To Download SoundCloud Songs for Free
Hello, fossBytes readers! As many of you are already familiar with the fact that I frequently write how-to articles, I keep on...
-

 297News
297NewsIran’ State TV Social Media Accounts Hacked by Pro-Saudi Hackers
Hackers took over the official Twitter account of Iran’s state Television ‘Al-Alam’ on Sunday, leaving material supportive of the Saudi-led air war against Iran-backed...
-

 277Hacked
277HackedAnonymous Wants to Completely Erase ISIS from the Internet
Anonymous, the international association of hacktivists, has been fighting with ISIS and aiming to take down its presence from the internet. Hacktivist...
-

 223Geek
223GeekFilipino maid rescued from alleged rapist after Facebook plea goes viral
A 28-year-old woman from Philippines who was working as a maid at a house in Bahrain used Facebook to spread the message about...
-

 252Hacked
252HackedHacking Software Used in Sony Pictures Hack is Available Online for Everyone
Remember last year’s cyber-attack on Sony Pictures? The attack is yet to fade from people’s memory and now researchers have pointed out...
-

 160Data Security
160Data SecurityTens of Thousands of IPs still Vulnerable to New Shellshock Worm
Security researchers have identified a new malicious operation that can enchain hosts helpless against the Shellshock bash bug. It is the default...
-

 78Cyber Crime
78Cyber CrimeAustralian government issues warning over ‘ISIS hacks’
Australia's federal government has issued a warning over the spate of recent website hacks claiming to have links with extremist group ISIS.
-
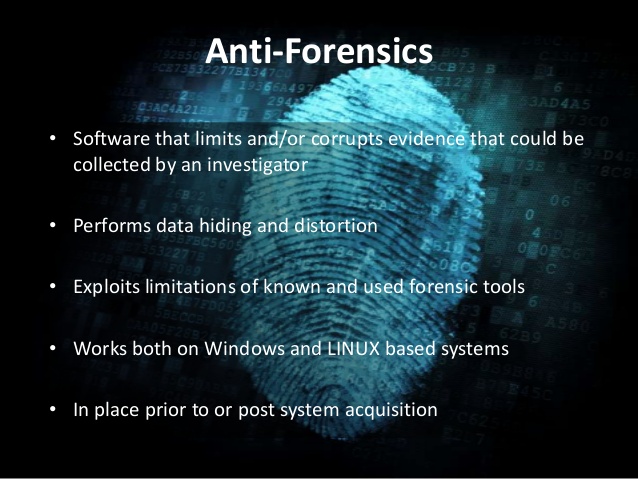
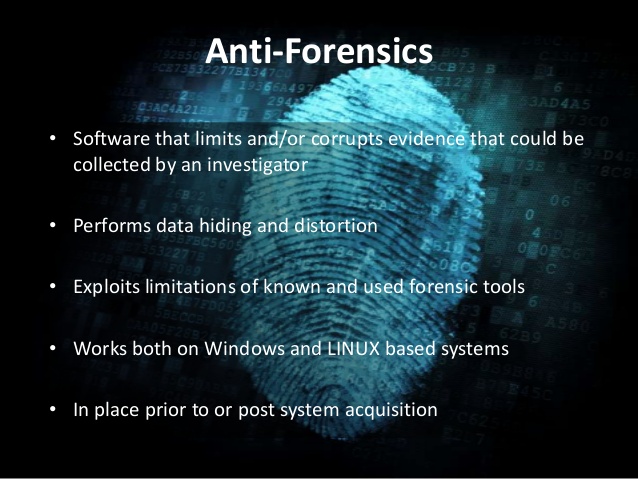 264Computer Forensics
264Computer ForensicsComplete Guide to Anti-Forensics – Leave no trace
The average personal computer is a security nightmare ,but what if i were to tell you there was a way around this,...
-

 225Cyber Events
225Cyber EventsSOPA & PIPA Act — Pakistan’s Bizarre Approach to Counter Cyber Terrorism
If you thought only the United State government loves censorship, you are wrong — Here are some shocking revelations about Pakistani Sopa & PIPA. Cyber...
-
 208Data Security
208Data SecurityThe Pirate Bay is down, Reason: Game of Thrones fans? (Update)
It seems that after the Police bust on The Pirate Bay last year, the domain has habit to go down often. Yes,...
-

 122Cyber Events
122Cyber EventsAnonymous Shuts Down Montreal Police Site Against Brutality on Student Demo
The infamous online hacker group Anonymous’ Quebec branch has taken the credit for penetrating the Montreal Police department website and the officers’...
-
 326Data Security
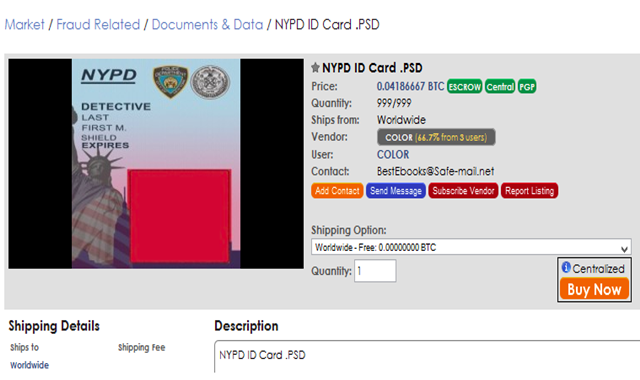
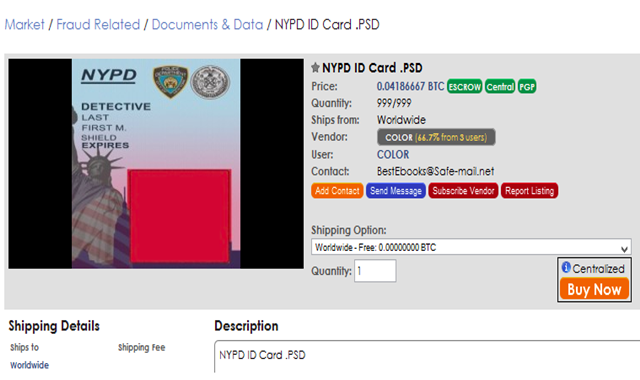
326Data SecurityStolen Accounts and Bogus NYPD Badges for Sale at Dark Web Marketplaces
Dark web marketplaces are famous for their pharmaceuticals and weapons souks but nowadays a lot more variety has been lurking there than...
-

 264Cyber Crime
264Cyber CrimeServers Having Standardized Test Information Hacked by a 14-year-old Student
Domanik Green, a 14-year-old student studying at Florida’s Paul R. Smith Middle School managed to bypass the school’s computer security network using...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




