Featured News
-

 379Cyber Events
379Cyber Events‘Great Cannon’ of China Blocks Websites Like No One Else Can
China to Use Stronger Weapons to Censor the Web and it is called Great Cannon — It can block websites and interrupt...
-

 318Cyber Crime
318Cyber CrimePolice Dept. in Massachusetts Paid Crypto-Malware Ransom to Retrieve Files
Ransomware equipped with encryption capabilities has been victimizing police departments rather indiscriminately nowadays. Although paying ransom to hackers is not recommended because it...
-
 334Geek
334GeekLinux Windows Dual Boot and More: Multi-booting Up to Five OS
Feels good to have lots of options to choose from, right? Then why stick to just one Operating System for a lifetime,...
-

 441News
441NewsOpIsrael: Anonymous Hacks Israeli Arms Importer Website, Leaks Thousands of Login Data
Online hacktivist Anonymous has breached into an Israeli gun shop website (lhbltd.com) and leaked login credentials plus personal details of its local and...
-

 338Cyber Events
338Cyber EventsDid ISIS Hack BBC the same day it took over France’ TV5Monde?
Is ISIS Behind BBC’s ‘Operational error’ that Interrupted its Broadcast and Left presenter flustered? Supposedly, BBC News Channel fell prey to a...
-
 284Geek
284GeekHey Developers, Now You Can Use Machine Learning Easily With Amazon
Following the footsteps of Microsoft, Amazon has launched its first product for machine learning service. At the AWS Summit in San Francisco,...
-

 123Surveillance
123SurveillanceIndian Police to Shoot Protesters with Pepper Spray Equipped Drones
In order to disperse protesters, Police in India will now use drones equipped with pepper spray. Is it possible to register police...
-

 285Surveillance
285SurveillanceFacebook accepts tracking non-users, claims a ‘bug’ made it happened
Facebook can Track Non-Users through ‘a bug’ — Working to fix it as fast as possible. Researchers at Facebook identified a “bug”...
-

 283News
283NewsOperationChina: Anonymous Hacks Chinese Police, Govt. Websites
Anonymous hacked several Chinese government websites including the Hunan (a province in China) Police Academy website in solidarity with pro-democracy protesters in Hong Kong....
-

 222Surveillance
222SurveillanceInteresting Facts about NSA Spying Tactics Exposed by CanTheySeeMyDick.com
The Internet was lit up by John Oliver’s interview with Edward Snowden since the host actually managed to make his chat subject...
-

 278Cyber Events
278Cyber EventsPrison Guards Quit Job After Beaten Inmate Photo Went Viral on Facebook
Two officers from Georgia’s correction facility had to resign when the picture of a beaten teen inmate having a leash bent around...
-

 330Surveillance
330SurveillanceFacebook Sued for Gathering World’s Biggest Stock of facial-recognition data
Facebook is back in the news, this time again for violating its users’ privacy by gathering a huge mass of facial data. A class-action...
-

 234Hacked
234HackedRunning a WordPress Website? Know How to Protect Yourself from ISIS Hacks
The US Federal Bureau of Investigation (FBI) has warned the WordPress users and urged them to patch their plugins of the content...
-

 205Data Security
205Data SecurityHackers Target Bank Customers with ‘Morning Update’ Malware Email
Australia’s Bendigo Bank is apparently sending out emails titled “Morning Update” to users. The email contains the staff member’s name as well...
-

 320News
320NewsOpIsrael: Pro-Palestine hackers stole Israeli credit cards to fund charities
AnonGhost hacktivist group’s leader and founder, Mauritania Attacker, revealed on Tuesday that his team has funded Palestinian charities through stolen Israeli credit...
-
 107Privacy
107PrivacyYour identity has already been stolen, ‘Catch Me If You Can’ subject warns US citizens
The reformed conman that the 2002 film 'Catch Me If You Can' is based on has told The Times that anyone living...
-

 199Privacy
199PrivacyGoogle pulls Chrome screenshot extension, after it leaks personal data
A Chrome extension designed for taking and annotating screenshots has been found to be leaking sensitive data from its 1.2 million users.
-
 296Geek
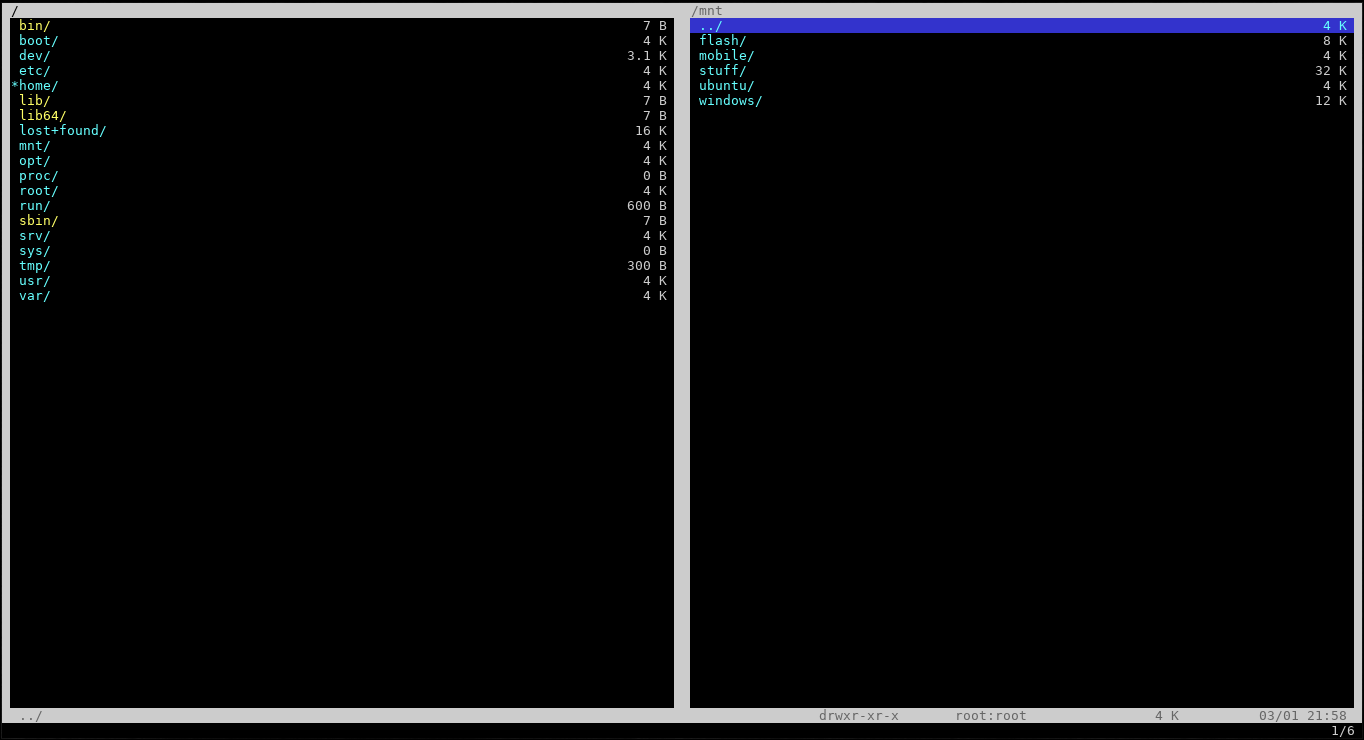
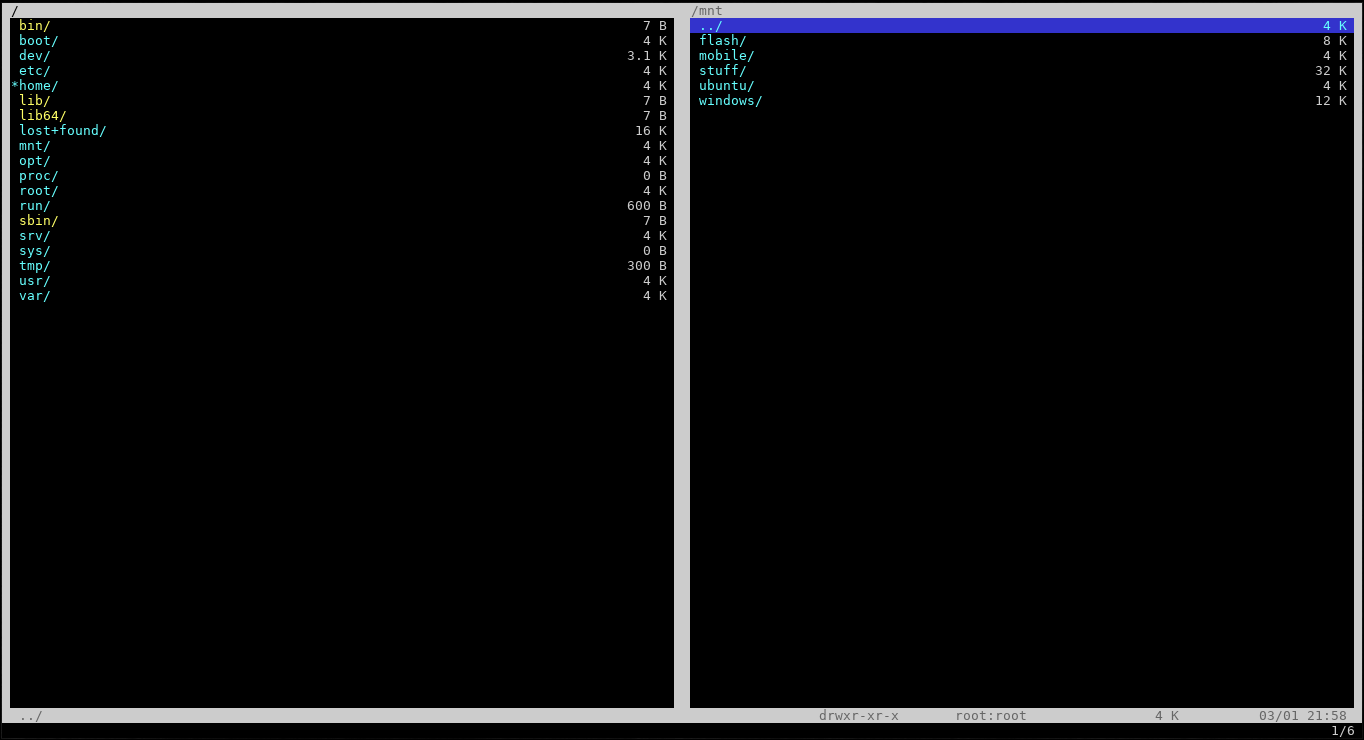
296GeekVifm – A Simple and Powerful Text Based File Manager for GNU/Linux
Vifm What is Vifm (Vi File Manager)? Vifm is a ncurses library based file manager for Linux which allows you to perform almost...
-
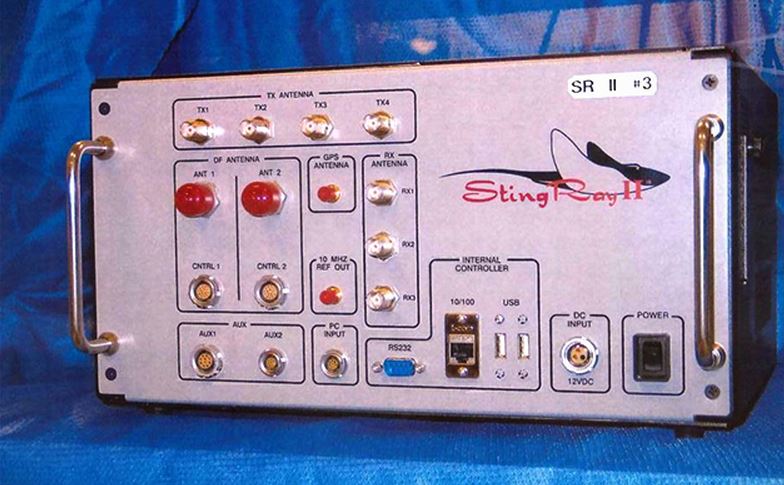
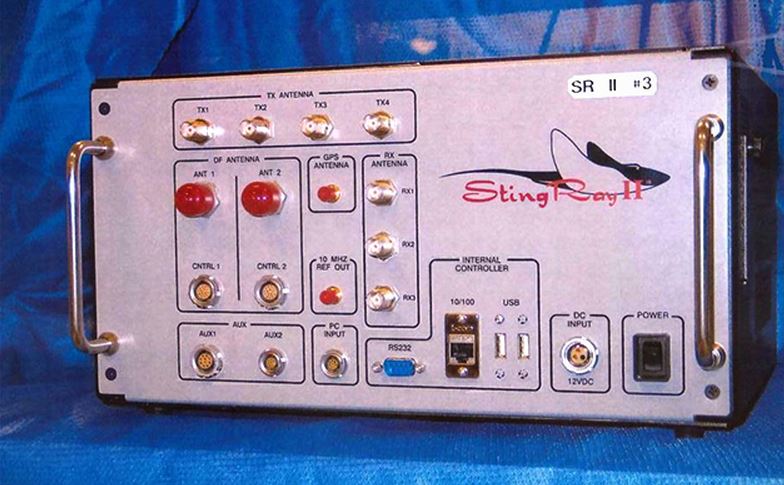 182Hacked
182HackedHere’s the Cell Phone Spy Tool Cops Are Using Without Warrant
So everyone knows that the big federal agencies and organizations like CIA, NSA and FBI are the one indulged in the mass...
-

 302Malware
302MalwareOperation Buhtrap, the trap for Russian accountants
The Operation Buhtrap campaign targets a wide range of Russian banks, used several different code signing certificates and implements evasive methods to...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




