Featured News
-

 118Mobile Security
118Mobile SecurityMobile security: IBM/Ponemon study finds enterprise app security weaknesses
Nearly 40 percent of large companies - including a significant number in the Fortune 500 - are not taking necessary precautions to...
-

 383Password
383PasswordTwitch backs down on 20‑character passwords in wake of hacking
Twitch has backed down on its attempts to force stronger password complexity on its site post-hacking, after multiple complaints from its userbase.
-

 267Hacking
267HackingFive hacker movies that got things badly wrong
5 hacker movies that got computer security well off the mark.
-

 95Privacy
95PrivacyHilton HHonors accounts put at risk of hijacking through simple web flaw
Security researchers discovered a vulnerability on the Hilton HHonors website, making it straightforward to hijack any other user's account.
-

 162Hacked
162HackedThousands of Popular iOS and Android Apps Still Vulnerable to FREAK
While whole world was worried about the FREAK vulnerability of the browsers, hundreds of popular apps of Android and iOS are still...
-
 291Hacking Tutorials
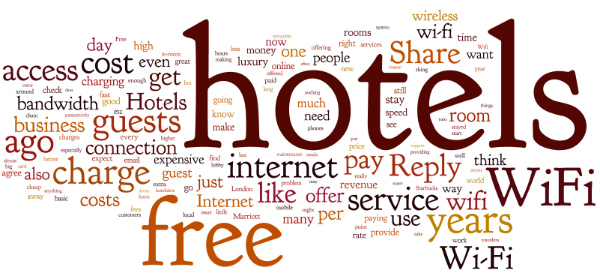
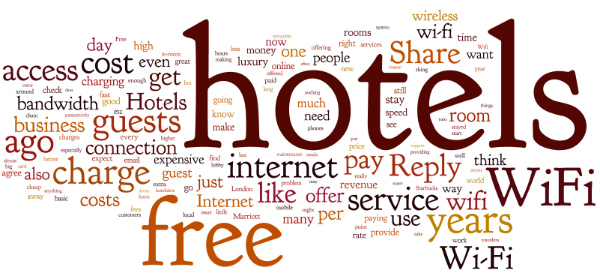
291Hacking TutorialsHow to hack a Hotel’s Wifi
Firstly, i would ask you whether or not you have had this situation before? Where for instance ,your phone is connected to...
-
 223Geek
223GeekFacebook Developer Tool for Slow Network App Testing is Now Open Source
Back in the year 2013, Facebook developed a tool to test its apps on slow connections named Augmented Traffic Control. Everyone is...
-

 193Tricks & How To's
193Tricks & How To'sHow to find a Wifi password with CMD
So, first start CMD. Most of the time CMD is built-in on the computer. Opened up CMD? Good. Now let’s go and...
-

 216Cyber Events
216Cyber EventsAnonymous Targets NYPD Captains Union Website with Malware
On Friday, a cyberattack on NYPD captains union website infected it with malware and forced it to shut down. According to union...
-

 194Malware
194MalwareMillions of computers left vulnerable to BIOS chip hack
A vulnerability has been detected in the BIOS chips found in millions of computers which could leave users open to hacking.
-

 151Privacy
151PrivacyCisco vulnerability could allow attackers to eavesdrop on private conversations
A vulnerability in Cisco's SPA300 and SPA500 IP phones could allow hackers to eavesdrop on private conversations from anywhere in the world,...
-

 254Data Security
254Data SecurityNew Snowden Documents Expose Canada’s Hidden Cyber Warfare Strength
On Monday, CBC News and The Intercept collaboratively disclosed for the very first time how Canada has endorsed aggressive strategies for attacking,...
-

 123Hack Tools
123Hack ToolsDecrypting a whatsapp account (Crypt7/8)
Use Whatsapp with Someone else’ number , this hack works by tricking the WhatsApp Verification Servers by receiving sms by a spoofer...
-

 91Surveillance
91SurveillanceFrance Announces New Spying Regulations After Terrorist Attacks
On Thursday, the Prime Minister of France Manuel Valls revealed debatable new laws that will allow intelligence agencies to gather cellphone and...
-

 217Cyber Events
217Cyber EventsPakistan Unblocks WordPress.com After Blocking It For One Day
Yesterday we reported how WordPress (WP) was banned in Pakistan due to internet security issues. We also revealed that the banned will be a...
-

 104Geek
104GeekGirl Poisons Mom Twice For Taking Away Her iPhone
A 12-year-old girl in Colorado has been arrested and charged for attempting to kill her mom through poisoning her with bleach just...
-
 228Geek
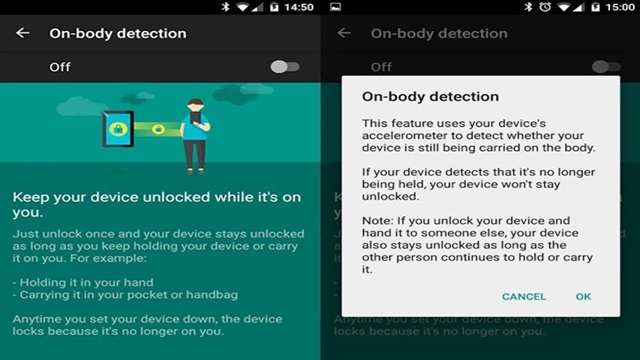
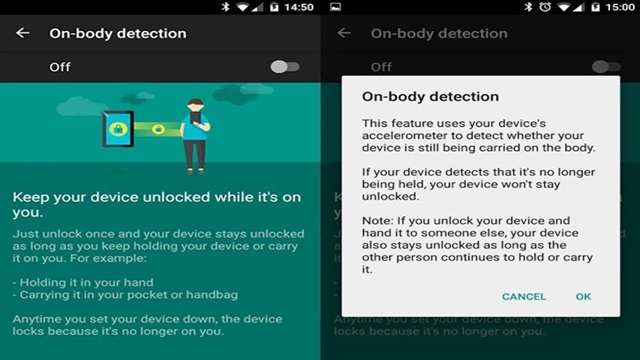
228GeekAndroid On-Body Detection Feature Will Keep Your Phone Safe From Thieves
The new on-body detection feature will lock your phone when you set it down, so thieves who swipe it can’t access your...
-

 203Hacked
203HackedWordPress Blocked In Pakistan, Blogs Hosted On WordPress Inaccessible
According to various sources and local media houses, WordPress.com has been banned in Pakistan. This shocking decision was today taken by the...
-

 258Data Security
258Data SecurityNew Chevy Malibu will come with built-in NSA-style Teen-Tracking Spyware
Chevrolet will offer parents an uncanny level of oversight when they need to lend the family ride to their kids with its...
-

 298Data Security
298Data SecurityISIS Releases Hacked Hit List of 100 U.S. Military Personnel
ISIS Wants Supporters To Kill a Hundred of its “Hacked Hit List” U.S. Military Employees. The Islamic State (ISIS) posted the names,...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




