Featured News
-

 250Data Security
250Data SecurityPremera Blue Cross Breached, Medical & Financial Data of 11 Million People Exposed
Medical and financial data of around 11 million Premera Blue Cross customers has potentially been exposed due to a breach that apparently...
-

 241Data Security
241Data SecurityFREAK Attacks Still a Threat for Hundreds of iOS and Android Apps
Apparently, a majority of iOS and Android apps are still potentially vulnerable to dangerous FREAK attacks that can easily compromise encrypted data....
-

 82How To
82How ToPremera Breach: Healthcare businesses in the crosshairs
Criminals are targeting medical records because of their value, and as a result, medical breaches are the fastest growing type of breach....
-

 266Surveillance
266SurveillanceSecurity Lines Get Short on Cincinnati Airport as Travelers’ Phones are Tracked
Travelers’ phone tracking strategy minimize Cincinnati airport’s Security line by one-third. We all know how miserable airport security processes are for the...
-

 167Cyber Crime
167Cyber CrimeDark Purple’s ‘killer USB’ will fry your computer’s circuit board
USB drives have been known to carry viruses and malware, but a Russian electronics expert has now created a thumb drive that...
-

 271Banking
271Banking$40k of bitcoin lost in Coinapult hot wallet hack
Coinapult, a long-running bitcoin wallet service, announced on Monday that its hot wallet had been compromised to the tune of 150 coins...
-
 268Hacked
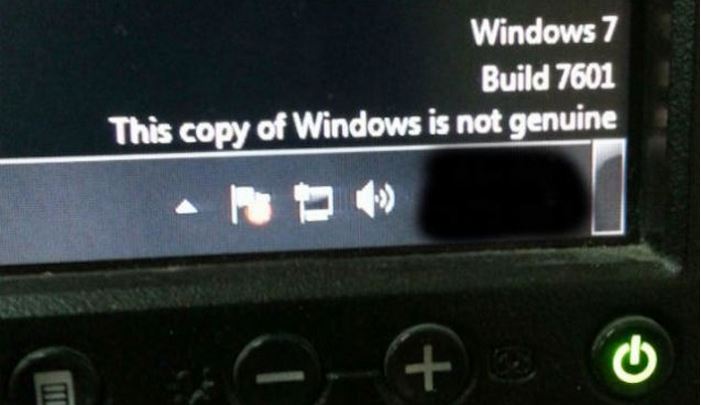
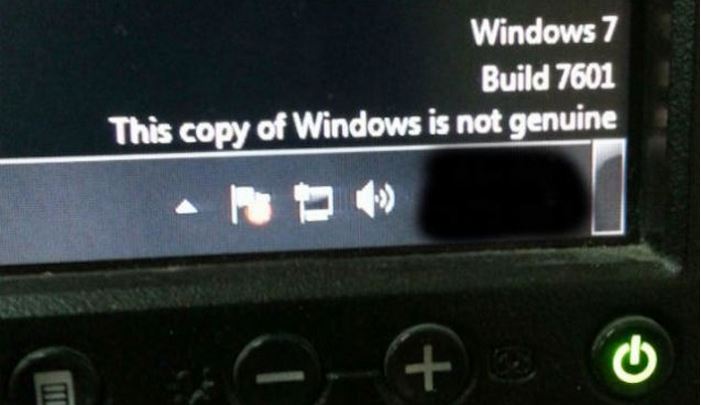
268HackedWindows 10 Upgrade Will be Free for Illegal and Pirated Copies
We all know that Windows will be releasing free upgrade for Windows 8 and Windows 7 users. Today Microsoft announced that it...
-

 440Surveillance
440SurveillancePentagon Wants Unhackable Boeing Drone Helicopters by 2018
Unhackable Drone Helicopters a must have for the Pentagon before 2018 – The Pentagon is looking for unhackable drone helicopters to avoid...
-

 125How To
125How ToWhy server side games generally can’t be hacked
We get many question daily asking us how to hack games such as Clash of Clans this article explains why server side...
-
 330How To
330How ToHow To Edit Any Website Using JavaScript?
Hey everyone, on some user request I wrote about How to Enable Hidden Offline Browsing In Google Chrome last time. And as expected,...
-

 193Cyber Events
193Cyber EventsFather witnesses Son’s birth from Thousands of Miles away Via Samsung’s GearVR
Samsung has done it yet again.. It has managed to do something entirely unique and introduce a new concept to the techno...
-
 272Surveillance
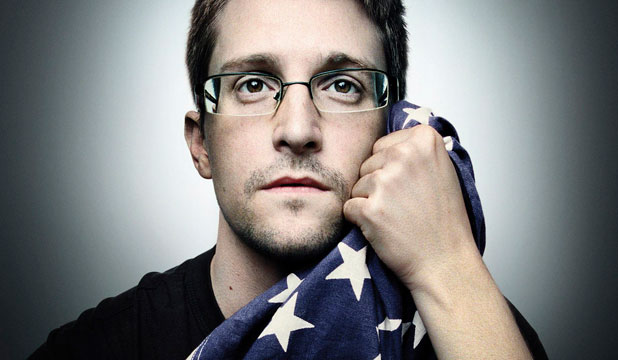
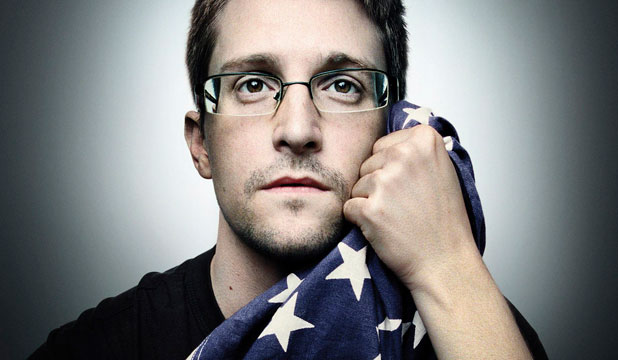
272SurveillanceTerrorism cannot be stopped through Mass Surveillance Tactics- Snowden
The ex-NSA spy and now a Whistleblower Mr. Edward Snowden said that terrorism cannot be stopped through mass surveillance tactics. He slammed...
-

 261Data Security
261Data SecurityOn-Demand passwords and e2e encryption source code Launched by Yahoo
Yahoo made two major announcements this week regarding its security protocol. One was the launching of the new “on-demand” password service and...
-

 354Cyber Crime
354Cyber Crime9‑year‑old cybersecurity expert hacks Android smartphone in minutes
Wondering how secure your Android smartphone is? Well, a 9-year-old cybersecurity expert has demonstrated how hackers could steal contacts, call logs and...
-

 174Surveillance
174SurveillanceMysterious Spy Cameras Secretly Spying on Post Office Customers in US
FOX31 Denver discovered a hidden camera which captured and recorded facial features and license plate numbers of whoever left the Golden Post...
-

 272Hacking
272HackingAdvantage Dental hacked – over 150,000 personal records breached
Advantage Dental has sent out notices to 151,626 customers after a hacking which may have led to the leaking of valuable patient...
-
 242Geek
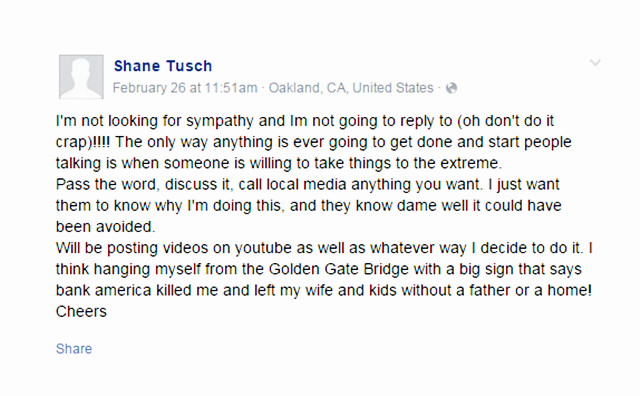
242GeekMan Fakes Suicide to See How Facebook Suicide Preventing Tool Works, Gets Detained
Shane Tusch learned about the authenticity of Facebook’s suicide prevention tools the hard way – What started as an attempt to check...
-

 316Geek
316GeekApp Store Phishing Email Stealing Apple User Credentials
A PhishTank has been located where the Apple store users have been the victims of phishing emails. OVH, very well-known web hosting...
-

 248Privacy
248PrivacyVPNs illegal in UAE, says Dubai Police
A senior official in the Dubai Police force has stated that the use of Virtual Private Networks is illegal across the United...
-

 280News
280NewsPay Ransom or Secret Data on South Korean Nuke Reactors Will Be Leaked: Hacker
An individual seems to be threatening the South Korean government with the confidential information associated with the country’s power plants and says...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




