Featured News
-

 204Hacked
204HackedWordPress Blocked In Pakistan, Blogs Hosted On WordPress Inaccessible
According to various sources and local media houses, WordPress.com has been banned in Pakistan. This shocking decision was today taken by the...
-

 260Data Security
260Data SecurityNew Chevy Malibu will come with built-in NSA-style Teen-Tracking Spyware
Chevrolet will offer parents an uncanny level of oversight when they need to lend the family ride to their kids with its...
-

 301Data Security
301Data SecurityISIS Releases Hacked Hit List of 100 U.S. Military Personnel
ISIS Wants Supporters To Kill a Hundred of its “Hacked Hit List” U.S. Military Employees. The Islamic State (ISIS) posted the names,...
-

 269Cyber Events
269Cyber EventsWordPress.com Banned in Pakistan Over National Security Issues
In a shocking decision the government of Pakistan has banned WordPress.com, the world renowned open-source blogging tool and a content management system. Users...
-
 326Hacked
326Hacked5 Best Alternatives to Tor Browser to Browse Anonymously
Security of Tor Project, the most popular service to browse the web anonymously, is under suspicion. Tor Project has suffered from a...
-

 420Geek
420GeekHow to Build Your Own Social Networking Website?
Image: Coinsaround Ever thought of building your own social networking website for college, organization or something like Facebook? If yes, then this...
-
 294Cyber Crime
294Cyber CrimeBank of America Phishing Link Stealing Customers’ Personal Data
Hackers are targeting bank of America’ customers with a phishing campaign – If you are a customer at the bank of America DO NOT...
-
 206Geek
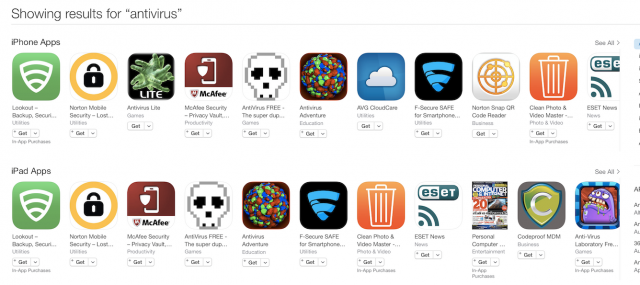
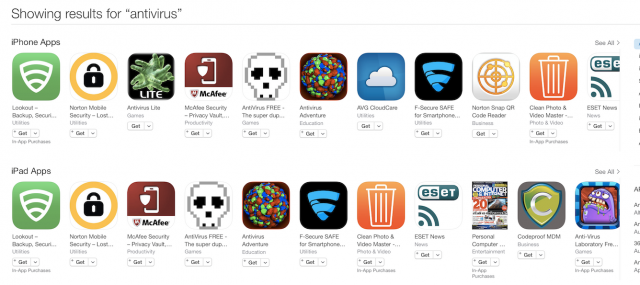
206GeekApple removes antivirus apps from iOS App Store
Apple is deleting antivirus and antimalware apps from its iOS App Store without official warning or announcement. It seems that Apple has...
-
 286Data Security
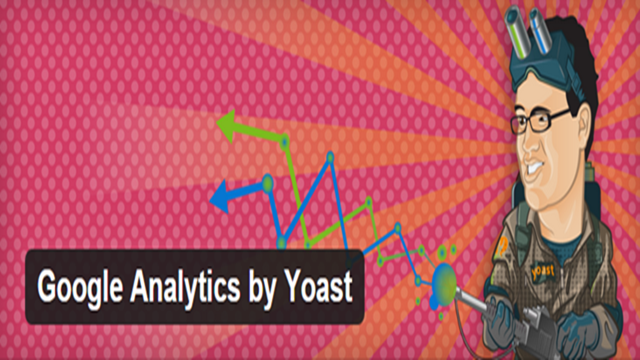
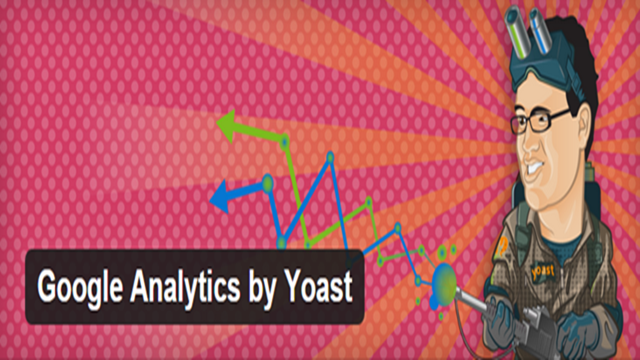
286Data SecurityWordPress Google Analytics Plugin by Yoast Vulnerable to critical site-hijacking
Yet another vulnerability has been found in the Yoast WordPress plugin that can be exploited by attackers allowing them to control the...
-

 334News
334NewsChina Blocks Reuters Website After DDoS Attack On The Great Firewall of China
The Great Firewall of China known for censoring/blocking websites in the country was under DDoS attack which caused a blockage of Reuters’ news website...
-
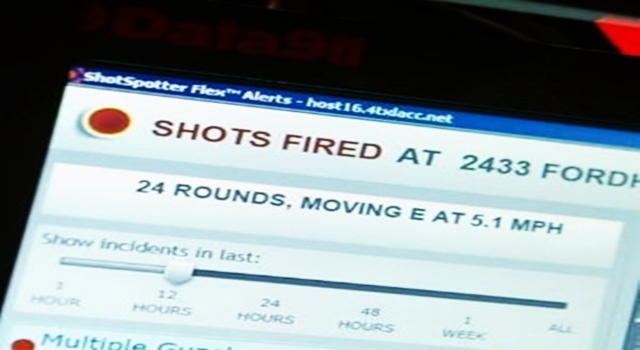
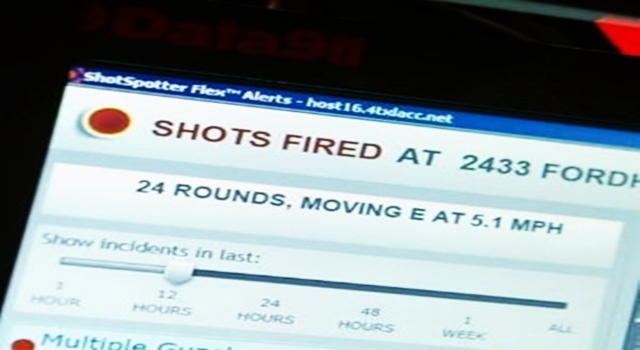 250Surveillance
250Surveillance$1.5 million Spent by NYPD on electronic ears for gunshots surveillance
NYPD cops have started testing a system, which allows them to immediately track the location within 82feet from where a gun was...
-

 336Hacked
336HackedHow to See If your Email is Being Tracked
Many of us probably think that what is the benefit of tracking a mail, so why should I care, right? Wrong! Everyone...
-

 74Cyber Crime
74Cyber CrimeUK businesses are unprepared for potential data breaches
Many UK businesses are unequipped to respond to potential data breaches, according to two new independent reports published this week.
-

 287Small business
287Small business7 tasks that waste your IT team’s time
IT teams' time is always limited, and it doesn't help when other things get in the way. Here's seven things that waste...
-

 74Cyber Crime
74Cyber CrimeHacker threatens cyberattacks against Detroit over court decision
A hacker going by the name of 'Bitcoin Baron' has issued a threat to the city of Detroit after a Wayne County...
-
 262Hacked
262HackedChina Finally Accepts it has an Army of Hackers
Well, something very unexpected has happened recently. The fact that China is having an army of hackers isn’t surprising; instead, acceptance of...
-

 89How To
89How ToThe future of security in healthcare: Mobile devices
The pressure for businesses to allow their employees to access work resources with their personal mobile devices may be overwhelming. How can...
-

 190Surveillance
190SurveillanceUnveil Stingray Surveillance Details To Public – Orders NY Court to Sheriff
A Supreme Court judge in Buffalo ordered the Sheriff Office at Erie Country to disclose secret information to public which was collected...
-

 509Banking
509BankingFacebook announces peer‑to‑peer payments between friends
Facebook has announced a new feature of its Messenger product, which allows friends to send payments directly to each other, reports Tech...
-

 102Malware
102MalwareGoogle Play security tightened with human screening process
Google is taking additional security measures to shut out malware from its app store by introducing a human screening process.
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




