Featured News
-

 96Password
96PasswordBritish Bank trials heartbeat based authentication
A British bank has been trialling a different type of biometrics, allowing their customers to confirm their identity via heartbeat according to...
-

 144How To
144How ToHeimdal blog, 19 Experts, 50+ Security Tips
Heimdal asked a range of security experts for their essential security tips. 19 experts (including David Harley) offered over 50 tips.
-

 497Windows
497WindowsWill Windows 10 leave enterprises vulnerable to zero‑days?
One thing Microsoft has been very public about is Windows 10's new strategy of releasing patches to update the operating system at...
-
 277Cyber Events
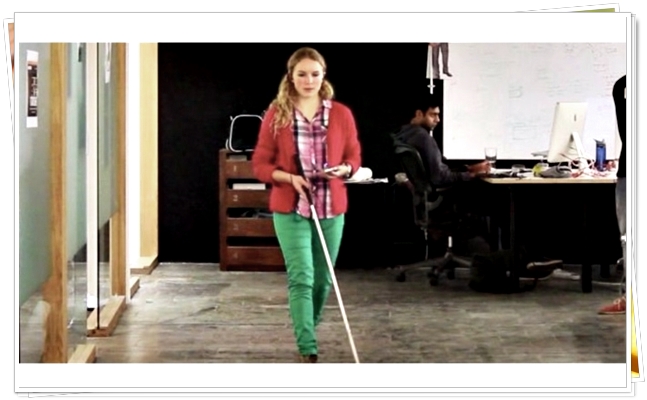
277Cyber EventsAn App that Helps Blind People Traverse London’s Tube via Sound
One of London’s tube stations will become more accessible for vision impaired and blind travelers by an amazing new Bluetooth setup. According...
-

 294Geek
294GeekDubai Police: Using VPN in United Arab Emirates is a Punishable Crime
Using VPN is a crime under UAE’s cyber laws – Anyone found using VPN can be charged for going against the country’s...
-

 177Surveillance
177SurveillanceU.S. Senate Rushing to Move Cyber-Surveillance CISA Bill Amid NSA Spying
The controversial cybersecurity legislation Cybersecurity Information Sharing Act (CISA) will be passed by the Senate Intelligence Committee on Thursday, said the panel’s...
-
 276Data Security
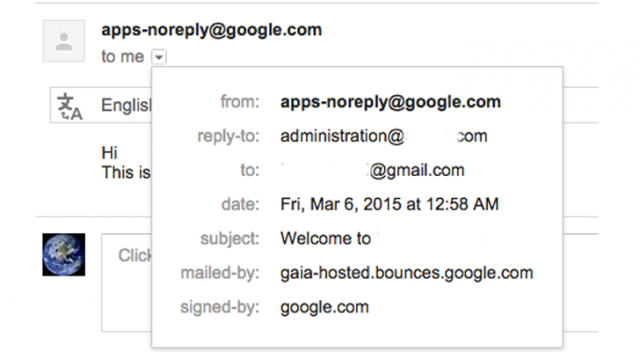
276Data SecurityCybercriminals Abusing Vulnerability in Google Apps to Send Phishing Emails
It has been found that hackers can now easily abuse any website’s domain name based email addresses through the Google Apps for...
-

 107Privacy
107PrivacyThe immortality of data (and people) in the digital age
In the future, everything around us will be managed by data, and those who have data will have power. So, will anonymity...
-

 142Scams
142ScamsHackers phish for data with fake Apple Watch giveaway
Apple fans keen to get their hands on the Apple Watch are advised to think before they click, after hackers exploited a...
-
 251Hacked
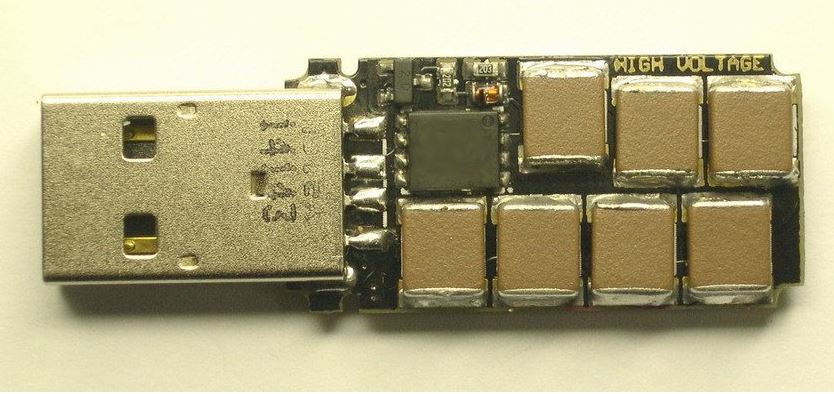
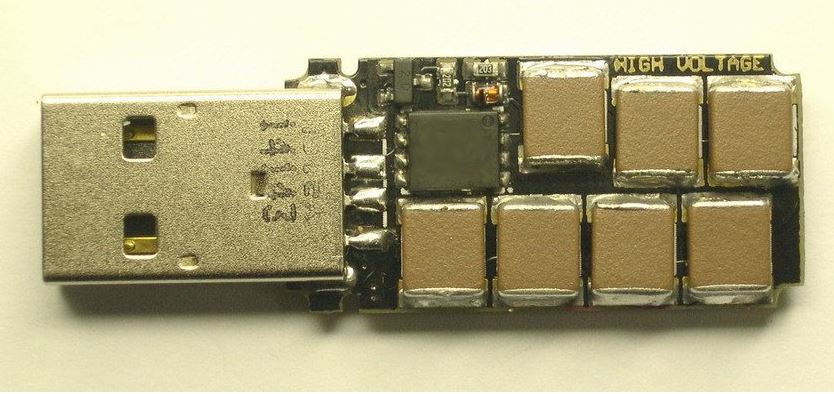
251HackedThis “Killer USB” Flash Drive Will Explode Your Computer
The Killer USB USB drives are known be humble creatures that help you out by transferring your data. But, what if a...
-
 98Privacy
98PrivacySuperfish: Lenovo goes on the bloatware offensive
Its been just under three weeks since February 19th, when Lenovo became entangled in a web of controversy over its preinstallation of...
-
 257Data Security
257Data SecurityWordPress SEO by Yoast’ Plugin Vulnerable to Hackers, Affecting Millions Worldwide
A number of websites have been put at risk due to a very popular plugin of the WordPress content management platform vulnerability...
-

 225Data Security
225Data Security‘Snowden Phone’ by FreedomPop vows to encrypt your calls and data
US Consumers looking for a wireless steal can now get encrypted free monthly phone service thanks to FreedomPop, the firm behind the...
-

 307Data Security
307Data SecurityUS Military to Hire 3,000 New Cybersecurity Professionals by 2016
Around 3,000 new security professionals will be added to the United States military’s infosec unit by 2016, according to reports. It says that...
-
 196Privacy
196PrivacyThe human cost of phone hacking
Phone hacking ruined the lives of celebrities, and - in at least one case - almost drove a victim to suicide.
-
 246News
246NewsRedHack Hacks Istanbul Police Assoc. website, Tributes Berkin Elvan on 1st Death Anniversary
The online Turkish hacktivist group RedHack has hacked and defaced the official website of Istanbul Police Association in tribute to Berkin Elvan, a 15-year-old teenager who...
-

 306Data Security
306Data SecurityVulnerability in WordPress Plugin Allows Hackers to take full control of website
WordPress’s MainWP Child Plugin has vulnerability… and it is very much exploitable. Researchers at Sucuri have identified a vulnerability in the MainWP...
-

 321News
321NewsFacebook Login Bug Lets Hackers Takeover User Accounts with Reconnect Tool
Even after almost a year, Facebook apparently has failed to fix a bug that lets attackers hijack accounts on sites that leverage...
-

 230Surveillance
230SurveillanceStop spying on us: Wikipedia sues NSA over mass Internet surveillance
A lawsuit has been filed against NSA (National Security Agency) to preserve the rights of the 500 million Wikipedia users who visit...
-

 70Cyber Crime
70Cyber Crime80 percent of global merchants fail card data security tests
Around 80 percent of global merchants including retailers, financial institutions and hospitality firms have failed interim tests which show they are not...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




