Featured News
-
 290News
290NewsLarimer County Sheriff’s Office Website Hacked by Pro-Palestinian Hackers
The official website of Colorado’s Larimer County Sheriff’s Office ( LCSO) was hacked early Tuesday morning by famous hacking group AnonGhost. Officials running the website acknowledged the...
-

 239Geek
239GeekYou can now Send Encrypted Messages to-and-from Android and iOS (FREE!)
Signal 2.0, is the second installment of the app of the same name that was created for iOS. Its release has been...
-

 281Surveillance
281SurveillanceFBI Admits Its Secret Spy Tool Stingray Disrupts Phone Service
Unsealed Document Exposes FBI – Bureau admits using Stingray Devices to Disrupt Phone Service. FBI’s Stingray secrecy has been compromised and exposed by...
-

 225Cyber Events
225Cyber EventsParalysed Woman Flies Fighter Jet Simulator Using Her Thoughts
The Defense Advanced Research Projects Agency (DARPA) is known for its secretive projects, but we have to agree the agency is also...
-

 234Malware
234MalwareFake Amazon gift cards offer only malware to Android devices
Fake Amazon gift cards are being sent to Android devices via text message, but it's malware not discounts that is being spread...
-

 294News
294NewsHacking YouTube Account Through Phishing Mails
The latest round of phishing scam is associated with YouTube. A mail asking one to update YouTube account information is actually a...
-

 250Cyber Events
250Cyber EventsFacebook’s New Tool Will Help Users Against Suicidal Thoughts
A set of tools has been rolled out by Facebook to help prevent suicide thoughts among its users. It is now possible to...
-
 201Tricks & How To's
201Tricks & How To'sHow to Host your website by creating a Linux Server
Alright here is the method, on how to host your website on Linux server (vps). Since these days you can see hosting...
-
 271Evasion & Obfuscation
271Evasion & ObfuscationHow to manually bypass Anti-Virus
This post is based on how to bypass Anti-Virus by using FUD (Fully Undetectable). There are many Crypters and binders but manually...
-

 284Data Security
284Data SecurityVulnerability in Blu-ray Players allow hackers to penetrate your network
Unsuspected Blu-Ray Players Vulnerabilities Present Open passage to Cybercriminals. A team of security researchers at NCC Group analyzed different Blu-ray players and...
-
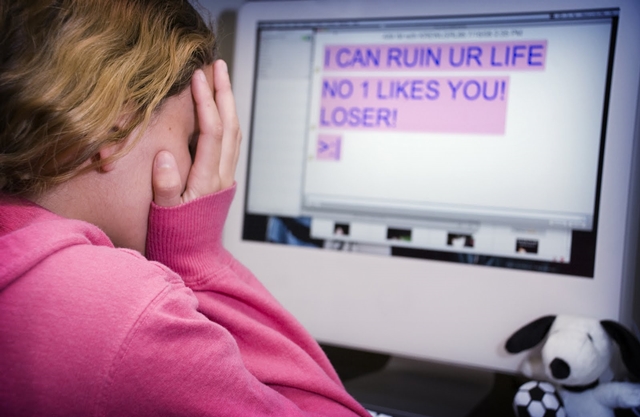
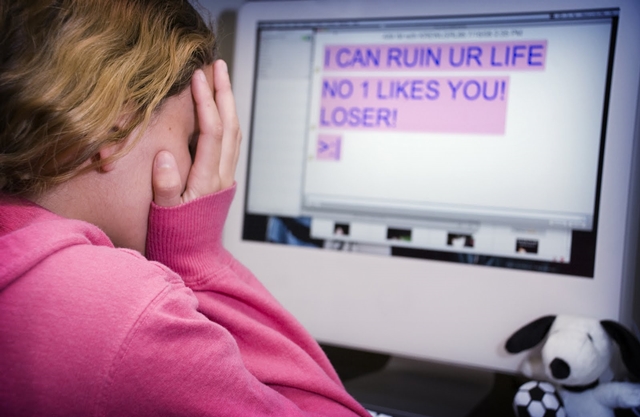 355Geek
355GeekStop!t: An App for Kids To Report Cyberbullies With Push of A Button
Internet penetration has eased our lives a lot: everything is just a click away and so are the cybercrimes. None is spared,...
-

 116Password
116PasswordToys “R” Us resets account passwords to counter stolen reward points
Account holders with Toys "R" Us have been informed that their passwords will be reset, after unauthorised third-parties attempted to gain access...
-
 359Hacked
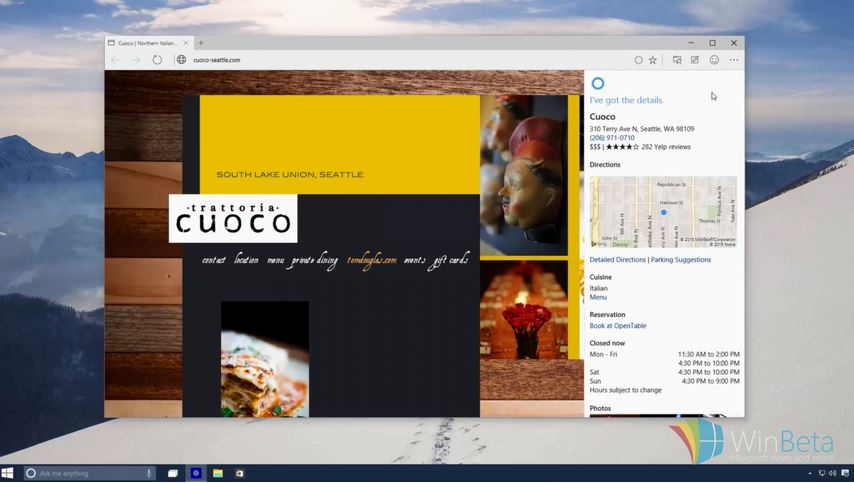
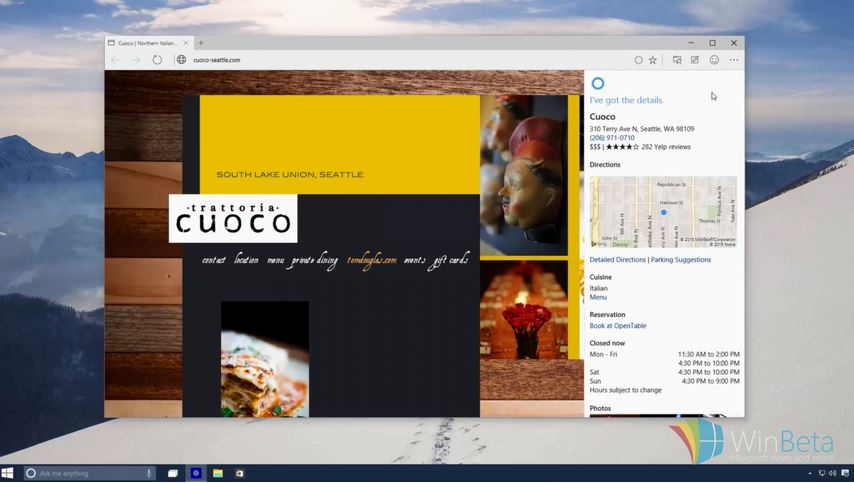
359HackedSpartan Browser Demo Video Leaked, Coming in Next Windows 10 Preview
Image: WinBeta Back in January, Microsoft first showed off the Internet Explorer successor – Project Spartan. The new browser is expected to...
-

 144Privacy
144PrivacyIndia blocks third party email services to government officials
The Indian government has changed the way in which its officials are allowed to operate when working, it has been announced.
-

 208How To
208How To10 tips for protecting your virtual Bitcoin wallet
There have been some high-profile Bitcoin thefts recently. Here are 10 tips on protecting your virtual bitcoin wallet.
-
 287Cyber Crime
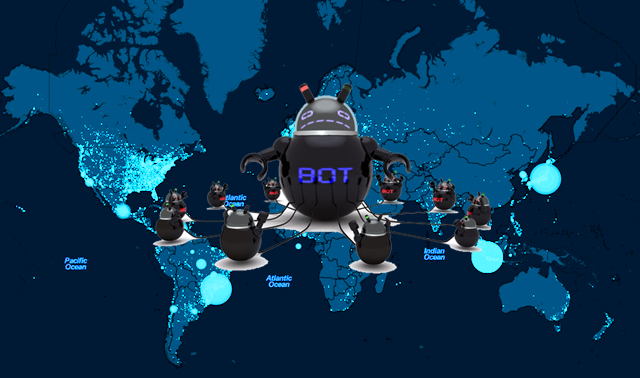
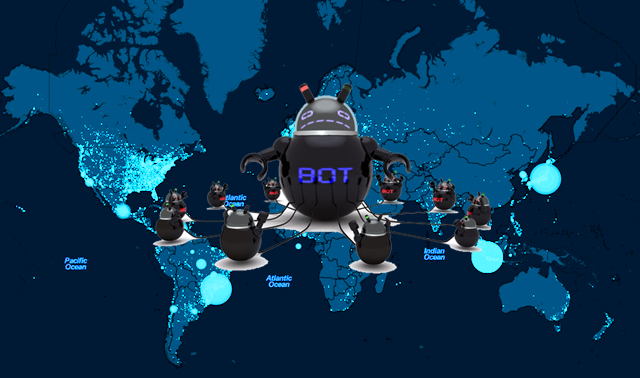
287Cyber CrimeEuropean Cyber Police Shuts Down World’s Biggest “Ramnit” Botnet
In a joint operation cyber police from United Kingdom, Netherlands, Germany and Italy have claimed successful breakdown of what can be the...
-

 200Geek
200GeekMicrosoft Outlook Users Targeted with Account Termination Phishing Scam
Another Phishing Scam Targeting Microsoft Outlook – The Request To Terminate Outlook Account Email is nothing but a Fraud. A new wave of...
-
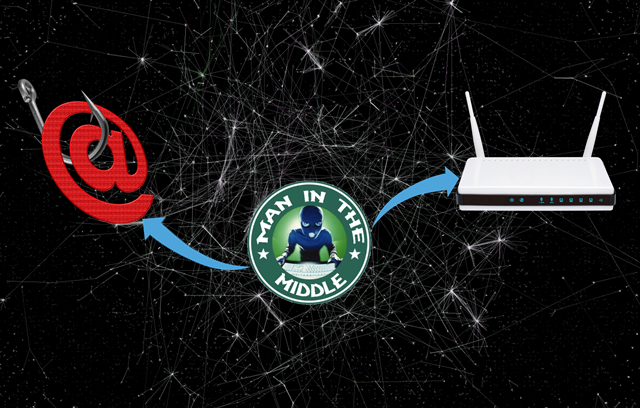
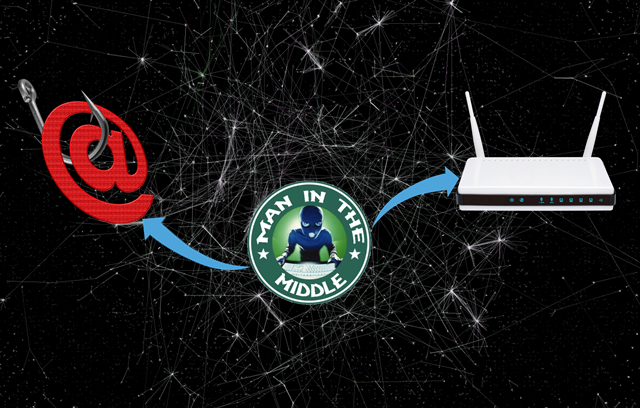 328Data Security
328Data SecurityPhishing Emails & Exploits Used by Attackers to Hijack Routers
ProofPoint researchers released a report on Tuesday, which revealed that cybercriminals are now hijacking the Brazilian internet connections by altering their DNS...
-

 280Data Security
280Data SecurityDARPA wants to use Unmanned Surveillance system to monitor The Arctic
To Monitor The Arctic DARPA willing to give $4million for an Unmanned Surveillance System. Ice melting in the Arctic has been the...
-
 90Geek
90GeekLearn How to Program Robots for Free. Anyone, Anywhere, Anytime.
Do you want to learn robotics and you are running short on cash? Do want to know a way to do so...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




