Featured News
-

 253Geek
253GeekWindows Vulnerable To Critical Freak SSl Flaw, Microsoft says
Microsoft has revealed that Windows is vulnerable to a critical Freak SSl Flaw. Freak is a security bug that facilitates cybercriminals to conduct...
-

 281Surveillance
281SurveillanceEntering Phone number now MUST for Tor users to open a new Twitter account
Tor users will now have to enter their phone number in order to make a new account on Twitter. Last week, Twitter...
-
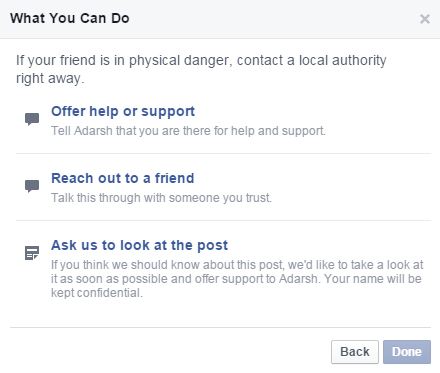
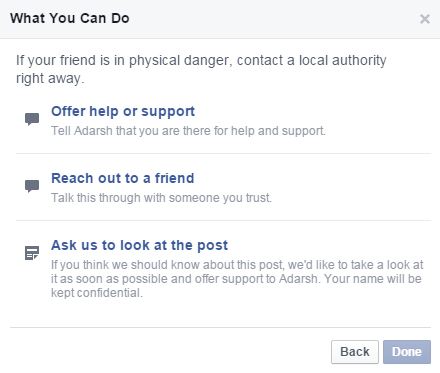 210How To
210How ToHow To Report Suicidal Posts on Facebook
In order make its product more helpful, Facebook updated its tool to report suicidal posts. Facebook claims that this tool will make it easy to...
-

 324Hacked
324HackeduTorrent Installs a Bitcoin Miner to Steal CPU Power from Your PC
uTorrent is one of the most popular torrent clients out there and a new update in the software has brought some unwanted...
-

 308Data Security
308Data SecurityCanadian jailed for refusing to unlock his phone at the airport
Alian Philippon, a 38-year-old citizen from Ste-Anne-des-Plaines, Quebec, will be facing up to 24,000 Canadian Dollars fine and one-year jail time for...
-

 104Cyber Crime
104Cyber CrimeAir traffic control vulnerability could allow criminals to hack the skies
The Federal Aviation Administration must tighten the security around air traffic control in the United States, according to a new report filed...
-

 203Interview
203InterviewLysa Myers: “There are still only a handful of women in the security field”
There are many female researchers and computer experts who contribute to the field, helping everyone enjoy safer technology. We spoke to one...
-

 277News
277NewsLarimer County Sheriff’s Office Website Hacked AGAIN! 2nd time this week
On Tuesday 3rd March, the official website of Colorado’s Larimer County Sheriff Office website (LCSO) was hacked by pro-Palestinian AnonGhost hacking group. Today, Thursday,...
-

 302Geek
302GeekiPhone, iPad theft Victims tricked into unlocking devices through iCloud Phishing Page
Victims of iPhone theft being tricked into unlocking their devices – Criminals luring victims to Fake iCloud login via text messaging. Seems like...
-

 289Data Security
289Data SecurityThis Mysterious Android App Emails Your Whereabouts to Stalkers
Smartphones are seriously wonderful since these have introduced us to some amazing things like Snapchat, Vine, Maps, Shazam and some not-so-amazing stuff too...
-

 86Cyber Crime
86Cyber CrimeAnthem refuses IT security audit following massive data breach
Anthem Inc. has refused to allow a federal watchdog to conduct an audit of its IT systems, following a huge data breach...
-

 323Banking
323BankingFive alternatives to Bitcoin
Here’s a small selection of alternatives to Bitcoin - each of which has its own advantages. All of them share Bitcoin’s fundamental...
-
 296Geek
296GeekMozilla, Linux and Tor Not Accepted for Google Summer of Code 2015
The list of organizations mentoring this year’s GSoC- Google Summer of Code 2015 – has been released and this list is having...
-
 301News
301NewsLarimer County Sheriff’s Office Website Hacked by Pro-Palestinian Hackers
The official website of Colorado’s Larimer County Sheriff’s Office ( LCSO) was hacked early Tuesday morning by famous hacking group AnonGhost. Officials running the website acknowledged the...
-

 248Geek
248GeekYou can now Send Encrypted Messages to-and-from Android and iOS (FREE!)
Signal 2.0, is the second installment of the app of the same name that was created for iOS. Its release has been...
-

 288Surveillance
288SurveillanceFBI Admits Its Secret Spy Tool Stingray Disrupts Phone Service
Unsealed Document Exposes FBI – Bureau admits using Stingray Devices to Disrupt Phone Service. FBI’s Stingray secrecy has been compromised and exposed by...
-

 231Cyber Events
231Cyber EventsParalysed Woman Flies Fighter Jet Simulator Using Her Thoughts
The Defense Advanced Research Projects Agency (DARPA) is known for its secretive projects, but we have to agree the agency is also...
-

 244Malware
244MalwareFake Amazon gift cards offer only malware to Android devices
Fake Amazon gift cards are being sent to Android devices via text message, but it's malware not discounts that is being spread...
-

 307News
307NewsHacking YouTube Account Through Phishing Mails
The latest round of phishing scam is associated with YouTube. A mail asking one to update YouTube account information is actually a...
-

 257Cyber Events
257Cyber EventsFacebook’s New Tool Will Help Users Against Suicidal Thoughts
A set of tools has been rolled out by Facebook to help prevent suicide thoughts among its users. It is now possible to...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




