Featured News
-

 286Lists
286ListsSome of the Weirdest and Awesomest Music Genres You Probably Have Never Heard Of
Are you an avid music geek like I am? You’re not just a keen music lover. You’re a fanatic. You’re a votarist....
-
 108Tricks & How To's
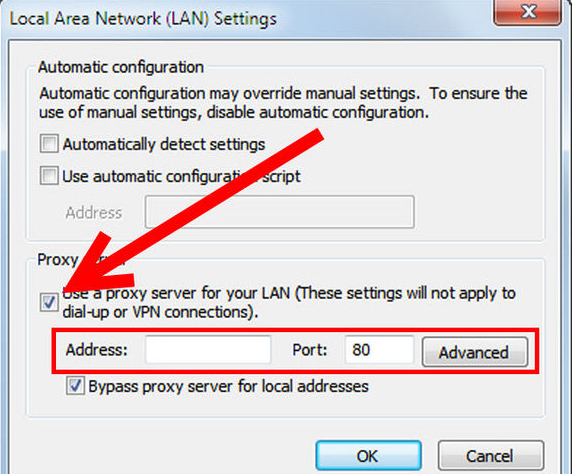
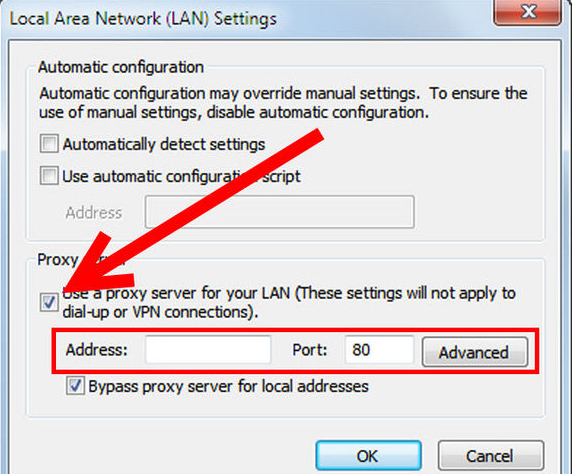
108Tricks & How To'sRemote PC without any software
Remote sharing is nowadays on its peak, people use remote sharing to provide live support or for sharing screens. Most of us...
-

 117Hacking
117HackingEven skateboards can be hacked
It seems even the humble skateboard isn't immune to hacking, as The Register reports that the 'Boosted' brand of electric skateboards has...
-

 109Privacy
109PrivacyMobile security: flaw allows hackers to read texts and listen to calls
Hackers can eavesdrop on your phone calls and text messages even with cell networks using "the most advanced encryption available" according to...
-

 76Cyber Crime
76Cyber CrimeUK Office of Communications reveals nature of recent cyberattacks
A Freedom of Information request to the UK's Office of Communications has revealed exactly how persistent hackers are at attacking government departments...
-

 280News
280NewsIran hacked Vegas Casino wiping hard drives, shutting down email
On the morning of February 10, 2014, the Las Vegas Sands casino, something was not right. Computers were flat-lining, telephone lines stopped...
-

 211News
211NewsOnline Transaction Company Payza Blog Hacked by Pakistani Hackers.
The famous Pakistani hacking group going with the handle of MadLeets has hacked the official blog of the U.S based online transaction company Payza...
-

 195Cyber Crime
195Cyber CrimeTarget breach 12 months on: a year of lessons learned
The Target hack that was revealed one year ago today brought new levels of awareness to the problem of cybercrime. Today we...
-

 172Hacking
172HackingICANN computers compromised by hackers
The nonprofit organization that looks after name and internet domains has been hit by a spear phishing hack that has compromised company...
-

 186Privacy
186PrivacyUber considers biometrics in bid to improve safety
The ride-sharing app Uber has unveiled new security plans to screen drivers, helping ensure passenger safety, Engadget reports.
-

 149Cyber Crime
149Cyber CrimeWebcam security – how to lock down the cameras in your home
Our tips will help you hacker-proof anything from baby monitors to surveillance cameras - and keep your home private.
-
 250How To
250How ToTips to stay safe on the Internet
Within the modern digital era that we live in today, we are constantly connected to the Internet either through a desktop PC,...
-

 297Banking
297BankingDutch University unveils ‘fraud proof’ credit card concept
A Dutch university has reportedly made great steps towards making the dream of a 'fraud-proof' credit card a reality by utilizing quantum...
-

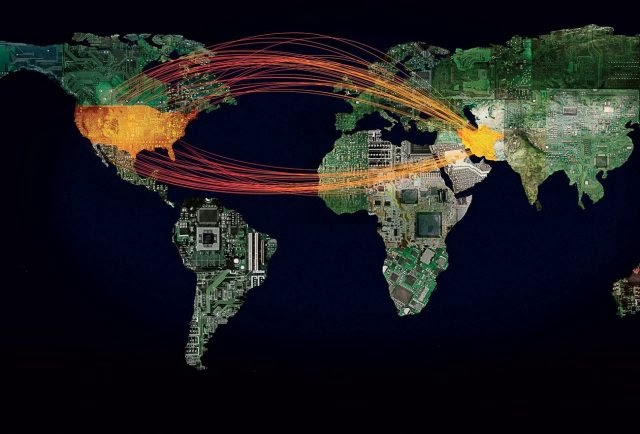
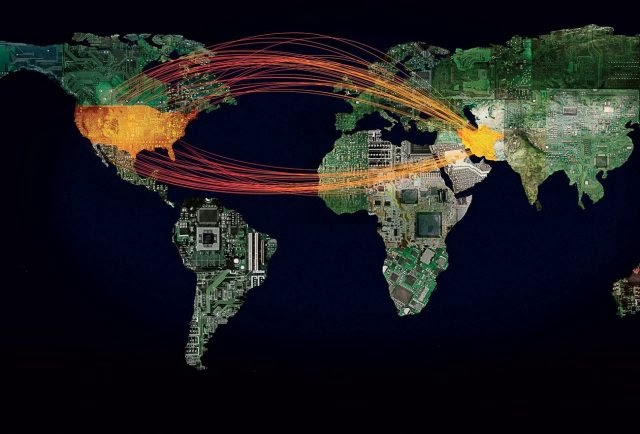
 378Cyber Crime
378Cyber CrimeTorrentLocker — Ransomware in a country near you
Today, we are publishing research on ransomware that emerged in 2014. We have posted blog articles about this threat before, to raise...
-

 213Social Media
213Social MediaFacebook scam: You won’t get a car for liking posts…
A new Facebook scam is doing the rounds promising users of the social network the chance to win a brand new car,...
-

 84Cyber Crime
84Cyber CrimeTorrentLocker: Racketeering ransomware disassembled by ESET experts
Security experts at ESET have released their latest research into the notorious TorrentLocker malware, which has infected thousands of computer systems around...
-
 303Cyber Crime
303Cyber CrimeFBI: Iran Hackers May Conduct Cyber Attacks on U.S Defence, Energy Sector
US energy, defense and educational institutions are the top targets of a possible sophisticated cyber attack from the Iranian hackers, says a...
-

 272Small business
272Small businessHypercom payment terminals bricked… but not by malware
When 'several thousand' payment terminals across the country stopped working last week, it would be easy to jump to the conclusion that...
-

 266News
266NewsCops scan social media to help access your ‘threat rating’: Reuters
Recent events have steered the national focus onto aggressive law enforcement and the public is not at ease with the situation. Physical...
-
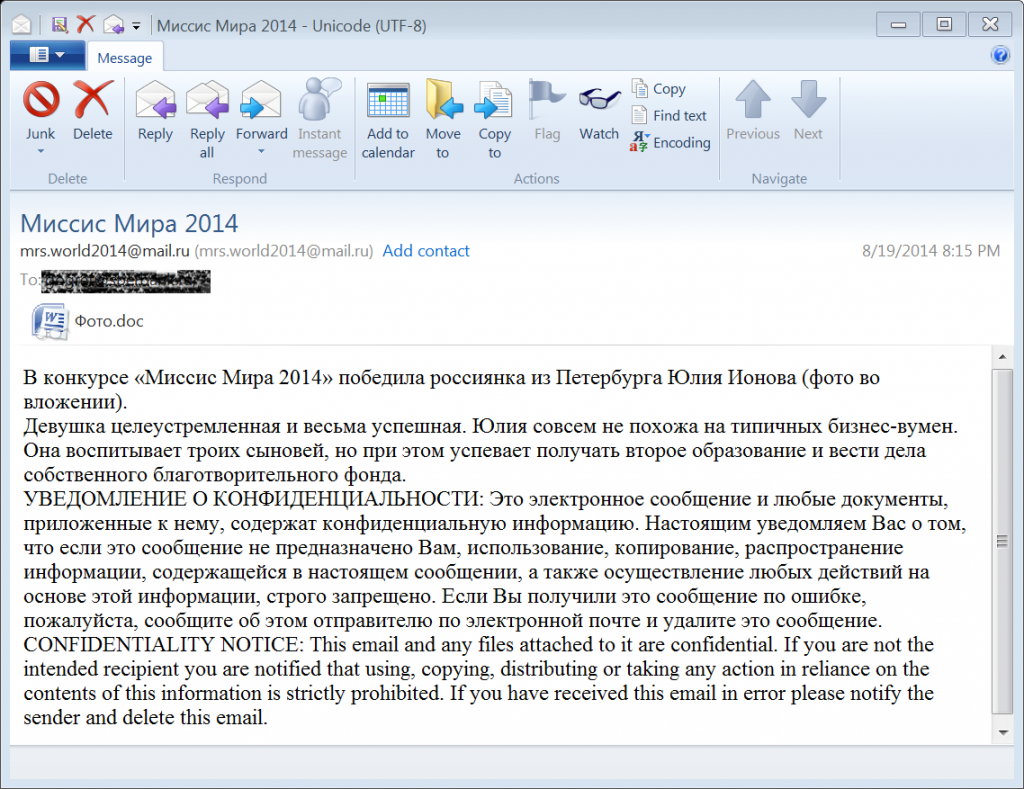
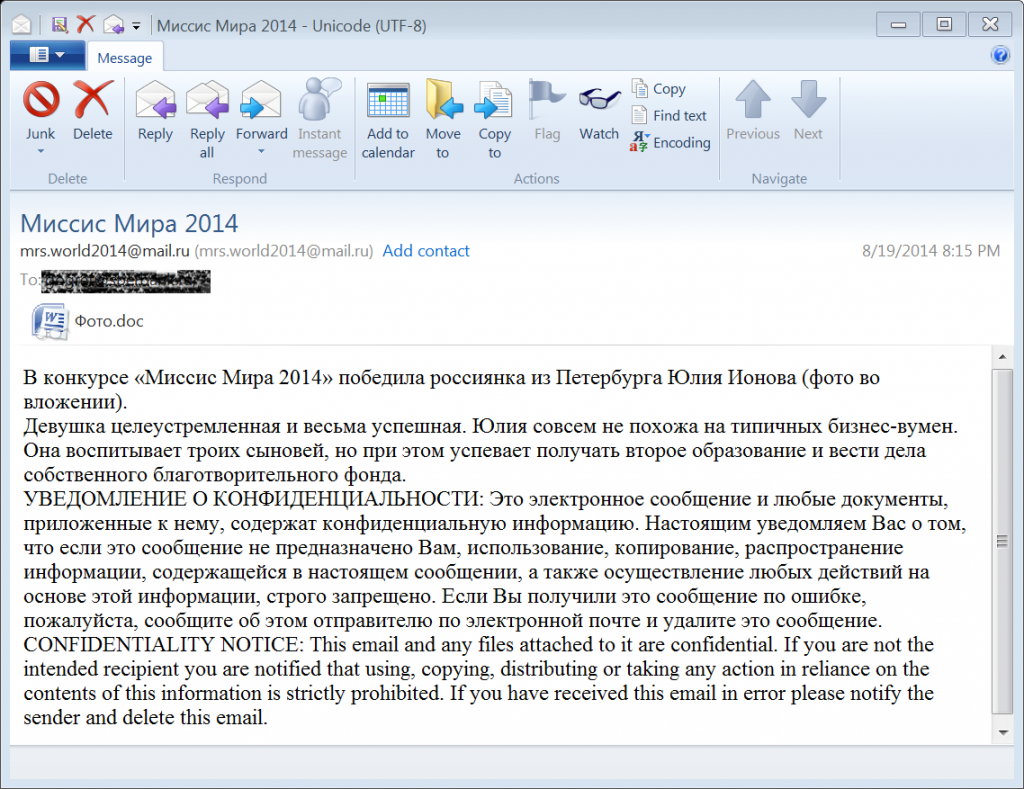 369Data Security
369Data SecurityMost Sophisticated Malware Campaign Targeting Diplomats, iPhones, Android, and PC.
Researchers from Blue Cat Labs are calling it the Inception attack framework, in reference to the movie “Inception” where a thief entered...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




