Featured News
-

 84Cyber Crime
84Cyber CrimeTorrentLocker: Racketeering ransomware disassembled by ESET experts
Security experts at ESET have released their latest research into the notorious TorrentLocker malware, which has infected thousands of computer systems around...
-
 305Cyber Crime
305Cyber CrimeFBI: Iran Hackers May Conduct Cyber Attacks on U.S Defence, Energy Sector
US energy, defense and educational institutions are the top targets of a possible sophisticated cyber attack from the Iranian hackers, says a...
-

 274Small business
274Small businessHypercom payment terminals bricked… but not by malware
When 'several thousand' payment terminals across the country stopped working last week, it would be easy to jump to the conclusion that...
-

 267News
267NewsCops scan social media to help access your ‘threat rating’: Reuters
Recent events have steered the national focus onto aggressive law enforcement and the public is not at ease with the situation. Physical...
-
 370Data Security
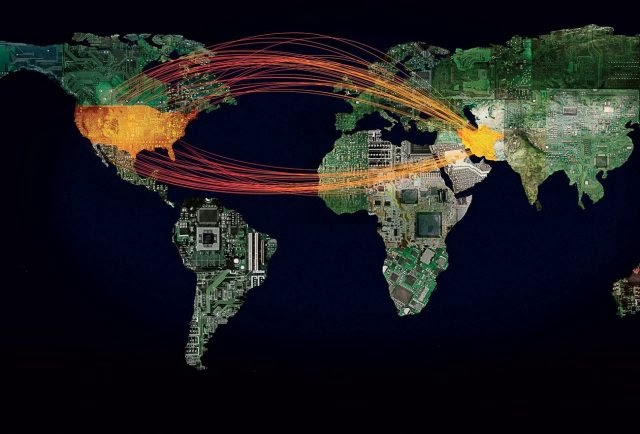
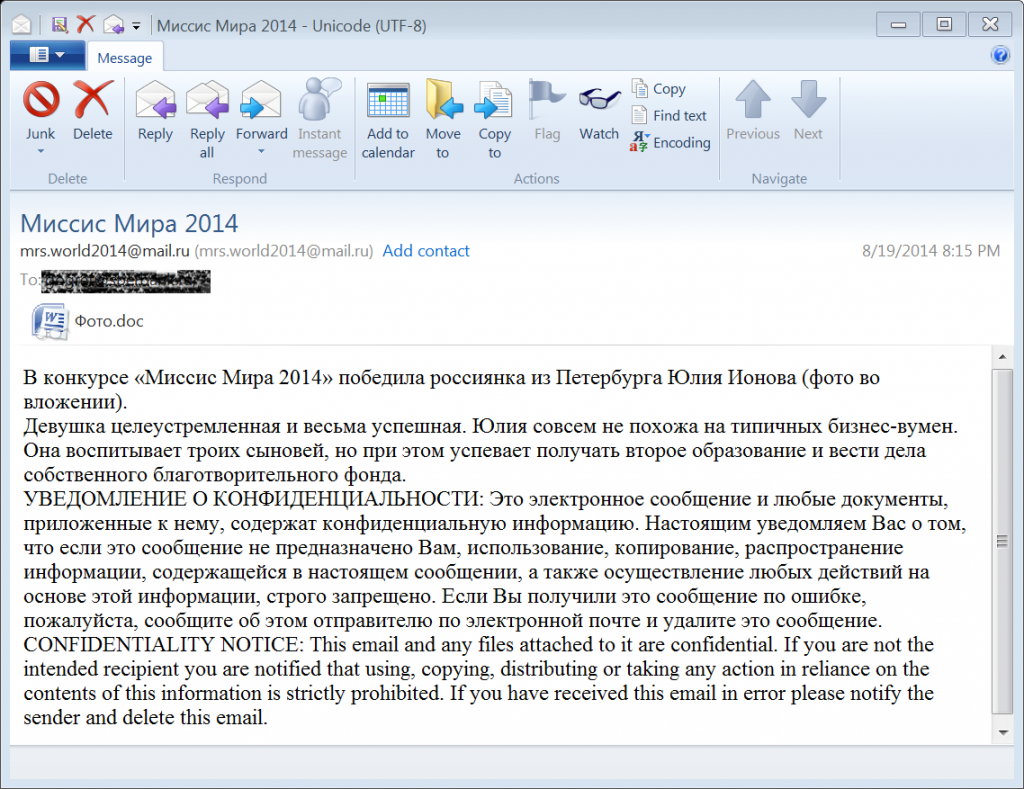
370Data SecurityMost Sophisticated Malware Campaign Targeting Diplomats, iPhones, Android, and PC.
Researchers from Blue Cat Labs are calling it the Inception attack framework, in reference to the movie “Inception” where a thief entered...
-
News
UK Dept of Education Sub-Domain Hacked by Pro-Palestinian Hackers.
A pro-Palestinian hacker going with the handle of ‘AlFeRoX’ hacked and defaced the sub-domain of United Kingdom’s Department of Education in support of a...
-

 183Cyber Crime
183Cyber CrimeFBI outlines proposals for dealing with cybercrime to Congress
Joseph Demarest, assistant director at the FBI, has been testifying on the threats of cybercrime to a Senate Committee on Banking, Housing...
-
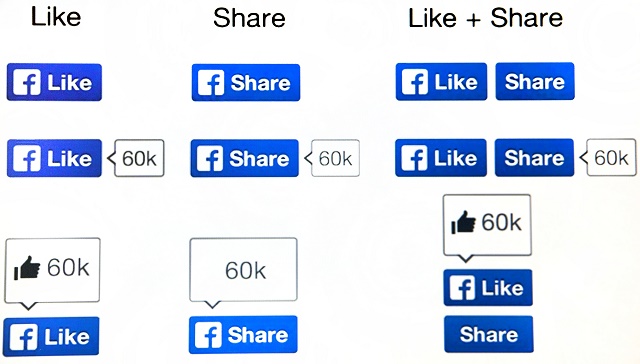
 169Social Media
169Social MediaFacebook hoax – how to tell instantly if a story is fake
Two-thirds of young people first learn about major news events via Facebook - but as cybercriminals cash in with hoax stories and...
-

 179Hacking
179HackingCharge Anywhere warns of payment data leak
Mobile payment platform Charge Anywhere has revealed an exploit in its software that means that five year's worth of credit card data...
-
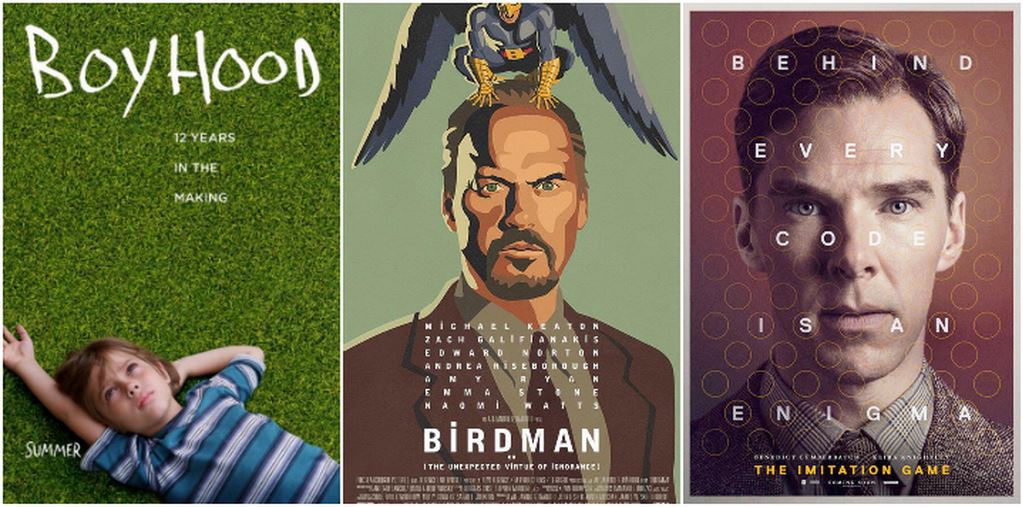
 76Lists
76Lists2015 Golden Globes Nominations: The Complete List
Today Kate Beckinsale, Peter Krause, Paula Patton and Jeremy Piven announced the 2015 Golden Globes Nominations (Hollywood Foreign Press Association’s awards). These...
-

 79Cyber Crime
79Cyber CrimeAndroid scam: Firms fined over $500,000 for malicious apps’ hidden subscriptions
Three UK firms have been fined over $500,000 for a scam that involved Android apps signing up to a subscription service, and...
-

 253Cyber Events
253Cyber EventsAnonymous Shuts Down Oakland Police, Fire Dept, City Websites
The online hacktivist Anonymous has conducted a massive cyber attack on the official website of Oakland police, fire department and city website....
-
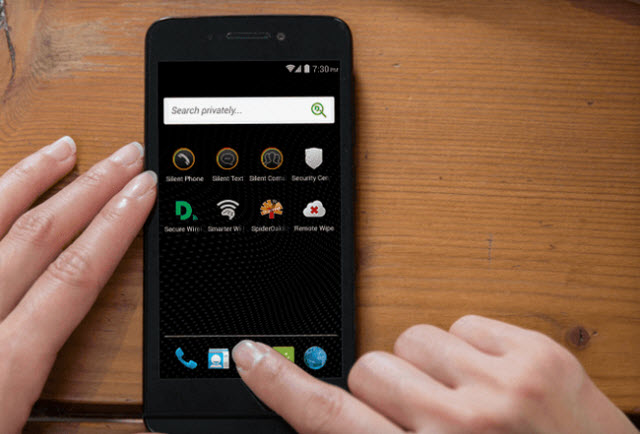
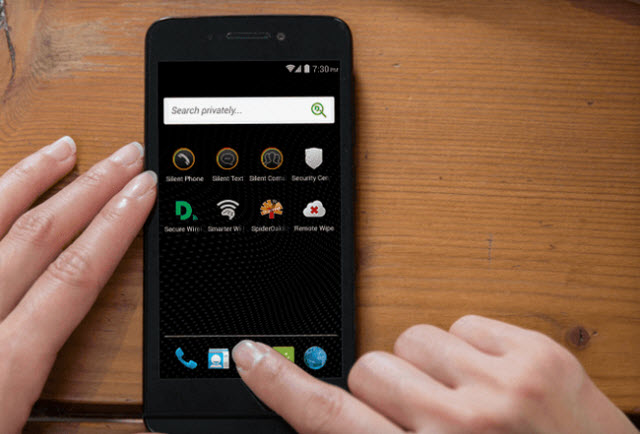 186Privacy
186PrivacyPrivacy focused Blackphone app store in development
Blackphone - the Android smartphone that pushes privacy and security above all else - is to open an app store set to...
-

 85Cyber Crime
85Cyber CrimeAdvertising fraud: a quarter of digital ads stolen by cybercriminals’ bots
Nearly a quarter of digital advert impressions are faked, according to a new study. This advertising fraud is set to cost advertisers...
-
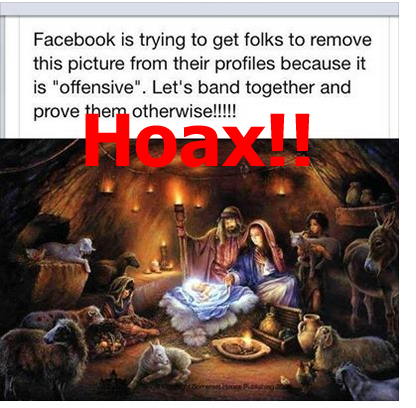
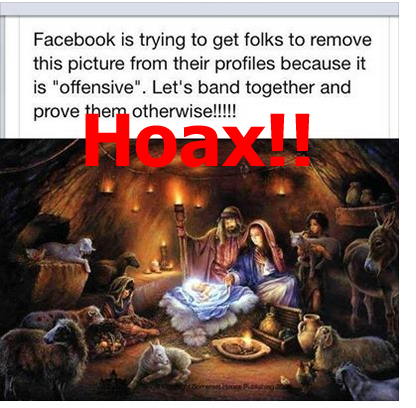 122Opinion
122OpinionTrust, Truth and Hoaxes in Social Media
Social networks are fun, but can also spread misinformation and worse. We discuss myths about your contract with Facebook, and whether British...
-
 278Small business
278Small businessCompany data at risk by widespread employee access
A large number of companies are leaving their confidential files at risk by over-sharing with employees, according to a new survey by...
-

 83Cyber Crime
83Cyber CrimeBebe clothing store suffers payment card breach
The clothing chain Bebe has been the latest company to suffer a breach of payment card information to hackers, reports PC World.
-

 273Cyber Crime
273Cyber CrimeSony Pictures hacking traced to Thai hotel as North Korea denies involvement
The identity of the Sony Pictures hackers who attacked last week remains a mystery, but we have an alleged location where the...
-

 63Cyber Crime
63Cyber CrimeTor a major source of bank fraud, says US Treasury Dept.
Tor has been used to mask the identities of cybercriminals in a significant number of bank frauds for over a decade, according...
-

 167Secure Coding
167Secure CodingLearn to Code
For those of you who would like to code in their free time or just gain more knowledge in a preferred language...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




