Featured News
-

 123Hacking
123HackingEven skateboards can be hacked
It seems even the humble skateboard isn't immune to hacking, as The Register reports that the 'Boosted' brand of electric skateboards has...
-

 121Privacy
121PrivacyMobile security: flaw allows hackers to read texts and listen to calls
Hackers can eavesdrop on your phone calls and text messages even with cell networks using "the most advanced encryption available" according to...
-

 85Cyber Crime
85Cyber CrimeUK Office of Communications reveals nature of recent cyberattacks
A Freedom of Information request to the UK's Office of Communications has revealed exactly how persistent hackers are at attacking government departments...
-

 291News
291NewsIran hacked Vegas Casino wiping hard drives, shutting down email
On the morning of February 10, 2014, the Las Vegas Sands casino, something was not right. Computers were flat-lining, telephone lines stopped...
-

 221News
221NewsOnline Transaction Company Payza Blog Hacked by Pakistani Hackers.
The famous Pakistani hacking group going with the handle of MadLeets has hacked the official blog of the U.S based online transaction company Payza...
-

 201Cyber Crime
201Cyber CrimeTarget breach 12 months on: a year of lessons learned
The Target hack that was revealed one year ago today brought new levels of awareness to the problem of cybercrime. Today we...
-

 182Hacking
182HackingICANN computers compromised by hackers
The nonprofit organization that looks after name and internet domains has been hit by a spear phishing hack that has compromised company...
-

 194Privacy
194PrivacyUber considers biometrics in bid to improve safety
The ride-sharing app Uber has unveiled new security plans to screen drivers, helping ensure passenger safety, Engadget reports.
-

 159Cyber Crime
159Cyber CrimeWebcam security – how to lock down the cameras in your home
Our tips will help you hacker-proof anything from baby monitors to surveillance cameras - and keep your home private.
-
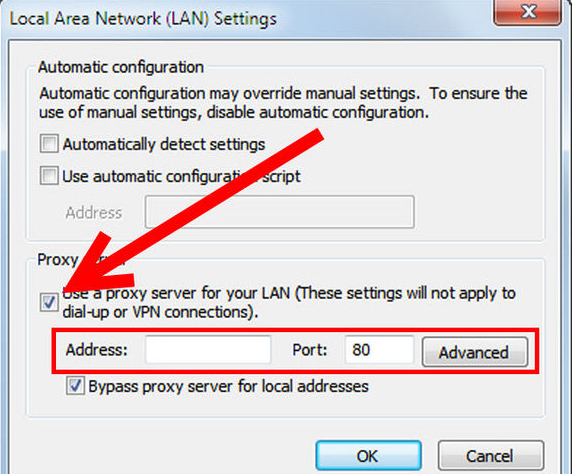
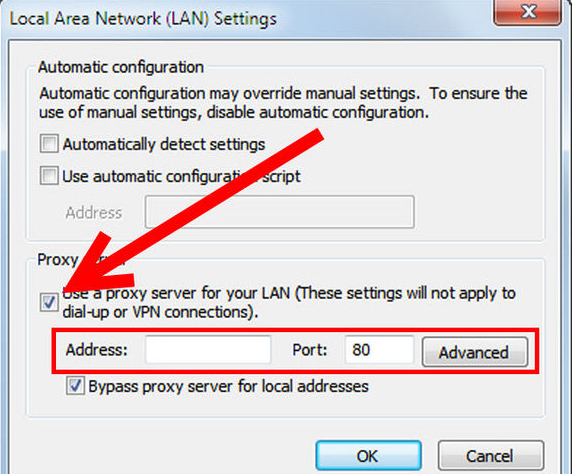 260How To
260How ToTips to stay safe on the Internet
Within the modern digital era that we live in today, we are constantly connected to the Internet either through a desktop PC,...
-

 306Banking
306BankingDutch University unveils ‘fraud proof’ credit card concept
A Dutch university has reportedly made great steps towards making the dream of a 'fraud-proof' credit card a reality by utilizing quantum...
-

 388Cyber Crime
388Cyber CrimeTorrentLocker — Ransomware in a country near you
Today, we are publishing research on ransomware that emerged in 2014. We have posted blog articles about this threat before, to raise...
-

 220Social Media
220Social MediaFacebook scam: You won’t get a car for liking posts…
A new Facebook scam is doing the rounds promising users of the social network the chance to win a brand new car,...
-

 90Cyber Crime
90Cyber CrimeTorrentLocker: Racketeering ransomware disassembled by ESET experts
Security experts at ESET have released their latest research into the notorious TorrentLocker malware, which has infected thousands of computer systems around...
-
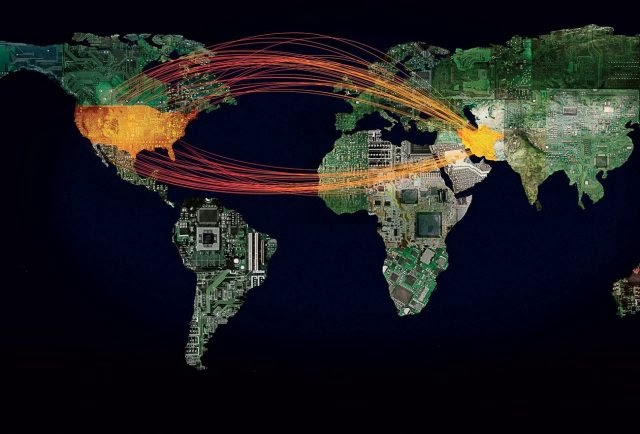
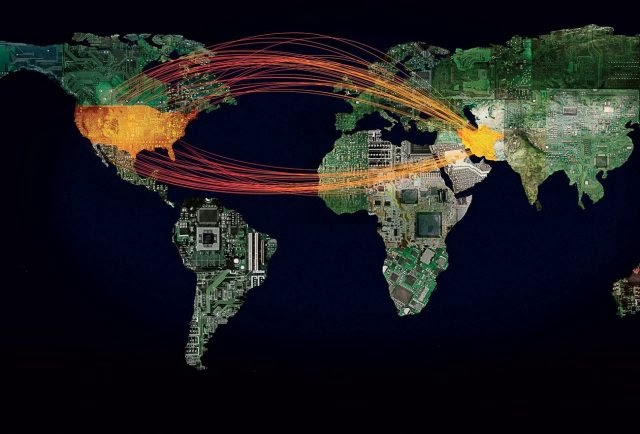 314Cyber Crime
314Cyber CrimeFBI: Iran Hackers May Conduct Cyber Attacks on U.S Defence, Energy Sector
US energy, defense and educational institutions are the top targets of a possible sophisticated cyber attack from the Iranian hackers, says a...
-

 282Small business
282Small businessHypercom payment terminals bricked… but not by malware
When 'several thousand' payment terminals across the country stopped working last week, it would be easy to jump to the conclusion that...
-

 274News
274NewsCops scan social media to help access your ‘threat rating’: Reuters
Recent events have steered the national focus onto aggressive law enforcement and the public is not at ease with the situation. Physical...
-
 378Data Security
378Data SecurityMost Sophisticated Malware Campaign Targeting Diplomats, iPhones, Android, and PC.
Researchers from Blue Cat Labs are calling it the Inception attack framework, in reference to the movie “Inception” where a thief entered...
-
News
UK Dept of Education Sub-Domain Hacked by Pro-Palestinian Hackers.
A pro-Palestinian hacker going with the handle of ‘AlFeRoX’ hacked and defaced the sub-domain of United Kingdom’s Department of Education in support of a...
-

 188Cyber Crime
188Cyber CrimeFBI outlines proposals for dealing with cybercrime to Congress
Joseph Demarest, assistant director at the FBI, has been testifying on the threats of cybercrime to a Senate Committee on Banking, Housing...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




