Featured News
-
 104Cyber Crime
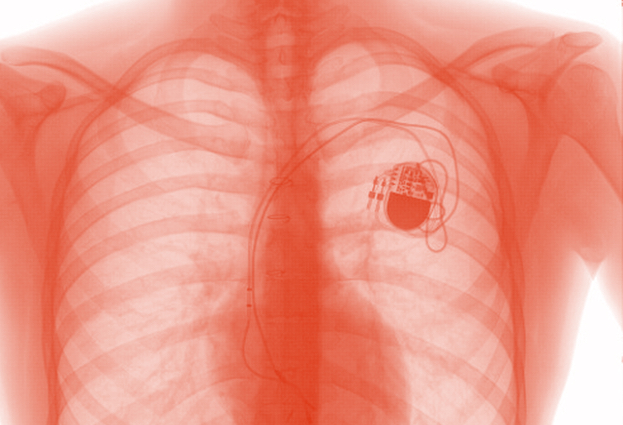
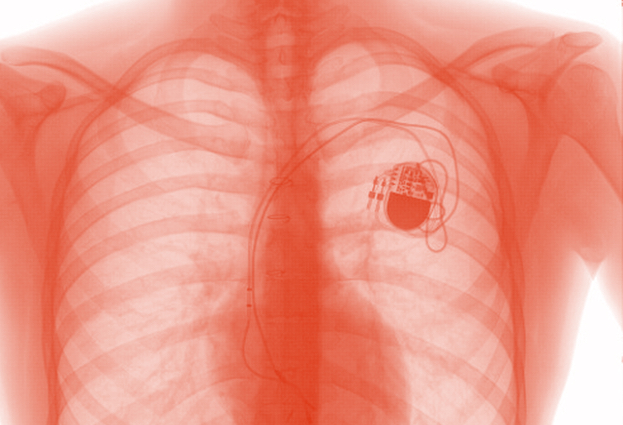
104Cyber CrimeCould hackers give you a heart attack or drugs overdose?
There is growing concern that in the rush to embrace technology to save and improve the lives of patients, medical scientists may...
-
 191How To
191How ToReady, set, shop: 10 top tips for a safe shopping season
Tips for safe holiday shopping: whether you shop online or at the mall, there are some simple strategies that can protect your...
-
 404Privacy
404PrivacyCounter surveillance tech – can gadgets spy‑proof your life?
Over the past few years, counter surveillance gadgets which might have been the preserve of secretive government departments a decade ago have...
-

 231Exploitation
231ExploitationCreate your own USB Password stealer
This tutorial will walk you through setting up a USB flash drive to steal the saved passwords on a computer. Method 1...
-
 415Cyber Crime
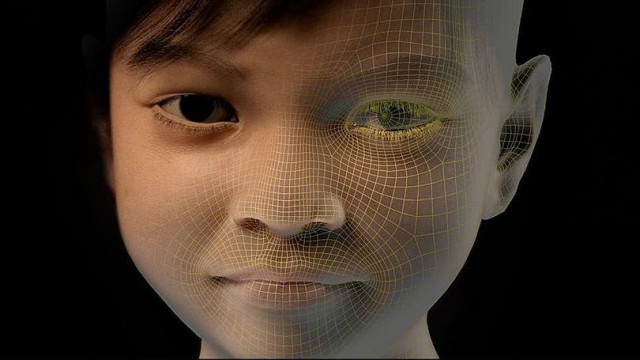
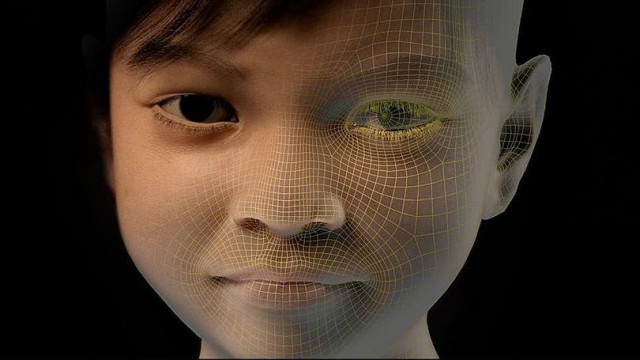
415Cyber Crime10-Year-Old Filipino Virtual Girl “Sweetie” Takes Pedophile To Prison In Australia
An Australian citizen Scott Robert Hansen, 37, was sentenced to one year in prison for keeping obscene conversations with children on the internet. Hansen...
-

 100Malware
100MalwareTop 5 Scariest Zombie Botnets
An army of the undead, wreaking havoc on the Internet – it's a nightmare scenario that has played out many times as...
-

 332Lists
332ListsTop Five Best But Lesser Known Features of Android 5.0 Lollipop
As I’ve written in my earlier posts, Android 5.0 Lollipop is the most significant change in Android line-up since 2011’s Android Ice...
-

 180Malware
180MalwareYahoo, Match and AOL hit by ransomware
Cybercriminals taking advantage of a 'malvertising' attack on big name sites including Yahoo!, Match.com and AOL were making in the region of...
-

 325Banking
325BankingThe Evolution of Webinject
Last month, we presented “The Evolution of Webinject” in Seattle at the 24th Virus Bulletin conference. This blog post will go over...
-

 91Password
91PasswordWindows 10 to tighten security with prominent 2FA
Microsoft is taking aim at traditional single password systems with the upcoming version of Windows, by including build in two-factor authentication according...
-
 77How To
77How ToLearn cyber security fundamentals (Free course) (online classes)
SANS Cyber Aces Online makes available, free and online, selected courses from the professional development curriculum offered by The SANS Institute, the...
-
 192How To
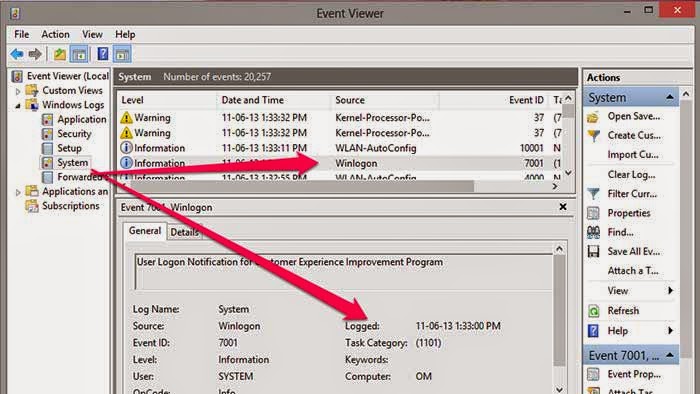
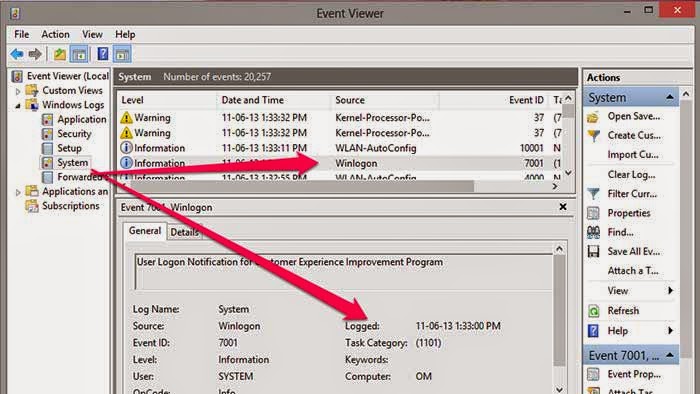
192How ToFind Out If Any One Opens Your Computer Without Your Permission
How to Know Who Logged into your computer and when? In Windows, there is one in-built too will records all events in...
-

 158How To
158How ToProtect your Eyes By Automatically Adjusting Computer Screen Brightness Based On Time of the Day
Today Most of the youngsters using their computers at night very long time than daytime. Staring at your computer screen for the...
-

 67Cyber Crime
67Cyber CrimeiCloud users in China under attack. But who could be after their passwords?
Make sure you are running a half-decent browser, don't ignore browser security warnings, and enable two-factor authentication. That appears to be the...
-

 91Cyber Crime
91Cyber CrimeUK takes aim at serious hacking offenses with planned life sentences
Law makers in Britain are discussing a dramatic increase in sentencing for serious hacking offences, according to The Register. Currently in discussion...
-

 131Password
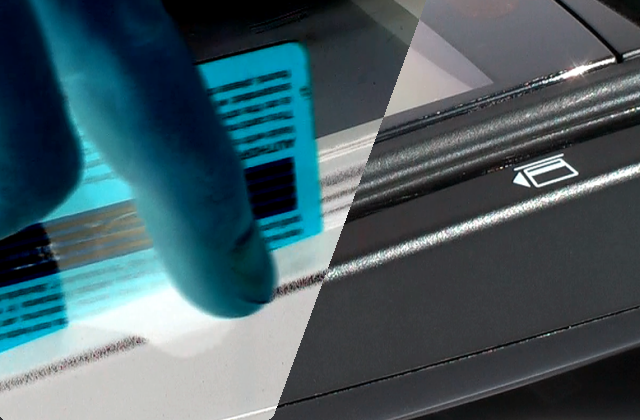
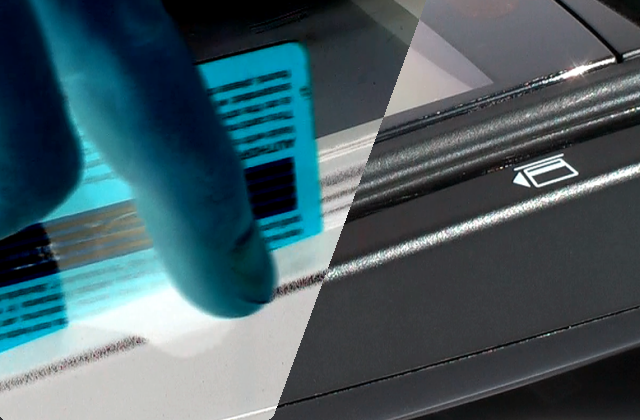
131PasswordGoogle now offers USB key authentication
Google has added an extra layer of security to its browser, by introducing USB authentication to Chrome, the company has announced in...
-
 251Malware
251MalwareBotnet malware: What it is and how to fight it
Malware or malicious computer code has been around in some form or other for over 40 years, but the use of malware...
-
 340Android Hacking
340Android HackingHow to Hack an android phone
In this tutorial i will show you a guide on how to hack someones android phone. First you will need to root...
-

 112Malware
112MalwareMyths about malware: an exploit is the same as malware
In this post we want to share with you a question that arose from the first post in this series: whether exploits...
-

 86Malware
86MalwareStaples the latest to be hit by credit card breach?
Stationary and office supply store Staples is the latest company to be dealing with a credit and debit card breach, according to...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




