Featured News
-
 187News
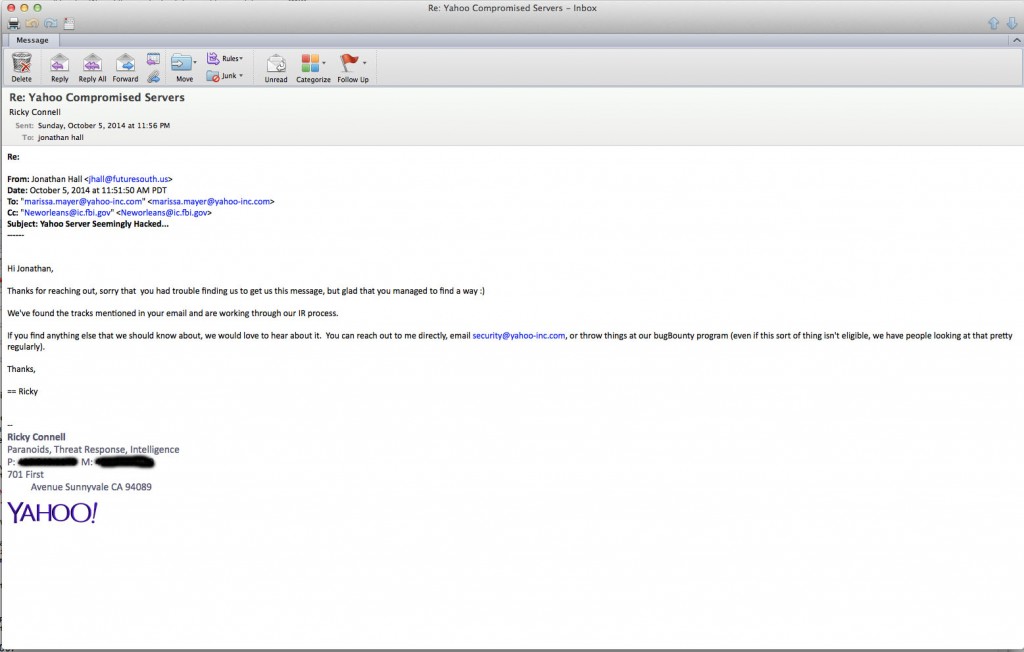
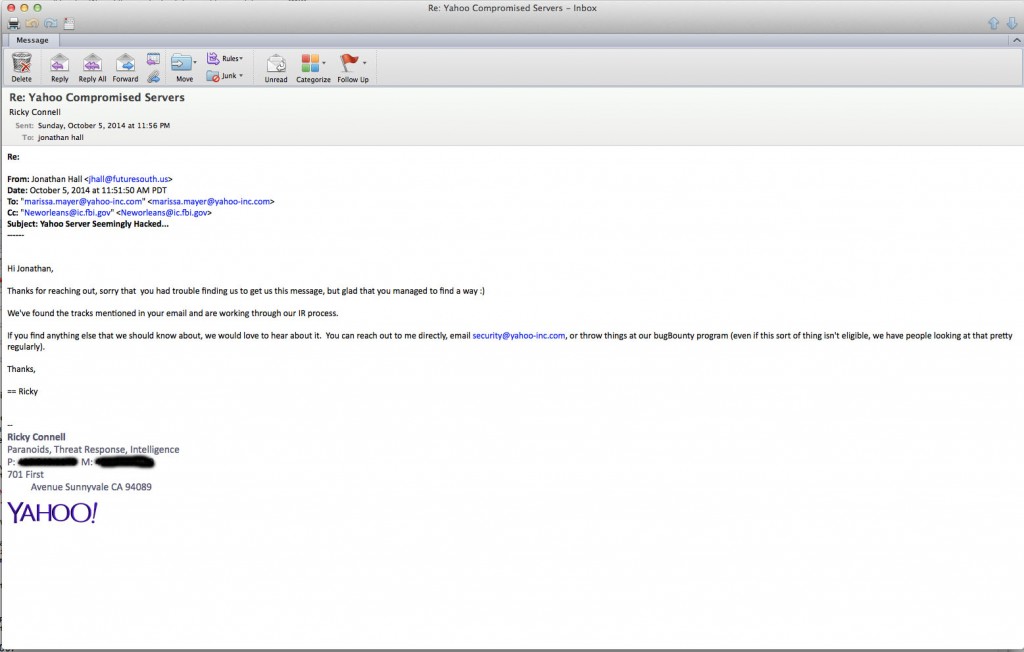
187NewsHackers breach Yahoo! servers through Bash Bug
Romanian hackers used Bash Bug flaw to hackYahoo servers, according to a recent security news update. Jonathan Hall, President of the IT...
-

 97Malware
97Malware‘Unpatchable’ USB exploit posted to GitHub
Techspot reports that a another USB exploit has been discovered by a pair of researchers who have "thrown caution to the wind...
-
 130Privacy
130PrivacyBing: no plans to offer search boost for encrypted websites
Over the summer, Google introduced plans to start giving preference to websites that use HTTPS encryption to try and incentivize good online...
-
 241Lists
241ListsThese Six Word Stories Are Going to Melt Your Brain
I came across this sub-genre of flash fiction about two years ago and I found it extremely captivating. According to the legend,...
-
 194Lists
194Lists12 Weird Cultural Customs From Around the World
This is a list of some weird cultural customs from all around the world. Take a look! 1) In India it is...
-
 327Lists
327ListsTop FossBytes of the Month – September 2014
Dear readers, it is hard to keep track of everything happening around you in tech, science, business and gaming world. So we...
-

 313Cyber Crime
313Cyber CrimeJP Morgan Chase data breach – bank admits 76 million affected
JP Morgan Chase, one of the largest banks in America has admitted that a JP Morgan Chase data breach has affected 76...
-

 411Privacy
411PrivacyUltra‑secure hard drive ‘shatters on demand’
A new gadget from British drive maker Secure Drives forges off into Mission Impossible territory with a genuine, physical 'self-destruct' command which...
-

 160Privacy
160PrivacyGoogle faced with $100m legal action over naked celebrity photos
Google is facing a threat of expensive legal action over the recent leaked naked celebrity photographs, according to IT Pro. The basis...
-

 218Scams
218ScamsSupport Scammers: Hoping to Reign in Spain?
More about the support scammer trend towards finding victims in Spain who aren't fluent English speakers.
-

 69Cyber Crime
69Cyber CrimePhishing attacks ‘enough’ to breach many industrial systems
Basic phishing attacks and easily available tools are all that is needed to compromise many industrial control systems, the head of cybersecurity...
-

 192Privacy
192PrivacyPeople are willing to trade private data for pistachio cookies
Many New Yorkers don’t place a particularly high value on their private data - from fingerprints to social security numbers - having...
-

 98Malware
98MalwareFBI opens malware tool for public “crowdsourcing”
The FBI has opened up its previously in-house malware analyzing tool to the public in order to crowdsource more samples for speedier...
-

 131Hacking
131HackingFound an exploit in Chrome? You could have just earned $15,000
In a bid to improve the security of its Chrome browser, Google has announced that it is upping the ‘bounty’ paid to...
-

 328News
328NewsWhy FBI is so concerned about Apple and Google’s smartphone encryption plans?
The Federal Bureau of Investigation (FBI) is not happy with Apple and Google for including encryption on their smartphone products, the agency’s director said Thursday....
-
 104Privacy
104PrivacySnapchat privacy – spam deluge may make users feel fat
Concerns over Snapchat privacy rocketed this week after users were bombarded with spam messages written in a style which suggests that a...
-

 203How To
203How ToHow to fix Shellshock Bash on Mac OS X: Mavericks edition
Apple Mac OS X users concerned about the Bash vulnerability dubbed Shellshock got some relief late yesterday as Apple published fixes for...
-

 70Cyber Crime
70Cyber CrimeStealthGenie CEO arrested for marketing ‘illegal stalking app’
The creator of an app that secretly allows you to monitor another person’s smartphone usage without their knowledge has been arrested in...
-

 101Mobile Security
101Mobile SecurityFBI Director “very concerned” with smartphone encryption
With Apple, Google and other tech companies responding to users’ demands for privacy with further smartphone encryption options, not everyone is happy....
-
 210Scams
210ScamsSupport Scams: Expect the Scammish Inquisition*
An update on support scams: but are the scammers looking for fresh fields and posturings new?
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




