Featured News
-

 317Hacked
317HackedCyber War Between India and Pakistan Gets Uglier, Websites Hacked
As a result of Bilawal Bhutto’s tweet regarding Kashmir and growing tension between India and Pakistan on LoC and International Border, hackers...
-

 798News
798NewsEmma Watson Nude Video/Pictures Scam Delivers Malware, Hijacks Facebook Session
The Curious Case of Brit Celeb Emma Watson’s leaked Facebook Video –Users Helplessly Welcomed Trojans instead of her Nude Pictures The scam of...
-

 175Malware
175MalwareWeek in security: Dubai Police use Google Glass facial recognition, Bugzilla gets bugged and ‘Unpatchable’ USB exploit lands on GitHub
This week in security, we covered a full range of privacy and malware, with controversial plans to equip police officers with facial...
-

 94Malware
94MalwareDairy Queen hit by card data stealing malware
Dairy Queen has become the latest company to be hit by payment card stealing malware, reports the Wall Street Journal. The breach...
-

 143How To
143How ToCyber Security Awareness Month: It’s on!
October is National Cyber Security Awareness Month in America and each year this program brings more and more attention to issues that...
-

 102Malware
102MalwareFuture malware might offer real functions to avoid detection
Malware may begin to offer genuinely helpful functionality in the future, in order to "fly under the radar" and fake legitimacy before...
-

 78Malware
78MalwareEuropean ATMs under malware attack
At least 50 cash machines in Eastern Europe have been targeted by malware that allows the hacker to withdraw up to 40...
-

 159Privacy
159PrivacyEllo privacy – what you need to know
For any security-conscious user, there are a few things worth remembering once you have secured that crucial invitation - we offer a...
-

 188Lists
188ListsMahendra Singh Dhoni Only Indian in Forbes’ Most Valuable Athlete Brand List
Mahendra Singh Dhoni is the only Indian in Forbes’ most valuable athlete brand list. He is ranked fifth after the likes of...
-

 101Malware
101MalwareManual fixes to USB malware revealed… with a catch
Since the BadUSB malware was released to the public with hopes of forcing a fix, a solution has emerged from the researchers...
-

 142Malware
142MalwareSednit espionage group now using custom exploit kit
For at least five years the Sednit group has been relentlessly attacking various institutions, most notably in Eastern Europe. The group used...
-

 88Cyber Crime
88Cyber CrimeYahoo told to “pull your pants up” after Shellshock hack claims
Yesterday, security researcher Jonathan Hall, of a company called Future South Technologies, accused Yahoo of having suffered a serious security breach via...
-

 147News
147NewsWindows 10 Technical Preview: A Spy in Disguise?
Windows 10 Technical Preview (TP), a trial version released last week, collects and transmits lots of user data to Microsoft, according to...
-

 184Privacy
184PrivacyGoogle Glass facial recognition used by Dubai Police force
The police force of Dubai will soon be equipped with crime-fighting face recognition technology via Google Glass, according to Reuters. The software,...
-

 73Cyber Crime
73Cyber CrimeCelebgate: Nude photo hack continues as first male celebrity targeted
The son of American wrestler Hulk Hogan has been the latest celebrity to fall victim to theft and publication of naked pictures...
-
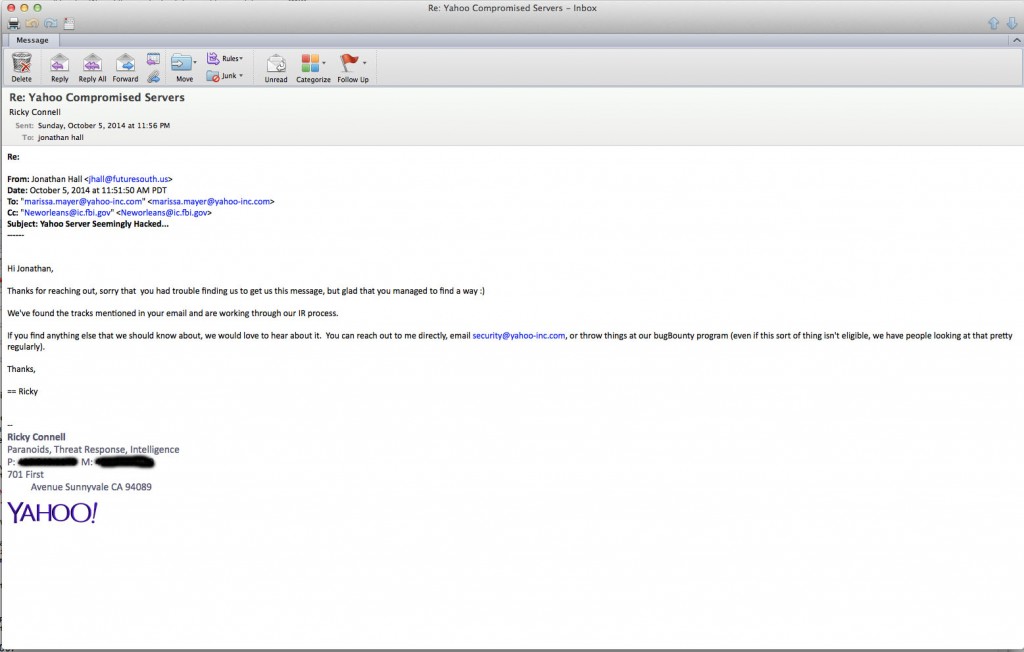
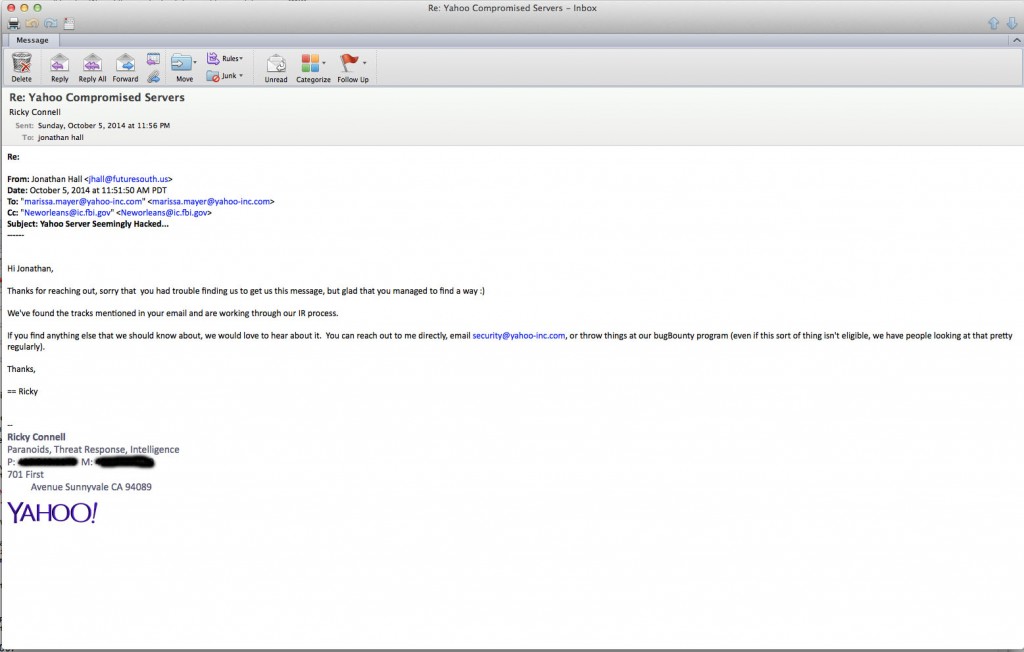 193News
193NewsHackers breach Yahoo! servers through Bash Bug
Romanian hackers used Bash Bug flaw to hackYahoo servers, according to a recent security news update. Jonathan Hall, President of the IT...
-

 101Malware
101Malware‘Unpatchable’ USB exploit posted to GitHub
Techspot reports that a another USB exploit has been discovered by a pair of researchers who have "thrown caution to the wind...
-
 135Privacy
135PrivacyBing: no plans to offer search boost for encrypted websites
Over the summer, Google introduced plans to start giving preference to websites that use HTTPS encryption to try and incentivize good online...
-
 246Lists
246ListsThese Six Word Stories Are Going to Melt Your Brain
I came across this sub-genre of flash fiction about two years ago and I found it extremely captivating. According to the legend,...
-
 197Lists
197Lists12 Weird Cultural Customs From Around the World
This is a list of some weird cultural customs from all around the world. Take a look! 1) In India it is...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




