Featured News
-

 230How To
230How ToHow to Install Cinnamon on Ubuntu 14.04?
Cinnamon is a popular Linux desktop based on GTK+ that got its start as a fork of GNOME Shell . It is...
-
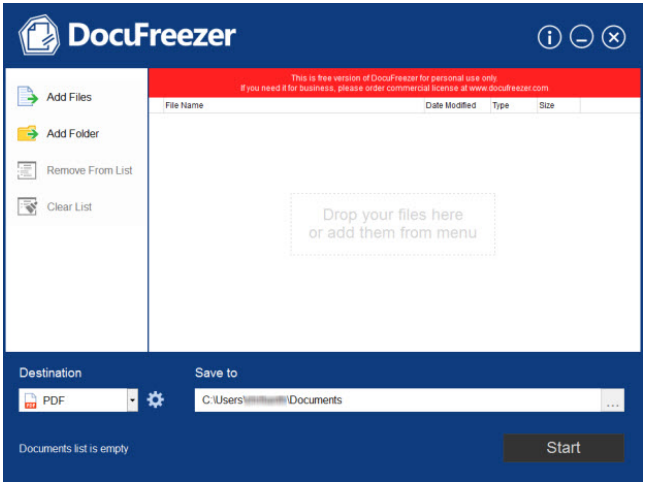
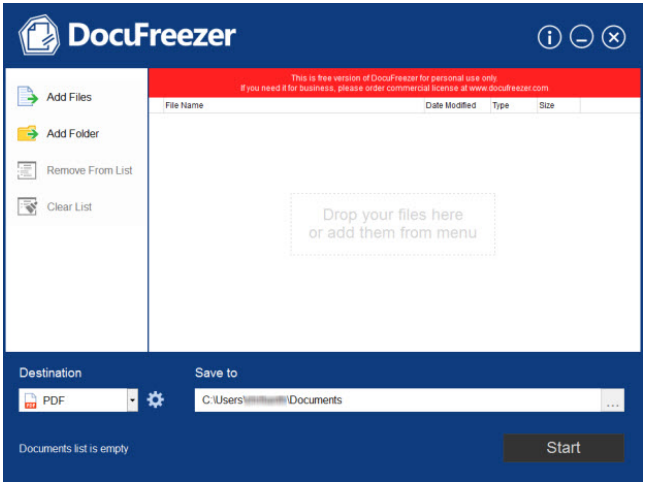 222How To
222How ToDocuFreezer: Offline conversion of documents to PDF and JPEG’s demystified [Review]
People handling hundreds of documents weekly as part of their personal or professional work know how it feels when their internet connection...
-

 416Password
416PasswordBank security – Barclays to offer vein‑scanner to big accounts
A bank is to allow remote log-ons using a hi-tech vein-scanning biometric system for large corporate accounts. The bank security system, using...
-

 86Malware
86MalwareTorrentLocker now targets UK with Royal Mail phishing
Three weeks ago, iSIGHT Partners discovered a new Ransomware encrypting victims’ documents. They dubbed this new threat TorrentLocker. TorrentLocker propagates via spam...
-

 71Cyber Crime
71Cyber CrimeNow your LinkedIn account can be better protected than ever before
LinkedIn may not have a spotless record when it comes to security and privacy, but we should give them credit when they...
-

 372Password
372PasswordIFA 2014: Huawei phablet has ‘iPhone‑like’ fingerprint ID
Another major phone brand has added biometric security to a flagship smartphone as Huawei unveiled the ultra-thin Mate P7, complete with a...
-

 123Scams
123ScamsYouTube scam warning after fake “suspension” emails strike users
A YouTube scam where users are threatened with suspension for an unspecified “violation” of the video site’s guidelines has been circulating via...
-

 386Cyber Crime
386Cyber CrimeCar hacking – are one‑third of thefts ‘electronic hacks’?
The government is to work with car manufacturers to prevent hackers using electronic means to break into increasingly hi-tech vehicles in Britain...
-

 83Cyber Crime
83Cyber CrimeCredit card security fears – could Home Depot breach be biggest yet?
Shoppers at Home Depot stores may have had their credit card details leaked online, after a massive batch of card information went...
-

 84Password
84PasswordSecure password: CyberVor hoard of 1.2 billion details ‘used in attack’
Hosting provider Namecheap said that it has come under attack from hackers apparently using the “Cybervor” hoard of 1.2 billion usernames and...
-

 365Lists
365ListsTop 5 Websites to Download Free Softwares
Have you wasted a lot of time in searching for a free software online? I know sometimes it can get very frustrating...
-
 402News
402NewsPossible iCloud accounts hacking: Nude Photos of 98 Hollywood Celebrities leaked online
An unknown hacker has hacked and leaked nude pictures of 100+ high profile Hollywood celebrities on Sunday. The nude photos are available...
-

 213Cyber Crime
213Cyber CrimeAnonymous to attack Pakistani Government against police brutality
The online hacktivist Anonymous has announced to conduct a massive cyber attack on Pakistani government servers against yesterday’s police brutality on unarmed...
-

 353Cyber Crime
353Cyber CrimeCybercrime: Top experts to form international crook‑hunting force
As many as 18 top cybercrime experts from around the world will form a new Joint Cybercrime Action Task Force based in...
-

 396Hacking
396HackingWi‑Fi password – “one second” hack allows attackers into many routers
A push-button function on many wireless routers designed to bypass the Wi-Fi password and provide quick access to the network could allow...
-
 166News
166NewsOpPakistan: Hackers deface Pakistani govt portal (Pakistan.gov.pk) to Support Protests
Hactivists have decided to play their role in on going political crisis, as a result the official portal of government of Pakistan...
-

 239Lists
239Lists5 Best URL Shortening Services Online
You may not be knowing of URL shortening but I can bet you that you click on these links every time you...
-

 259News
259NewsMassive Cyber Attack: Anonymous takes down Pakistan Army and Govt websites against Police brutality
The online hacktivist Anonymous has conducted as massive cyber attack on Pakistanigovernment, as a result Pakistani Army and government websites have been...
-

 63Cyber Crime
63Cyber CrimeWeek in Security: Game over in Korea, cellphone snoops and phishy Bitcoins
Gamers and cellphone users were targeted by criminal groups around the world this week - while retailers continued to suffer at the...
-

 273Privacy
273PrivacyInternet privacy: Seven rules to keep secrets safe
You are never truly invisible online - and even if you equip yourself with an arsenal of privacy tools, you'll still be...
The Latest
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor




