Featured News
-

 362Cyber Crime
362Cyber CrimeMH17 plane crash victims exploited by cold‑hearted scammers
The sad truth is that scammers and fraudsters don't have any conscience, and are prepared to do anything if it might net...
-

 132Privacy
132PrivacyBitcoin creator – could he be ‘outed’ after email ransom?
Bitcoin’s mysterious creator, who goes by the pseudonym ‘Satoshi Nakamoto’, could be about to have his identity made public, after a series...
-

 143Cyber Crime
143Cyber CrimeNude Celebs, Target, Home Depot: Who is to blame? Criminals!
The blame game rages on in the wake of Celebgate and massive payment card hacks like Home Depot and Target, as though...
-

 74Cyber Crime
74Cyber CrimeOnline ad threat – Yahoo, Amazon, YouTube ‘victims of malvertising’
Anyone who has visited popular domains such as YouTube.com, Amazon.com or Ads.Yahoo.com could be a victim of a new, mutating malware attack...
-
 210How To
210How ToHow to Install a Screensaver in Ubuntu ?
You know the time when LCD, LED screens were not common and CRT monitors were mostly used for video output? it was...
-

 154Privacy
154PrivacyChat apps leak: Billion app users from OKCupid to Grindr at risk
Nearly a billion users of a dozen chat apps for Android including popular apps such as Instagram, Oovoo, OKCupid and Grindr could...
-

 234Cyber Crime
234Cyber CrimeHome Depot credit cards: chain confirms breach, fraud spikes
The world’s largest home improvement chain store, Home Depot, yesterday confirmed a data breach affecting credit cards and debit cards used in...
-

 93Privacy
93PrivacyPrivate browsing – Americans ‘care deeply’ about privacy
A new Harris survey found that almost all Americans care about online privacy, and 71% said that they ‘care deeply’ about it....
-

 102Password
102PasswordStrong password – Chrome now offers ‘pronounceable’ choices
Google Chrome will now recommend pronounceable password hoices, according to developer and Chrome “happiness evangelist” Francois Beaufort, who announced the change via...
-
 199Geek
199GeekR.I.P MSN Messenger :(
It’s time to say good bye to once the best instant messaging platform MSN Messenger (also known as Windows Live Messenger). Microsoft started shutting...
-

 231How To
231How ToHow to Install Cinnamon on Ubuntu 14.04?
Cinnamon is a popular Linux desktop based on GTK+ that got its start as a fork of GNOME Shell . It is...
-
 222How To
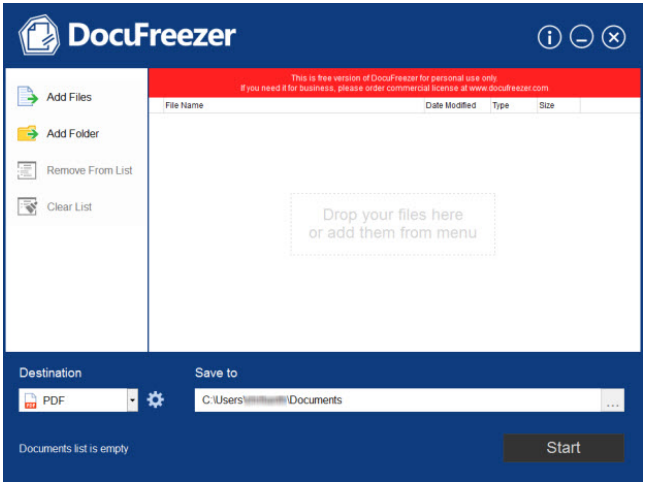
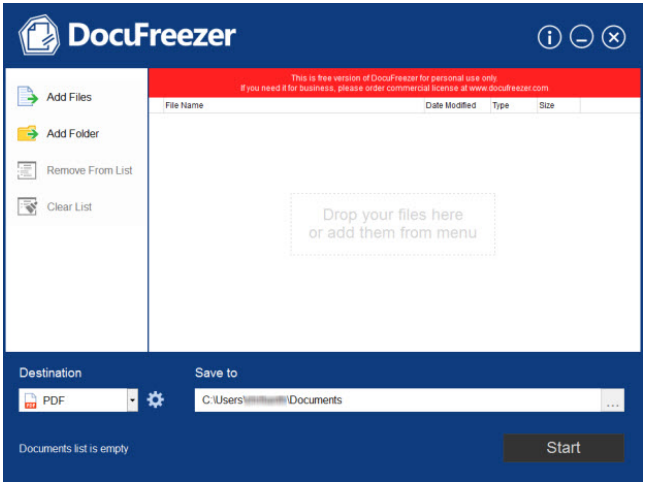
222How ToDocuFreezer: Offline conversion of documents to PDF and JPEG’s demystified [Review]
People handling hundreds of documents weekly as part of their personal or professional work know how it feels when their internet connection...
-

 416Password
416PasswordBank security – Barclays to offer vein‑scanner to big accounts
A bank is to allow remote log-ons using a hi-tech vein-scanning biometric system for large corporate accounts. The bank security system, using...
-

 87Malware
87MalwareTorrentLocker now targets UK with Royal Mail phishing
Three weeks ago, iSIGHT Partners discovered a new Ransomware encrypting victims’ documents. They dubbed this new threat TorrentLocker. TorrentLocker propagates via spam...
-

 71Cyber Crime
71Cyber CrimeNow your LinkedIn account can be better protected than ever before
LinkedIn may not have a spotless record when it comes to security and privacy, but we should give them credit when they...
-

 373Password
373PasswordIFA 2014: Huawei phablet has ‘iPhone‑like’ fingerprint ID
Another major phone brand has added biometric security to a flagship smartphone as Huawei unveiled the ultra-thin Mate P7, complete with a...
-

 123Scams
123ScamsYouTube scam warning after fake “suspension” emails strike users
A YouTube scam where users are threatened with suspension for an unspecified “violation” of the video site’s guidelines has been circulating via...
-

 386Cyber Crime
386Cyber CrimeCar hacking – are one‑third of thefts ‘electronic hacks’?
The government is to work with car manufacturers to prevent hackers using electronic means to break into increasingly hi-tech vehicles in Britain...
-

 83Cyber Crime
83Cyber CrimeCredit card security fears – could Home Depot breach be biggest yet?
Shoppers at Home Depot stores may have had their credit card details leaked online, after a massive batch of card information went...
-

 84Password
84PasswordSecure password: CyberVor hoard of 1.2 billion details ‘used in attack’
Hosting provider Namecheap said that it has come under attack from hackers apparently using the “Cybervor” hoard of 1.2 billion usernames and...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




