Featured News
-

 365Lists
365ListsTop 5 Websites to Download Free Softwares
Have you wasted a lot of time in searching for a free software online? I know sometimes it can get very frustrating...
-
 403News
403NewsPossible iCloud accounts hacking: Nude Photos of 98 Hollywood Celebrities leaked online
An unknown hacker has hacked and leaked nude pictures of 100+ high profile Hollywood celebrities on Sunday. The nude photos are available...
-

 214Cyber Crime
214Cyber CrimeAnonymous to attack Pakistani Government against police brutality
The online hacktivist Anonymous has announced to conduct a massive cyber attack on Pakistani government servers against yesterday’s police brutality on unarmed...
-

 354Cyber Crime
354Cyber CrimeCybercrime: Top experts to form international crook‑hunting force
As many as 18 top cybercrime experts from around the world will form a new Joint Cybercrime Action Task Force based in...
-

 397Hacking
397HackingWi‑Fi password – “one second” hack allows attackers into many routers
A push-button function on many wireless routers designed to bypass the Wi-Fi password and provide quick access to the network could allow...
-
 167News
167NewsOpPakistan: Hackers deface Pakistani govt portal (Pakistan.gov.pk) to Support Protests
Hactivists have decided to play their role in on going political crisis, as a result the official portal of government of Pakistan...
-

 240Lists
240Lists5 Best URL Shortening Services Online
You may not be knowing of URL shortening but I can bet you that you click on these links every time you...
-

 261News
261NewsMassive Cyber Attack: Anonymous takes down Pakistan Army and Govt websites against Police brutality
The online hacktivist Anonymous has conducted as massive cyber attack on Pakistanigovernment, as a result Pakistani Army and government websites have been...
-

 64Cyber Crime
64Cyber CrimeWeek in Security: Game over in Korea, cellphone snoops and phishy Bitcoins
Gamers and cellphone users were targeted by criminal groups around the world this week - while retailers continued to suffer at the...
-

 274Privacy
274PrivacyInternet privacy: Seven rules to keep secrets safe
You are never truly invisible online - and even if you equip yourself with an arsenal of privacy tools, you'll still be...
-

 103Opinion
103OpinionAnyone want to know my Social Security Number?
Your home may be your castle, but on social networks, your friends are your perimeter. Will they enclose and protect your personal...
-

 201Cyber Crime
201Cyber CrimeAndroid security mystery – ‘fake’ cellphone towers found in U.S.
Seventeen mysterious cellphone towers have been found in America which can only be identified by a heavily customized handset built for Android...
-
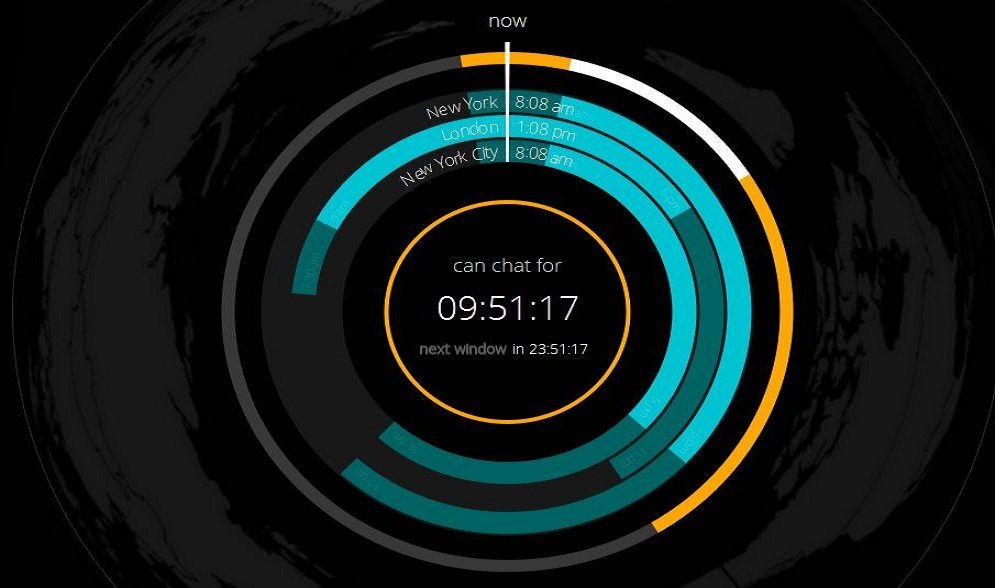
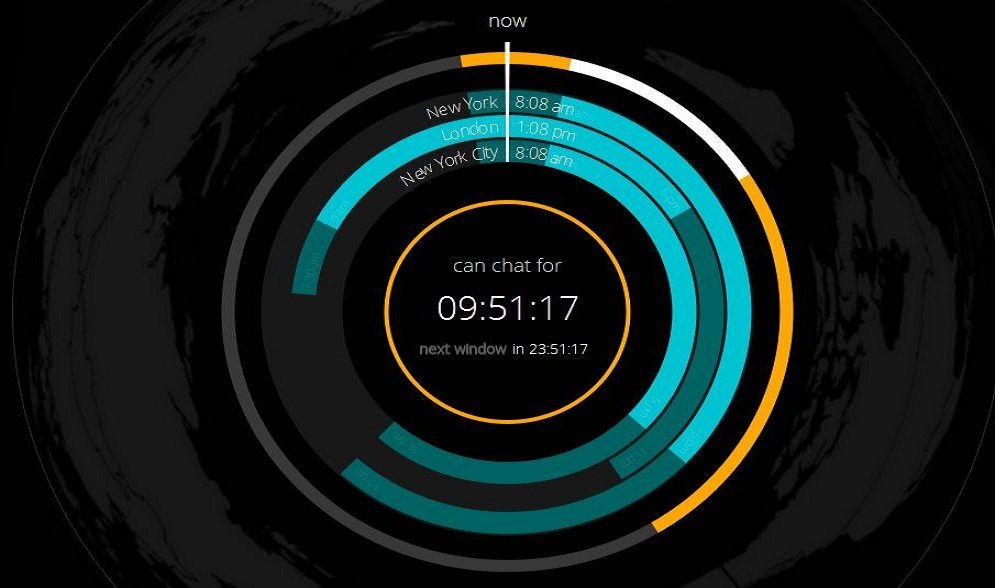 161How To
161How ToHow to Find Suitable Time to Chat/Talk Between Different Time Zones?
So you have contacts all around the world, or you are in a job that needs you to talk to people in...
-

 186Cyber Crime
186Cyber CrimeGoogle dorks – FBI warning about dangerous ‘new’ search tool
The FBI has issued a warning to police and other emergency response personnel about a lethal new tool which 'malicious actors' have...
-

 196Cyber Crime
196Cyber CrimeData breach in South Korea hits 27 million – half the population
A data breach of staggering proportions has hit South Korea - involving 27 million people and 220 million private records - all...
-

 84Privacy
84PrivacySurveillance fears over systems which ‘follow’ cellphone users
Concern is growing over the export of surveillance equipment which can track the movements of anyone carrying a cellphone. Such technnologies are...
-

 155News
155NewsGoogle Image Search Hacked? Search results filled with Russian car crash images
Users witness looking at pictures of Russian car crash regardless of what they searched on Google Images. If someone searched for ‘cat’ the search result...
-

 65Cyber Crime
65Cyber CrimeOnline fraud – POS malware has now hit 1,000 U.S. firms
More than a thousand U.S. businesses have been affected by point-of-sale malware - malicious software written specifically for online fraud, to steal...
-

 82Cyber Crime
82Cyber CrimeGoogle Images hacked? Searches fill with morbid image
An image of a Russian car crash has piled up in Google Images - leading to speculation that the service has been...
-

 236Lists
236Lists2014 Emmy Award Winners : Breaking Bad Wins Big, Game of Thrones Scores Zero
2014 Emmy Awards were pretty much unsurprising and a lot of fan favorites won. NBC drama Breaking Bad won the Emmy Award for...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




