Featured News
-

 86Password
86PasswordBanking security – new apps ‘know’ your touch
Everyone hates passwords - even the guy who invented them - but some bank app users in the Nordic region are experiencing...
-

 230Lists
230ListsTop 5 Torrent sites of 2014
In the world of torrent downloading, you must understand one thing that there always will be more “Leechers” than “Seeders”. Telling about...
-

 91Malware
91MalwarePhishing emails: U.S. nuke authority hit three times
America’s Nuclear Regulatory Commission was successfully attacked three times within the past hree years, by unknown attackers, some foreign - and largely...
-

 158Privacy
158PrivacyTwitter hacked – Cricket legend ‘Beefy’ Botham exposed
One of England’s greatest-ever cricketers, Sir Ian Botham, appeared to have been the victim of a Twitter hack yesterday as an obscene...
-
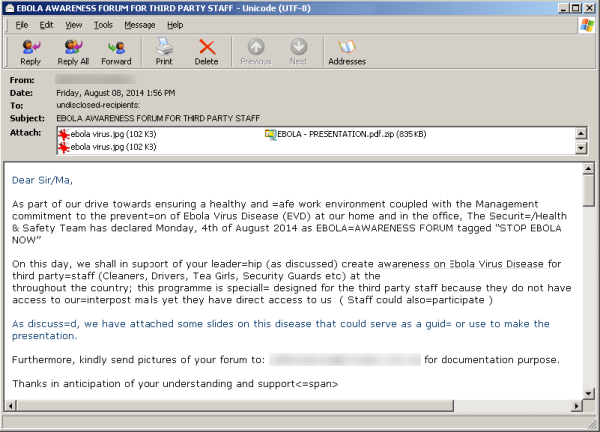
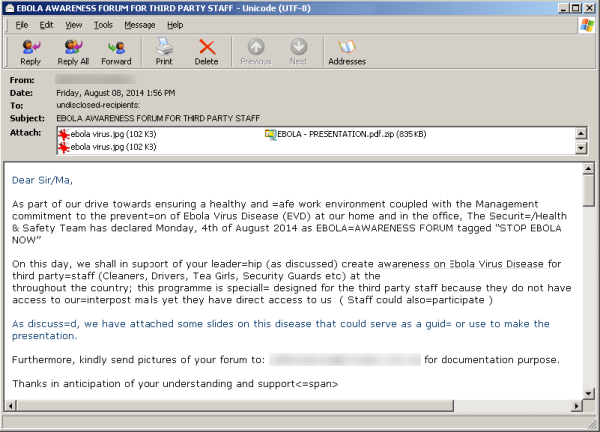 382News
382NewsHackers Sending Fake Ebola Virus reports in emails with Malware and Phishing Links
A new malicious campaign has been identified by security researchers spreading fake news about the Ebola virus, in order to redirect users...
-
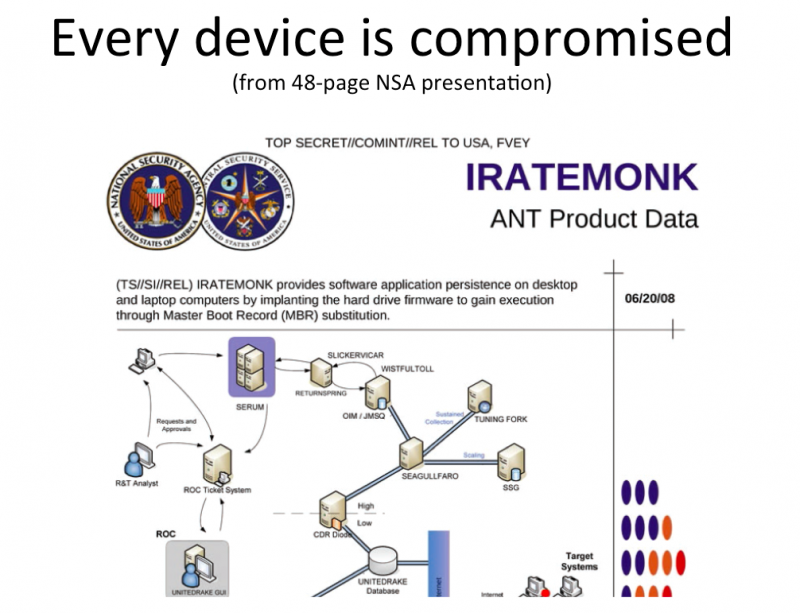
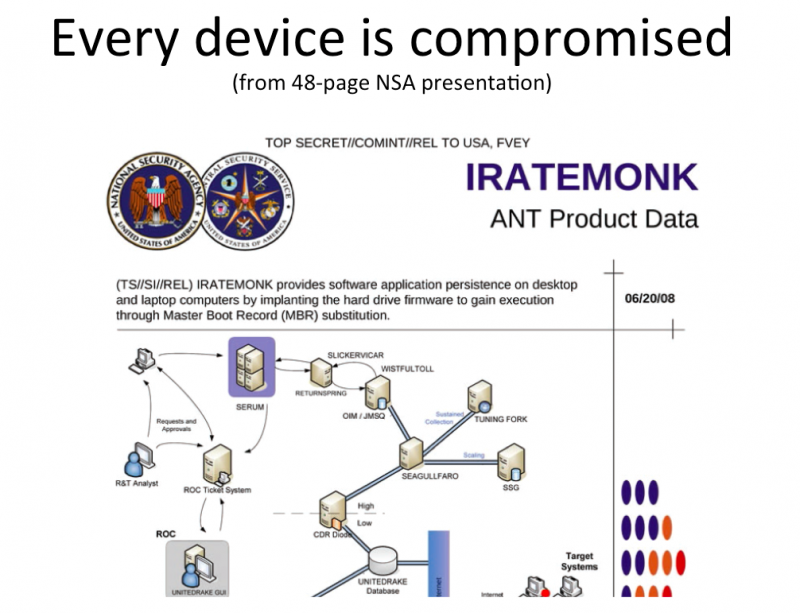 317Geek
317GeekDon’t freak out about Facebook messenger app, NSA already has your chats
Privacy concerns over the Facebook Chat App is at an all time high. Increasingly more and more people are voicing their concern...
-

 186Privacy
186PrivacyPrivacy: Workers “would pay” to stop snoopers
Online privacy has gone from being a minority concern to something that worries the man in the street - after a study...
-

 79Cyber Crime
79Cyber CrimeGamescom: How gaming grew up into a target for crime
Video games have gone since the late 1970s and early 1980s from being a small offshoot of the "traditional" computing industry to...
-

 167Cyber Crime
167Cyber CrimeWeek in security: Blackphone unmasked, RATs vs Androids, and browsers kill cars
Blackphone, billed as a privacy tool to keep the puplic safe ruled the headlines when it was is hacked in five minutes,...
-

 280Scams
280ScamsRobin Williams’ last phone call? Sick Facebook video scam exploits celebrity suicide
Sick-hearted scammers have proven themselves to have no morals once again, exploiting the death of Robin Williams with their latest Facebook scam.
-

 73Cyber Crime
73Cyber CrimeRussian PM has his Twitter account hacked, announces “I resign”
There may be red faces in Red Square, after Russian prime minister Dmitry Medvedev had his Twitter account hacked.
-

 92Password
92Password‘Biometric’ earbuds invisibly prove it’s you, with no need for passwords
Biometrics are touted as a replacement for the passwords and PINs we all know and hate - and Intel’s new earbuds could...
-

 89Malware
89MalwareGamescom 2014: World of Malware?
The gaming industry keeps growing, and the crowds at Cologne's Gamescom 2014, show why big game titles are rapidly becoming a target...
-

 103Scams
103ScamsPhone scams: card fraud with that steak, Sir?
A new telephone scam in upscale restaurants in London, has “convincing” scammers calling restaurant staff and tricking them into believing there's a...
-

 133Hacking
133HackingWill web browsers turn cars lethal?
Two researchers have launched a petition to change how car companies and technology cmpanies work together - with a new villain: in-car...
-

 92Cyber Crime
92Cyber Crime2FA – are big banks failing America?
The Target breach caused real damage to millions of American card users - but big financial institutions are doing little to remedy...
-

 384Cyber Crime
384Cyber CrimeWɑit! Stοp! Is that ℓιηκ what it claims to be?
Can you tell the difference between exɑmple and example? Google adds non-Latin support to Gmail, and we explain why characters matter when...
-

 368Password
368PasswordWi‑Fi security – routers “like fish in a barrel”
Researchers flexed their hacking muscles at DefCon 22 to hunt the technology world’s most defenceless beasts - routers. More than a dozen...
-

 172Privacy
172Privacy‘Secure’ Blackphone hacked in 5 minutes
An ultra-secure phone claimed to be the first privacy-focused smartphone on sale swiftly fell victim to a security researcher - who hacked...
-
 101Malware
101MalwareKrysanec trojan: Android backdoor lurking inside legitimate apps
One of the most important pieces of advice we give Android users is to refrain from downloading applications from dubious sources and...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




