Featured News
-

 91Privacy
91PrivacyThe state of healthcare IT security: are Americans concerned enough?
The privacy and security of medical records is a matter of concern to many Americans now that most are now stored electronically,...
-

 167Hacking
167HackingInternet of things: Hacker unleashes “mayhem” in 200 hotel rooms
Today’s fashion for high-end electronics in luxury hotels allowed a hacker to wreak havoc in 200 suites at once in a five-star...
-

 93Privacy
93PrivacyOnline privacy – FBI ‘using malware’ to track site visitors
For several years, FBI agents have been taking an unusual approach to detective work online - using malware against suspects who have...
-

 76Cyber Crime
76Cyber CrimeCyberVor hacking gang steals 1.2 billion usernames and passwords
Somewhere in a small city in south central Russia, a group of men in their twenties have got away with what some...
-

 105Malware
105MalwareMalware behind 25% of cyber attacks – and DoS is ‘so last year’ says CERT team
Cybercriminals are waging a game of ‘cat and mouse’ with corporations, well-armed with malware protection AV software but facing adversaries who scan...
-
 76Cyber Crime
76Cyber CrimeDark web II: Tor’s markets ramp up security – and business booms
Since a recent claim researchers could “uncloak” Tor users for less than $3,000, there has been a flurry of activity in the...
-

 192News
192NewsBadUSB exploit hacks your computer
A common shortcoming that most of the USB devices possess is one which can be noiselessly made use of to introduce infection...
-

 380Surveillance
380SurveillanceNSA proof Email Service ProtonMail launching Mobile App
Previously we told you about ProtonMail, an email service said to be totally surveillance proof. The developers of this service are going...
-

 400Cyber Crime
400Cyber CrimeData breach burns Firefox – add‑on creators hit by email leak
After a technical error on a Mozilla database, thousands of email addresses and encrypted passwords were exposed for nearly a month -...
-
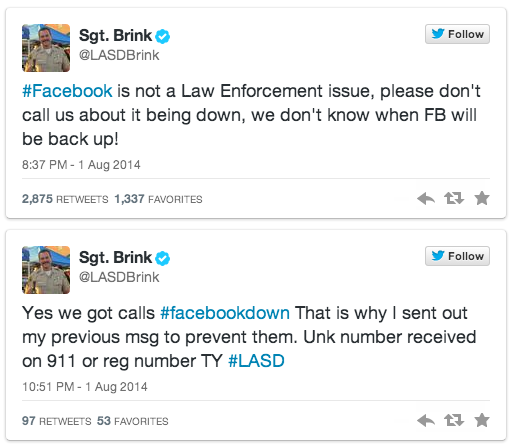
 108News
108NewsFacebook goes down; users call police to bring back the service
As we all know Facebook was down yesterday for unknown reason, but how the users took it is a totally different story....
-

 276Cyber Crime
276Cyber CrimeAnonymous hackers take down Mossad website against Gaza attacks
The hacktivist group Anonymous has claimed responsibility of taking down the official website of Israeli intelligence agency Mossad against Gaza attacks. Mossad’s...
-

 79Malware
79MalwareMalware is called malicious for a reason: the risks of weaponizing code
The risks of using government use of malicious code in cyber conflict are examined in this paper by Andrew Lee and Stephen...
-

 156Malware
156MalwareHomeland Security warns of new Point of Sale attacks
New malware targeting point of sale (PoS) systems, detected by ESET as Win32/Spy.Agent.OKG is described in a warning and analysis distributed by...
-

 65Cyber Crime
65Cyber CrimeWeek in Security: Tor in turmoil, USB ports in a storm, Android app attack
This week in security news saw the world’s researchers discover a whole new range of Achilles Heels for PCs, the online privacy...
-

 94Privacy
94PrivacyTor ‘unmasked’ – but who is at risk?
Users of the online privacy service Tor - designed to allow users to access hidden sites anonymously - may have been unmasked...
-

 115Malware
115MalwareMalware: Every USB port is “defenseless” against new scam
The billions of USB ports in use in PCs are vulnerable to a new attack - which can undetectably install malware, steal...
-

 529Android
529AndroidAndroid security flaw gives bad apps super‑powers
A new Android flaw potentially affecting up to 80% of users could leave handsets vulnerable to rogue apps - leapfrogging the defenses...
-

 310Windows
310WindowsWindows XP Doomed – hackers play classic shooter on ATM
For computer hackers, making the classic first-person shooter Doom play on odd devices is a quest that never ends - but an...
-

 174Privacy
174PrivacyMicrosoft denies it has ever been asked to plant a snooping backdoor into its products
If intelligence and law enforcement agencies have a genuine need to spy upon some communications then it should not be via a...
-

 67Cyber Crime
67Cyber CrimeIdentity fraud: How one email wiped out $300m – and sender walked free
A single email wiped $300 million off the value of an Australian mining company, after an environmental activist, Jonathan Moylan and sent...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




