Featured News
-

 63Cyber Crime
63Cyber CrimeWeek in security: FBI malware, billion password leak – Chinese hotel goes mad
With Black Hat 2014 in full swing in Las Vegas, it was never going to be a quiet week - but revelations...
-

 549Hacking
549HackingInternet of Things: Google’s Nest hacked into “full‑fledged” spy gizmo
Yet another “connected” device was outed as a potential spy this week - as researchers showed how Google’s Nest thermostat could be...
-

 91Privacy
91PrivacyThe state of healthcare IT security: are Americans concerned enough?
The privacy and security of medical records is a matter of concern to many Americans now that most are now stored electronically,...
-

 168Hacking
168HackingInternet of things: Hacker unleashes “mayhem” in 200 hotel rooms
Today’s fashion for high-end electronics in luxury hotels allowed a hacker to wreak havoc in 200 suites at once in a five-star...
-

 94Privacy
94PrivacyOnline privacy – FBI ‘using malware’ to track site visitors
For several years, FBI agents have been taking an unusual approach to detective work online - using malware against suspects who have...
-

 77Cyber Crime
77Cyber CrimeCyberVor hacking gang steals 1.2 billion usernames and passwords
Somewhere in a small city in south central Russia, a group of men in their twenties have got away with what some...
-

 106Malware
106MalwareMalware behind 25% of cyber attacks – and DoS is ‘so last year’ says CERT team
Cybercriminals are waging a game of ‘cat and mouse’ with corporations, well-armed with malware protection AV software but facing adversaries who scan...
-
 77Cyber Crime
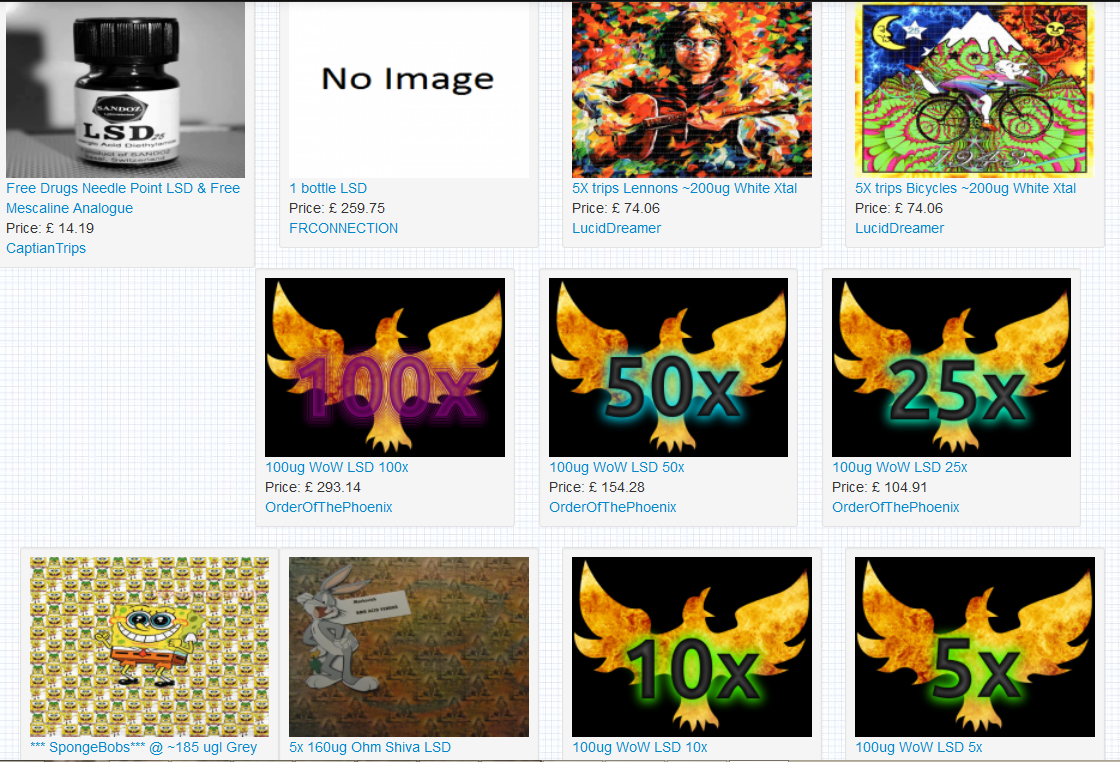
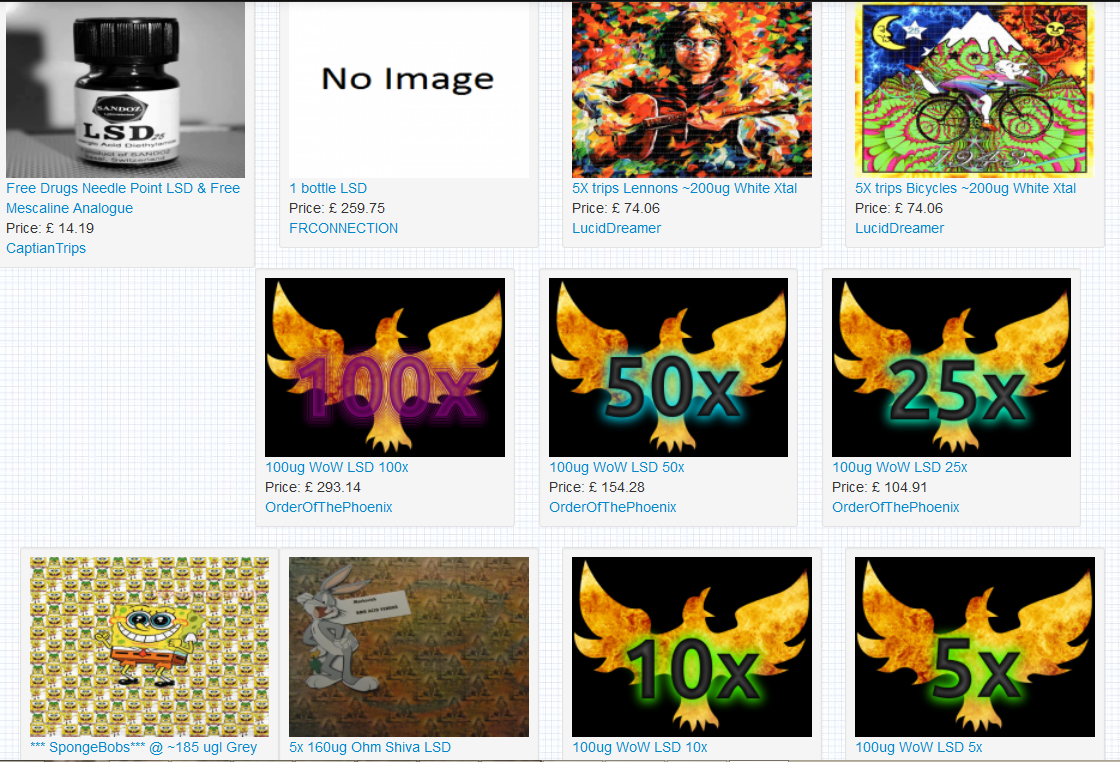
77Cyber CrimeDark web II: Tor’s markets ramp up security – and business booms
Since a recent claim researchers could “uncloak” Tor users for less than $3,000, there has been a flurry of activity in the...
-

 193News
193NewsBadUSB exploit hacks your computer
A common shortcoming that most of the USB devices possess is one which can be noiselessly made use of to introduce infection...
-

 380Surveillance
380SurveillanceNSA proof Email Service ProtonMail launching Mobile App
Previously we told you about ProtonMail, an email service said to be totally surveillance proof. The developers of this service are going...
-

 401Cyber Crime
401Cyber CrimeData breach burns Firefox – add‑on creators hit by email leak
After a technical error on a Mozilla database, thousands of email addresses and encrypted passwords were exposed for nearly a month -...
-
 110News
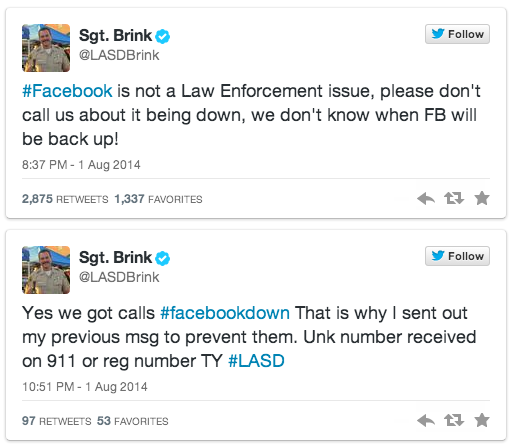
110NewsFacebook goes down; users call police to bring back the service
As we all know Facebook was down yesterday for unknown reason, but how the users took it is a totally different story....
-

 277Cyber Crime
277Cyber CrimeAnonymous hackers take down Mossad website against Gaza attacks
The hacktivist group Anonymous has claimed responsibility of taking down the official website of Israeli intelligence agency Mossad against Gaza attacks. Mossad’s...
-

 79Malware
79MalwareMalware is called malicious for a reason: the risks of weaponizing code
The risks of using government use of malicious code in cyber conflict are examined in this paper by Andrew Lee and Stephen...
-

 158Malware
158MalwareHomeland Security warns of new Point of Sale attacks
New malware targeting point of sale (PoS) systems, detected by ESET as Win32/Spy.Agent.OKG is described in a warning and analysis distributed by...
-

 67Cyber Crime
67Cyber CrimeWeek in Security: Tor in turmoil, USB ports in a storm, Android app attack
This week in security news saw the world’s researchers discover a whole new range of Achilles Heels for PCs, the online privacy...
-

 94Privacy
94PrivacyTor ‘unmasked’ – but who is at risk?
Users of the online privacy service Tor - designed to allow users to access hidden sites anonymously - may have been unmasked...
-

 116Malware
116MalwareMalware: Every USB port is “defenseless” against new scam
The billions of USB ports in use in PCs are vulnerable to a new attack - which can undetectably install malware, steal...
-

 533Android
533AndroidAndroid security flaw gives bad apps super‑powers
A new Android flaw potentially affecting up to 80% of users could leave handsets vulnerable to rogue apps - leapfrogging the defenses...
-

 312Windows
312WindowsWindows XP Doomed – hackers play classic shooter on ATM
For computer hackers, making the classic first-person shooter Doom play on odd devices is a quest that never ends - but an...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




