Featured News
-

 81Cyber Crime
81Cyber CrimeGamescom: How gaming grew up into a target for crime
Video games have gone since the late 1970s and early 1980s from being a small offshoot of the "traditional" computing industry to...
-

 169Cyber Crime
169Cyber CrimeWeek in security: Blackphone unmasked, RATs vs Androids, and browsers kill cars
Blackphone, billed as a privacy tool to keep the puplic safe ruled the headlines when it was is hacked in five minutes,...
-

 284Scams
284ScamsRobin Williams’ last phone call? Sick Facebook video scam exploits celebrity suicide
Sick-hearted scammers have proven themselves to have no morals once again, exploiting the death of Robin Williams with their latest Facebook scam.
-

 75Cyber Crime
75Cyber CrimeRussian PM has his Twitter account hacked, announces “I resign”
There may be red faces in Red Square, after Russian prime minister Dmitry Medvedev had his Twitter account hacked.
-

 95Password
95Password‘Biometric’ earbuds invisibly prove it’s you, with no need for passwords
Biometrics are touted as a replacement for the passwords and PINs we all know and hate - and Intel’s new earbuds could...
-

 91Malware
91MalwareGamescom 2014: World of Malware?
The gaming industry keeps growing, and the crowds at Cologne's Gamescom 2014, show why big game titles are rapidly becoming a target...
-

 105Scams
105ScamsPhone scams: card fraud with that steak, Sir?
A new telephone scam in upscale restaurants in London, has “convincing” scammers calling restaurant staff and tricking them into believing there's a...
-

 139Hacking
139HackingWill web browsers turn cars lethal?
Two researchers have launched a petition to change how car companies and technology cmpanies work together - with a new villain: in-car...
-

 94Cyber Crime
94Cyber Crime2FA – are big banks failing America?
The Target breach caused real damage to millions of American card users - but big financial institutions are doing little to remedy...
-

 385Cyber Crime
385Cyber CrimeWɑit! Stοp! Is that ℓιηκ what it claims to be?
Can you tell the difference between exɑmple and example? Google adds non-Latin support to Gmail, and we explain why characters matter when...
-

 372Password
372PasswordWi‑Fi security – routers “like fish in a barrel”
Researchers flexed their hacking muscles at DefCon 22 to hunt the technology world’s most defenceless beasts - routers. More than a dozen...
-

 173Privacy
173Privacy‘Secure’ Blackphone hacked in 5 minutes
An ultra-secure phone claimed to be the first privacy-focused smartphone on sale swiftly fell victim to a security researcher - who hacked...
-
 104Malware
104MalwareKrysanec trojan: Android backdoor lurking inside legitimate apps
One of the most important pieces of advice we give Android users is to refrain from downloading applications from dubious sources and...
-
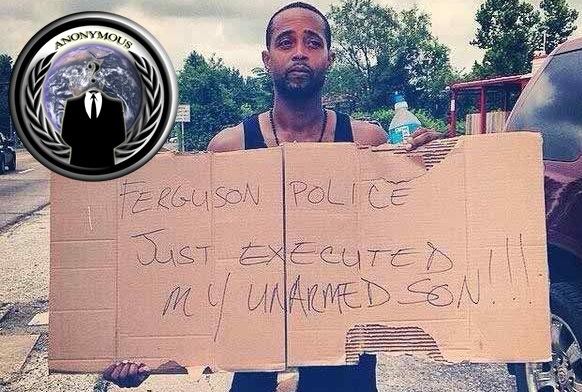
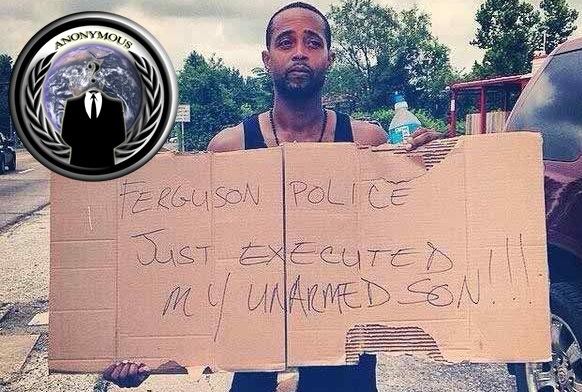 231Cyber Crime
231Cyber CrimeAnonymous to conduct cyber attack on Ferguson PD for shooting unarmed teen
The hacktivist group Anonymous is set to launch a massive cyber attack on Ferguson Police Department against shooting and killing of an unarmed...
-
 138Social Media
138Social MediaFacebook privacy – is Messenger watching you?
Facebook's new Messenger app has spared privacy concerns after a list of Permisssions appears to show the app could be taking video...
-

 427Hacking
427HackingWi‑Fi security: Flight systems “are safe… for now” claims expert
An aircraft security expert has eased the worries of a lot of frequent flyers this week -- by reassuring them that aircraft...
-

 64Cyber Crime
64Cyber CrimeWeek in security: FBI malware, billion password leak – Chinese hotel goes mad
With Black Hat 2014 in full swing in Las Vegas, it was never going to be a quiet week - but revelations...
-

 557Hacking
557HackingInternet of Things: Google’s Nest hacked into “full‑fledged” spy gizmo
Yet another “connected” device was outed as a potential spy this week - as researchers showed how Google’s Nest thermostat could be...
-

 92Privacy
92PrivacyThe state of healthcare IT security: are Americans concerned enough?
The privacy and security of medical records is a matter of concern to many Americans now that most are now stored electronically,...
-

 171Hacking
171HackingInternet of things: Hacker unleashes “mayhem” in 200 hotel rooms
Today’s fashion for high-end electronics in luxury hotels allowed a hacker to wreak havoc in 200 suites at once in a five-star...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




