Featured News
-

 312News
312NewsIsrael’s Channel 10 TV Station Hacked by Hamas
Hackers from Hamas military wing in Palestine hacked the satellite communication of the Channel 10 TV station in Israel on Monday for a few...
-

 102Cyber Crime
102Cyber CrimeHacked Japanese porn sites spread banking malware attack
Thinking of spending some time perusing Japanese porn websites before you do your online banking? Security researchers at ESET have analysed an...
-

 176Cyber Crime
176Cyber CrimeWin32/Aibatook: Banking Trojan Spreading Through Japanese Adult Websites
Win32/Aibatook targets Japanese bank customers with an unusual Internet Explorer monitoring technique. We believe the malware has been in development for months...
-

 99Privacy
99PrivacyArtist mails NSA ‘uncrackable’ mixtape
An artist has created what he claims to be an ‘uncrackable’ mixtape, using freely available encryption tools and housed on a home-made...
-
 79Cyber Crime
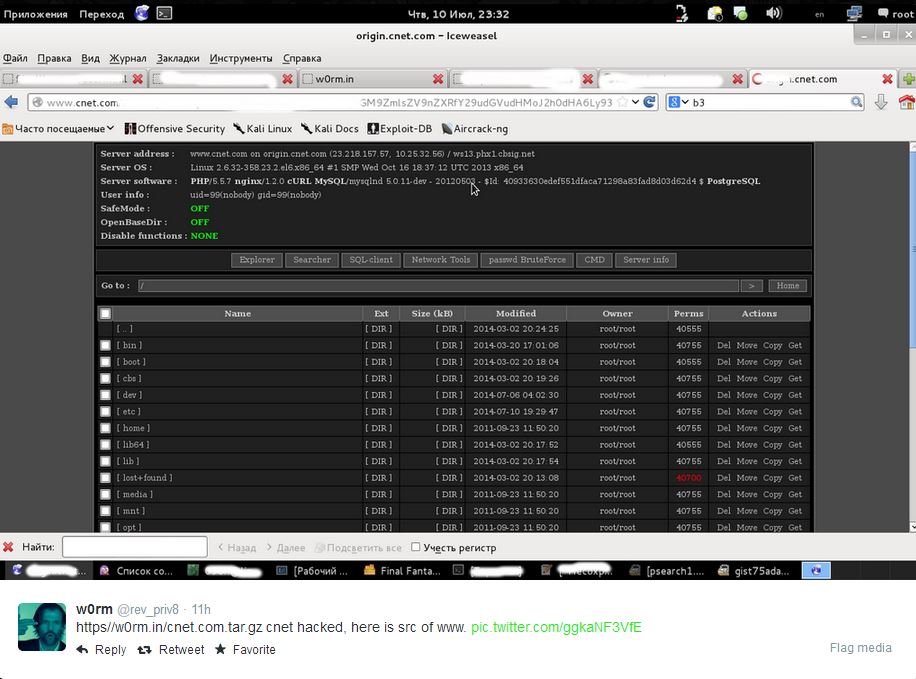
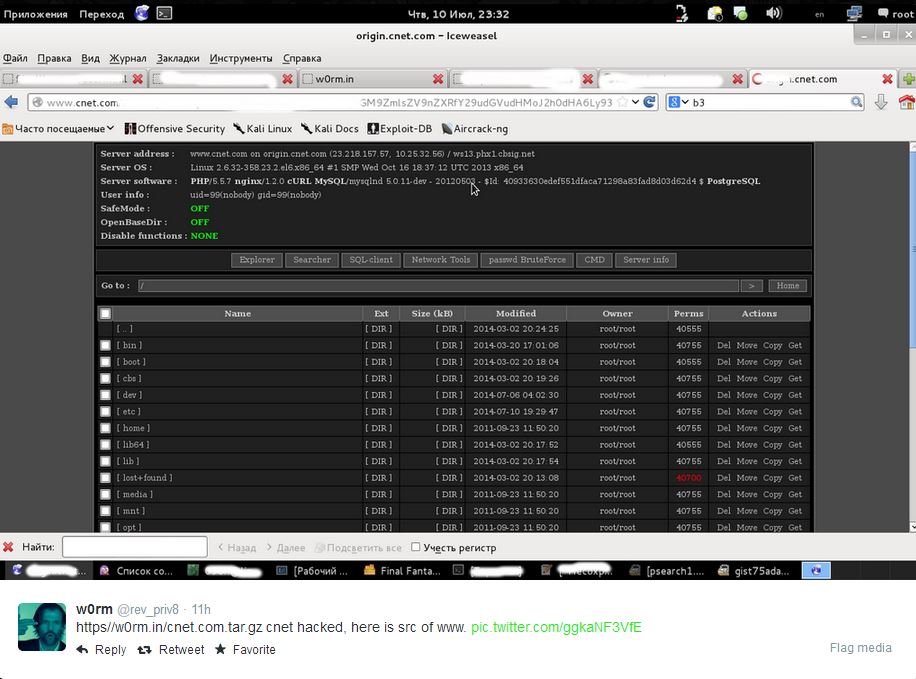
79Cyber CrimeCNET ‘database leak’ – are your details safe?
Popular technology news and review website CNET faced the threat of having a million users' data exposed this week, with an unknown...
-
 140News
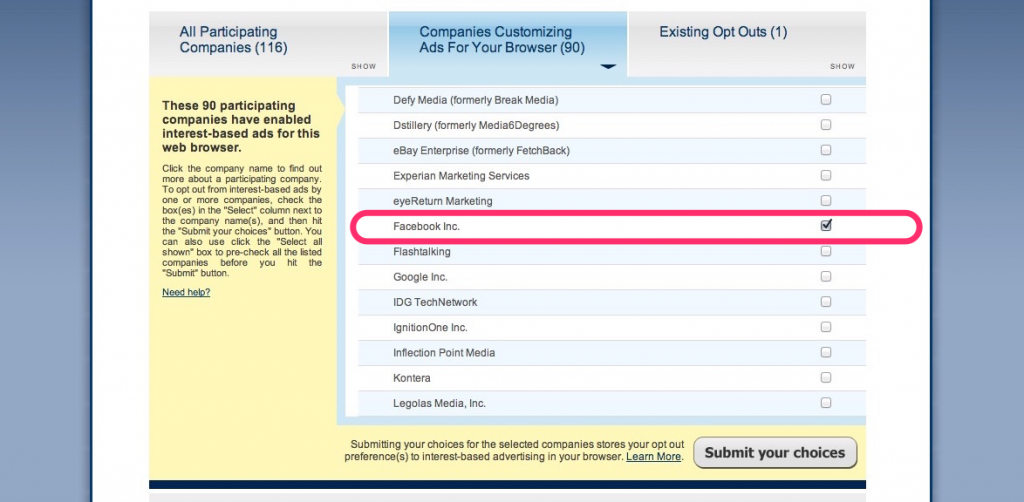
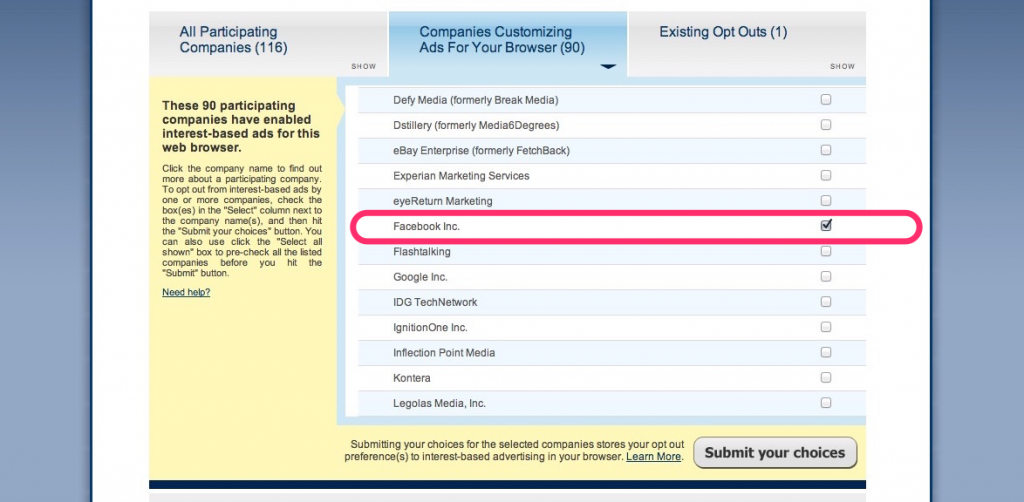
140NewsThis is How You Stop Facebook From Using Your Browsing History
A couple of weeks ago, the social media giant Facebook announced that in order to serve us with targeted ads – it will starting...
-

 71Cyber Crime
71Cyber CrimeData breaches in New York have tripled
Data breaches have hit a record high in the state of New York, tripling since 2006, according to records released by the...
-

 62Cyber Crime
62Cyber CrimeGoogle Chrome security warnings – now in plain English
“Phishing attack ahead” is similar to the stark, clear warnings delivered by road signs - and web users will soon benefit from...
-

 65Cyber Crime
65Cyber CrimeKeylogger malware in hotel business centers – should you worry?
Guests who used business centers in American hotels may be at risk from gangs installing keylogger malware on the computers to steal...
-

 183Password
183PasswordRetina scanner for Samsung Galaxy Note 4?
A Tweet from an official Samsung Galaxy Note 4 account has dropped a very unsubtle hint that its upcoming Galaxy Note 4...
-

 110Privacy
110PrivacyLastPass security holes found by researcher, says password management firm – but no need to panic
LastPass has gone public about a couple of security holes that were found in its popular online password management software. That's enough...
-
 219How To
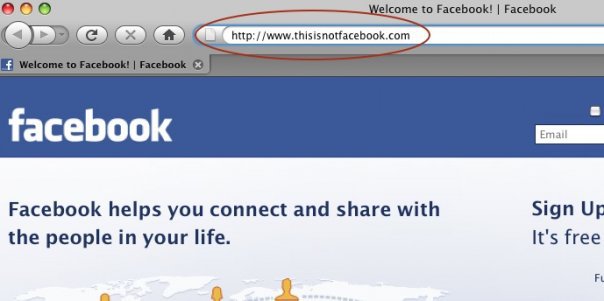
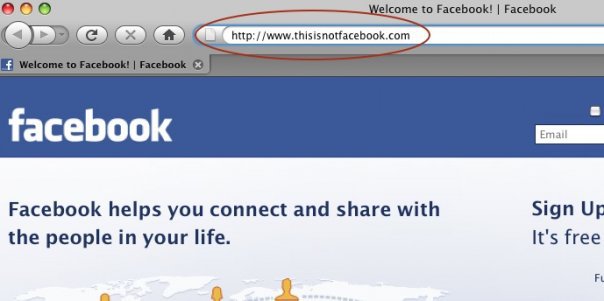
219How ToHow do Facebook accounts get hacked [Protect Yourself Against It]
Facebook phishing. Phishing is a way of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as...
-

 74Cyber Crime
74Cyber CrimeBanking malware Shylock’s servers knocked out by law enforcement
A notorious strain of banking malware, known as Caphaw - or Shylock, due to snippets of Shakespeare’s Merchant of Venice embedded in...
-

 121Privacy
121PrivacyGoogle Drive privacy warning – could yours have leaked data?
Files sent as a link from Google Drive could have shared more than their senders intended, Google admitted this week - in...
-

 2.3KCyber Events
2.3KCyber EventsNorway�s financial sector under massive cyber attack, Anonymous claims �responsibility�
Norway�s�top financial institutions came under massive cyber attacks on Tuesday.Anonymous Norway appears to be behind this attack. The attack�on Norway�s�top financial institutions/banks,...
-

 86Malware
86MalwareCopyright emails ‘poisoned with Trojan’
Emails warning internet users that they have violated copyright and owe companies such as Sony and Paramount a cash settlement have been...
-

 87Cyber Crime
87Cyber CrimeNigerian scams expand to Malaysia – fraud doubles
Nigeria’s notorious fraud industry has expanded overseas - with Nigerian conmen entering Malaysia on student visas to perpetrate fraud using the country’s...
-

 131Privacy
131PrivacyHow to remove your house from Google Street View
How are YOU supposed to remove your house from Google Street View if you don't like the idea that Google drove one...
-

 493Cyber Crime
493Cyber CrimeNew ‘slimline’ ATM skimmers are near‑invisible
New ‘slimline’ ATM skimmers are proving far harder to spot - with some of the hi-tech models remaining in place for up...
-

 150Geek
150GeekAmazon Fire Phone: An Amazing Smartphone (Specifications)
Amazon�s new smartphone launch is all set to fire up the smartphone market and is likely to give a hard time to...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




