Featured News
-

 98Privacy
98PrivacyOnline privacy – FBI ‘using malware’ to track site visitors
For several years, FBI agents have been taking an unusual approach to detective work online - using malware against suspects who have...
-

 79Cyber Crime
79Cyber CrimeCyberVor hacking gang steals 1.2 billion usernames and passwords
Somewhere in a small city in south central Russia, a group of men in their twenties have got away with what some...
-

 108Malware
108MalwareMalware behind 25% of cyber attacks – and DoS is ‘so last year’ says CERT team
Cybercriminals are waging a game of ‘cat and mouse’ with corporations, well-armed with malware protection AV software but facing adversaries who scan...
-
 79Cyber Crime
79Cyber CrimeDark web II: Tor’s markets ramp up security – and business booms
Since a recent claim researchers could “uncloak” Tor users for less than $3,000, there has been a flurry of activity in the...
-

 198News
198NewsBadUSB exploit hacks your computer
A common shortcoming that most of the USB devices possess is one which can be noiselessly made use of to introduce infection...
-

 388Surveillance
388SurveillanceNSA proof Email Service ProtonMail launching Mobile App
Previously we told you about ProtonMail, an email service said to be totally surveillance proof. The developers of this service are going...
-

 404Cyber Crime
404Cyber CrimeData breach burns Firefox – add‑on creators hit by email leak
After a technical error on a Mozilla database, thousands of email addresses and encrypted passwords were exposed for nearly a month -...
-
 112News
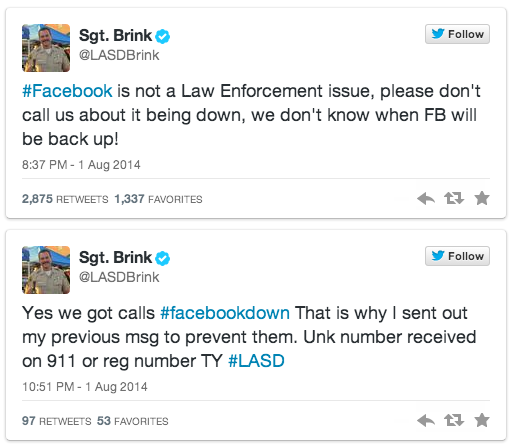
112NewsFacebook goes down; users call police to bring back the service
As we all know Facebook was down yesterday for unknown reason, but how the users took it is a totally different story....
-

 283Cyber Crime
283Cyber CrimeAnonymous hackers take down Mossad website against Gaza attacks
The hacktivist group Anonymous has claimed responsibility of taking down the official website of Israeli intelligence agency Mossad against Gaza attacks. Mossad’s...
-

 81Malware
81MalwareMalware is called malicious for a reason: the risks of weaponizing code
The risks of using government use of malicious code in cyber conflict are examined in this paper by Andrew Lee and Stephen...
-

 160Malware
160MalwareHomeland Security warns of new Point of Sale attacks
New malware targeting point of sale (PoS) systems, detected by ESET as Win32/Spy.Agent.OKG is described in a warning and analysis distributed by...
-

 68Cyber Crime
68Cyber CrimeWeek in Security: Tor in turmoil, USB ports in a storm, Android app attack
This week in security news saw the world’s researchers discover a whole new range of Achilles Heels for PCs, the online privacy...
-

 98Privacy
98PrivacyTor ‘unmasked’ – but who is at risk?
Users of the online privacy service Tor - designed to allow users to access hidden sites anonymously - may have been unmasked...
-

 118Malware
118MalwareMalware: Every USB port is “defenseless” against new scam
The billions of USB ports in use in PCs are vulnerable to a new attack - which can undetectably install malware, steal...
-

 539Android
539AndroidAndroid security flaw gives bad apps super‑powers
A new Android flaw potentially affecting up to 80% of users could leave handsets vulnerable to rogue apps - leapfrogging the defenses...
-

 316Windows
316WindowsWindows XP Doomed – hackers play classic shooter on ATM
For computer hackers, making the classic first-person shooter Doom play on odd devices is a quest that never ends - but an...
-

 177Privacy
177PrivacyMicrosoft denies it has ever been asked to plant a snooping backdoor into its products
If intelligence and law enforcement agencies have a genuine need to spy upon some communications then it should not be via a...
-

 70Cyber Crime
70Cyber CrimeIdentity fraud: How one email wiped out $300m – and sender walked free
A single email wiped $300 million off the value of an Australian mining company, after an environmental activist, Jonathan Moylan and sent...
-

 65Cyber Crime
65Cyber CrimeSony hacked: Victims to get $15m in ‘quality’ games – some day
Victims of the notorious attack against Sony’s online gaming service and associated websites in 2011, which exposed details for up to 77...
-

 121Cyber Crime
121Cyber CrimeCloud security – fears as zombie army finds gold in heavens
Using free cloud application hosting can allow an attacker to create a “free supercomputer” according to The Register's report - used to...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




