Featured News
-

 101Privacy
101PrivacyOnline privacy – FBI ‘using malware’ to track site visitors
For several years, FBI agents have been taking an unusual approach to detective work online - using malware against suspects who have...
-

 83Cyber Crime
83Cyber CrimeCyberVor hacking gang steals 1.2 billion usernames and passwords
Somewhere in a small city in south central Russia, a group of men in their twenties have got away with what some...
-

 113Malware
113MalwareMalware behind 25% of cyber attacks – and DoS is ‘so last year’ says CERT team
Cybercriminals are waging a game of ‘cat and mouse’ with corporations, well-armed with malware protection AV software but facing adversaries who scan...
-
 82Cyber Crime
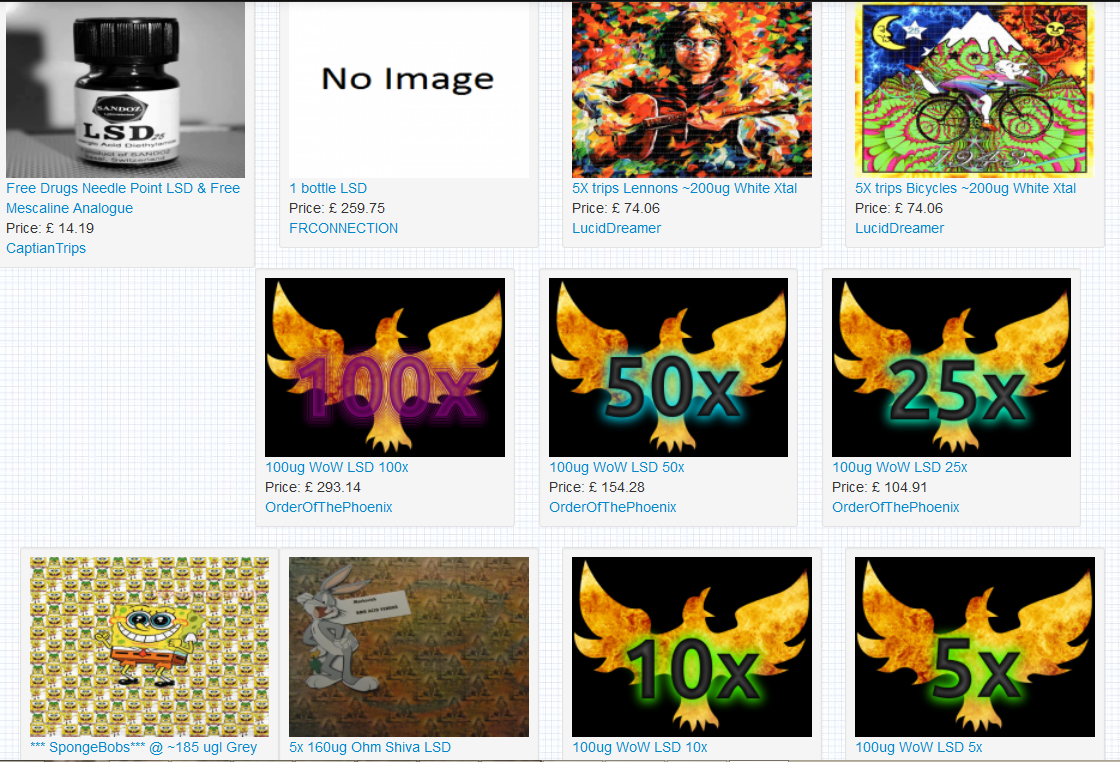
82Cyber CrimeDark web II: Tor’s markets ramp up security – and business booms
Since a recent claim researchers could “uncloak” Tor users for less than $3,000, there has been a flurry of activity in the...
-

 205News
205NewsBadUSB exploit hacks your computer
A common shortcoming that most of the USB devices possess is one which can be noiselessly made use of to introduce infection...
-

 395Surveillance
395SurveillanceNSA proof Email Service ProtonMail launching Mobile App
Previously we told you about ProtonMail, an email service said to be totally surveillance proof. The developers of this service are going...
-

 410Cyber Crime
410Cyber CrimeData breach burns Firefox – add‑on creators hit by email leak
After a technical error on a Mozilla database, thousands of email addresses and encrypted passwords were exposed for nearly a month -...
-
 115News
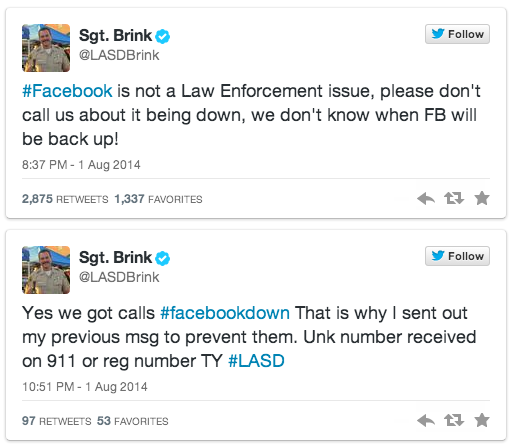
115NewsFacebook goes down; users call police to bring back the service
As we all know Facebook was down yesterday for unknown reason, but how the users took it is a totally different story....
-

 286Cyber Crime
286Cyber CrimeAnonymous hackers take down Mossad website against Gaza attacks
The hacktivist group Anonymous has claimed responsibility of taking down the official website of Israeli intelligence agency Mossad against Gaza attacks. Mossad’s...
-

 85Malware
85MalwareMalware is called malicious for a reason: the risks of weaponizing code
The risks of using government use of malicious code in cyber conflict are examined in this paper by Andrew Lee and Stephen...
-

 165Malware
165MalwareHomeland Security warns of new Point of Sale attacks
New malware targeting point of sale (PoS) systems, detected by ESET as Win32/Spy.Agent.OKG is described in a warning and analysis distributed by...
-

 70Cyber Crime
70Cyber CrimeWeek in Security: Tor in turmoil, USB ports in a storm, Android app attack
This week in security news saw the world’s researchers discover a whole new range of Achilles Heels for PCs, the online privacy...
-

 102Privacy
102PrivacyTor ‘unmasked’ – but who is at risk?
Users of the online privacy service Tor - designed to allow users to access hidden sites anonymously - may have been unmasked...
-

 121Malware
121MalwareMalware: Every USB port is “defenseless” against new scam
The billions of USB ports in use in PCs are vulnerable to a new attack - which can undetectably install malware, steal...
-

 542Android
542AndroidAndroid security flaw gives bad apps super‑powers
A new Android flaw potentially affecting up to 80% of users could leave handsets vulnerable to rogue apps - leapfrogging the defenses...
-

 320Windows
320WindowsWindows XP Doomed – hackers play classic shooter on ATM
For computer hackers, making the classic first-person shooter Doom play on odd devices is a quest that never ends - but an...
-

 181Privacy
181PrivacyMicrosoft denies it has ever been asked to plant a snooping backdoor into its products
If intelligence and law enforcement agencies have a genuine need to spy upon some communications then it should not be via a...
-

 73Cyber Crime
73Cyber CrimeIdentity fraud: How one email wiped out $300m – and sender walked free
A single email wiped $300 million off the value of an Australian mining company, after an environmental activist, Jonathan Moylan and sent...
-

 71Cyber Crime
71Cyber CrimeSony hacked: Victims to get $15m in ‘quality’ games – some day
Victims of the notorious attack against Sony’s online gaming service and associated websites in 2011, which exposed details for up to 77...
-

 125Cyber Crime
125Cyber CrimeCloud security – fears as zombie army finds gold in heavens
Using free cloud application hosting can allow an attacker to create a “free supercomputer” according to The Register's report - used to...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




