Featured News
-
 433Scams
433ScamsWorld Cup scams: an early kick‑off
Amazingly, it was way back in 2011 that I came across my very first World Cup 2014 scam. Surely that merits a...
-

 375Surveillance
375Surveillance“Riot Control” Drone Will Shoot Pepper Spray Bullets At Protesters
We know how drones are used for surveillance, target killings or in some cases to save human lives, but now a South African company...
-

 101Cyber Crime
101Cyber CrimeInternet firm goes out of business after DDoS extortion attack
Blackmailers force internet site Code Spaces out of business, leaving customers in the lurch.
-

 91Malware
91MalwareInteractive exploit kit redirection technique
The usual pattern we see when dealing with exploit kits starts with a legitimate website that gets compromised and used to automatically...
-

 76Cyber Crime
76Cyber CrimeCalifornia company sues bank over cybercrime, wins $350,000 settlement
A California oil company that lost thousands after being attacked by hackers has won $350,000 in a legal settlement after suing its...
-

 150Scams
150ScamsWorld Cup Phishing Scam hits FIFA 14 players through Instagram, Twitter
As the World Cup heads into its third week, there’s a new phishing scam to be aware of. EA Games’ FIFA 14...
-

 111Malware
111MalwareTargeted attack against Vietnamese government: right on the MONRE
ESET researchers recently came across a targeted attack against the Vietnamese government's Ministry of Natural Resources and Environment (MONRE).
-

 520Malware
520MalwareCatch the ESET 2014 Mid‑Year Threat Report broadcast
With the first half of the year almost over, it's time for the ESET 2014 Mid-Year Threat Review. Presented as a webinar,...
-

 144Hacking
144HackingAncestry.com brought down by DDOS attack, but says user data is safe
Ancestry.com has become the latest site to be taken down by a distributed denial-of-service (DDOS) attack. The genealogy website was shut down...
-
 215Hacking
215HackingNokia paid millions to blackmailing hackers
Nokia paid several million euros to criminals who threatened to reveal the source code for part of its smartphone operating system seven...
-
 122Malware
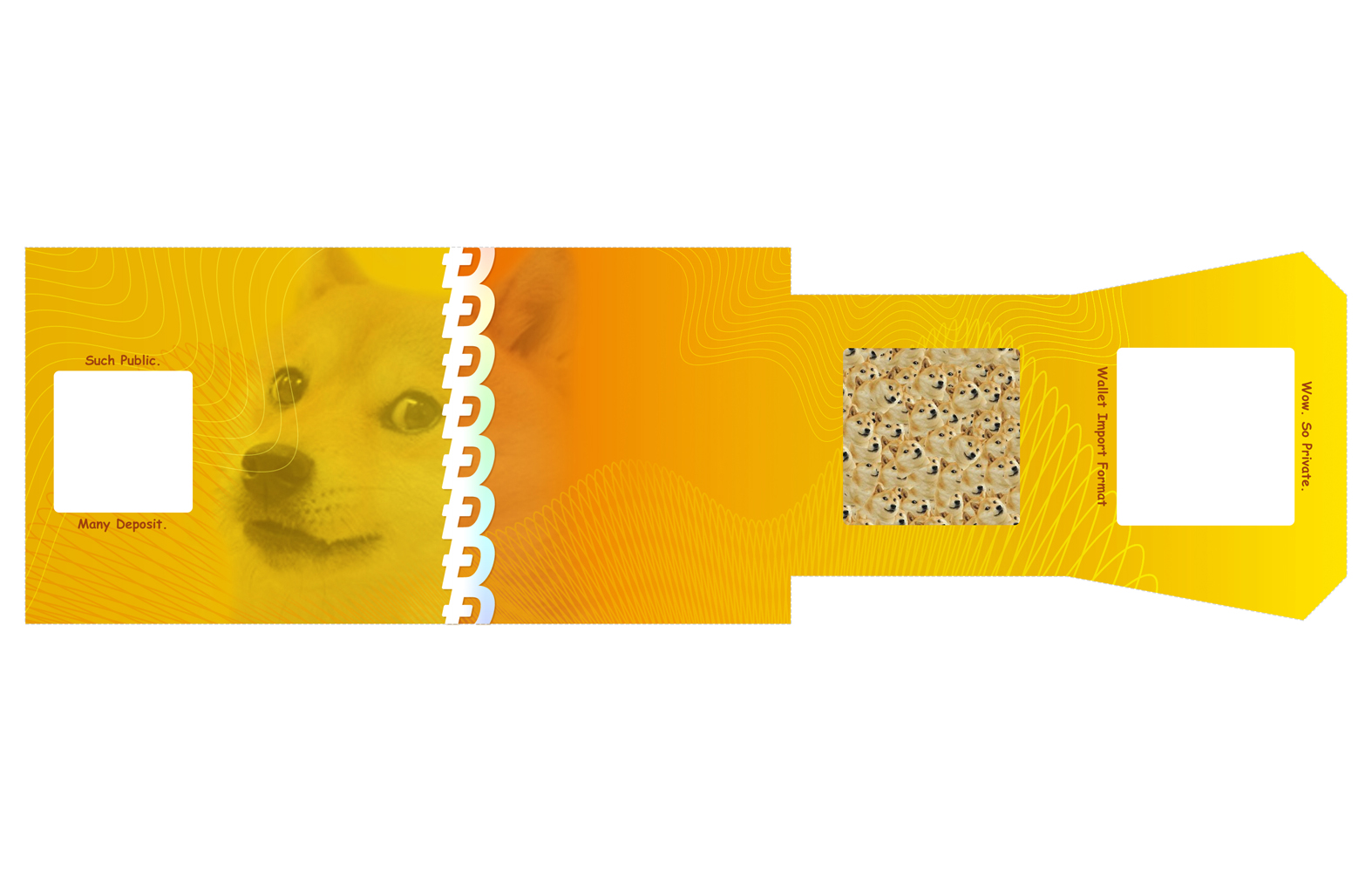
122MalwareHacker amasses $620,000 in cryptocurrency using infected computers
A hacker has reportedly harvested over $600,000 in digital currency, using a network of hijacked machines, in what is believed to be...
-

 64Cyber Crime
64Cyber CrimeNew banking malware ‘Dyre’ targets Bank of America, CitiGroup accounts
A dangerous new strain of malware has been discovered, able to steal banking credentials without alerting users to the interception.
-
 81Password
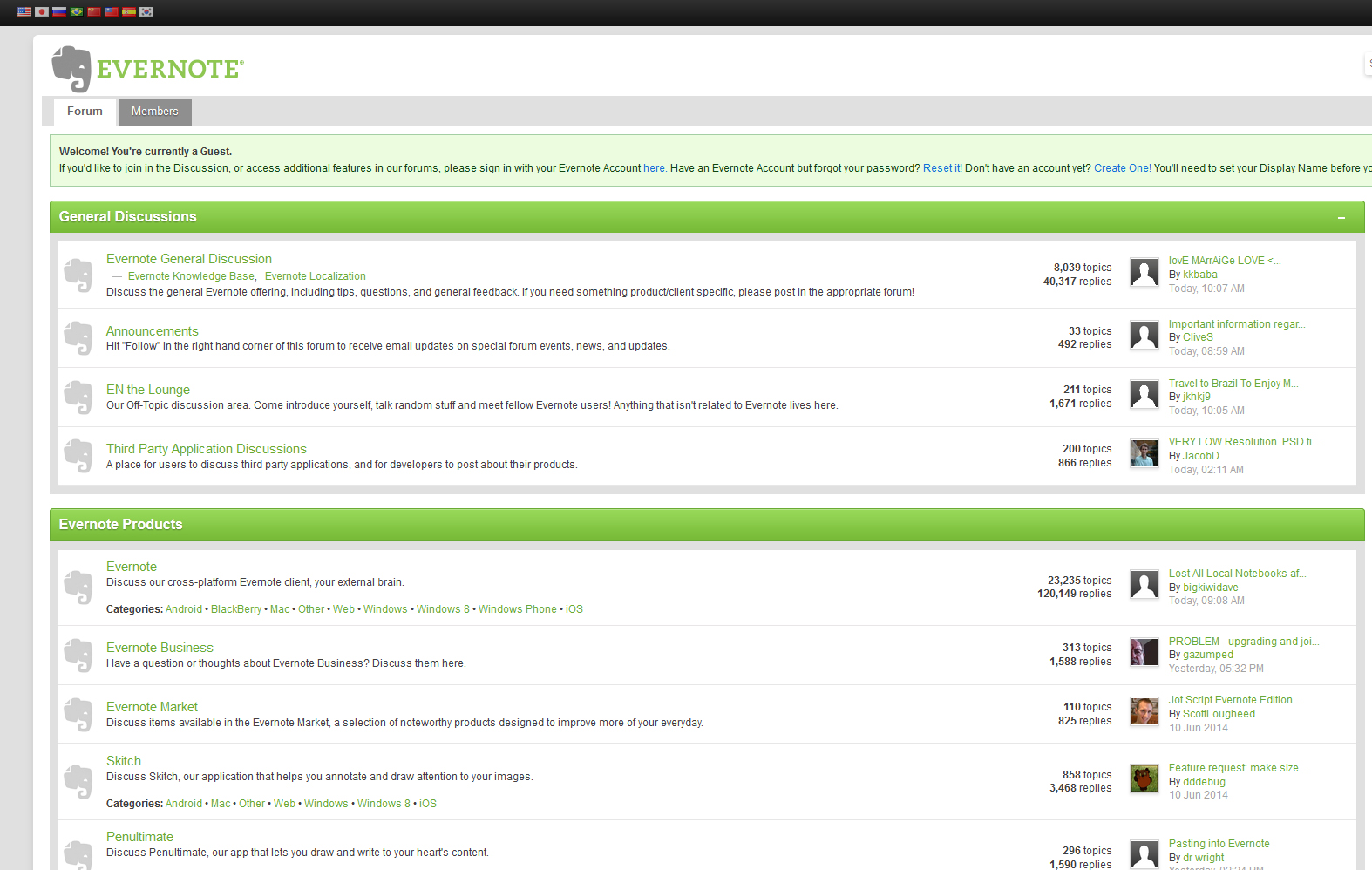
81PasswordEvernote forum hacked, revealing users’ passwords and email addresses
Note-taking and archiving app Evernote has announced that its discussion forum has been hacked, compromising some users’ passwords, dates of birth and...
-
 176News
176News#OpWorldCup: Anonymous Hacks Brazilian Govt, Police, Court & Globo TV
Anonymous has fulfilled its promise of conducting cyber attacks on the government of Brazil during the football World Cup. Anonymous has come up...
-

 75Cyber Crime
75Cyber CrimeDomino’s Pizza refuses to pay ransom after customer database hacked
A group of hackers claim to have stolen the personal details of some 650,000 pizza lovers, and have threatened to release them...
-

 131Hacking
131HackingPinterest hit by weight loss spam
Picture-sharing social media site Pinterest appears to have been hacked, as multiple users reported weight-loss spam messages both on Pinterest itself and...
-
News
Domino�s Pizza Database Hacked, 650,000+ Customer Records Stolen
A group of hackers going with the handle of Rex Mundi breached into the database of Domino�s Pizza websites in France and...
-

 141Opinion
141OpinionCyber Boot Camp and tomorrow’s cyber security professionals
The top three teams from the fifth annual Mayors' Cyber Cup will attend Cyber Boot Camp at the headquarters of ESET North...
-

 123Opinion
123OpinionDon’t let social media undermine the promise of graduation
Graduation is a great time to review your social media profile. Don't let a wild and crazy social network presence undermine the...
-

 62Cyber Crime
62Cyber CrimeP F Chang’s chain suffers breach – thousands of cards for sale online
Newly stolen credit and debit card details, from cards used in P F Chang’s China Bistro, a nationwide American chain of restaurants,...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




