Featured News
-

 531Malware
531MalwareCatch the ESET 2014 Mid‑Year Threat Report broadcast
With the first half of the year almost over, it's time for the ESET 2014 Mid-Year Threat Review. Presented as a webinar,...
-

 146Hacking
146HackingAncestry.com brought down by DDOS attack, but says user data is safe
Ancestry.com has become the latest site to be taken down by a distributed denial-of-service (DDOS) attack. The genealogy website was shut down...
-
 219Hacking
219HackingNokia paid millions to blackmailing hackers
Nokia paid several million euros to criminals who threatened to reveal the source code for part of its smartphone operating system seven...
-
 123Malware
123MalwareHacker amasses $620,000 in cryptocurrency using infected computers
A hacker has reportedly harvested over $600,000 in digital currency, using a network of hijacked machines, in what is believed to be...
-

 65Cyber Crime
65Cyber CrimeNew banking malware ‘Dyre’ targets Bank of America, CitiGroup accounts
A dangerous new strain of malware has been discovered, able to steal banking credentials without alerting users to the interception.
-
 83Password
83PasswordEvernote forum hacked, revealing users’ passwords and email addresses
Note-taking and archiving app Evernote has announced that its discussion forum has been hacked, compromising some users’ passwords, dates of birth and...
-
 178News
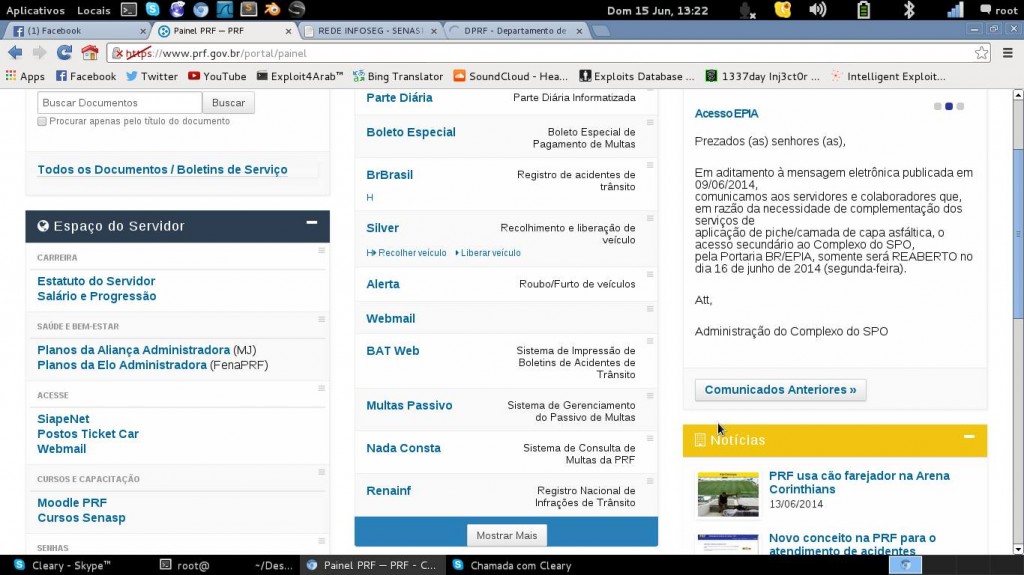
178News#OpWorldCup: Anonymous Hacks Brazilian Govt, Police, Court & Globo TV
Anonymous has fulfilled its promise of conducting cyber attacks on the government of Brazil during the football World Cup. Anonymous has come up...
-

 76Cyber Crime
76Cyber CrimeDomino’s Pizza refuses to pay ransom after customer database hacked
A group of hackers claim to have stolen the personal details of some 650,000 pizza lovers, and have threatened to release them...
-

 135Hacking
135HackingPinterest hit by weight loss spam
Picture-sharing social media site Pinterest appears to have been hacked, as multiple users reported weight-loss spam messages both on Pinterest itself and...
-
News
Domino�s Pizza Database Hacked, 650,000+ Customer Records Stolen
A group of hackers going with the handle of Rex Mundi breached into the database of Domino�s Pizza websites in France and...
-

 142Opinion
142OpinionCyber Boot Camp and tomorrow’s cyber security professionals
The top three teams from the fifth annual Mayors' Cyber Cup will attend Cyber Boot Camp at the headquarters of ESET North...
-

 124Opinion
124OpinionDon’t let social media undermine the promise of graduation
Graduation is a great time to review your social media profile. Don't let a wild and crazy social network presence undermine the...
-

 63Cyber Crime
63Cyber CrimeP F Chang’s chain suffers breach – thousands of cards for sale online
Newly stolen credit and debit card details, from cards used in P F Chang’s China Bistro, a nationwide American chain of restaurants,...
-

 120Scams
120ScamsTweetDeck flaw uncovered “by accident”
A vulnerability in the official Twitter client Tweetdeck left users vulnerable to attack, forcing thousands of users to retweet cryptic lines of...
-

 71Cyber Crime
71Cyber CrimeBank of England “fends off” eight cyber attacks per week, says CISO
The Bank of England weathers an average of eight cyber attacks including malware-laced “spear phishing” campaigns per week, according to Chief Information...
-

 116Scams
116ScamsWorld Cup scams: team tactics to keep you safe
With the World Cup in Brazil poised to begin, the whole world is watching - and that includes cybercriminals. Here's the latest...
-

 67Cyber Crime
67Cyber CrimeBanks to work with UK government experts to ‘predict’ cyber attacks
A new intelligence-sharing network aims to protect financial institutions by sharing information between government, security firms and financial institutions to “predict” vulnerabilities.
-
 108Privacy
108PrivacyFacial recognition camera used to convict robber for first time
In a world-first case, biometric facial recognition software has been used to convict an armed robber, with a Chicago robber “matched” from...
-

 354Opinion
354OpinionEncryption essential for cyber security: A million reasons to encrypt sensitive data
Encryption is essential to cyber security today, with encryption of personally identifiable information (PII) being a top priority for organizations large and...
-

 199News
199NewsTwo Big Anonymous Hacktivist Pages on Facebook get Verified Badges
While surfing Facebook, you must have seen a blue badge indicating verified pages and profiles of famous people such as celebrities, journalists...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




