Featured News
-

 96Password
96PasswordNew iPad could be latest to add fingerprint security
New evidence has emerged that the new iPad will have fingerprint security built in, as found on the Apple iPhone 5S.
-

 237Cyber Crime
237Cyber CrimeEdward Snowden’s Leaks Helped Terrorists: Hillary Clinton
Hillary Clinton, former Secretary of State, a Senator and the First Lady, is not yet convinced that Snowden leaked the classified documents...
-

 203News
203NewsOfficial Website of City of Westminster, California hacked by Saudi Hackers
Two Saudi Arabian hackers going with the handle of NeT-DeViL and Dr-TaiGaR from Group Hp-Hack have hacked and defaced the official website...
-

 278Surveillance
278SurveillanceInternet is a CIA project, be careful before making Google searches: Putin
Russian president Vladimir Putin has said that Internet is a CIA project and Russians should be careful while making Google searches. While...
-

 240News
240NewsSyrian hacker hacks and defaces UNICEF New Zealand Official blog for Free Syria
A Syrian hacker going with the handle of Dr.SHA6H has hacked and defaced the official blog of The United Nations Children’s Fund (UNICEF) designated for...
-

 278Cyber Events
278Cyber EventsSnowden Delivers his Maiden Speech as Glasgow University Rector
The whistleblower kept the students glued as he addressed them via a video link from Russia stressing on “speaking out” for human...
-

 293Cyber Crime
293Cyber CrimeThe perfect job? Dream on! Five signs a job offer is a scam
Job scams are a permanent fixture in cyberspace. Anyone who has posted their resume online has offered cyber gangs two crucial pieces...
-

 73Cyber Crime
73Cyber CrimeBad business: ALL major companies are hosting malware – Cisco
Every single one of 30 major companies tested by Cisco over the course of 2013 had malicious traffic on their networks, according...
-

 95Privacy
95PrivacyYoung people fear internet of things will give away their secrets
Young people are seriously worrried about connected gadgets when it comes to privacy - worrying that 'connected' gadgets such as Smart TVs...
-

 205Cyber Events
205Cyber EventsAnonymous Exposes How Rothschild Family Profited from missing Malaysian Airliner MH 370
A couple of weeks ago, a video was uploaded on YouTube by online hacktivist group Anonymous. In the video anonymous gives an depth...
-

 234Data Security
234Data SecurityAndroid Trojan Virus: iBanking Malware ‘Qadars’ Targets Facebook Users via Webinjects
Cyber criminals have targeted millions of Facebook users through a sophisticated Android Trojan app that can bypass the two-factor authentication shield used...
-

 71Cyber Crime
71Cyber CrimeGoogle offers refunds for buyers of fake Virus Shield app
Google is offering full refunds to buyers of the Virus Shield app which briefly topped the Android charts last week - but...
-

 72Cyber Crime
72Cyber CrimeLack of cyber risk insurance could lead to “global financial shock”
The financial damage caused by a large data breach or malicious employee activity can be enormous, but the lack of financial protection...
-

 98Kids Online
98Kids OnlineHow do you know if your child’s ID has been stolen?
When it comes to identity theft, the most successful attack is on the person least likely to be aware of activity being...
-

 125Privacy
125PrivacyCybercrime evolves as criminal gangs join forces with spies – report
Hackers targeting sensitive information or stealing from retailers work at such speed that customers often notice data breaches first - and for...
-
 104Malware
104MalwareFake Facebook app attack can lead to your Android being spied upon, and your bank account being hacked
Hackers are using a notorious banking Trojan horse to display a bogus message from Facebook, in an aggressive attempt to infect Android...
-
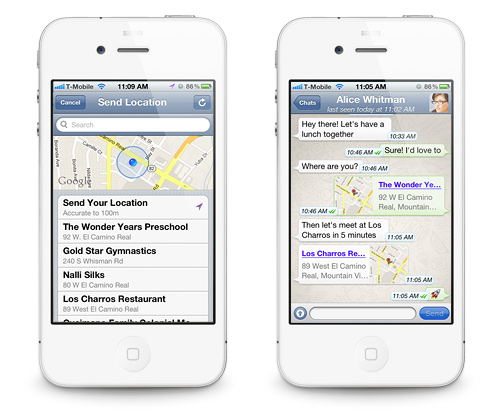
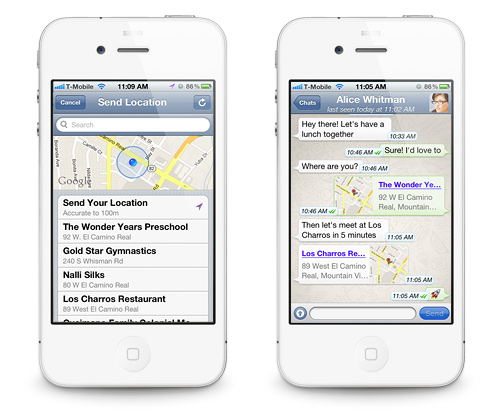 175Data Security
175Data SecurityWhatsApp Flaw leaves User Location Vulnerable to Hackers and Spies.
Researchers warn that the highly popular mobile application WhatsApp cannot be trusted blindly. WhatsApp has been one of the most popular mobile...
-

 144Surveillance
144SurveillanceNo Room for Privacy: Facebook Launches Friend-Spying Feature ‘Nearby Friends’
A new feature introduced by Facebook to allow meeting the Facebook friends in real time when they are actually close by has...
-

 241News
241NewsOfficial website of Bangalore City Police hacked by Pakistani hacker
A Pakistani hacker going with the handle of H4x0r10ux m1nd has hacked and defaced the official website of Bangalore City Police India, yesterday....
-

 222How To
222How ToHow to run Kali on your Android device
This tutorial mainly created for Linux fans. Follow the given steps below to install Kali Linux on your Android phone. Step 1:...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets




