Featured News
-

 295Cyber Events
295Cyber EventsSuspended Israeli soldier gets ‘60,000 Facebook likes’ for aiming at Palestinian teen
An Israeli soldier has received massive online support after being suspended for aiming gun at a Palestinian teenager, reported by AFP. A...
-

 85Cyber Crime
85Cyber CrimeCyber defense: businesses need to “spy on” cybercriminals to survive
The key to a good cyber defense strategy is to improve knowledge of current threats, and risks to businesses, according to law...
-

 110Password
110PasswordNo credit card required – Swedish shops let you pay in blood
At 15 payment machines dotted around the Swedish city of Lund, people can buy items without needing a card - or a...
-

 150Geek
150GeekFacebook Introduces Anonymous Login App to Tackle Privacy Concerns
The Facebook CEO Mark Zuckerberg announced on Wednesday that company is introducing an anonymous login feature, which allows users to access applications for...
-
 179Cyber Crime
179Cyber CrimeFBI may put Anonymous hacker behind bars for 440 years on 44 charges
A Texas man and an alleged member of the famous Anonymous hacktivist group, may face prison up to 440 years in the...
-

 201How To
201How ToBusiness continuity management: key to securing your digital future
Business continuity management is the key to securing your company's digital future despite disruptive incidents, from power outages and IT errors to...
-

 81Password
81PasswordKiller app? Lastpass on Samsung Galaxy S5 unlocks EVERYTHING with a fingertip
Samsung has upstaged rival Apple with a fingerprint-locked version of the password-vault app LastPass for its flagship Samsung Galaxy S5, available free...
-

 189Cyber Crime
189Cyber Crime‘Millions’ of users at risk after AOL email breach
Anyone with an AOL email address was urged to change their password and security questions this week after a cyber attack which...
-

 268News
268NewsKALI Linux Website Hacked Using Heartbleed Bug
When it comes to hacking there is nothing like 100% security. Same has happened with the popular penetration testing and Security-related Linux...
-
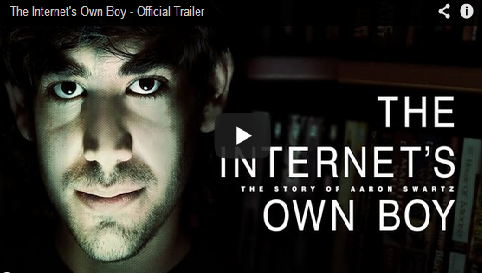
 224Cyber Events
224Cyber EventsWatch Powerful Trailer For The Aaron Swartz Documentary: The Internet’s Own Boy
Earlier it was reported how Reddit developer, Internet genius and hacktivist Aaron Swartz was found dead in his Brooklyn, New York apartment, where he had...
-

 201Surveillance
201SurveillanceNSA Ruined it for US: Brazil ignores Boeing, awards Saab USD 4.5 billion fighter jet deal
Brazil recently awarded a USD 4.5 billion deal for new fighter jets to a Swedish company on Wednesday. The deal, which was...
-

 388Password
388PasswordHow to protect children from in‑app purchase rip‑offs
Parents who simply hand an iPhone or iPad to a child and let them play a favorite game risk children buying expensive...
-

 86Malware
86MalwareAndroid malware worm catches unwary users
An interesting new piece of Android malware has been spotted this week. The threat, detected by ESET security products as Android/Samsapo.A, uses...
-

 168Surveillance
168SurveillanceFacebook shares your data but what about WhatsApp? Do you still want to use it?
WhatsApp, one of the most popular instant messaging services, scaled its highest point recently when it handled more than 64 billion messages...
-

 218News
218NewsAOL Accounts Hacked: Email Addresses, Passwords, Home Addresses Swiped
The AOL website has confirmed a security breach that could have compromised AOL users’ sensitive personal information such as email passwords, postal...
-

 437Cyber Crime
437Cyber CrimeHeart‑breaking – or side‑splitting? Online video offers worst Heartbleed advice possible
Many mainstream news outlets offered advice on dealing with the Heartbleed bug - some misleading. This week, a spoof video has finally...
-

 318Cyber Events
318Cyber Events#OpJustina: Anonymous allegedly Targets Boston Children’s Hospital against Justina Pelletier custody.
The online collective Anonymous has attacked the Boston Children’s Hospital over the recent Justina Pelletier child-custody case, said a recent report by The Boston Globe. The...
-

 198News
198NewsEgyptian Ministry of Information Website Hacked by Libyan Hackers
The official website of Egyptian Ministry of Information has been hacked and defaced by hackers from a group going with the handle of Libyan...
-

 235Opinion
235OpinionMicrosoft Internet Explorer zero day flaw will be even worse for XP users
Microsoft announces a zero-day security flaw in many versions of Internet Explorer, the first to hit Windows users since XP support was...
-

 90Cyber Crime
90Cyber CrimeNetwork structure must change to resist cyber attacks, warns Dr. Eric Cole
Infosecurity expert Dr Eric Cole is to urge companies to take a close look at their network structure, and change it to...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




